Featured News
-
 195Password
195PasswordWhat are the alternatives to passwords?
Is it time for big companies - at the very least - to abandon weak password security? If so, what password alternatives...
-
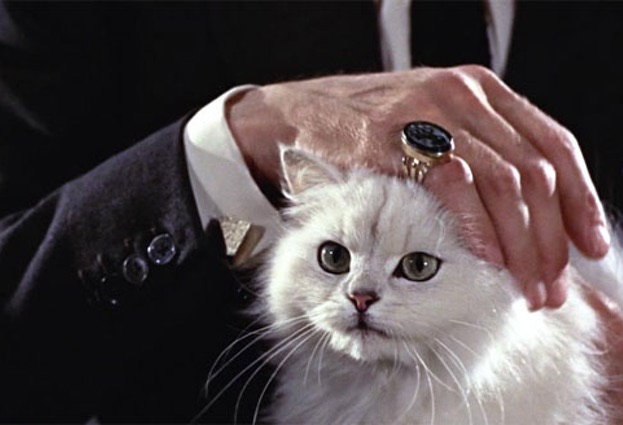
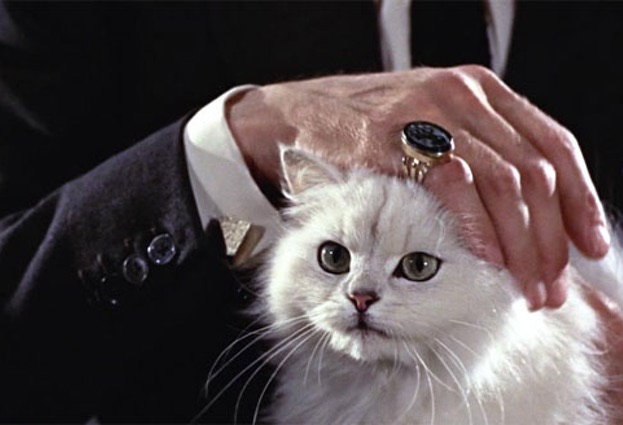 82Cyber Crime
82Cyber CrimeThe utterly crazy story of the death threat hacker (involves a cat)
A cat leads to a notorious death threat hacker finally being caught and jailed in Japan.
-

 107Password
107PasswordRaptr gaming hack leaves user passwords and personal info exposed
Gamers using Raptr and AMD Gaming Evolved chat services should change their login details immediately, following a breach that could give hackers...
-

 254Hacked
254HackedNew Adware Found in Google Play Apps Infecting Millions Of Android Users
Image: Phandroid Generally the mischievous applications on the Android store Google Play don’t last long due to Google’s security measures or...
-

 271Privacy
271PrivacyFacebook turns 11 – what you need to know, and what do your likes say about you?
Facebook updated its privacy settings at the end of January. As Facebook turns 11 today, here’s what you need to know about...
-

 203News
203NewsPro-Assad Hackers Used Female Avatars To Steal Data From Syrian Opposition
It has been found by researchers that a hacking operation has been conducted targeting military intelligence so as to collect it for...
-

 299Data Security
299Data SecurityNew Adobe Flash 0-Day Using Dailymotion.com In Malvertising Campaign
Adobe Flash Player has again seen a zero-day exploit that has appeared in the field due to a critical vulnerability that enables...
-

 240Data Security
240Data SecuritySpotCam Review – this new cloud monitoring camera is trying to change the game
Home monitoring devices are the hot topic recently no matter it is crowd funding website, geeky technology website, or technology news website...
-

 171Cyber Events
171Cyber Events‘Hoodie Bill’: New law against masks aimed at Anonymous, say members
Senate Bill 13 targets Anonymous and its Guy Fawkes masks, according to members of Anonymous, a hacker collective. The bill by Sen....
-

 176Cyber Crime
176Cyber CrimeWhite House seeks 10% increase in cybersecurity spend
President Obama's budget proposal for the 2016 fiscal year includes a projected 10 percent increase in cybersecurity spend, reports Reuters.
-

 104Privacy
104PrivacyHacked dating website Topface buys back stolen personal data from hacker
A Russian dating website that had 20 million email addresses stolen last week, has paid the hackers not to sell the information,...
-

 113Opinion
113OpinionThe New Hacker’s List and an Old Debate: Would you Hire a Hacker?
The recent opening of the Hacker List portal brings to mind the age-old question: Would you hire a hacker?
-

 93Cyber Crime
93Cyber CrimeHipChat hack leads to precautionary password reset
Use HipChat? Be aware that hackers have accessed the names, usernames, email addresses and encrypted passwords for some users.
-

 285Android
285AndroidGoogle announces ‘Vulnerability Research Grants’
Google has announced it is to pay out research grants to security researchers seeking out potential bugs, even if they turn up...
-

 105Malware
105MalwareFacebook porn scam infects 110k users in 48 hours
A new porn scam is spreading startlingly quickly through Facebook - one that has managed to spread malware to over 110,000 users...
-
 188Geek
188GeekBeware: Porn-based malware Infects 110K Facebook Users
Facebook appears to be infected with a porn-based malware that has affected about 110,000 Facebook users in just two days. The malware,...
-

 205News
205NewsRaptr site Hacked – Users advised to Immediately Change their Passwords
One of the most popular online gaming profile trackers Raptr has been hacked and its users are pressed to change their user...
-

 199Hacked
199HackedWarning: Microsoft Outlook App for iOS Harms Your Corporate Security
A developer claims that the newly launched Outlook app for iOS breaks your companies security for mobile PIM access on many levels....
-
 337Lists
337ListsList of Funniest and Useful Commands on Apple’s Siri
For those who do not know much about Siri, Siri is a voice based application which was designed by Apple. It is...
-
 310Data Security
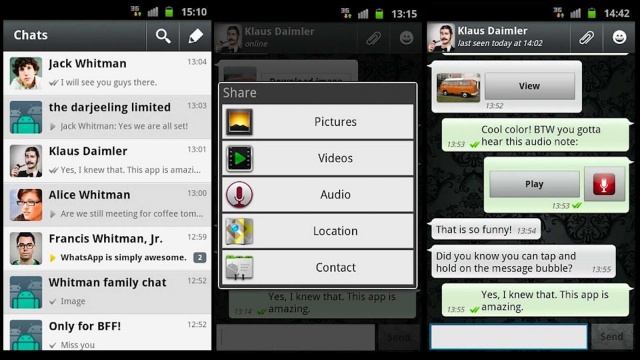
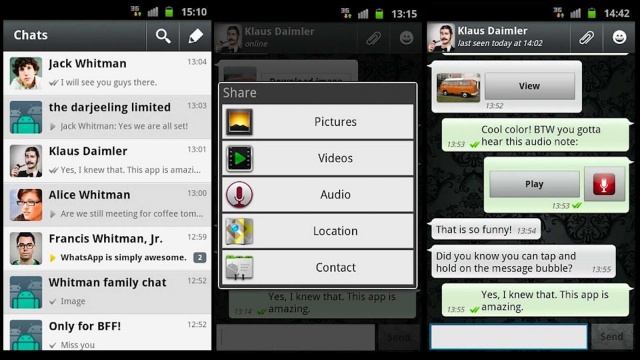
310Data SecurityWhatsApp Web has vulnerability that could expose user photos
Uploading Photos on WhatsApp Web Risky as Privacy Lapses Discovered: WhatsApp Web: WhatsApp Web is a new service launched by WhatsApp. It...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




