Featured News
-

 307News
307NewsPro-ISIS Group Hacked Isle of Wight, Virginia Website
It seems that the tiny county in southeastern Virginia is the new victim of the pro-ISIS hackers as Team System DZ hacked...
-

 145Data Security
145Data Security#JeSuisCharlie Being Used by Hackers To Spread Malware
This news bit strengthens the presumption that hackers can make use of just about anything to fulfill their malicious motives. After the...
-
 285Data Security
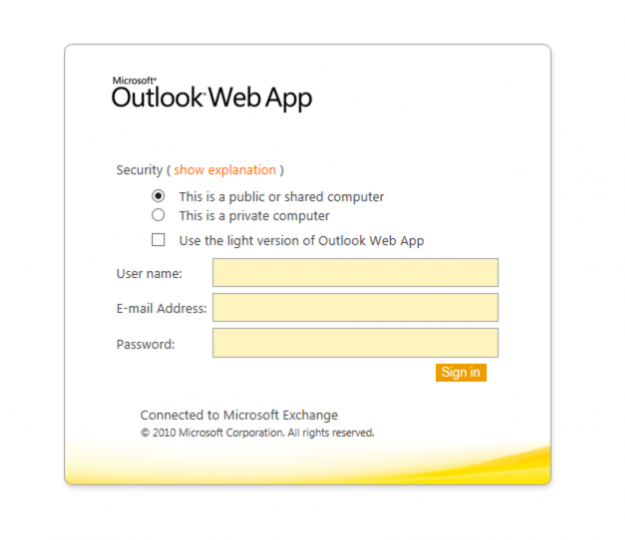
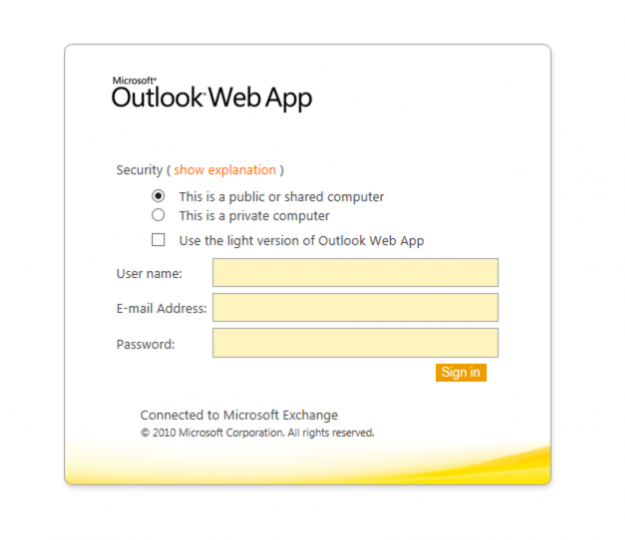
285Data SecurityRussian Spear-Fishing Website Hosts Outlook Web App Phishing Page
Originally this Russian website was designed for purely non-controversial spear-fishing activities, but now its log-in page has been compromised and displays a...
-

 295News
295NewsCharlie Hebdo Aftermath:- About 19,000 French websites hacked so far
As the aftermath of the attack on French satirical magazine Charlie Hebdo, more than 19,000 French websites have been hacked by some...
-

 188Geek
188GeekCan Computer Judge Your Personality Better Than Your Mom?
Social networking has become a major part of lives these days. ‘Being online’ is what that is trending! We spend more time...
-

 438Scams
438ScamsPoliticians and journalists stung by fake open Wi‑Fi protest
Delegates were left red-faced after connecting to an open Wi-Fi network set up to protest mass digital surveillance.
-

 256News
256NewsOhio city’ Website Hacked by Free Syrian Hacker
The Famous Syrian Hacker Dr.SHA6H known for his anti-Bashar Al Assad views has struck again. This time the hackers has hacked and defaced the official Ohio...
-

 154Cyber Crime
154Cyber CrimeObama to call for longer hacking prison sentences with revised Computer Fraud and Abuse Act
President Barack Obama intends to persuade Congress to increase the sentence for hackers, as well as widen the definition of what hacking...
-

 70Cyber Crime
70Cyber CrimeGoogle puts a stop to Adsense malvertising campaign
A 'widespread' malicious advertising campaign that sent web browsers to immitation websites has been stopped by Google
-

 267Data Security
267Data SecurityLA Police’ New Taser Records Footage If Fired
The Los Angeles Police Department has ordered some Tasers with built-in cameras that can actually record if the Taser is used. This...
-

 218Data Security
218Data SecurityFake BBC Website lures victims with Charlie Hebdo misinformation
A website mimicking the official BBC News site has garnered immense traffic earlier this week through false information about Charley Hebdo massacre...
-

 223News
223NewsHackers take free rides after hacking American, United airlines accounts
Countless American and United airlines’ User Accounts Stolen by Hackers – Dozens of free trips booked as hackers retrieve user ids and passwords...
-
 311Windows
311WindowsThe end of mainstream support for Windows 7. Learn from past mistakes
The end of mainstream support for Windows: Don't repeat the mistakes of the past, and be prepared. Especially if you've only just...
-

 98Cyber Crime
98Cyber CrimeSwiss bank data released by hackers
The Swiss state owned Banque Cantonale de Geneve has confirmed that hackers have released confidential customer correspondences after the bank refused to...
-

 77Cyber Crime
77Cyber Crime2015: The cybersecurity threatscape for the year ahead
Presenting a recorded webinar that seeks to answer this question: How is the landscape changing for cybersecurity and what do businesses need...
-

 333Cyber Events
333Cyber EventsList of Eight Popular websites That are Banned in China
Since April 1994, when the first cable connected to China‘s Internet, the Beijing government strives to maintain control over online content accessed...
-

 270Small business
270Small businessObama to propose legislation that protects firms sharing cyberthreat data
President Barack Obama is planning to push legislation which would protect companies from lawsuits for sharing cyberthreat data with the government, reports...
-

 99Cyber Crime
99Cyber CrimeHacked routers used for paid DDoS attacks
The rent-a-DDoS service that knocked out Xbox Live and Playstation Network is powered by thousands of hacked residential internet routers.
-

 98Privacy
98PrivacyBritish Prime Minister wants access to messaging apps
British Prime Minister David Cameron has stated his belief that encrypted messaging services must have backdoor access to government agencies
-

 83Cyber Crime
83Cyber CrimeUS military’s CENTCOM Twitter account hacked – were they not using 2FA?
Twitter and YouTube accounts run by the US military's Central Command are hijacked by hackers claiming to back Islamic State.
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




