Featured News
-

 132Social Media
132Social MediaFacebook launches ThreatExchange for companies to share security threats
Facebook has officially launched ThreatExchange - a collaborative social network where companies can share information on cybersecurity threats, in an effort to...
-

 226Data Security
226Data SecurityHackers target Forbes visitors through chained Flash and IE Zero-days vulnerabilities
Hackers pieced together zero-day vulnerabilities in Flash and Internet Explorer 9+ to attack financial services and defense contractor employees visiting Forbes.com, according...
-

 190How To
190How ToHow to Use TileArt App for Windows Phone?
The TileArt app for Windows Phone takes phone customization to a whole new level. See these incredible parallax effects come to...
-

 123Geek
123GeekMicrosoft Imagine Cup: A Global Student Technology Competition
Every year for the last 12 years, the Microsoft Imagine Cup has driven young, bright minds from all over the globe to help...
-
 200News
200NewsResearcher publishes 10 million passwords, usernames amid FBI raid
A security researcher has revealed from a research of various data breaches, a collection of 10 million usernames and passwords. The leaked...
-

 416Data Security
416Data SecurityKali Linux 1.1.0 Released! Download Now
The developers at Offensive Security are back with yet another great version of Debian-derived Linux distribution Kali Linux version 1.10. Kali Linux 1.1.0 was...
-

 194Surveillance
194SurveillanceSamsung’s Smart TV may be Spying on YOU!
Samsung decision to process voice commands in its latest Smart TV through cloud server has sparked a new debate on data retention,...
-

 111Cyber Crime
111Cyber CrimeHacker gets 8 Years in Jail for Making Prank Death Threats
Remote Control Virus was used by the Hacker to Penetrate into Computer Systems and issue death threats to users. On Wednesday, the...
-

 145Cyber Crime
145Cyber CrimeCyber Threat Intelligence Integration Center: will CTIIC be a game changer?
Is America's new Cyber Threat Intelligence Integration Center a step forward? Or a duplication of the National Cybersecurity and Communications Integration Center...
-
 198Hacked
198HackedHow to Get 2GB Free Google Drive Space by Checking Security Settings
Why is Google giving you free Drive space? On the occasion of Safer Internet Day, Google is giving away a bit of...
-

 91Privacy
91PrivacyOutlook app blocked by EU parliament over ‘serious security issues’
The Microsoft Outlook app has been banned from use in the EU Parliament, according to emails from the parliament's IT department, seen...
-

 155Cyber Crime
155Cyber CrimeWhite House creates new agency to centralize cyberthreat intelligence
The White House is creating a new agency to help counter cyberthreats, analyzing intelligence from around the government so it is better...
-
 161Opinion
161OpinionCensus Scams and ‘Grandparent Scams’
Two phone scams of a type that might be new to you: fake surveys asking dangerous questions, and a Londoning scam that...
-

 295Cyber Events
295Cyber EventsThe Guy who Developed World’s First Email Encryption Software is Broke!
The person who developed the free email encryption software Gnu Privacy Guard in 1997, which was used by famous NSA whistleblower Edward...
-
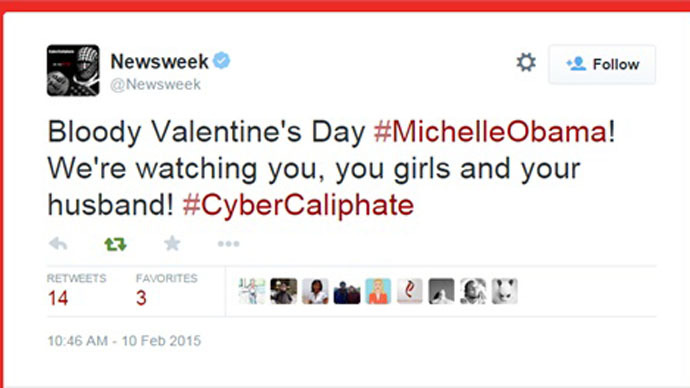
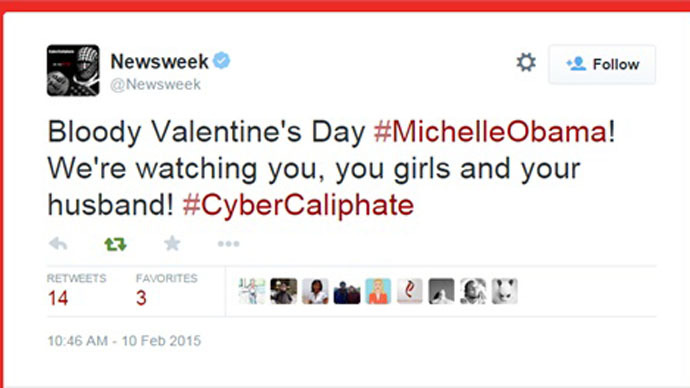 282News
282NewsNewsweek Twitter account hacked by Pro-ISIS hackers
The official Twitter account of world renowned American based Newsweek Magazine was hacked by Cyber Caliphate, a pro-ISIS hacker who previously had hacked Malaysian Airlines...
-

 205Hacked
205HackedHow to Check if You Were Exposed in the 10 Million Password Release?
What is the news? A security researcher has released 10 million usernames and passwords in public domain. Mark Burnett has collected this...
-

 425Cyber Events
425Cyber EventsOpISIS: Anonymous crushes 800 Twitter accounts, 12 Facebook pages of ISIS supporters
The online hacktivist Anonymous has claimed that it took down about 800 Twitter accounts and 12 Facebook pages belonging or somehow supporting the...
-

 226Hacking Tutorials
226Hacking TutorialsWebsite Hacking Methods
Today i’m going to teach you some basics of website hacking , so first , we going to learn about website defacement....
-

 455Privacy
455PrivacyWhatsApp privacy is ‘broken,’ reveals proof‑of‑concept hack
WhatsApp's privacy settings are "broken" and can be bypassed by downloading a simple bit of software, claims the Dutch developer behind proof-of-concept...
-

 91Malware
91MalwareMicrosoft phishing email targeting corporate networks with ‘neurotic malware’
Security researchers have uncovered a trojan that evades sandboxes specifically targeted at corporate users, hidden in legitimate looking phishing email that apes...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks




