Featured News
-

 95Password
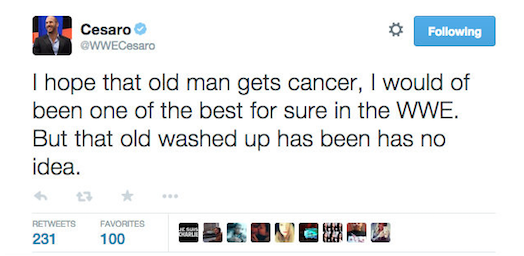
95PasswordHacker puts words into wrestler’s mouth in WWE Twitter hack
WWE superstar Antonio Cesaro was the victim of a Twitter hack this week, as a wrestling fanatic hacked his account to vent...
-

 92Privacy
92Privacy12,000 exposed to possible ID theft after Jeb Bush publishes emails
Possible 2016 Republican presidential candidate Jeb Bush has has had to retroactively redact over 12,000 personal details from emails published in the...
-

 331News
331News#OpChapelHill: Hackers Deface Military Boarding School Website
The online hacktivist AnonGhost is back in action. This time by defacing the official website of an Army and Navy Academy, a Carlsbad, California based...
-
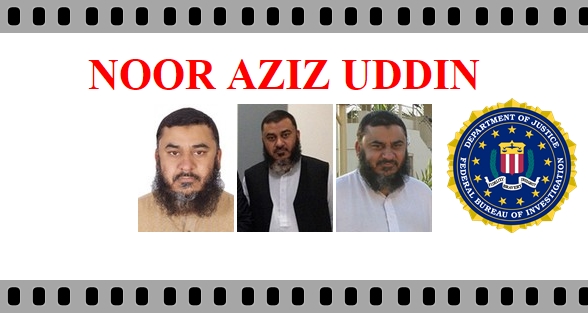
 131Cyber Crime
131Cyber CrimePakistan arrests FBI’s most-wanted Cyber criminal
Officials from Cybercrime Circle of Federal Investigation Agency (FIA) have revealed that two of the Federal Bureau of Investigation (FBI)’s ten most-wanted...
-

 211Privacy
211PrivacyDid GCHQ illegally spy on you? Here’s how to find out
Law enforcement agencies shouldn't be above the law. Find out if the UK's GCHQ illegally spied on you...
-

 292Data Security
292Data SecurityNSA Hiding Undetectable Spyware in Hard Drives Worldwide
The US National Security Agency (NSA) hid undetectable spying software within the hard drives of computers, be it of any make, says...
-

 343News
343NewsGaza Hackers Successfully Target Israel with ‘Porn Star Video’ Malware
Egypt and Gaza-based hackers seem to have united against the Israeli government, military network and research infrastructure since the traces of two...
-

 293News
293NewsChinese Bitcoin exchange Bter hacked, $1.75 million in Bitcoin stolen
While you were celebrating valentines day, the hackers were busy doing what they are good at. Yes, on 14th Feb, 2015, a China-based...
-
 178News
178NewsWWE Superstar Antonio Cesaro’ Twitter account hacked, ‘wish cancer’ on McMahon
The official verified Twitter account of WWE superstar Antonio Cesaro (@WWECesaro) was hacked earlier Tuesday by unknown hacker wishing cancer to the company’s Chairman and...
-

 305Data Security
305Data SecurityVisa to track your smartphone location to “prevent” credit card fraud
Visa, famed payment processing company, will be rolling out its new software with location-tracking capabilities this summer. It will allow banks to...
-
 266How To
266How ToDownload and Run Windows 10 on Mac for Free With Parallels Desktop
Here’s a good news for the Apple users who are in love with Windows 10. Parallels Desktop 10 has just released an...
-

 93Privacy
93PrivacyRussia seeks VPN and Tor ban in anonymity clamp down
Russian authorities have indicated that VPNs and online anonymising software Tor could soon be banned for the country's 143.5 million residents.
-

 295Cyber Crime
295Cyber CrimeC-93 Virus Alert Email from Microsoft is a Phishing Scam
An email is being received by users of Microsoft’s email accounts claiming to be sent from Windows Outlook. It has been titled...
-

 144How To
144How ToKnow How to Map Your Home’s WiFi Signal in 3D
There are ways to map the WiFi signal in your home or surrounding in 2D but it has some limitations. A YouTuber...
-

 309News
309NewsWebsite of UAE’ oldest newspaper Al Ittihad hacked by ISIS hackers
On 14th February, 2015, when people were busy celebrating Valentines day; the ISIS hackers were busy targeting UAE’s oldest Arabic language newspaper Al...
-

 242Hacked
242HackedOne of the Largest Bank Thefts in History, Hackers Steal More Than $300 Million
According to a report by security firm Kaspersky Labs, numerous banks of Russia, the Unites States, Japan and Europe have been the...
-

 188News
188NewsHackers Steal $100 millions+ from US and global banks via Malware
In an isolated incident in late 2013, an ATM at Kiev started dispensing cash randomly without any human interaction; much to the...
-
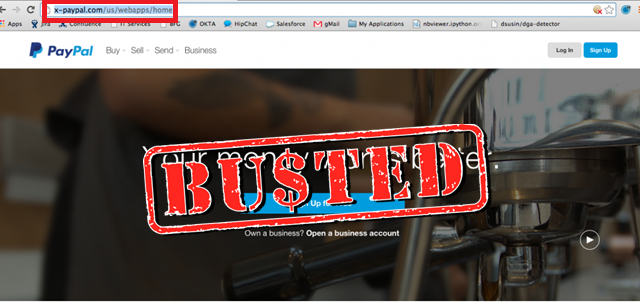
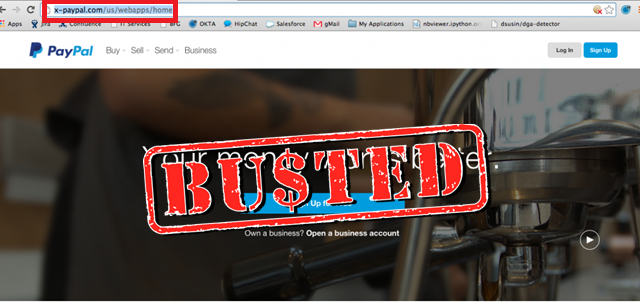 317Cyber Crime
317Cyber CrimeCrackdown: Fake PayPal lookalike phishing websites taken offline
PayPal has always been a target for cybercriminals in fake campaigns to steal money from users. Sometimes PayPal fake emails or phishing links...
-
 216Geek
216GeekInformation Technology Trends – 2015
Short Bytes: Here we’ll be telling you about Docker and Hybrid Cloud that are one of the major tech breakthroughs to happen...
-

 383Data Security
383Data SecurityFBI wants to hide how cops are spying on you via “stingray” cellphone tracker
If by any chance, you have been into a local police department for filing a public request in order to know about...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




