Featured News
-

 85Privacy
85PrivacyGovernment requests for private Facebook data up 24%
Government requests for private Facebook data have increased by nearly 25% since the second half of 2013, the social networking giant has...
-

 97Malware
97MalwareWireLurker: new malware targets Apple users
A new malware has been discovered that targets both Apple Mac computers and iPhones, Neowin reports. It is the first known malware...
-
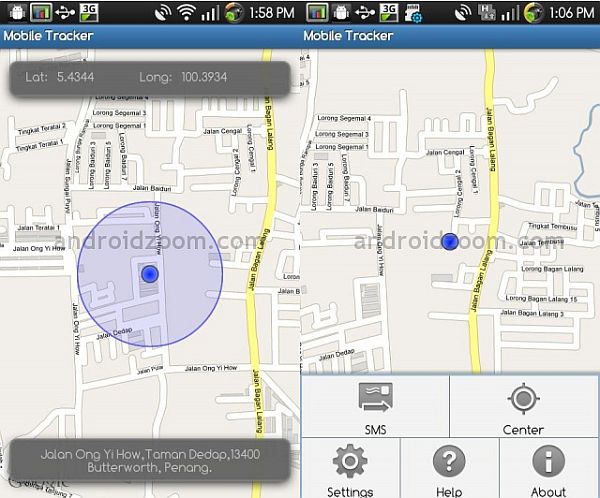
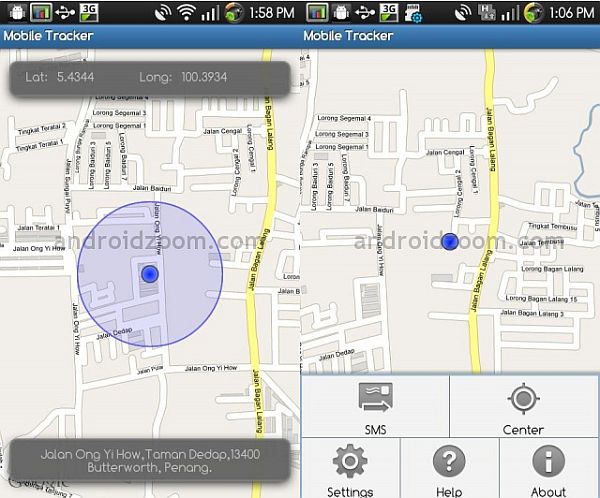 210Android Hacking
210Android HackingHow to track your Android phone with no software installed
Have you (ever) lost your Android smartphone or tablet without having a device tracking app installed? Then you should read this! This...
-

 199IOS Hacking
199IOS HackingJailbreak IOS 7.1x and IOS 8.x
Here’s a quick tut on jailbreaking your Iphone/Ipad/Ipod Touch. This wil work on any Iphone with IOS 7.x up to IOS 8.x....
-

 338Geek
338GeekMozilla to Release New Developer Web Browser on November 10
The latest blog post on Mozilla’s blog revealed that they were working on a new web browser specially developed for developers. Mozilla...
-

 161Privacy
161PrivacyBritish intelligence service echoes FBI’s call for mobile backdoors
Echoing sentiments from across the Atlantic earlier in the year, the head of British spy agency GCHQ as made calls for crypto...
-

 289Banking
289BankingBiometric wristband piloted by Canadian bank
A group of Canadian issuing banks have begun a pilot test of an NFC-enabled version of Nymi - a biometric wristband that...
-

 292Banking
292BankingAmerican Express wants to swap card numbers for tokens
American Express has launched a new service, which looks to swap payment card numbers with unique tokens, reports Network World.
-

 478Malware
478MalwareHacking planes – researchers developing system to stop in‑flight malware
City University professor Dr David Stupples and a team of researchers are looking into ways of minimizing the risk of hacking planes...
-

 145Tricks & How To's
145Tricks & How To'sGetting a Serial Number of any Program/App
Here’s a small tutorial on getting a serial you may need for any program/app. * Go to Google. * In the search...
-
 245Lists
245ListsTop Tech News of the Month, October 2014 | Top Fossbytes
Dear readers, we are back with the Top Fossbytes – Top tech news of the Month. We have covered best stories from...
-
 323News
323NewsHow Gmail ID Can Be Hacked Despite Having Google’s Two-Factor Authentication On
The Two-factor authentication is believed to prevent Gmail accounts from getting hacked. But what happened with indie developer Grant Blakeman shows how two-factor authentication can...
-
 230How To
230How ToHow To Get Google Inbox Without an Invite?
Last week Google launched Google Inbox – a supplement (actually a good one) to the existing Gmail on your computer or your phone. It...
-

 142Lists
142ListsBest Celebrity Halloween Costumes of 2014
Take a look at the best celebrity Halloween costumes of the year 2014! Katy Perry as a cheeto (along with a bag...
-
 271Geek
271GeekFacebook is now available on Tor for Anonymous browsing
Big news from Facebook, if you are a Tor user! Facebook has developed a link that will allow Tor users to browse...
-

 258Privacy
258PrivacyFacebook welcomes private browsers with dedicated Tor link
Facebook has opened its doors to privacy concerned users, but opening up a dedicated Tor link, guaranteeing that people who visit the...
-

 124Mobile Security
124Mobile SecurityMicrosoft issues rapid fix to GroupMe exploit
iOS and Android messaging app GroupMe has had a possible vulnerability fixed quickly by Microsoft, according to The Register. There was no...
-

 116Privacy
116PrivacyPolice can make you unlock your phone with a fingerprint – judge
A judge in Virginia has ruled that the police can require you to unlock your smartphone with a fingerprint, but not with...
-

 440How To
440How ToHow to make sure Adobe Flash is up‑to‑date and enabling it on‑demand
Learn how to update Adobe Flash Player, to help protect against malware attacks.
-

 119Tricks & How To's
119Tricks & How To'sHow to create a Hotspot with notepad
Always wanted to make a hotspot with your pc or laptop , but didn’t have the software? Well today i’ll show you...
The Latest
-
 Cyber Attack
Cyber AttackMicrosoft Outlook Flaw Exploited by Russia’s APT28 to Hack Czech, German Entities
-
 Data Breach
Data BreachPopular Android Apps Like Xiaomi, WPS Office Vulnerable to File Overwrite Flaw
-
 Data Breach
Data BreachDropbox Discloses Breach of Digital Signature Service Affecting All Users
-
 Data Breach
Data BreachCISA Warns of Active Exploitation of Severe GitLab Password Reset Vulnerability
-
 Data Breach
Data BreachNew Cuttlefish Malware Hijacks Router Connections, Sniffs for Cloud Credentials
-
 Cyber Attack
Cyber AttackAndroid Malware Wpeeper Uses Compromised WordPress Sites to Hide C2 Servers
-
 Malware
MalwareEternal Malware: CVE-2024-3400 Rootkits Persist Through Palo Alto Firewalls Updates and Resets
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Data Breach
Data BreachNavigating the Threat Landscape: Understanding Exposure Management, Pentesting, Red Teaming and RBVM
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage




