Featured News
-
 103Privacy
103PrivacySnapchat privacy – spam deluge may make users feel fat
Concerns over Snapchat privacy rocketed this week after users were bombarded with spam messages written in a style which suggests that a...
-

 199How To
199How ToHow to fix Shellshock Bash on Mac OS X: Mavericks edition
Apple Mac OS X users concerned about the Bash vulnerability dubbed Shellshock got some relief late yesterday as Apple published fixes for...
-

 67Cyber Crime
67Cyber CrimeStealthGenie CEO arrested for marketing ‘illegal stalking app’
The creator of an app that secretly allows you to monitor another person’s smartphone usage without their knowledge has been arrested in...
-

 100Mobile Security
100Mobile SecurityFBI Director “very concerned” with smartphone encryption
With Apple, Google and other tech companies responding to users’ demands for privacy with further smartphone encryption options, not everyone is happy....
-
 205Scams
205ScamsSupport Scams: Expect the Scammish Inquisition*
An update on support scams: but are the scammers looking for fresh fields and posturings new?
-
 174Lists
174ListsLast Day of Orkut : 11 Embarrassing & Funny Things We Did on Orkut, a GIF Essay
Yesterday my friend reminded me that September 30th is Orkut‘s last day. It took me back in time when I stopped using...
-

 152Privacy
152PrivacyHow George Clooney made sure phone hackers didn’t ruin his wedding
Newly weds George Clooney and Amal Alamuddin supplied guests with "burner phones" to prevent photographs from falling into the hands of hackers...
-

 226How To
226How ToWrite Your Message in the Sky and Name with the Galaxies
Each time we look at the sky we get amazed by its brilliance and vastness . Whenever I need to spend some...
-

 239Geek
239GeekHong Kong protesters targeted with Android spyware disguised as OccupyCentral app
The pro-democracy protesters in Hong Kong have been targeted with an Android spyware disguised as an #OccupyCentral app, according to a team of security...
-

 338News
338NewsResearcher Hacks iPhone6 TouchID, Big Question over ‘Apple Pay’ Security
Remember when Apple’s iPhone 5S fingerprint sensor or in other words TouchID was hacked? Well history is repeating itself because the Apple...
-
 211Data Security
211Data SecurityShellshock Bash Bug Leaves Almost Every User on The Internet Vulnerable
They call it Shellshock bug, they say it is way more dangerous than the previous Heartbleed bug which left all the secure SSL...
-

 92Cyber Crime
92Cyber CrimeWeek in security: Bash Bug, BlackEnergy and hoax attacks
This week, a serious software vulnerability, which rapidly became known as the ‘Bash Bug’ or ‘Shellshock’ dominated the headlines, as two other...
-

 328Linux
328LinuxHow to resolve Shellshock on Mac OS X, web servers and more
The "Bash Bug" or "Shellshock" vulnerability means a wide range of devices, servers and computers, including Mac OS X, will need to...
-

 229Opinion
229Opinion4Chan: destructive hoaxes and the Internet of Not Things
The media have associated a number of destructive hoaxes with 4chan: people need some historical perspective on how the site actually works.
-

 63Cyber Crime
63Cyber CrimeHealthcare data worth ten times price of credit card data
Medical information is now worth up to 10 times the price of credit card details on online black markets, due to weak...
-

 64Cyber Crime
64Cyber CrimeeBay scams – site says ‘no plans’ to ban ‘active’ listings
Auction site eBay has remained defiant about ‘active’ listings ,containing computer code, despite multiple reports indicating that these are being used for...
-

 66Cyber Crime
66Cyber CrimeDestiny game servers under attack
The hit shoot ‘em up Destiny has been targeted by a cybercriminal gang thought to be behind recent attacks on game companies...
-

 157How To
157How ToHow The Pirate Bay Remains Untouchable
The Pirate Bay still remains the world’s largest torrent site which handles requests from millions of users every single day and is...
-
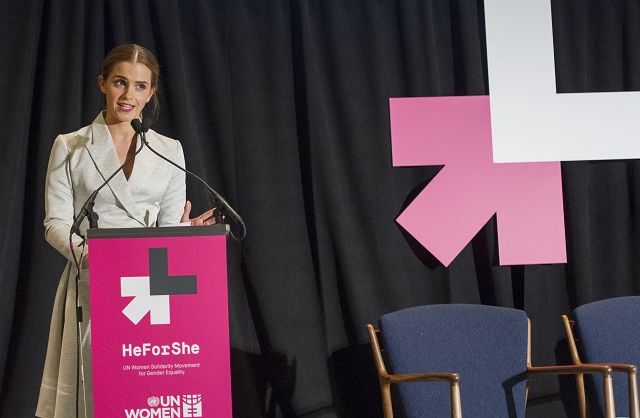
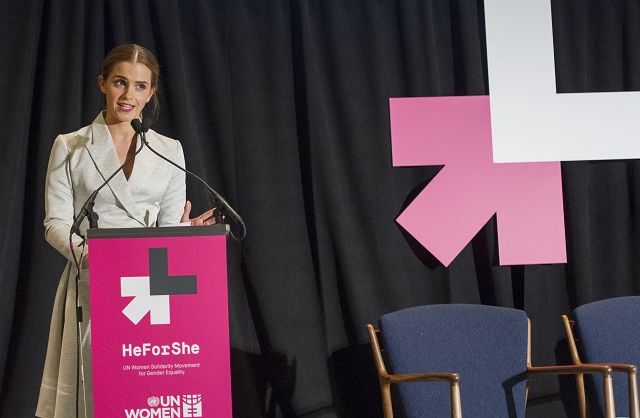 141Cyber Crime
141Cyber CrimeEmma Watson images – ‘countdown’ to leak after UN speech
In what appears to be a misogynist attack directed at Harry Potter actress Emma Watson, a site has appeared supposedly offering a...
-

 91Privacy
91PrivacyFacial recognition – boom in sites such as dating services
Facial recognition is booming, with the market expected to grow from $1.92 billion to $6.5 billion in 2018 - and invading markets...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




