Featured News
-

 81Privacy
81PrivacySurveillance fears over systems which ‘follow’ cellphone users
Concern is growing over the export of surveillance equipment which can track the movements of anyone carrying a cellphone. Such technnologies are...
-

 152News
152NewsGoogle Image Search Hacked? Search results filled with Russian car crash images
Users witness looking at pictures of Russian car crash regardless of what they searched on Google Images. If someone searched for ‘cat’ the search result...
-

 63Cyber Crime
63Cyber CrimeOnline fraud – POS malware has now hit 1,000 U.S. firms
More than a thousand U.S. businesses have been affected by point-of-sale malware - malicious software written specifically for online fraud, to steal...
-

 80Cyber Crime
80Cyber CrimeGoogle Images hacked? Searches fill with morbid image
An image of a Russian car crash has piled up in Google Images - leading to speculation that the service has been...
-

 232Lists
232Lists2014 Emmy Award Winners : Breaking Bad Wins Big, Game of Thrones Scores Zero
2014 Emmy Awards were pretty much unsurprising and a lot of fan favorites won. NBC drama Breaking Bad won the Emmy Award for...
-

 191Cyber Crime
191Cyber CrimePSN hacked – Network back after cyber attack and bomb threat
Sony’s PlayStation Network was back online and the information of its 53 million users safe, despite a weekend-long cyber attack, and a...
-

 383Cyber Crime
383Cyber CrimeBitcoin wallet phishing scores unlikely hit with crypto‑curious
A new tactic where waves of Bitcoin wallet phishing emails are targeted at corporations has proved a success for the criminals behind...
-

 395How To
395How ToHow to Download Only Audio from a Youtube Video?
There would have been many times when you wanted to download just the audio of a YouTube video, but not finding any...
-

 91How To
91How ToHow to protect your identity at school
Young people are targeted for data theft at 35 times the rate of adults – they are considered an easy target for...
-

 388Cyber Crime
388Cyber CrimeWeek in security: Nuclear attack, scareware back and traffic‑light hack
This week saw two of the scariest targets for hacks ever - nuclear plants and city-wide traffic systems. Tthe traffic-light hack could...
-
 173How To
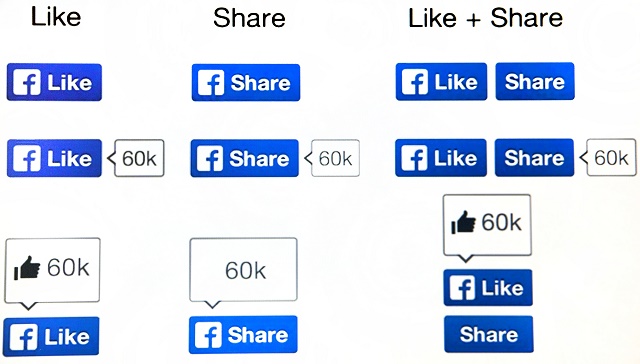
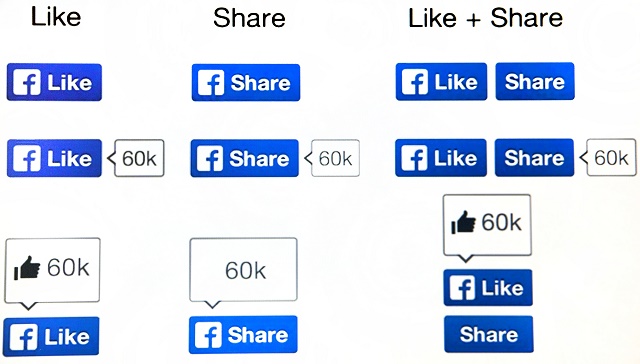
173How ToFacebook scams – the ‘classics’ and how to avoid them
But some things on Facebook haven’t changed - namely, the scams. It’s not that cybercriminals are unoriginal - it’s just that there...
-
News
Researchers show how to hack Gmail with 92% success rate
Security researchers from University of Michigan and the University of California Riverside Bourns College of Engineering have found out a security flaw...
-
 192How To
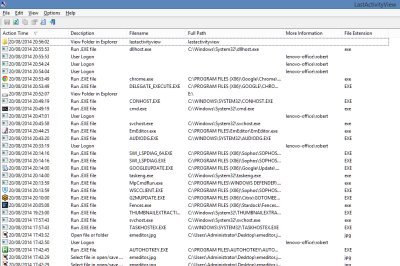
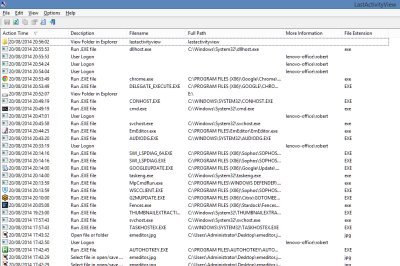
192How ToFree Software to Monitor Your PC’s Activity
If you ever get asked to fix the PC of a friend or colleague which has been having problems, the first thing...
-

 83Malware
83MalwareScareware: It’s back, and now it’s even scarier
‘Scareware’ - fake antivirus programs which attempt to fool the user into downloading malware, by warning him or her of a “threat”...
-

 73Cyber Crime
73Cyber CrimeFlight MH370 – did cyber attack steal its secret?
Classified documents relating to the missing Malaysian Airlines Flight MH370 were stolen using a carefully-crafted spear-phishing attack, targeting 30 government officials just...
-
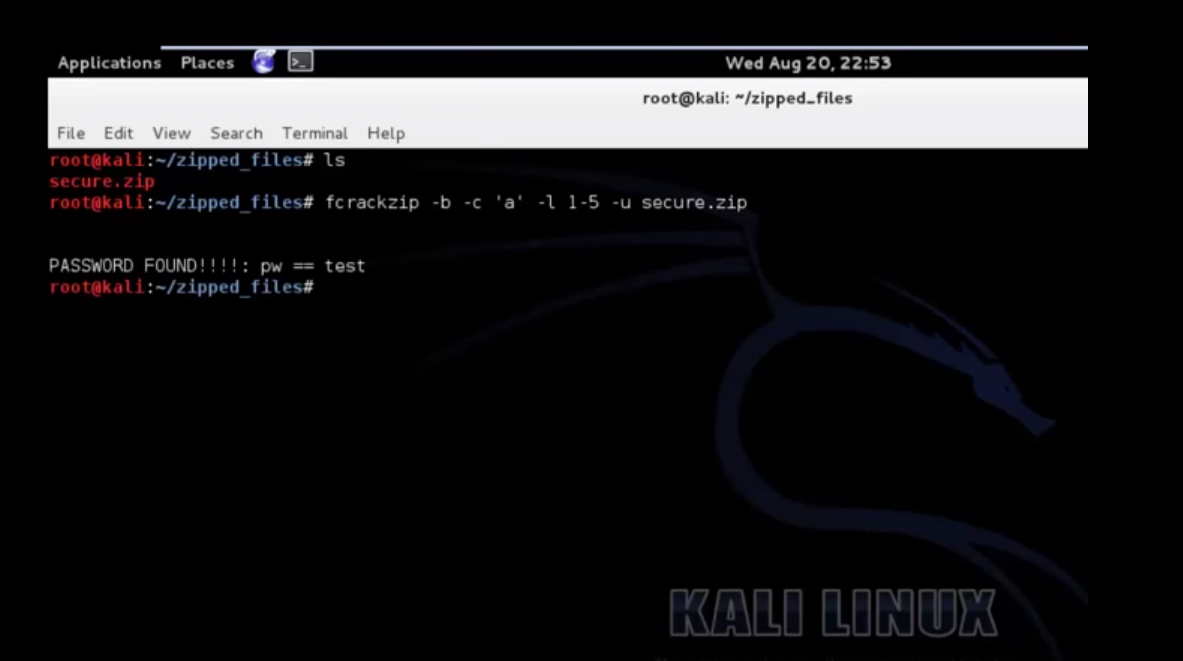
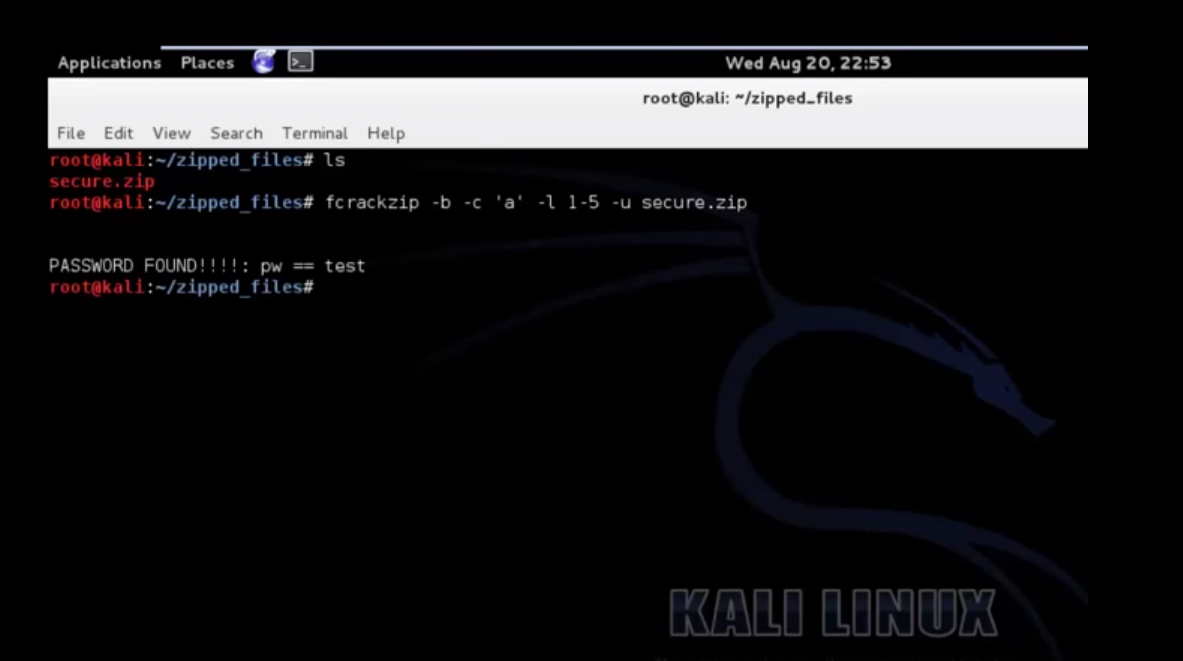 200How To
200How ToCrack A Password Protected Zip File Using Kali
Also Read: Download Kali 2.0 Now
-

 83Cyber Crime
83Cyber CrimeTraffic light – ‘easy’ to hack whole city’s systems
The most famous traffic light ‘hack’ in history is in the classic film, The Italian Job (1969), where the heist involves paralyzing...
-

 89Password
89PasswordPIN number: Police want codes on ALL devices
Police hope to work with leading mobile phone manufacturers such as Samsung to build in the requirement for a password or PIN...
-

 86Password
86PasswordBanking security – new apps ‘know’ your touch
Everyone hates passwords - even the guy who invented them - but some bank app users in the Nordic region are experiencing...
-

 231Lists
231ListsTop 5 Torrent sites of 2014
In the world of torrent downloading, you must understand one thing that there always will be more “Leechers” than “Seeders”. Telling about...
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




