Search results for "hack"
-

 2.5KMalware
2.5KMalwareRussian Hacker Vladimir Dunaev Convicted for Creating TrickBot Malware
A Russian national has been found guilty in connection with his role in developing and deploying a malware known as TrickBot, the...
-

 2.2KMalware
2.2KMalwareChinese Hackers Using SugarGh0st RAT to Target South Korea and Uzbekistan
A suspected Chinese-speaking threat actor has been attributed to a malicious campaign that targets the Uzbekistan Ministry of Foreign Affairs and South...
-

 1.9KMalware
1.9KMalwareNorth Korea’s Lazarus Group Rakes in $3 Billion from Cryptocurrency Hacks
Threat actors from the Democratic People’s Republic of Korea (DPRK) are increasingly targeting the cryptocurrency sector as a major revenue generation mechanism...
-

 4.8KCyber Attack
4.8KCyber AttackIranian Hackers Exploit PLCs in Attack on Water Authority in U.S.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) revealed that it’s responding to a cyber attack that involved the active exploitation of...
-
 2.7KData Breach
2.7KData BreachHow Hackers Phish for Your Users’ Credentials and Sell Them
Account credentials, a popular initial access vector, have become a valuable commodity in cybercrime. As a result, a single set of stolen...
-

 740Vulnerabilities
740VulnerabilitiesHackers Can Exploit ‘Forced Authentication’ to Steal Windows NTLM Tokens
Cybersecurity researchers have discovered a case of “forced authentication” that could be exploited to leak a Windows user’s NT LAN Manager (NTLM)...
-

 4.3KVulnerabilities
4.3KVulnerabilitiesN. Korean Hackers Distribute Trojanized CyberLink Software in Supply Chain Attack
A North Korean state-sponsored threat actor tracked as Diamond Sleet is distributing a trojanized version of a legitimate application developed by a...
-
 4.9KMalware
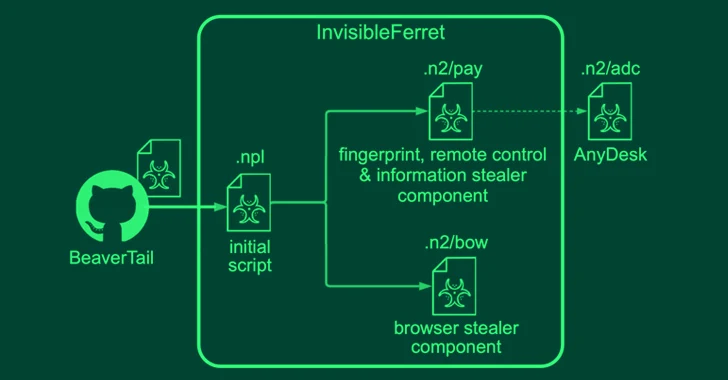
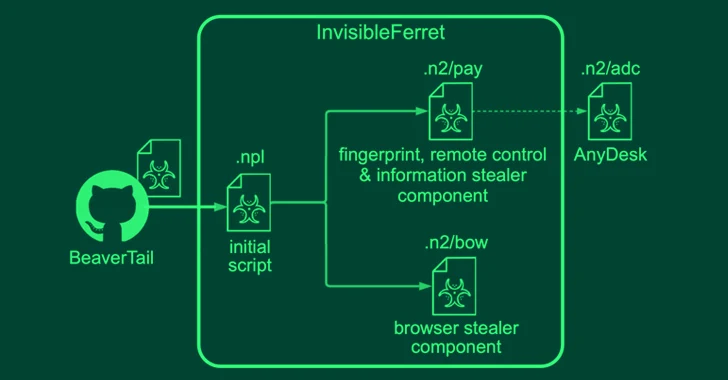
4.9KMalwareNorth Korean Hackers Pose as Job Recruiters and Seekers in Malware Campaigns
North Korean threat actors have been linked to two campaigns in which they masquerade as both job recruiters and seekers to distribute...
-
 1.4KVulnerabilities
1.4KVulnerabilitiesKinsing Hackers Exploit Apache ActiveMQ Vulnerability to Deploy Linux Rootkits
The Kinsing threat actors are actively exploiting a critical security flaw in vulnerable Apache ActiveMQ servers to infect Linux systems with cryptocurrency...
-

 2.0KCyber Attack
2.0KCyber AttackMustang Panda Hackers Targets Philippines Government Amid South China Sea Tensions
The China-linked Mustang Panda actor has been linked to a cyber attack targeting a Philippines government entity amid rising tensions between the...
-

 900Data Breach
900Data BreachWhy Defenders Should Embrace a Hacker Mindset
Today’s security leaders must manage a constantly evolving attack surface and a dynamic threat environment due to interconnected devices, cloud services, IoT...
-

 4.5KVulnerabilities
4.5KVulnerabilitiesZero-Day Flaw in Zimbra Email Software Exploited by Four Hacker Groups
A zero-day flaw in the Zimbra Collaboration email software was exploited by four different groups in real-world attacks to pilfer email data,...
-

 3.6KVulnerabilities
3.6KVulnerabilitiesRussian Hackers Linked to ‘Largest Ever Cyber Attack’ on Danish Critical Infrastructure
Russian threat actors have been possibly linked to what’s been described as the “largest cyber attack against Danish critical infrastructure,” in which...
-

 1.7KData Security
1.7KData SecurityYour Google Cloud Security Might Be at Risk. Hacking GCP via Google Workspace flaw
In a startling revelation, Bitdefender, a leading cybersecurity firm, has disclosed a series of sophisticated attack methods that could significantly impact users...
-
 212Data Security
212Data SecurityAzure CLI stores credentials in plaintext in logs. A easy technique to hack cloud environments
CVE-2023-36052 is a critical security vulnerability in the Azure Command-Line Interface (CLI), a tool for managing Azure resources. This vulnerability, reported by...
-

 3.0KMalware
3.0KMalwareVietnamese Hackers Using New Delphi-Powered Malware to Target Indian Marketers
The Vietnamese threat actors behind the Ducktail stealer malware have been linked to a new campaign that ran between March and early...
-

 4.1KVulnerabilities
4.1KVulnerabilitiesChinese Hackers Launch Covert Espionage Attacks on 24 Cambodian Organizations
Cybersecurity researchers have discovered what they say is malicious cyber activity orchestrated by two prominent Chinese nation-state hacking groups targeting 24 Cambodian...
-

 399Data Security
399Data SecurityHow Living-off-the-land (LotL) technique is used to hack into power grids & cause power outages
Living-off-the-land (LotL) techniques in cyber attacks refer to the use of legitimate, native tools already present in the target system to carry...
-

 3.4KMalware
3.4KMalwareRussian Hackers Sandworm Cause Power Outage in Ukraine Amidst Missile Strikes
The notorious Russian hackers known as Sandworm targeted an electrical substation in Ukraine last year, causing a brief power outage in October...
-

 4.7KCyber Attack
4.7KCyber AttackMuddyC2Go: New C2 Framework Iranian Hackers Using Against Israel
Iranian nation-state actors have been observed using a previously undocumented command-and-control (C2) framework called MuddyC2Go as part of attacks targeting Israel. “The...
-

 4.5KData Security
4.5KData SecurityHackers’ new favorite: CVE-2023-4911 targeting Debian, Ubuntu and Fedrora servers in the Cloud
CVE-2023-4911 is a serious security vulnerability within the GNU C Library (glibc), specifically in the dynamic loader ld.so, associated with the processing...






