Search results for "hack"
-
 2.0KData Security
2.0KData SecurityXXXGPT and WolfGPT new ChatGPT like tools used by hackers
Since threat actors aggressively exploit AI technology for a variety of illegal objectives, the whole danger landscape is undergoing a profound transformation as...
-

 4.9KMalware
4.9KMalwareIranian Company Cloudzy Accused of Aiding Cybercriminals and Nation-State Hackers
Services offered by an obscure Iranian company known as Cloudzy are being leveraged by multiple threat actors, including cybercrime groups and nation-state...
-

 4.9KVulnerabilities
4.9KVulnerabilitiesHow to easily hack TP-Link Archer AX21 Wi-Fi router
TP-Link has released a fix for a severe vulnerability in its Archer AX21 router. This vulnerability might have allowed attackers to take...
-

 5.1KIncidents
5.1KIncidentsMattress Company Sealy shuts down IT systems and production plant after a big hack
Because to a “cybersecurity event” that occurred on July 23, Tempur Sealy International was forced to shut down some of its information...
-

 699Vulnerabilities
699VulnerabilitiesHacking WordPress websites via vulnerabilities in Ninja Forms plugin
It has come to light that the Ninja Forms plugin for WordPress has many security flaws that might be abused by malicious...
-

 4.7KCyber Attack
4.7KCyber AttackPatchwork Hackers Target Chinese Research Organizations Using EyeShell Backdoor
Threat actors associated with the hacking crew known as Patchwork have been spotted targeting universities and research organizations in China as part...
-
 489Vulnerabilities
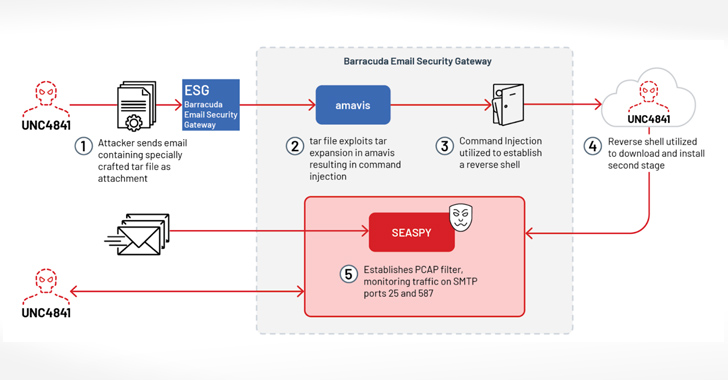
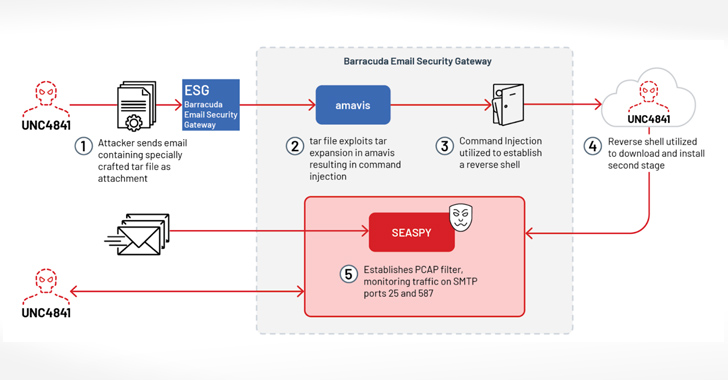
489VulnerabilitiesHackers Deploy “SUBMARINE” Backdoor in Barracuda Email Security Gateway Attacks
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday disclosed details of a “novel persistent backdoor” called SUBMARINE deployed by threat...
-
 4.5KData Security
4.5KData SecurityNew attack technique to hack Apache Tomcat Servers
This “pure Java” HTTP web server environment is provided by Apache Tomcat, which is a server that is both open-source and free...
-

 4.7KMalware
4.7KMalwareHacker Using Google and Bing ads to Deliver Weaponized IT tools
The latest research discovered malvertising campaigns abusing Google and Bing ads to target users seeking certain IT tools and deploying ransomware. This...
-

 483Data Security
483Data SecurityKenya to only grant visas on arrival after online visa system hacked
Following the failure of an online application platform that made the majority of government services unavailable, Kenya said on Thursday that it...
-
 1.2KData Security
1.2KData SecurityVersions of Ubuntu prior to 23.04 can be hacked thanks to these 2 severe security flaws
Two vulnerabilities in the Linux operating system Ubuntu have been found by researchers. Both of these vulnerabilities have the ability to offer...
-
 1.4KMalware
1.4KMalwareHackers Target Apache Tomcat Servers for Mirai Botnet and Crypto Mining
Misconfigured and poorly secured Apache Tomcat servers are being targeted as part of a new campaign designed to deliver the Mirai botnet...
-

 2.5KData Security
2.5KData SecurityUS hacked into Chinese earthquake monitoring systems to spy upon underground military bases
A recent cyberattack on the Wuhan Earthquake Monitoring Center was carried out by an entity located outside of China, according to a...
-

 1.1KVulnerabilities
1.1KVulnerabilitiesCritical MikroTik RouterOS Vulnerability Exposes Over Half a Million Devices to Hacking
A severe privilege escalation issue impacting MikroTik RouterOS could be weaponized by remote malicious actors to execute arbitrary code and seize full...
-

 404Data Security
404Data SecurityHacking Encrypted Police and Military Radios exploiting 5 vulnerabilities
Global radios depend on the TETRA (Terrestrial Trunked Radio) standard, however a number of vulnerabilities have been found that have an influence...
-
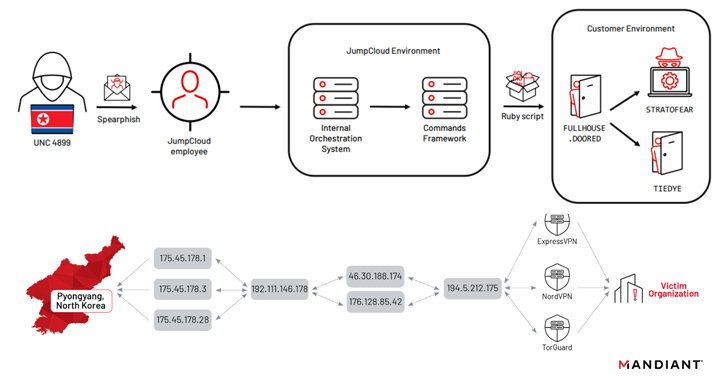
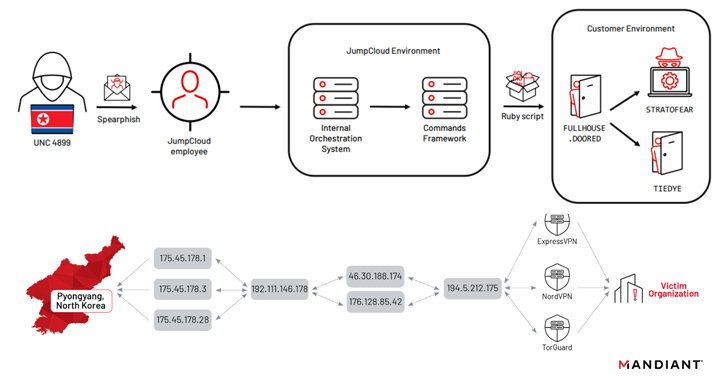 2.6KCyber Attack
2.6KCyber AttackNorth Korean Nation-State Actors Exposed in JumpCloud Hack After OPSEC Blunder
North Korean nation-state actors affiliated with the Reconnaissance General Bureau (RGB) have been attributed to the JumpCloud hack following an operational security...
-

 959Vulnerabilities
959VulnerabilitiesTwo serious zero-day vulnerabilities allow hacking iPhone, iPad and Mac
Recent news reports have brought attention to two serious zero-day vulnerabilities that pose a risk to the digital security of Apple products...
-

 4.8KData Security
4.8KData SecurityClop ransomware hacked DHL, summing up 20 million victims & profit of $100 million via MOVEit
It is thought that tens of thousands, if not hundreds of thousands, of employees were impacted by a cyberattack that took place...
-

 2.0KMalware
2.0KMalwareHackers Deliver HotRat as Hidden Scripts in cracked software
The use of illegal software has been under circulation ever since there have been torrents and cracked software. Recent reports show that...
-

 3.3KMalware
3.3KMalwareFIN8 Revamped Hacking Toolkit with New Stealthy Attack Features
Syssphinx (aka FIN8) is a financially motivated cyber-crime group deploying revamped sardonic backdoor to deliver Noberus ransomware. This group has been active since...
-

 926Data Security
926Data SecurityTop 5 free cloud security tools, that can protect your AWS & Azure cloud data from hackers
The Cybersecurity and Infrastructure Security Agency (CISA) has come up with a list of free tools that businesses may use to protect...






