Search results for "DoS"
-

 2.4KIncidents
2.4KIncidentsFortnite online servers worldwide under DDoS attack
Increasingly, cybersecurity incidents are affecting thousands, or even millions, of members of the gamer community. According to experts in ethical hacking, this...
-

 872Cyber Events
872Cyber EventsAWS hit by massive DDoS attacks that lasted 8 hours
Under “usual circumstances,” AWS makes headlines for exposing databases of companies using its services. A few days ago (Oct 22, 2019), the...
-

 2.6KIncidents
2.6KIncidentsAmazon Web Services servers and customers affected by a massive DDOS attack for hours
According to digital forensics specialists, Amazon Web Services (AWS), the technology giant’s cloud computing services division, has been the victim of a...
-

 3.3KData Security
3.3KData SecurityMillions of websites using CDNs at risk of CPDoS attack
CPDoS can be used to attack content delivery networks (CDNs) to serve error pages instead of legitimate sites through caching. Freshly termed...
-

 455Vulnerabilities
455Vulnerabilities18 Vulnerabilities that Affected Cisco Software’s Let Hackers Perform DOS, RCE to Gain Unauthorized System Access
Cisco released new security updates for multiple software products such as Cisco ASA, FMC, and FTD Software that affects 18 vulnerabilities in...
-
 470Mobile Security
470Mobile Security9 Android Zero-day Vulnerabilities Affects Billions of Android Devices – Hackers Perform DOS, RCE, Make, Deny & Spoof Calls
Exclusive research found 9 critical system-level Android VoIP Zero-day vulnerabilities that allow attackers to perform malicious operations, including denying voice calls, caller...
-
 563DDOS
563DDOSHow to Find out if you are under a DDoS Attack?
Cyberattacks have always surprised security experts because they are sneaky and come in different forms. Distributed Denial of Service is a process...
-

 467Vulnerabilities
467VulnerabilitiesAlmost every Cisco device is vulnerable to DoS attacks; fix now using this patch
It seems that companies will never stop being inconvenienced by some security flaws. Vulnerability testing experts report that Cisco has extended the...
-
 338Incidents
338IncidentsWikipedia is under a massive DDoS attack. Who’s behind the attack?
According to ethical hacking specialists, over the past weekend multiple Wikipedia sites for some regions of Europe and the Middle East experienced...
-
 659DDOS
659DDOSWikipedia Hacked – Hackers Take Down the Website with Massive DDOS Attack
Wikipedia Hacked: cybercriminals have launched a massive DDOS attack on Wikipedia and take down the website in several countries in Europe and parts...
-
 2.1KData Security
2.1KData SecurityWikipedia suffers DDoS attack causing worldwide service disruption
The DDoS attack on Wikipedia is first of its kind. The popular online encyclopedia Wikipedia has suffered a DDoS attack over the...
-

 514Cyber Events
514Cyber EventsWebsite used by Hong Kong protesters suffers DDoS attack
The prime suspect of the DDoS attack is China. An online forum used by activists behind the ongoing Hong Kong protests has...
-
 542Malware
542MalwareMultistage Attack Delivers BillGates/Setag Backdoor to Turn Elasticsearch Servers into DDoS Botnet
A new multistage attack exploiting Elasticsearch servers using the old unpatched vulnerability to invoke a shell with a crafted query and encoded...
-
 404DDOS
404DDOSMassive DDoS Attack on Streaming Service with 292,000 RPS (Requests Per Second) From 402,000 Different Botnet IP’s
An unrevealed streaming site hit with massive DDoS attack from 402,000 different IoT(Internet of Things) Botnet IPs, which directed a peak flow...
-
 411Data Security
411Data SecurityNew malware attack turns Elasticsearch databases into DDoS botnet
The malware attack involves two stages including one in which existing cryptomining malware is removed. The IT security researchers at Trend Micro...
-
 346Denial of service
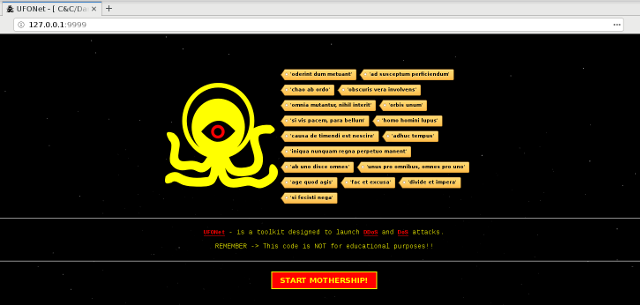
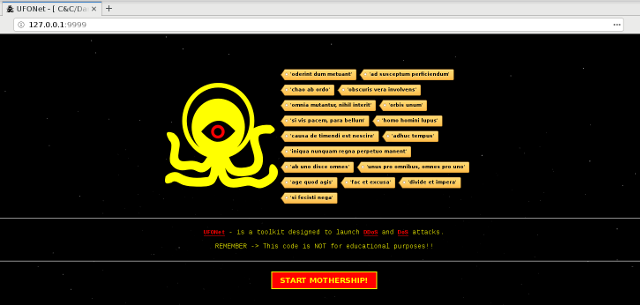
346Denial of serviceUFONet – Toolkit Designed to launch DDoS and DoS attacks.
UFONet is a tool designed to launch Layer 7 (HTTP/Web Abuse) DDoS attacks, using ‘Open Redirect’ vectors, generally located on third part-y...
-

 386Malware
386MalwareNew Miori Malware Uses Text-based Protocol to Communicate with C&C Server for Launching a DDoS Attack
A new Mirai variant dubbed Miori uses text-based protocols to establish communication with command-and-control (C&C) servers. The Miori campaign was identified in...
-

 374Cyber Crime
374Cyber CrimeMan who carried out DDoS attacks against PSN & Xbox jailed
The cybercriminal was also involved in several other cybercrimes including swatting and deleting databases of targeted websites. Austin Thompson, a DDoS attacker...
-

 295News
295NewsTor Project Is Finally Fixing A DDoS Vulnerability In Onion Sites After Years
The Tor Project is finally going to release a fix for a bug that has been plaguing Onion sites for years, making...
-
 347Incidents
347IncidentsThis guy launched DDoS attacks against video game companies like PlayStation Xbox, etc.
This week, Austin Thompson, a 23-year-old from Utah, US, was sentenced to two years and three months in prison after being charged...
-

 330News
330NewsMan Gets Prison For DDoSing Steam, EA, Microsoft, Sony, Nintendo, DOTA2, Riot Games….
In one of its kind acts, a Utah-based man named Austin Thompson (23) is going to prison for launching DDoS attacks on...






