Featured News
-

 1.8KMalware
1.8KMalwarePyPI Halts Sign-Ups Amid Surge of Malicious Package Uploads Targeting Developers
The maintainers of the Python Package Index (PyPI) repository briefly suspended new user sign-ups following an influx of malicious projects uploaded as...
-

 2.2KVulnerabilities
2.2KVulnerabilitiesLinux Version of DinodasRAT Spotted in Cyber Attacks Across Several Countries
A Linux version of a multi-platform backdoor called DinodasRAT has been detected in the wild targeting China, Taiwan, Turkey, and Uzbekistan, new...
-

 1.7KMalware
1.7KMalwareFinland Blames Chinese Hacking Group APT31 for Parliament Cyber Attack
The Police of Finland (aka Poliisi) has formally accused a Chinese nation-state actor tracked as APT31 for orchestrating a cyber attack targeting...
-

 1.2KVulnerabilities
1.2KVulnerabilitiesNew ZenHammer Attack Bypasses RowHammer Defenses on AMD CPUs
Cybersecurity researchers from ETH Zurich have developed a new variant of the RowHammer DRAM (dynamic random-access memory) attack that, for the first...
-

 3.4KMalware
3.4KMalwareNew Webinar: Avoiding Application Security Blind Spots with OPSWAT and F5
Considering the ever-changing state of cybersecurity, it’s never too late to ask yourself, “am I doing what’s necessary to keep my organization’s...
-

 3.0KVulnerabilities
3.0KVulnerabilitiesBehind the Scenes: The Art of Safeguarding Non-Human Identities
In the whirlwind of modern software development, teams race against time, constantly pushing the boundaries of innovation and efficiency. This relentless pace...
-

 4.1KMalware
4.1KMalwareHackers Hit Indian Defense, Energy Sectors with Malware Posing as Air Force Invite
Indian government entities and energy companies have been targeted by unknown threat actors with an aim to deliver a modified version of...
-
 2.7KVulnerabilities
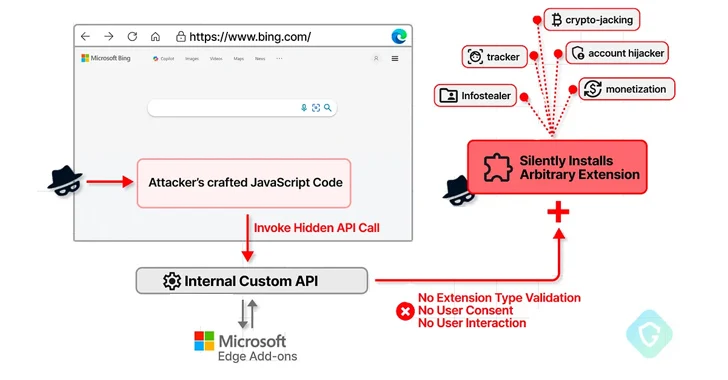
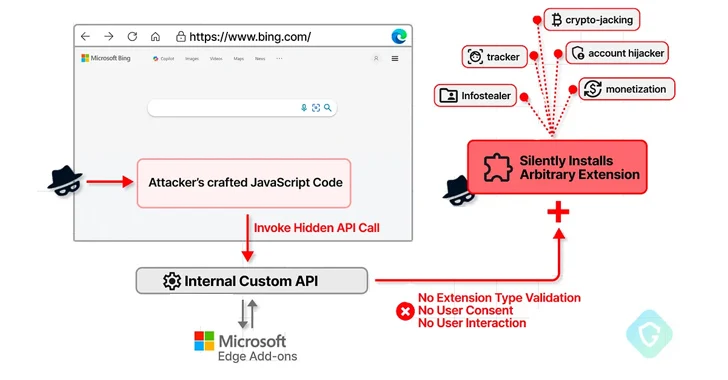
2.7KVulnerabilitiesMicrosoft Edge Bug Could Have Allowed Attackers to Silently Install Malicious Extensions
A now-patched security flaw in the Microsoft Edge web browser could have been abused to install arbitrary extensions on users’ systems and...
-
 4.6KVulnerabilities
4.6KVulnerabilitiesSASE Solutions Fall Short Without Enterprise Browser Extensions, New Report Reveals
As SaaS applications dominate the business landscape, organizations need optimized network speed and robust security measures. Many of them have been turning...
-

 2.0KVulnerabilities
2.0KVulnerabilitiesCritical Unpatched Ray AI Platform Vulnerability Exploited for Cryptocurrency Mining
Cybersecurity researchers are warning that threat actors are actively exploiting a “disputed” and unpatched vulnerability in an open-source artificial intelligence (AI) platform...
-
 329Vulnerabilities
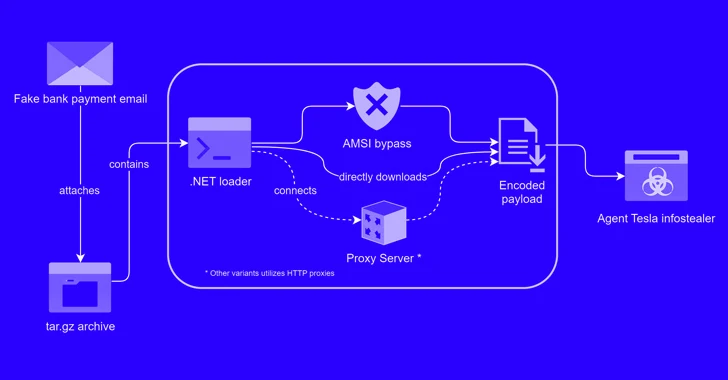
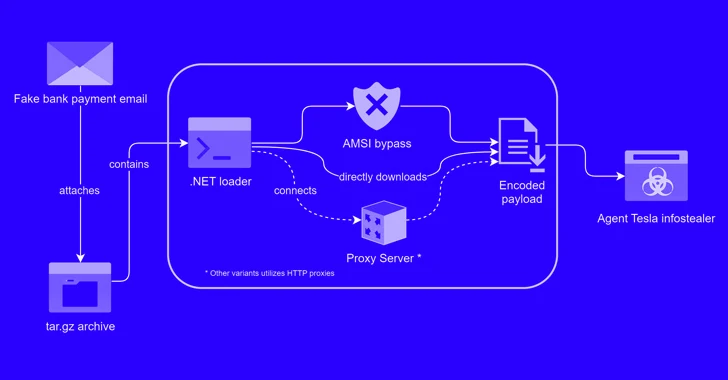
329VulnerabilitiesAlert: New Phishing Attack Delivers Keylogger Disguised as Bank Payment Notice
A new phishing campaign has been observed leveraging a novel loader malware to deliver an information stealer and keylogger called Agent Tesla....
-

 2.2KVulnerabilities
2.2KVulnerabilitiesTwo Chinese APT Groups Ramp Up Cyber Espionage Against ASEAN Countries
Two China-linked advanced persistent threat (APT) groups have been observed targeting entities and member countries affiliated with the Association of Southeast Asian...
-
 4.5KData Security
4.5KData SecuritySocial Media Conspiracy Theory: Was the Baltimore Bridge Collision a Result of Cyber Attack?
On an unexpected Tuesday, the collision of a container ship with the Francis Scott Key Bridge in Baltimore not only disrupted the...
-

 2.3KMalware
2.3KMalwareSketchy NuGet Package Likely Linked to Industrial Espionage Targets Developers
Threat hunters have identified a suspicious package in the NuGet package manager that’s likely designed to target developers working with tools made...
-

 1.2KMalware
1.2KMalwareU.S. Charges 7 Chinese Nationals in Major 14-Year Cyber Espionage Operation
The U.S. Department of Justice (DoJ) on Monday unsealed indictments against seven Chinese nationals for their involvement in a hacking group that...
-
 3.2KVulnerabilities
3.2KVulnerabilitiesCISA Alerts on Active Exploitation of Flaws in Fortinet, Ivanti, and Nice Products
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday placed three security flaws to its Known Exploited Vulnerabilities (KEV) catalog, citing...
-

 2.6KMalware
2.6KMalwareMajor Python Infrastructure Breach – Over 170K Users Compromised. How Safe Is Your Code?
The Checkmarx Research team has unearthed a sophisticated attack campaign that leveraged fake Python infrastructure to target the software supply chain, affecting...
-

 4.2KData Breach
4.2KData BreachKey Lesson from Microsoft’s Password Spray Hack: Secure Every Account
In January 2024, Microsoft discovered they’d been the victim of a hack orchestrated by Russian-state hackers Midnight Blizzard (sometimes known as Nobelium)....
-

 4.4KVulnerabilities
4.4KVulnerabilitiesNew “GoFetch” Vulnerability in Apple M-Series Chips Leaks Secret Encryption Keys
A new security shortcoming discovered in Apple M-series chips could be exploited to extract secret keys used during cryptographic operations. Dubbed GoFetch,...
-
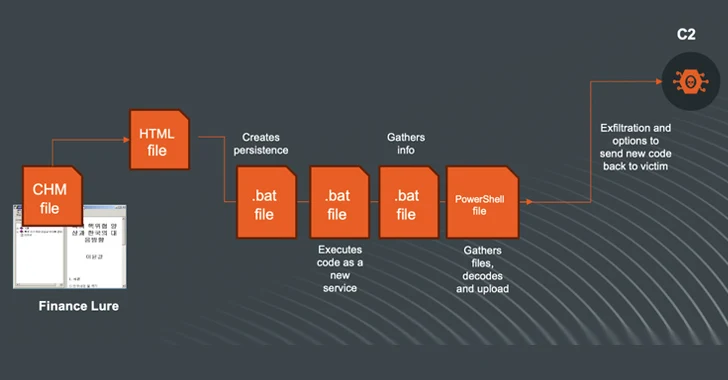
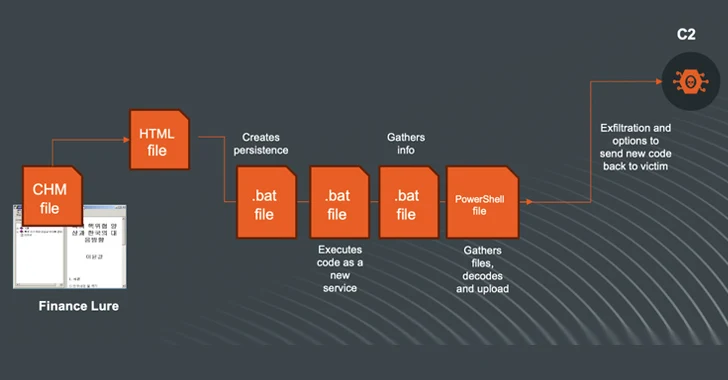 1.7KMalware
1.7KMalwareN. Korea-linked Kimsuky Shifts to Compiled HTML Help Files in Ongoing Cyberattacks
The North Korea-linked threat actor known as Kimsuky (aka Black Banshee, Emerald Sleet, or Springtail) has been observed shifting its tactics, leveraging...
The Latest
-
 Data Breach
Data BreachFBI Seizes BreachForums Again, Urges Users to Report Criminal Activity
-
 Cyber Attack
Cyber AttackMicrosoft Patches 61 Flaws, Including Two Actively Exploited Zero-Days
-
 Cyber Attack
Cyber AttackThe 2024 Browser Security Report Uncovers How Every Web Session Could be a Security Minefield
-
 Vulnerabilities
VulnerabilitiesSevere Vulnerabilities in Cinterion Cellular Modems Pose Risks to Various Industries
-
 Data Breach
Data BreachBlack Basta Ransomware Strikes 500+ Entities Across North America, Europe, and Australia
-
 Malware
MalwareMalicious Python Package Hides Sliver C2 Framework in Fake Requests Library Logo
-
 Malware
MalwareFIN7 Hacker Group Leverages Malicious Google Ads to Deliver NetSupport RAT
-
 Malware
MalwareNorth Korean Hackers Deploy New Golang Malware ‘Durian’ Against Crypto Firms
-
 Vulnerabilities
VulnerabilitiesChrome Zero-Day Alert — Update Your Browser to Patch New Vulnerability
-
 Malware
MalwareMalicious Android Apps Pose as Google, Instagram, WhatsApp to Steal Credentials
-
 Cyber Attack
Cyber AttackKremlin-Backed APT28 Targets Polish Institutions in Large-Scale Malware Campaign
-
 Vulnerabilities
VulnerabilitiesMirai Botnet Exploits Ivanti Connect Secure Flaws for Malicious Payload Delivery
-
 Data Breach
Data BreachA SaaS Security Challenge: Getting Permissions All in One Place
-
 Vulnerabilities
VulnerabilitiesThe Fundamentals of Cloud Security Stress Testing
-
 Malware
MalwareHijack Loader Malware Employs Process Hollowing, UAC Bypass in Latest Version
-
 Vulnerabilities
VulnerabilitiesHackers Exploiting LiteSpeed Cache Bug to Gain Full Control of WordPress Sites
-
 Malware
MalwareRussian Hacker Dmitry Khoroshev Unmasked as LockBit Ransomware Administrator
-
 Malware
MalwareAPT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
-
 Vulnerabilities
VulnerabilitiesChina-Linked Hackers Used ROOTROT Webshell in MITRE Network Intrusion
-
 Data Breach
Data BreachNew Case Study: The Malicious Comment




