Search results for "Backdoor"
-

 105Data Security
105Data SecurityIBM Researchers Hack Into A Smart Building To Highlight The Backdoors Created For Hackers
This smart building was hacked by IBM researchers to show hacking risks associated with Internet of Things. IBM security researchers are warning...
-
 118Malware
118MalwareRent the infamous AlienSpy backdoor is now quite easy
Security experts at Kaspersky have spotted in the wild a new variant of AlienSpy RAT Family openly offered with a model of...
-

 95Malware
95MalwareT9000 Backdoor Malware Targets Skype Users, Records Conversations
T9000 can also steal files from your hard drives. A new backdoor trojan is making the rounds, coming equipped with features that allow...
-

 105Data Security
105Data SecurityPossible Encryption Backdoor Discovered in Socat Networking Utility
Backdoor code was committed by a former Oracle employee. Developers of Socat, a *NIX-based networking utility, have discovered and patched a security bug...
-

 239Data Security
239Data SecurityFrom Linux to Windows – New Family of Cross-Platform Desktop Backdoors Discovered
Recently we came across a new family of cross-platform backdoors for desktop environments. First we got the Linux variant, and with information...
-
 183Data Security
183Data SecurityCertain MediaTek phones contain a dangerous debug backdoor
MediaTek may not be on the short list of SoC companies whose chips you seek out when buying a new phone, but...
-

 135Data Security
135Data SecuritySimple Yet Efficient Linux Backdoor Trojan Discovered
Linux. BackDoor.Xunpes trojan lets cyber-crooks take control and execute commands on your Linux machine. Threats to Linux computers are now appearing on a...
-
 252Data Security
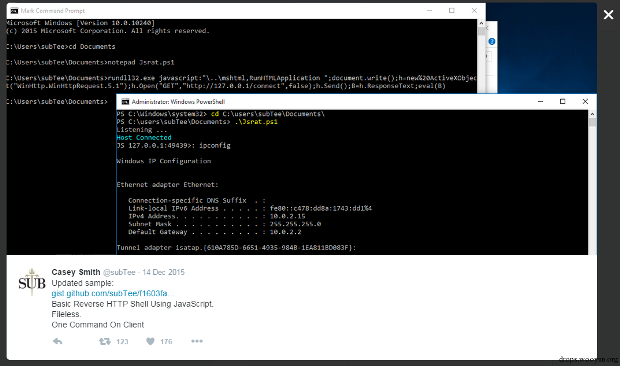
252Data SecurityJavaScript Backdoor
Casey Smith recently shared his research on twitter, which is to reverse HTTP Shell by using JavaScript. I found it rather interesting...
-

 201Incidents
201IncidentsChinese Group Trying to Exploit Old Fortinet SSH Backdoor
Scans for Fortinet devices have intensified. An unknown group has been scanning the Internet for old Fortinet equipment that includes a secret SSH...
-
 164Incidents
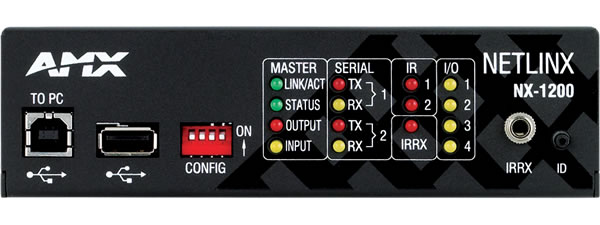
164IncidentsMedia devices sold to feds have hidden backdoor with sniffing functions
Highly privileged account could be used to hack customers’ networks, researchers warn. A company that supplies audio-visual and building control equipment to...
-

 195Data Security
195Data SecurityBritish Government Has Already Created a Data Encryption Protocol Complete With a Backdoor
GCHQ insists on shooting itself in the foot with backdoored VoIP encryption protocol, developed in-house by CESG. Britain’s intelligence agency, GCHQ (Government...
-

 227Data Security
227Data SecurityHere’s how a cheap webcam can be converted into network backdoor
This is how a $30 D-Link webcam can be converted into a backdoor. Researchers at US security firm Vectra Networks have hacked a ‘tiny’...
-

 206Data Security
206Data SecurityNew York tries to force phone makers to put in crypto backdoors
The sport of holding Apple, Google and other tech companies over a barrel to demand backdoors now has a new player: New...
-

 113Incidents
113IncidentsCryptsy Bitcoin Trader Robbed, Blames Backdoor in the Code of a Wallet
The stolen Bitcoin & Litecoin were worth over $5.7 million. Cryptsy, a website for trading Bitcoin, Litecoin, and other smaller crypto-currencies, announced a...
-

 229Data Security
229Data SecuritySSH Backdoor Identified in Fortinet Firewalls
Fortinet’s FortiOS operating system, deployed on the company’s FortiGate firewall networking equipment includes an SSH backdoor on versions from the 4.x series...
-

 237Data Security
237Data SecurityJuniper drops NSA-developed code following new backdoor revelations
Researchers contradict Juniper claim that Dual_EC_DRBG weakness couldn’t be exploited. Juniper Networks, which last month made the startling announcement its NetScreen line...
-

 114Data Security
114Data SecurityFireEye Security Devices Provide Attackers with Backdoor into Corporate Networks
FireEye security equipment can be compromised, Google finds. Two security researchers working for Google have discovered a simple method of compromising FireEye security...
-

 195Data Security
195Data SecurityWhat the government should’ve learned about backdoors from the Clipper Chip
The Obama administration’s calls for backdoors echo the Clinton-era key escrow fiasco. In the face of a Federal Bureau of Investigation proposal...
-
 168Data Security
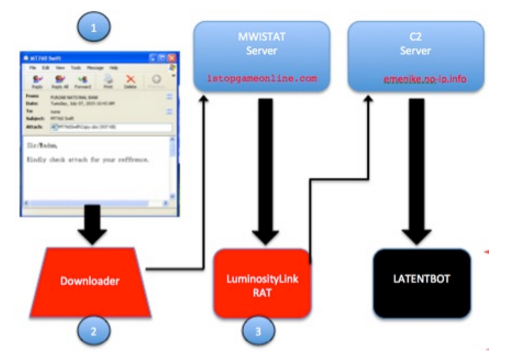
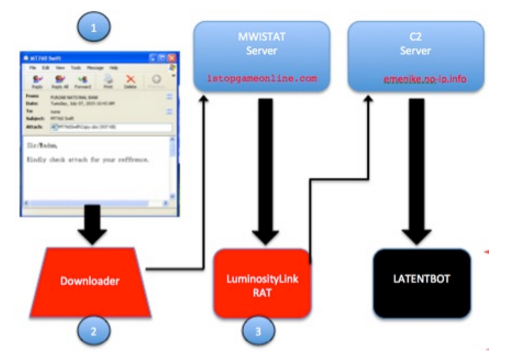
168Data SecurityLATENTBOT, one the highly obfuscated backdoor in the wild
Experts at FireEye have discovered a stealthy botnet relying on a backdoor called LATENTBOT has compromised companies around. Experts at FireEye have discovered...
-

 211Data Security
211Data SecurityAPT Group Upgrades Malware from the Black Market into Dangerous Backdoor
Cyber-espionage group targeted companies in Asia. Details about the operations of a new cyber-espionage group are emerging, and this gang has been buying...
-

 157Data Security
157Data SecurityFBI head: terror fight requires open backdoors to encrypted user data
FBI director James Comey called on tech companies to create backdoor access to their users’ data on Wednesday, arguing it was necessary...






