Search results for "Backdoor"
-
 190Hacked
190HackedAllwinner’s Linux Kernel Code Has An Easy-to-use Root Debug Backdoor
Short Bytes: The code of Linux kernel of Chinese chipmaker Allwinner contains an easily exploitable root backdoor. Combined with networked services, this could...
-

 148Data Security
148Data SecurityHey FBI, India can Hack iPhones but Doesn’t Want Backdoors
Maybe the FBI should team up with India because that country’s government says it can hack into Apple’s iPhones. Both think access...
-

 172Incidents
172IncidentsNew backdoor attacks Windows users
Backdoors are typically designed to execute cybercriminals’ commands on the infected machine. As a rule, they are used to gain a remote...
-

 219Backdoors
219BackdoorsSideDoor – Debian/Ubuntu Backdoor Using A Reverse SSH Tunnel
Sidedoor maintains a reverse tunnel to provide a backdoor. sidedoor can be used to remotely control a device behind a NAT. Sidedoor...
-

 114Data Security
114Data SecurityTUTO4PC UTILITIES SILENTLY INSTALL 12M BACKDOORS, CISCO
Security experts are warning PC users of scareware computer utilities published by the French firm Tuto4PC that secretly bundle adware and spyware....
-

 188Hacked
188HackedHow A Bug Hunter Hacked Facebook And Found Another Hacker’s Backdoor
Short Bytes: If you lead the life of a penetration tester or a bug hunter, your job offers you new challenges every...
-
 224Data Security
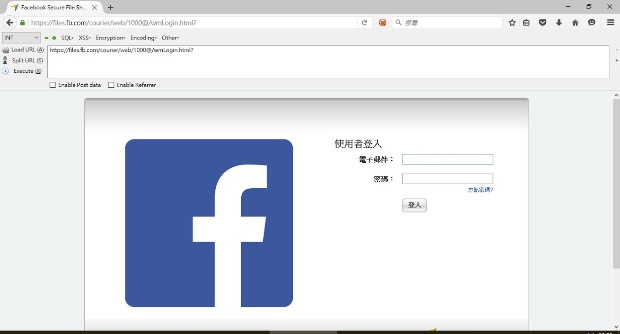
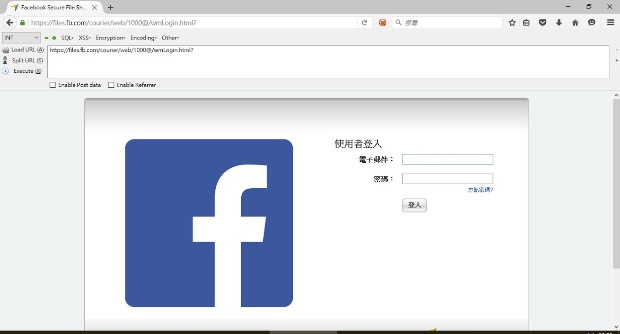
224Data SecurityHow I Hacked Facebook, and Found Someone’s Backdoor Script
How I Hacked Facebook, and Found Someone’s Backdoor Script(English Version) Foreword As a pentester, I love server-side vulnerabilities more than client-side ones....
-

 141Vulnerabilities
141VulnerabilitiesJBOSS Backdoor opens 3 million servers at risk of attacks
Experts at Cisco Systems discovered more than 3 million vulnerable servers exposed on the Internet while scanning for the presence of JBOSS...
-
 99Data Security
99Data SecurityLinux Computers Targeted by New Backdoor and DDoS Trojan
Threat level is not high, the virus requires users to give it root privileges in order to infect their computers. After being...
-
 204Hacked
204HackedThe TOR Project: “Our Developers Will Quit If Ordered To Backdoor TOR Browser”
Short Bytes: The TOR Project has expressed its commitment to researching and developing new ways to mitigate the threats of security failure....
-

 279Geek
279GeekBackdoor on Your Smartphone Already Exists — Explained
Though the FBI has already hacked into the iPhone of suspected San Bernardino shooter Syed Rizwan Farook, there’s something missing — Mr. Kokumai, President of...
-
 220Data Security
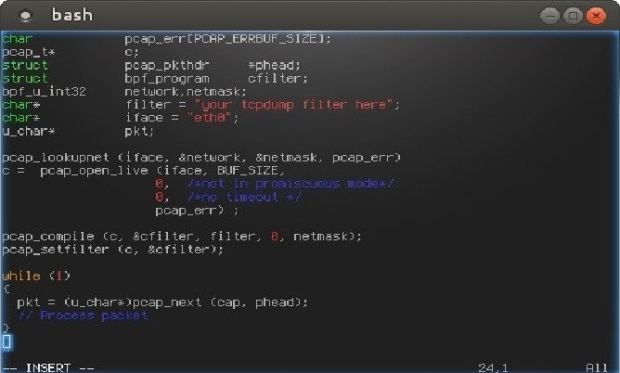
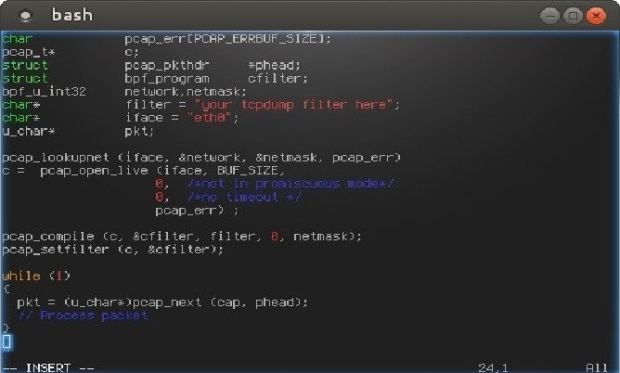
220Data SecurityHow to Build Stealth Backdoors
Today I’m going to tell you about a couple of techniques used to build stealth backdoors. Then, I will also show you...
-

 95Malware
95MalwareSecurity pros believe an encryption backdoor is open to abuse
The Government wants backdoor access to our devices so that it can protect us from terrorists and defend matters of national security....
-

 172Data Security
172Data SecurityPopular WordPress Plugin Comes With a Backdoor, Steals Site Admin Credentials
Last summer we shared a story about the SweetCaptcha WordPress plugin injecting ads and causing malvertising problems for websites that leveraged the plugin....
-

 123Data Security
123Data Security$17 smartwatch includes a backdoor in the pairing app
A group of researchers that analyzed security of a number of smart watches discovered a $17 smartwatch is sold with a backdoor...
-
 85Malware
85MalwareSystem Updates: Governments Can Hack Most Software Using This “Golden Key” Backdoor
Short Bytes: When you read the headlines like “FBI is forcing Apple to create a backdoor in their products”, what you are really...
-

 86Data Security
86Data SecurityFBI could use 3 other hacks on killer’s iPhone besides an Apple backdoor
Other than an Apple backdoor hack, FBI could use 3 other hacks on killer’s iPhone. According to hardware-security experts, there are at least...
-

 258News
258NewsHackers Compromise the Download Link for Linux Mint with Backdoor
Hackers Compromise the Download Link for Linux Mint Deemed to be a “modern, elegant and comfortable operating system which is both powerful and easy to...
-

 106Malware
106MalwareWhy Tim Cook is right to call court-ordered iPhone hack a “backdoor”
Custom version of iOS could undo years of work Apple put into securing iPhones. Tuesday’s court order compelling Apple to hack the iPhone...
-

 348Geek
348GeekApple defiant in San Bernardino Shooting Case; says no to backdoor access
Judge Issues Order to Apple to Unlock iPhone Vital in the San Bernardino Shooting Case — Apple refuses to follow orders The...
-

 104Malware
104MalwareBackdoor in MVPower DVR Firmware Sends CCTV Stills to an Email Address in China
IoT security experts from Pen Test Partners have confirmed the presence of a backdoor in the firmware used by some DVR devices...






