Search results for "Backdoor"
-

 204Data Security
204Data SecuritySecurity Firm Detects 57M Attempts to Exploit 2-Year-Old Router Firmware Backdoor
The case of the Netis router firmware backdoor shows you that even if a company puts out a patch to resolve security...
-

 146Vulnerabilities
146VulnerabilitiesPowerful backdoor/rootkit found preinstalled on 3 million Android phones
Firmware that actively tries to hide itself allows attackers to install apps as root. Almost three million Android phones, many of them...
-

 157Data Security
157Data SecurityPoisonTap Can Hijack Web Traffic and Install Backdoors on Password-Protected PCs
Hardware hacker Samy Kamkar has released a new tool called PoisonTap that is capable of a plethora of malicious actions, all of...
-

 246Hacked
246Hacked[Updated: ZTE Statement] Chinese Secret Backdoor Is Sucking Data From 700 Million Android Smartphones Without Permission
Short Bytes: Kryptowire has found a secret backdoor in budget Android smartphones. They took the BLU R1 HD for testing and concluded...
-

 70Malware
70MalwareChinese company installed secret backdoor on hundreds of thousands of phones
In “mistake,” AdUps collected data from BLU Android phones in US. Security firm Kryptowire has uncovered a backdoor in the firmware installed...
-
 71Malware
71MalwareFake Cain XPii Cleaner App Is Actually a Backdoor with Very Annoying Features
If you ask any malware analyst these days, they’ll tell you they come across countless of useless or unfinished malware variants on...
-
 219Data Security
219Data SecurityFakeFile Trojan Opens Backdoors on Linux Computers, Except openSUSE
Trojan targets desktops, not servers or IoT devices. Malware authors are taking aim at Linux computers, more precisely desktops and not servers, with...
-

 243Data Security
243Data SecurityCrooks exploit a zero-day in WordPress eCommerce Plugin to upload a backdoor
Experts from the White Fir Design discovered cybe rcriminals exploited a zero-day flaw in an e-commerce plugin for WordPress to upload a...
-

 342News
342NewsDangerous Pork Explosion backdoor found in Android Devices
Android Smartphones from Foxconn Manufacturer Plagued with Dangerous Security Flaw known as Pork Explosion. Android operating system has become quite vulnerable to...
-
 239How To
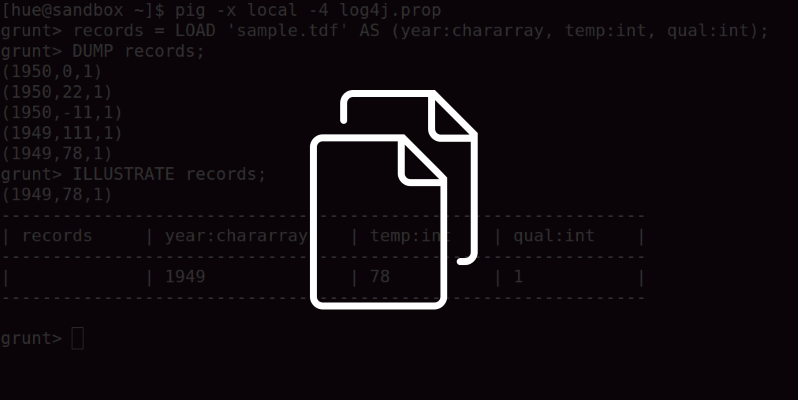
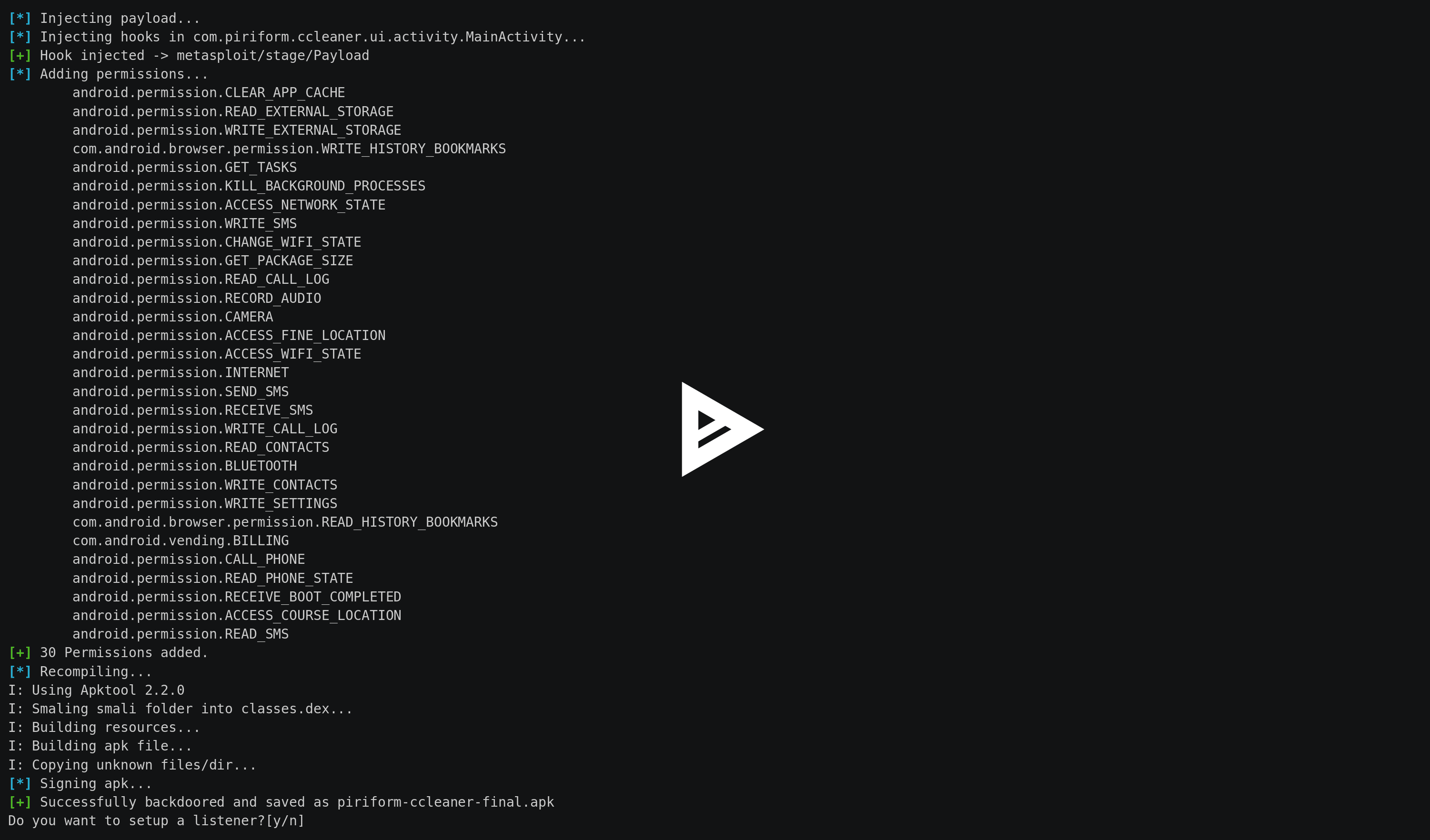
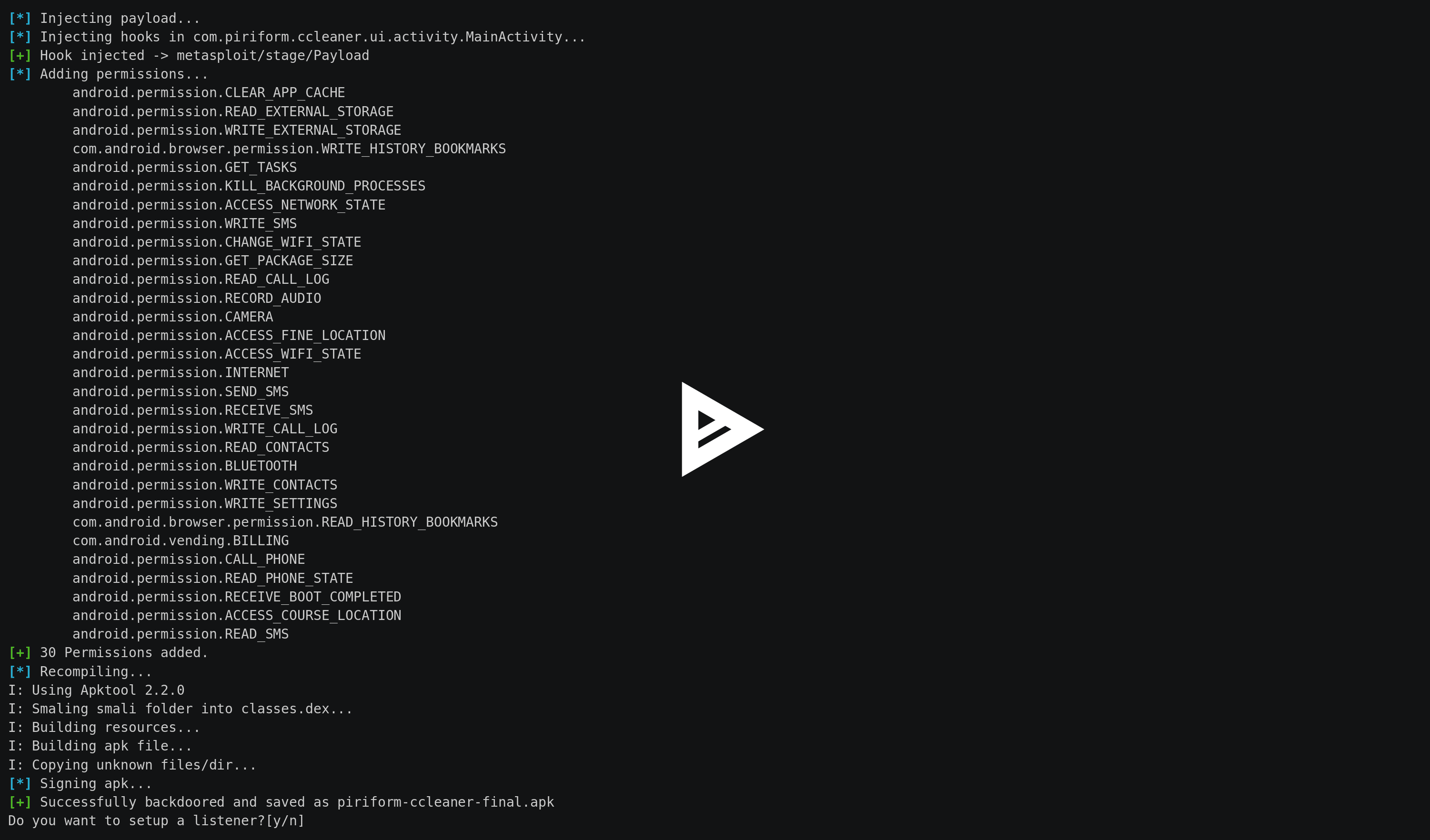
239How ToSpade – Android APK Backdoor Embedder
Quick and handy APK backdoor embedder with metasploit android payloads. Requirements: metasploit Installation and execution: Then you can download smap by cloning...
-
 339Trojan / Worms
339Trojan / WormsMalcrafted Microsoft Publisher files(PUB) Delivering backdoor Torjan?
Spam wave dropping trapped PUB file spotted by security experts at Bitdefender. These PUB file deliver a backdoor which is capable of setting sensitive...
-

 103Malware
103MalwareA backdoor on Xiaomi device allows silent and remote deliver of any app
A Dutch Computer Science student discovered the presence of a backdoor that could allow an attacker to silently install any app on...
-

 92Incidents
92IncidentsMicrosoft Publisher files spread backdoor to steal corporate data, Bitdefender warns
A targeted spam wave is infecting Windows computers with a backdoor capable of stealing sensitive corporate information from medium and small-sized businesses....
-

 192Hacked
192HackedMokes: This Single Malware Creates “Backdoor” In Windows, Linux, Mac OS X
Short Bytes: A cross-platform malware family has been reported by a security researcher from Kaspersky Lab. The malware can create a backdoor...
-

 127Data Security
127Data SecurityThe Missing Piece – Sophisticated OS X Backdoor Discovered
In a nutshell Backdoor.OSX.Mokes.a is the most recently discovered OS X variant of a cross-platform backdoor which is able to operate on...
-
 115Data Security
115Data SecurityLinux.PNScan Trojan is back to compromise routers and install backdoors
The Linux Trojan Linux.PNScan is back and it is actively targeting routers based on x86 Linux in an attempt to install backdoors...
-

 227Data Security
227Data SecurityBackdoor Trojan Uses TeamViewer Components to Spy on PCs in Europe, Russia, US
Crooks also delivering keyloggers and password stealers. A new trojan called BackDoor.TeamViewerENT.1 is using parts of the legitimate TeamViewer application to allow crooks...
-
 175Malware
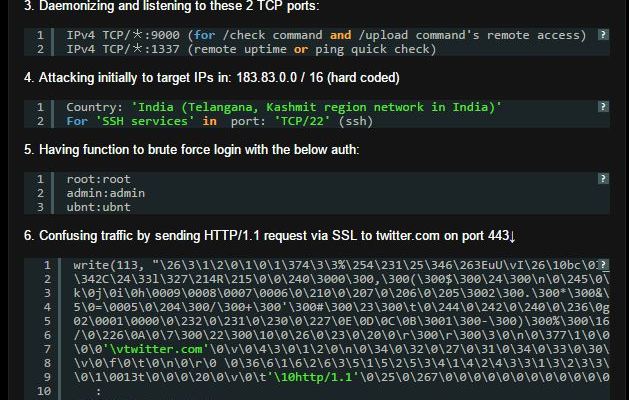
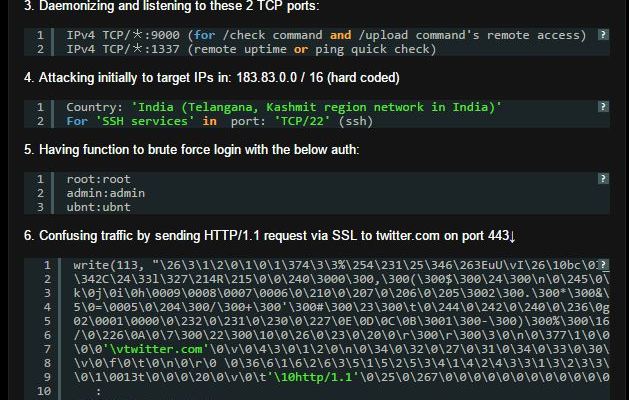
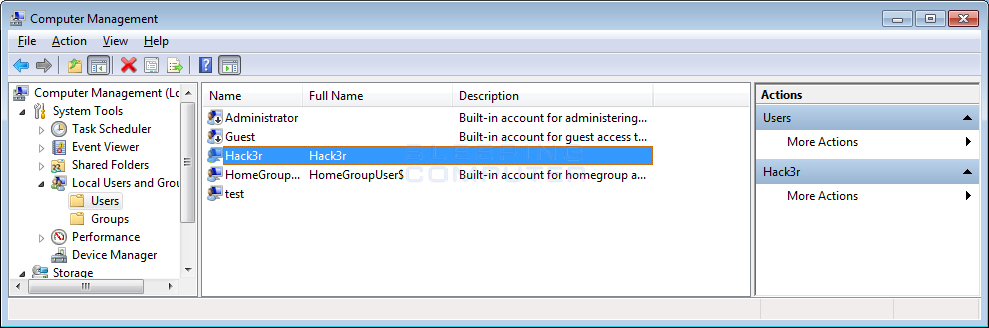
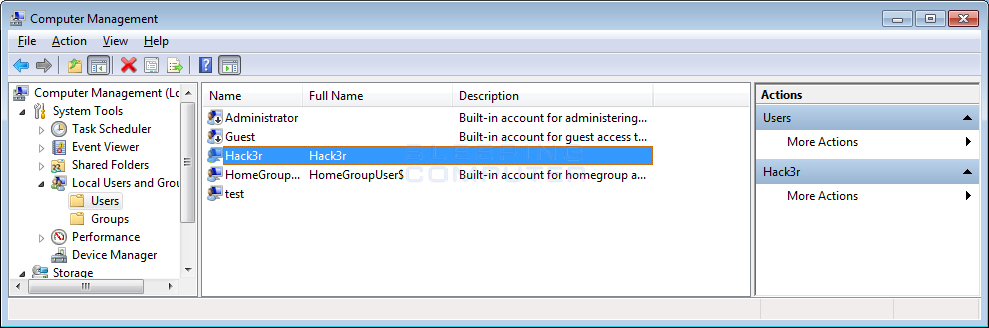
175MalwarePokemonGo Ransomware installs Backdoor Account and Spreads to other Drives
With the popularity of PokemonGo, it was inevitable that a malware developer would create a ransomware that impersonates it. This is the case...
-

 302Cyber Attack
302Cyber AttackOMG!! Accidentally Microsoft leaked backdoor Keys to BYPASS UEFI secure boot
Keys to BYPASS UEFI secure boot Microsoft accidentally leaked the Secret keys to BYPASS UEFI secure boot that allow hackers to unlock devices...
-
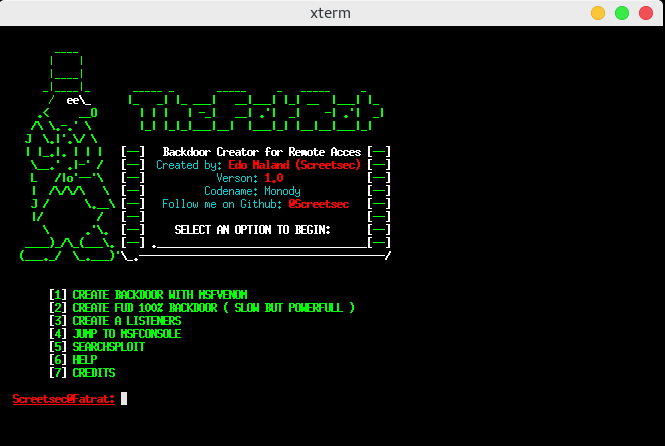
 318Hack Tools
318Hack ToolsTheFatRat – Easy Tool to Generate Backdoor
Easy tool for generate backdoor with msfvenom ( part of metasploit framework ) and program compiles a C program with a meterpreter...
-

 208Hacked
208HackedMicrosoft Creates Backdoor In Windows, Accidentally Leaks UEFI Secure Boot Keys
Short Bytes: Two researchers reported that Microsoft accidently compromised the golden keys to its UEFI Secure boot feature. The golden keys allow...






