Search results for "Backdoor"
-
 329Malware
329MalwareAPT-C-27 Hackers Launching njRAT Backdoor via Weaponized Word Documents to Control the Compromised Device
Goldmouse APT group (APT-C-27) now start exploiting the WinRAR vulnerability (CVE-2018-20250[6]) to hide the njRAT backdoor and targeting users reside in the...
-

 178Incidents
178IncidentsChinese hackers install backdoors in three videogame companies
Three companies in the videogame industry established in Asian countries have been affected by this attack campaign According to experts in network security and...
-
 312Data Security
312Data SecurityNew backdoor malware hits Slack and Github platforms
The cybersecurity researchers at Trend Micro have discovered A new malware strain tapped into GitHub posts and Slack channels. Dubbed Slub by researchers; the malware works by exploiting...
-
 313Malware
313MalwareHackers Launching FlawedAmmyy Malware Via Undetected MS Excel Macros that Carried Powerful Backdoor
Threat actors from TA505 currently spreading powerful FlawedAmmyy RAT via weaponized MS Excel documents with malicious Excel 4.0 macro which is hard...
-

 272Malware
272MalwareA new dangerous Linux backdoor could trigger severe attacks
Many researchers believe that this new Trojan could detonate an important wave of cyberattacks Network security and ethical hacking researchers from the...
-
 284Malware
284MalwareSpeakUp – A New Undetected Backdoor Exploiting Six Linux Distributions With Known Vulnerabilities
A new trojan dubbed SpeakUp exploiting six different Linux distributions with know vulnerabilities. The campaign primarily targeting East Asia and Latin America,...
-

 331News
331News22 Apps in Google Play Store Taken Down Due To Backdoor Downloaders
Google continues its quest to keep Android users safe by actively banning apps they think will harm its users. This time around,...
-
 314Malware
314MalwareHackers Distributing PowerShell-based Backdoor Via MS Office document That Shares Stolen Data Via C&C Sever
Researchers observed a new Powershell based backdoor via Microsoft office document that infects similar to MuddyWater threat actor hacking tools to steal...
-
 263Exploitation Tools
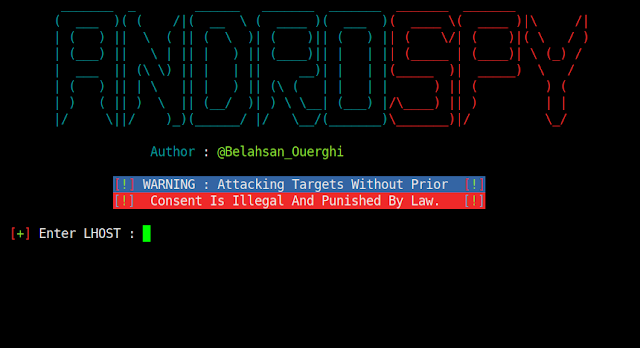
263Exploitation ToolsAndrospy – Backdoor Crypter & Creator With Automatic IP Poisener
Androspy is Backdoor Crypter & Creator with Automatic IP Poisener Coded By Belahsan Ouerghi Dependencies keytool jarsigner Apache2 Metasploit-Framework xterm Installation...
-
 259Backdoors
259BackdoorsAndrospy – Backdoor Crypter & Creator With Automatic IP Poisener
Androspy – Backdoor Crypter & Creator With Automatic IP Poisener Dependencies keytool jarsigner Apache2 Metasploit-Framework xterm Installation sudo apt-get install git git...
-

 240News
240NewsWordPress GDPR Compliance plugin hacked to spread backdoor
Update your GDPR Compliance plugin right now. Security researchers have identified a critical vulnerability in the popular WP GDPR Compliance plugin assisting over...
-

 168Malware
168MalwareWidely Used Cryptocurrency App Launching 2 Different Powerful Backdoor on Mac Users
A cryptocurrency app, CoinTicker which is widely used in cryptocurrency industry pushing 2 different backdoors on Mac users to steal the cryptocurrency coins...
-
 253Backdoors
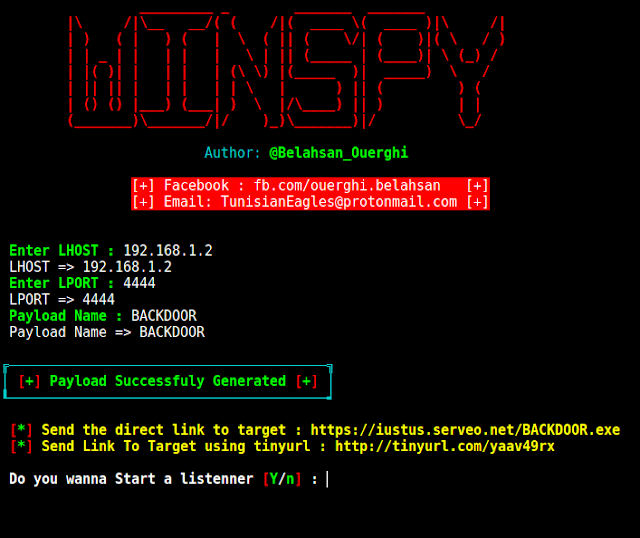
253BackdoorsWinSpy – A Windows Reverse Shell Backdoor Creator With An Automatic IP Poisener
WinSpy: Windows Reverse Shell Backdoor Creator With ip poisener. Dependencies 1 – metasploit-framework 2 – xterm 3 – apache2 4 – whiptail...
-

 314Malware
314MalwareDarkPulsar – A Shadow Brokers Group’s New Hacking Tool Leak To Open Backdoor & Provide Remote Control
Shadow Brokers Hacking Group’s new administrative module Tool called DarkPulsar Leaks with persistance backdoor to provide remote control to the attackers. There...
-
 282Malware
282MalwareMost Advanced Backdoor Obfuscation and Evasion Technique That used by Hackers
Cybercriminals are using the most sophisticated techniques to bypass the security controls in various organization such as IT, medical, manufacturing industries, energy...
-

 312Backdoors
312BackdoorsDoor404 – PHP Backdoor For Web Servers
Door404 is Open Source PHP Backdoor For Web Servers Developed By MrSqar & Rizer This Project Developed For 2 Reasons First ”...
-

 232Backdoors
232BackdoorsCloak – An Intelligent Python Backdoor Framework
Cloak generates a Python payload via msfvenom and then intelligently injects it into the python script you specify. o evade basic detection,...
-
Malware
Chinese Cyber Espionage Group APT10 Delivers UPPERCUT Backdoor Via Malicious Word Documents
Chinese cyber espionage group APT10 know for targeting construction and engineering, aerospace, and telecom firms, and governments agencies in United States, Europe,...
-

 241Malware
241MalwareExperts ask Google for clarifications about backdoor in Titan Security Key
The company has been asked for information about its security software produced in China According to ethical hacking specialists from the International...
-

 348Malware
348MalwareFive Eyes Group demands access to crime suspects data through encryption backdoors
The group threatens to take legal action Five Eyes alliance member countries have threatened to implement legislation if technology providers do not cooperate...
-
 330Backdoors
330BackdoorsSMBetray – Backdooring and Breaking Signatures
The goal of this tool is to switch the aim of MiTM on SMB from attacking the server through relayed connections, to...






