Search results for "Backdoor"
-

 181News
181NewsEuropean Government Proposes Ban On Encryption Backdoors
The European Parliament has set up a revised list does not require that the encryption of a party to a party when...
-

 242Car Hacking
242Car HackingThe Bicho – An Advanced Car Backdoor Maker
For the first time, a hardware backdoor tool is presented having several advanced features, such as: remote control via SMS commands, automated...
-

 173Vulnerabilities
173VulnerabilitiesHIKVISION PATCHES BACKDOOR IN IP CAMERAS
Hikvision, a Chinese manufacturer of video surveillance equipment, recently patched a backdoor in a slew of its cameras that could have made...
-

 137Malware
137MalwareLeaked: The UK’s secret blueprint with telcos for mass spying on internet, phones – and backdoors
Real-time full-blown snooping with breakable encryption. The UK government has secretly drawn up more details of its new bulk surveillance powers –...
-
 157Malware
157MalwareMalware Author Inflates Backdoor Trojan With Junk Data Hoping to Avoid Detection
A malware coder is injecting megabytes of junk data inside his malicious payloads, hoping to avoid detection by some antivirus solutions or...
-

 198Malware
198MalwareOpen Ports Create Backdoors in Millions of Smartphones
Mobile applications that open ports on Android smartphones are opening those phones to remote hacking, claims a team of researchers from the...
-

 80Malware
80MalwareBackdoor Code Discovered in Popular Bitcoin Mining Equipment
An unknown security researcher has published details on a vulnerability named “Antbleed,” which the author claims is a remote backdoor affecting Bitcoin...
-
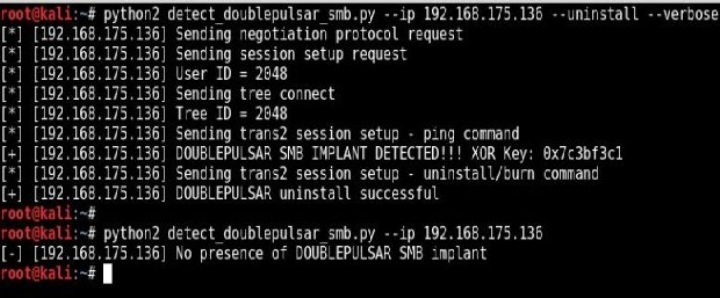
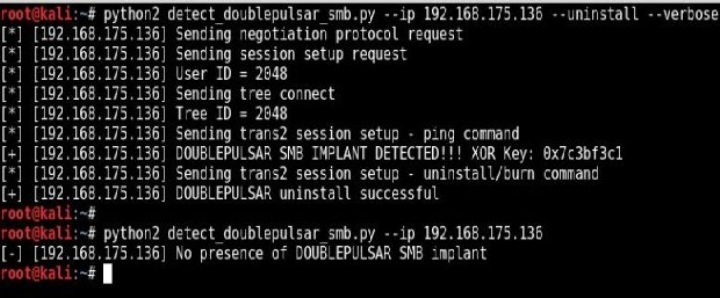 86Malware
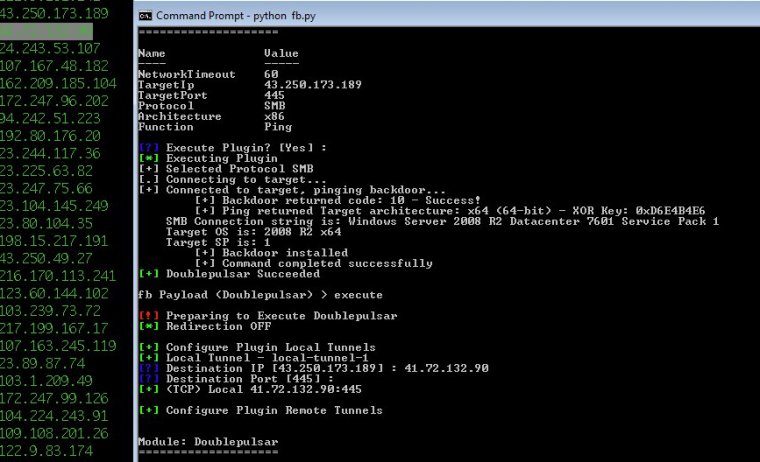
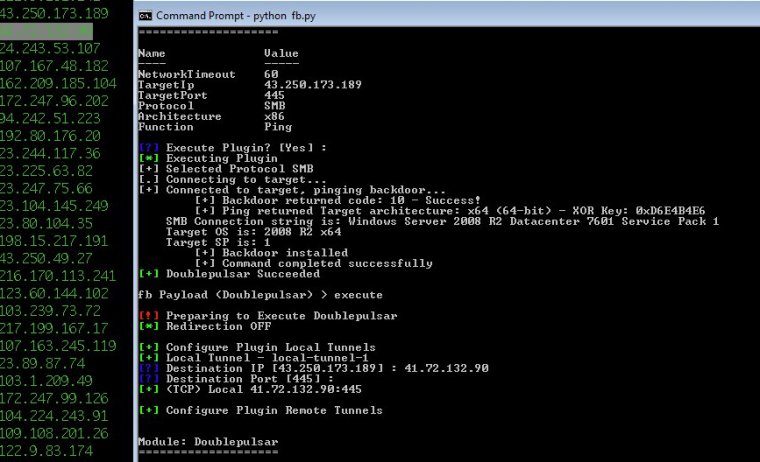
86MalwareNSA backdoor detected on >55,000 Windows boxes can now be remotely removed
Microsoft dismisses DoublePulsar infection estimates, but otherwise remains silent. After Microsoft officials dismissed evidence that more than 10,000 Windows machines on the...
-
 265Malware
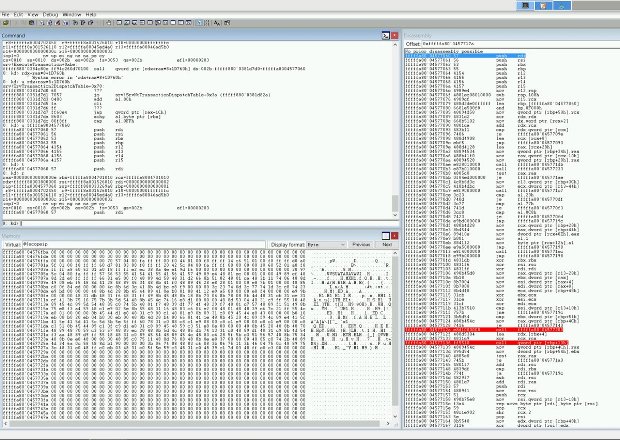
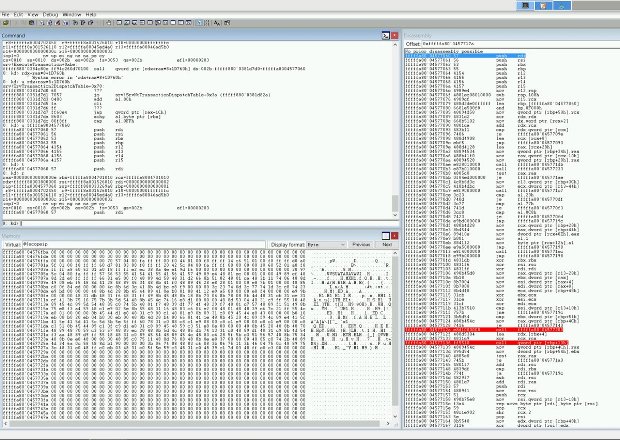
265MalwareDoublePulsar Initial SMB Backdoor Ring 0 Shellcode Analysis
One week ago today, the Shadow Brokers (an unknown hacking entity) leaked the Equation Group’s (NSA) FuzzBunch software, an exploitation framework similar...
-
 143Vulnerabilities
143Vulnerabilities10,000 Windows computers may be infected by advanced NSA backdoor
Did script kiddies use DoublePulsar code released by NSA-leaking Shadow Brokers? Security experts believe that tens of thousands of Windows computers may...
-
 335Malware
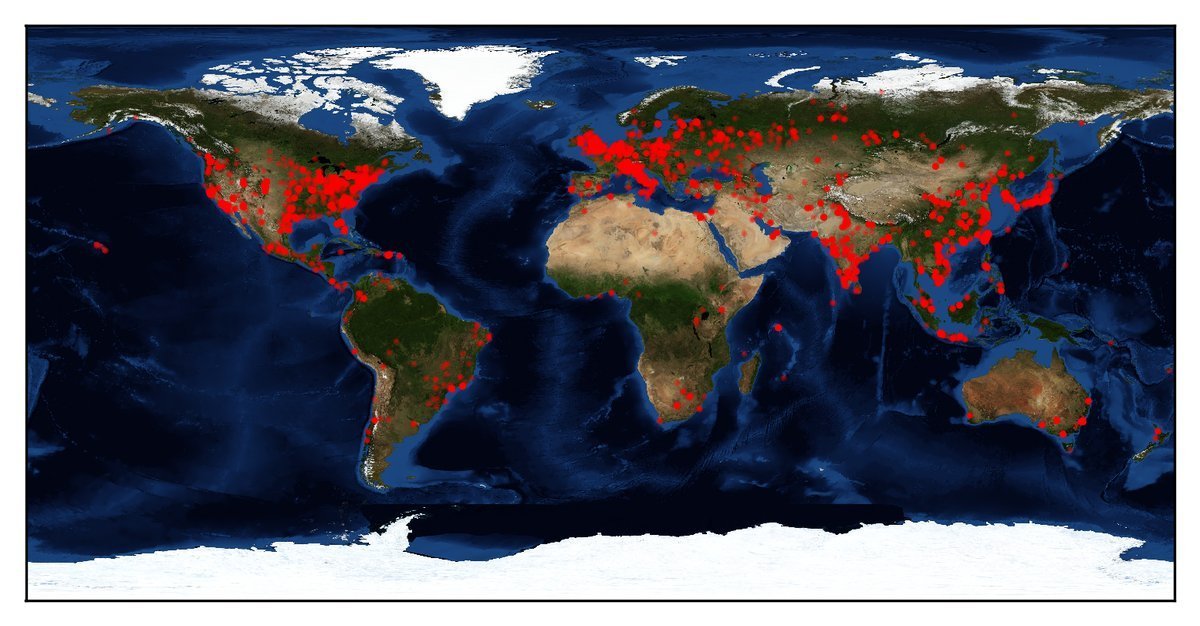
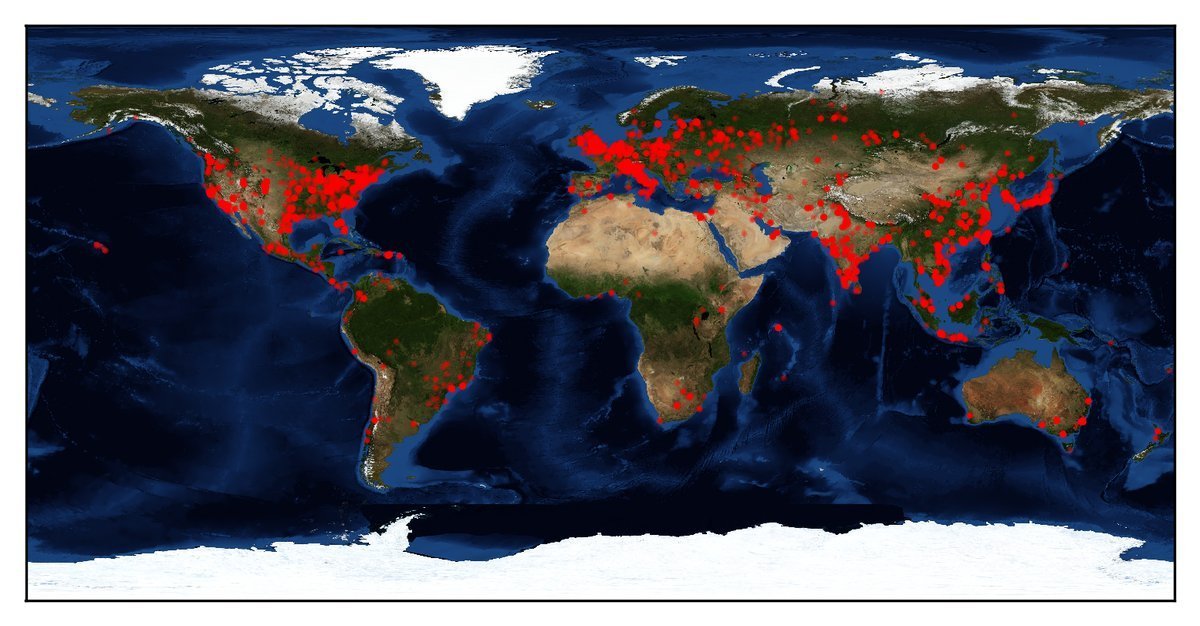
335MalwareMass Scan Revealed More Than 30000 Windows Computers Infected by NSA backdoor DoublePulsar
[jpshare] A Recent Mass Scan Revealed That More than 30000 Windows Machine Infected by National Security Agency Backdoor DOUBLEPULSAR .DOUBLEPULSAR one of the NSA...
-
 97Malware
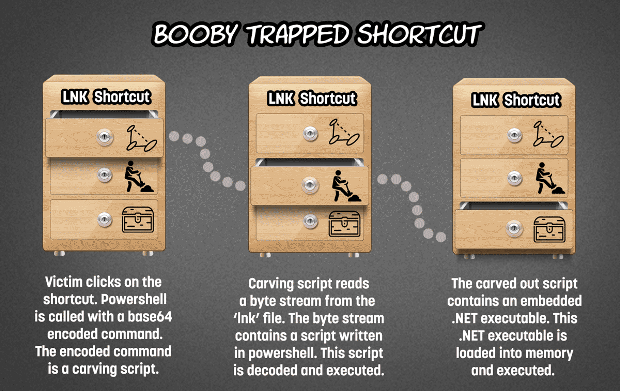
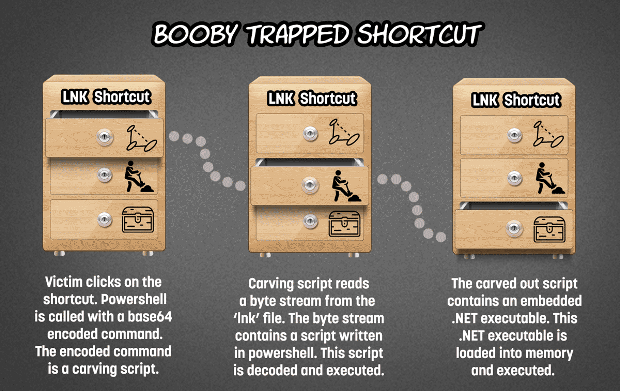
97MalwareBooby trap a shortcut with a backdoor
Embedding a shortcut (.lnk file) which points to powershell (accompanied by an encoded command) in a word document or zip file is...
-

 284Cyber Crime
284Cyber CrimeCarbon Paper: Peering into Turla’s second stage backdoor
The Turla espionage group has been targeting various institutions for many years. Recently, ESET found several new versions of Carbon.
-
 107Data Security
107Data SecurityAPT29 USED DOMAIN FRONTING, TOR TO EXECUTE BACKDOOR
APT29, a/k/a Cozy Bear, has been utilizing a technique called domain fronting in order to secure backdoor access to targets for nearly two...
-
 206Malware
206MalwareChinese PUPs distributing Backdoored Drivers which affect Windows operating system
PUP(potentially unwanted program) packages that install’s along with Chinese software’s consist of backdoors targeting English speakers. The backdoor was uncovered by Malware...
-

 98Malware
98MalwareBig Surprise: Chinese PUPs Deliver Backdoored Drivers
A driver secretly installed via PUPs packages for Chinese software contain backdoors enabling a third-party to load unsigned drivers or to execute...
-

 237Backdoors
237BackdoorsBrainDamage – A fully featured backdoor that uses Telegram as a C&C server
A python based backdoor which uses Telegram as C&C server. Setup Telegram setup: Install Telegram app and search for “BOTFATHER”. Type /help...
-

 105Vulnerabilities
105VulnerabilitiesFormer IT Admin Accused of Leaving Backdoor Account, Accessing It 700+ Times
In another classic example of why you shouldn’t leaving your work laptop in the car, national security may have been compromised. An...
-
 104Malware
104MalwareHidden backdoor discovered in Chinese IoT devices
Researchers at Trustwave have uncovered a backdoor in IoT devices from a Chinese manufacturer that could leave them open to exploitation. The...
-

 169Vulnerabilities
169VulnerabilitiesTwo new Mac backdoors discovered
On Valentine’s Day, Mac users got a special “treat” in the form of new malware. Then, later that same week, there were signs of...
-
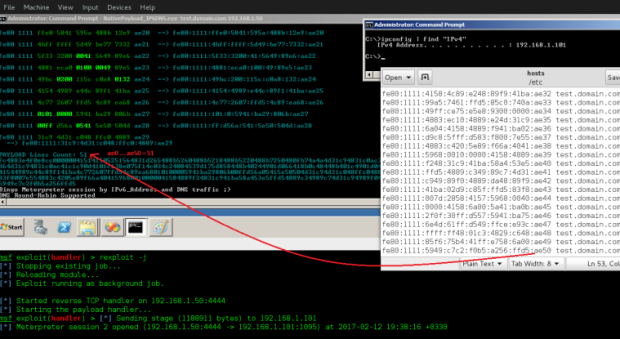
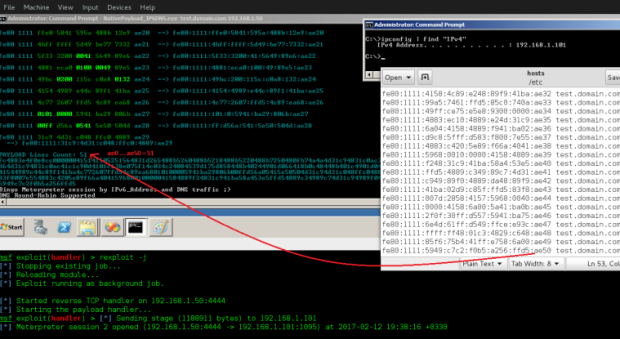 182Vulnerabilities
182VulnerabilitiesTransferring Backdoor Payloads by DNS AAAA records and IPv6 Address
Transferring Backdoor Payloads by DNS AAAA records and IPv6 Address. in this article i want to explain how can use IPv6 Address (AAAA)...






