Search results for "Backdoor"
-
 234Backdoors
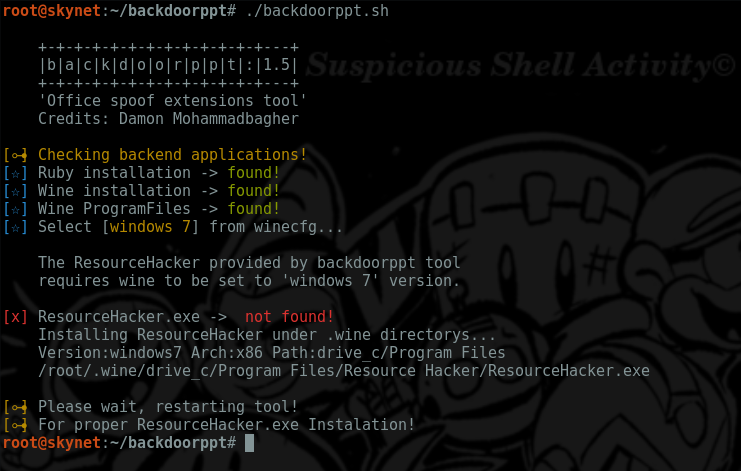
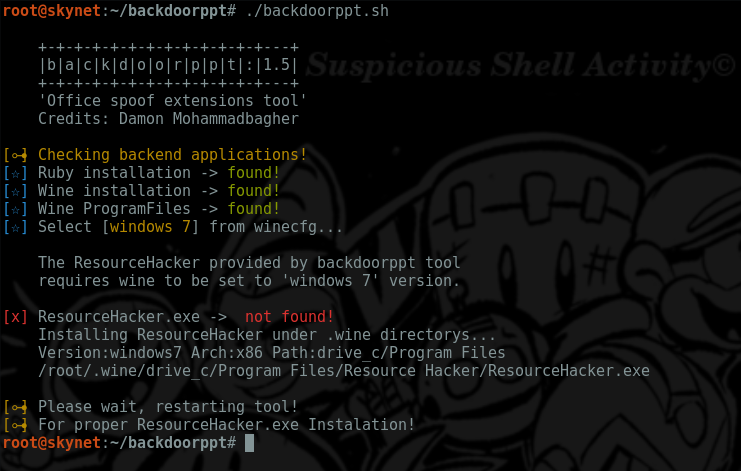
234Backdoorsbackdoorppt – Transform your payload.exe into one fake word doc
Simple script that allow users to add a ms-word icon to one existing executable.exe (using resource-hacker as backend appl) and a ruby...
-

 213Malware
213MalwareExpect renewed push for encryption backdoors from Trump administration
Top law enforcement officers, FBI director James Comey and Trump’s nominee for attorney general, Sen. Jeff Sessions, are supportive of giving law...
-

 101Data Security
101Data SecurityResearchers condemn unsubstantiated WhatsApp “Backdoor” story by Guardian
The Guardian, a well known UK-based newspaper, is being heavily criticized by security researchers for publishing an unverified story on WhatsApp vulnerability....
-

 96Malware
96MalwareNew Mac backdoor using antiquated code
The first Mac malware of 2017 was brought to my attention by an IT admin, who spotted some strange outgoing network traffic from a...
-
 304Malware
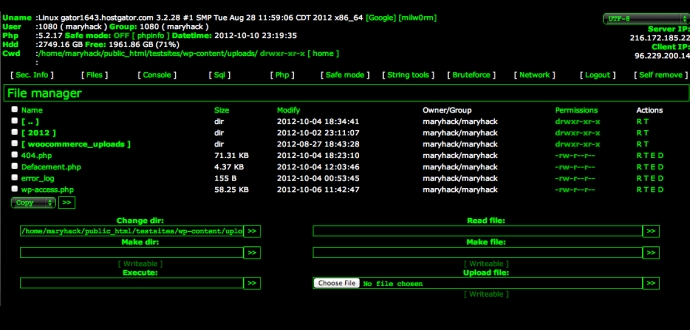
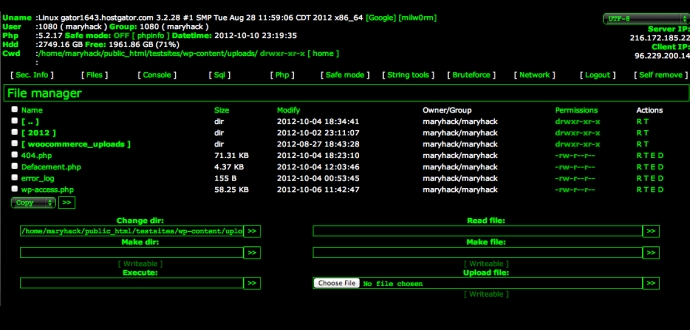
304MalwareDutch coder built backdoors into thousands of websites
Dutch developer used built-in backdoors in websites to steal personal information of customers. A 35-year-old unnamed web developer from Leeuwarden, Netherlands has...
-

 196Hacked
196HackedWhatsApp’s Alleged “Secret Backdoor” Is Actually A “Feature”, Company Claims
Update (13:30 IST): Open Whisper Systems, whose Signal protocol is used in WhatsApp, has claimed that the “secret backdoor” story is not...
-

 167Data Security
167Data SecurityWhatsApp backdoor allows snooping on encrypted messages
Exclusive: Privacy campaigners criticise WhatsApp vulnerability as a ‘huge threat to freedom of speech’ and warn it could be exploited by government...
-
 221How To
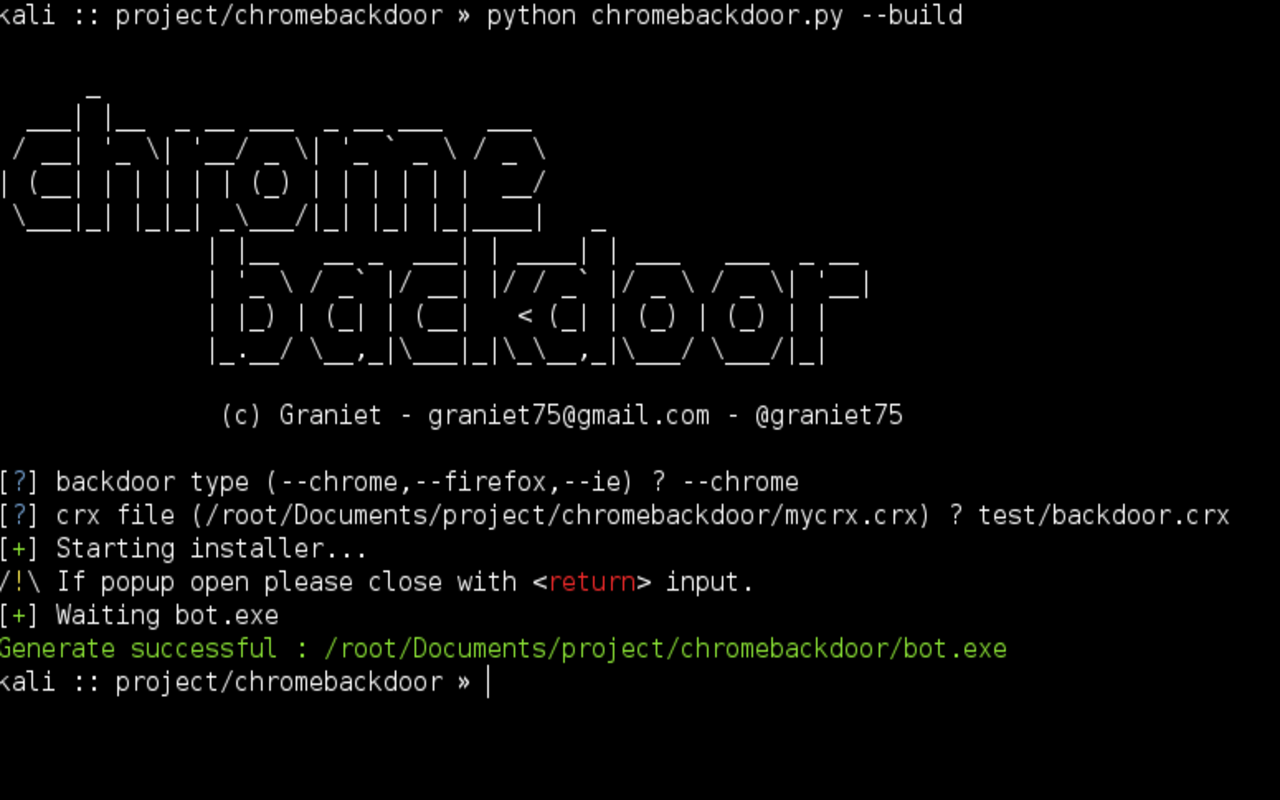
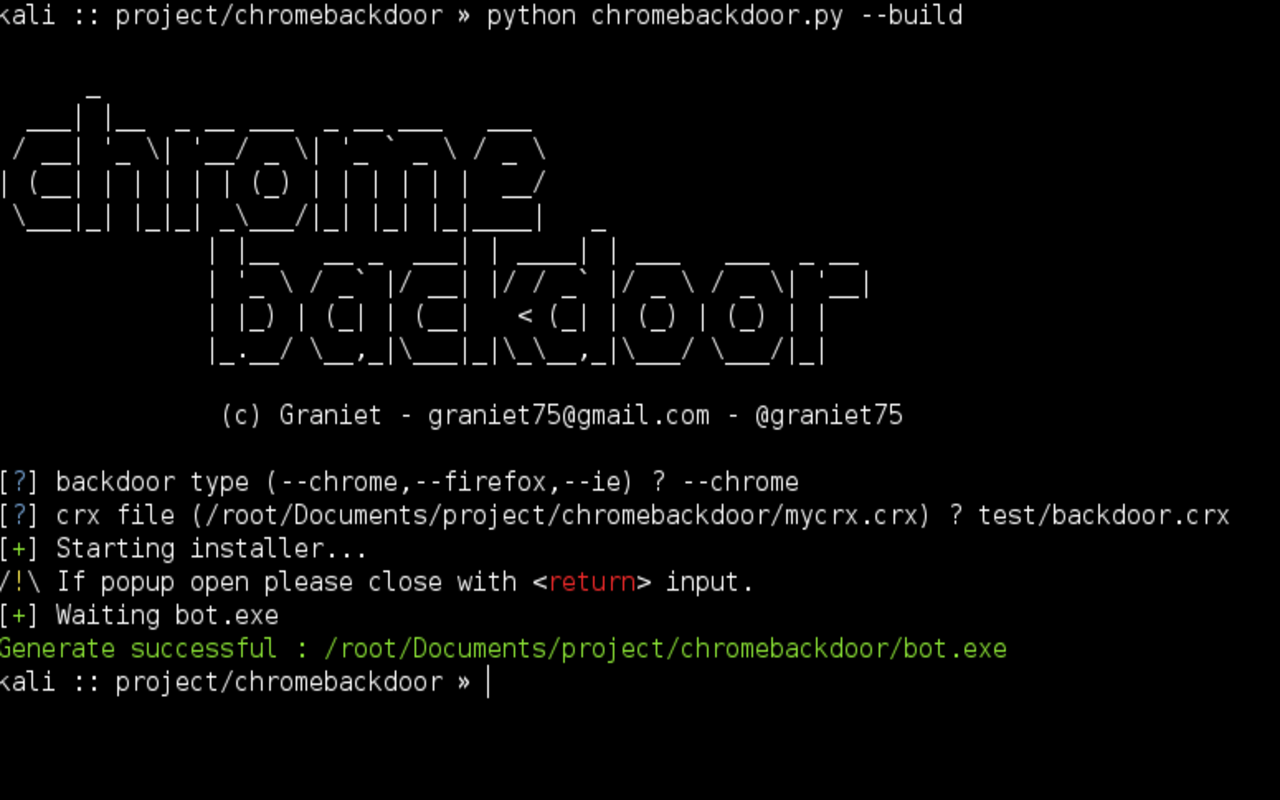
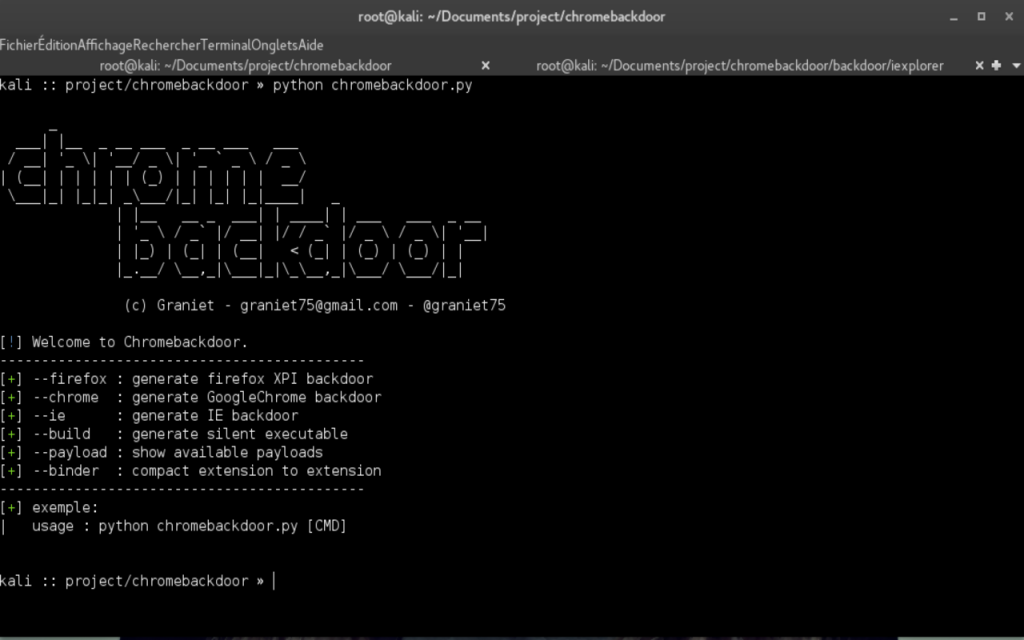
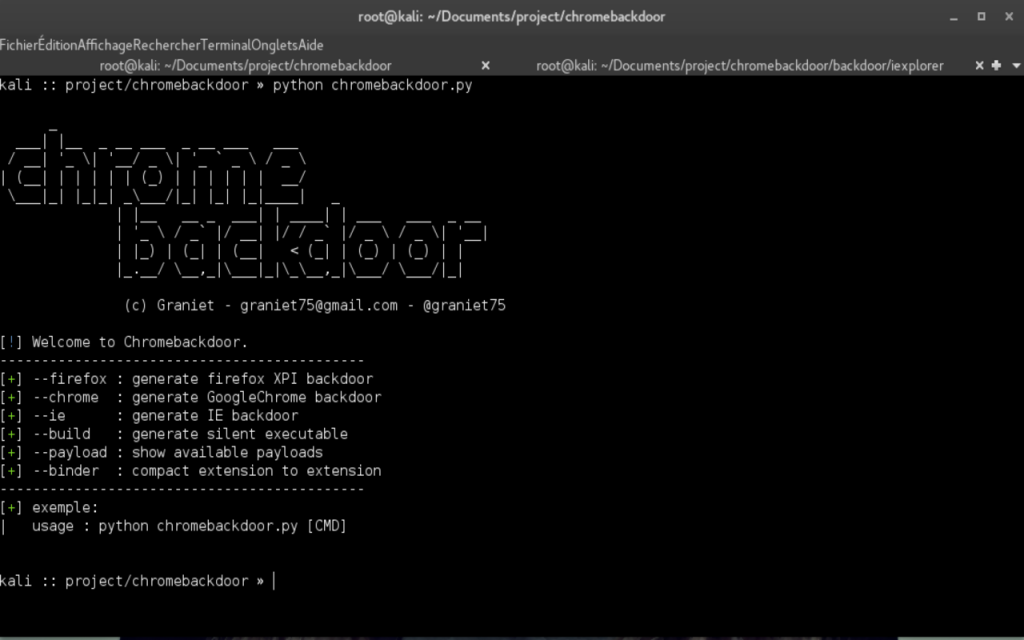
221How ToChromebackdoor – Backdoor C&C for Populars Browsers
Chromebackdoor is a pentest tool, this tool use a MITB technique for generate a windows executable “.exe” after launch run a malicious...
-
 244Backdoors
244BackdoorsChromebackdoor – Backdoor C&C for Populars Browsers
Chromebackdoor is a pentest tool, this tool uses a MITB technique to generate a windows executable “.exe”, after launch, it runs a...
-

 90Vulnerabilities
90VulnerabilitiesMM CORE IN-MEMORY BACKDOOR RETURNS AS “BIGBOSS” AND “SILLYGOOSE”
we will detail our discovery of the next two versions of MM Core, namely “BigBoss” (2.2-LNK) and “SillyGoose” (2.3-LNK). Attacks using “BigBoss” appear likely...
-

 120Malware
120MalwareHow to protect your company against a potential encryption backdoor policy
The election of Donald Trump has alarmed privacy advocates who worry that the self-described “law-and-order” president will take a more heavy-handed approach...
-

 244Malware
244MalwareCongress Report Rules Against Encryption Backdoors
Last week, a report published by the House of Representatives Judiciary Committee and the House of Representatives Energy and Commerce Committee has...
-

 105Malware
105MalwareAdups Backdoor Found in Latest Barnes & Noble NOOK Tablet
Barnes & Noble has joined the list of Android device vendors who sold smartphones and tablets affected by the Adups backdoor. According...
-

 153Vulnerabilities
153VulnerabilitiesA Backdoor Discover in Skype allows to hack everything that Skype can offer for Mac OS X
Trustwave recently reported a locally exploitable issue in the Skype Desktop API Mac OS-X which provides an API to local programs/plugins executing...
-
 226Backdoors
226BackdoorsBackdoorMan – Toolkit That Helps You Find Malicious, Hidden And Suspicious PHP Scripts And Shells
A Python open source toolkit that helps you find malicious, hidden and suspicious PHP scripts and shells in a chosen destination, it...
-

 169Vulnerabilities
169VulnerabilitiesOld Skype for Mac API Doubles as a Backdoor
A soon-to-be-deprecated API included with Skype for Mac contains a vulnerability that allows an attacker to bypass authentication procedures and query for...
-

 326Data Security
326Data SecurityNearly 80 Sony IP Camera Models Plagued with Backdoor Accounts
SEC Consult, renowned IT security services and consultation firm, has identified that there is a critical flaw in Sony’s 80 SNC series...
-

 182Malware
182MalwareCanadian Government Is Asking Citizens If They Want Encryption Backdoors
The Canadian government is asking citizens for their feedback on several privacy and cyber-security topics, as part of a public consultation period...
-

 113Data Security
113Data SecurityBackdoor Found in 80 Sony Surveillance Camera Models
Sony has released firmware updates that remove a remotely exploitable backdoor account from 80 models of IP and security cameras. Because attackers...
-
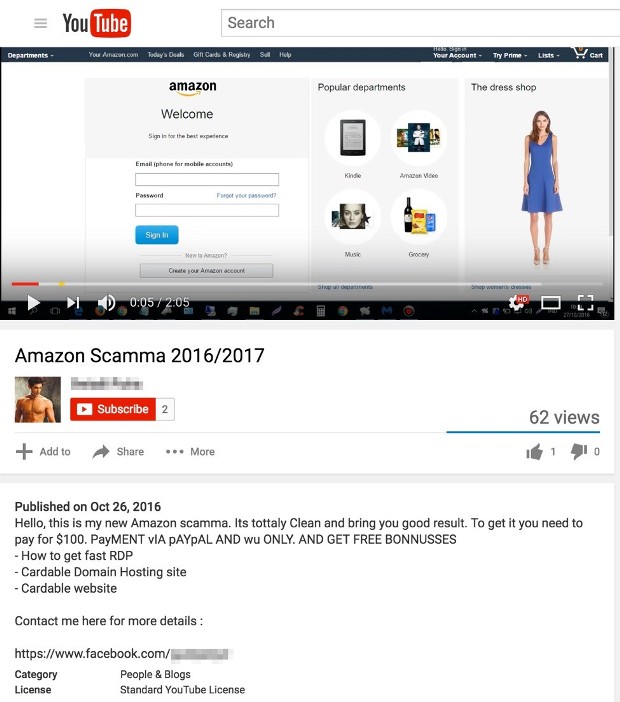
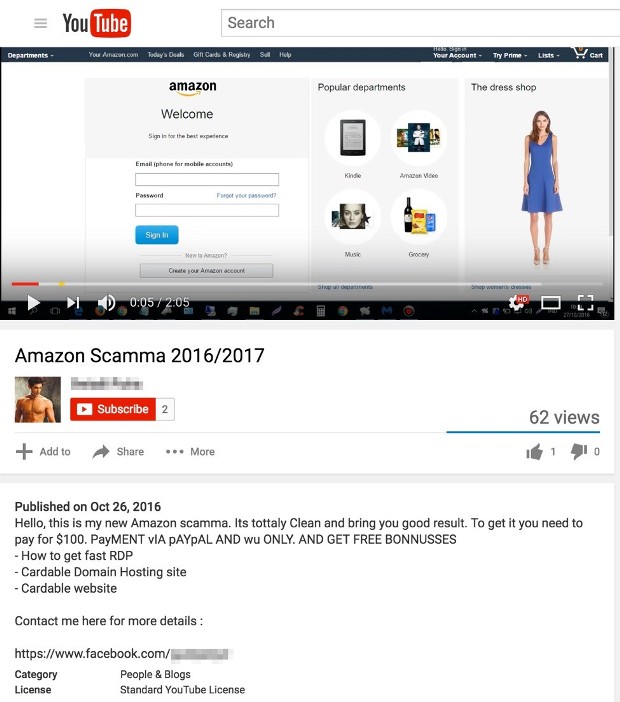 146Incidents
146IncidentsHackers Hunting Hackers: Backdoor-Infected Phishing Kits for Sale on YouTube
The technical nature of cyber crime can sometimes obscure the fact that creating, using, and distributing malware, phishing kits and other threats...
-

 118Incidents
118IncidentsKeygen Websites Spreading Gatak Backdoor Trojan
Websites offering free keygens for various enterprise software applications are helping crooks spread the Gatak malware, which opens backdoors on infected computers...






