Search results for "Backdoor"
-
 686Malware
686MalwareRussian Turla APT Group Hacked Iranian APT C2 Server For Backdoor Access To Expand The Cyber Attack
Hackers-Hack-Hackers: Russian APT group Turla known as Waterbug compromised the Iranian hacker’s command and control server infrastructure, and the Exfiltrated of data...
-

 547Malware
547MalwareChinese hackers could install backdoors on Microsoft SQL 11 and 12 servers using a “magic word”
The activities of government-sponsored hacker groups can have disastrous consequences. A group of digital forensics experts from ESET has revealed the existence...
-

 474Incidents
474IncidentsAvast internal networks were hacked. Did attackers install backdoors in CCleaner? Is it secure to use this tool?
Even security companies are exposed to cyberattacks. IT system audit specialists report that security software developer Avast has become victim of an...
-

 743Malware
743MalwareWinnti Group’s skip‑2.0: A Microsoft SQL Server backdoor
Notorious cyberespionage group debases MSSQL
-
 582Malware
582MalwareFree music files on the Internet could contain malware and backdoors
Digital forensics specialists report a new attack method consisting of the use of WAV audio files to hide and deliver backdoors and...
-

 661Malware
661MalwareWinnti Hackers Group Launching New Malware via Supply-chain Attacks to Inject Backdoor in Windows
Researchers discovered a new malware campaign from the Winnti threat group that utilizes the supply-chain attacks with a new set of artifacts to...
-

 368News
368NewsHuawei Could Sign ‘No Backdoor’ Agreement With India For 5G
India, the second-largest cellular market, is set to roll out 5G in upcoming years. The first step in the process is organizing...
-
 417Exploitation
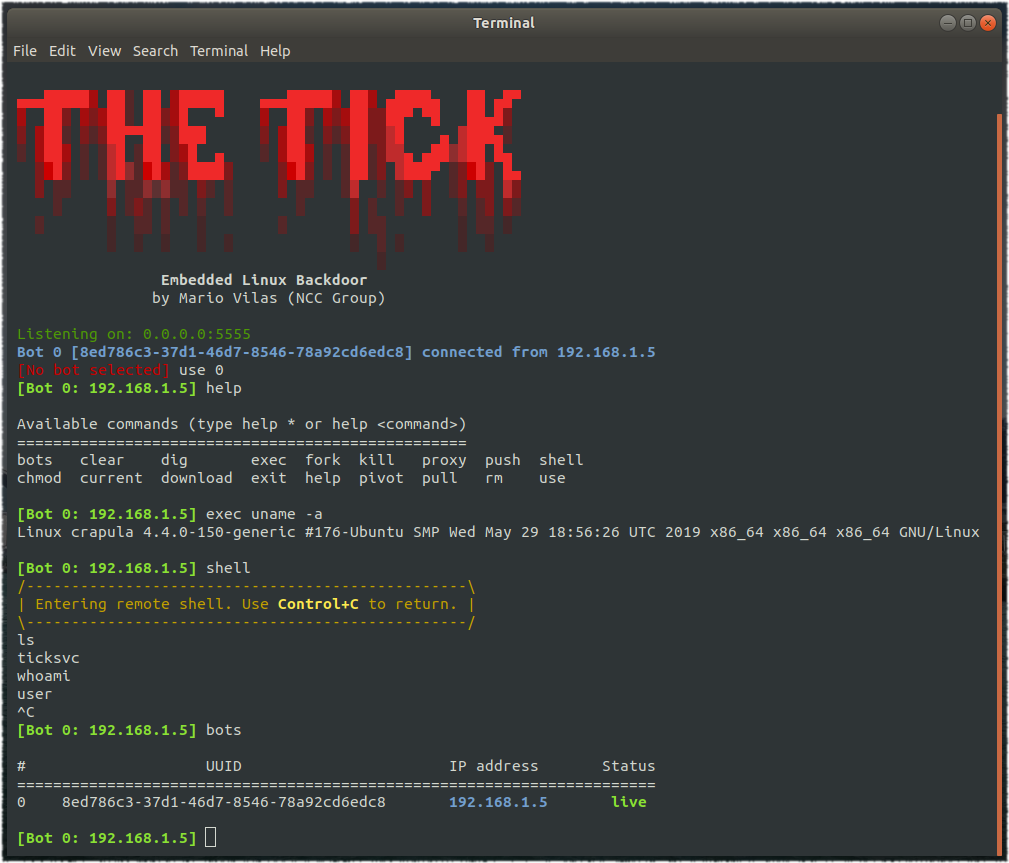
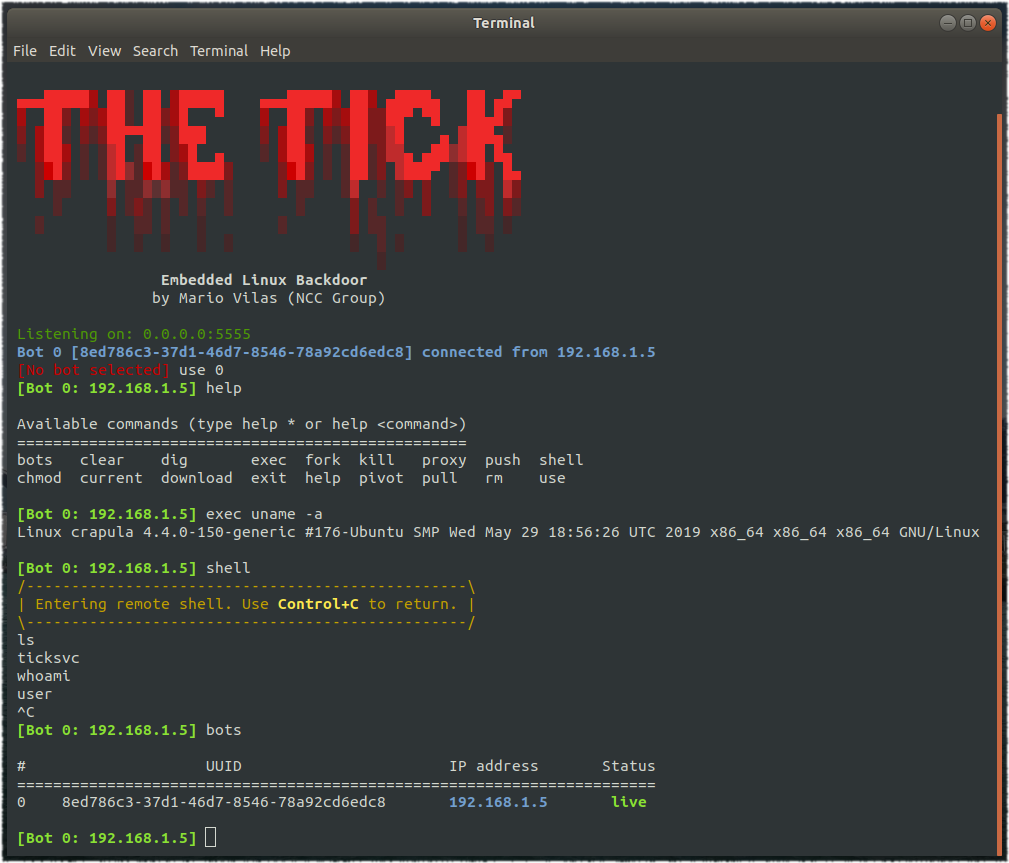
417ExploitationTheTick – A simple embedded Linux backdoor
A simple embedded Linux backdoor. Compiling The Tick depends only on libcurl, so make sure you have the corresponding development package. For...
-

 368News
368NewsUS And UK Ask Facebook To Create A “Backdoor” To Access Encrypted Texts
The US, UK, and Australia are putting pressure on Facebook to create a backdoor in its encrypted messaging apps that would allow...
-

 3.1KCyber Attack
3.1KCyber AttackCylance Security Researchers Warn Technology Firms in Southeast Asia for Chinese Open –Source Backdoor
Attackings of technology businesses in Southeast Asia by a suspected Chinese threat actor employ a version of the open-source PcShare backdoor, safety...
-

 272Malware
272MalwareESET discovered an undocumented backdoor used by the infamous Stealth Falcon group
ESET researchers discovered a backdoor linked to malware used by the Stealth Falcon group, an operator of targeted spyware attacks against journalists,...
-

 435Vulnerabilities
435VulnerabilitiesHackers are exploiting a backdoor on Fortinet SSL VPN; update now
Ethical hacking experts report that, in recent days, threat actors have been scanning the Internet looking for non updated SSL VPNs developed...
-

 443Malware
443MalwareNew Malware Attack Targeting 60 Million WordPress Websites to add Backdoor & Exploit Plugins Vulnerability
Researchers discovered an ongoing malvertising campaign targeting millions of WordPress websites to infect with backdoor and exploiting the various WordPress plugins vulnerabilities....
-
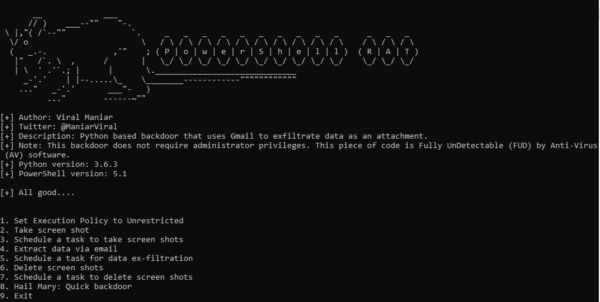
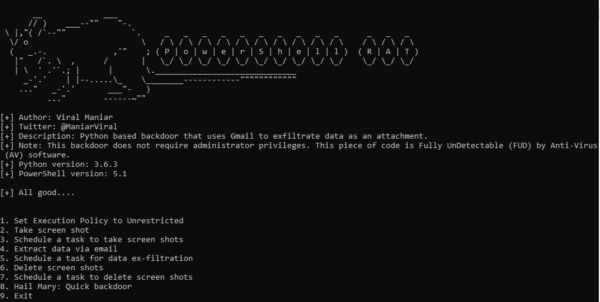 427Hacking Tools
427Hacking ToolsPowershell-RAT | A Backdoor Tool to Extract Data via Gmail
Powershell-RAT is a Python and Powershell script tool that has been made to help a pen tester during red team engagements to backdoor...
-

 405Vulnerabilities
405VulnerabilitiesFortinet backdoored FortiOS or hackers did for monitoring since last 5 years
About a week ago, two reports of vulnerabilities affecting the Virtual Private Network (VPN) Secure Socket Layer (SSL) systems of Fortinet appeared....
-
 261Malware
261MalwareStop programming in Ruby, applications using Ruby libraries have a backdoor
The RubyGems package repository maintenance team recently announced the removal of at least 18 malicious versions of 11 Ruby libraries due to...
-

 288Vulnerabilities
288VulnerabilitiesHackers Planted Backdoor in Webmin, Popular Utility for Linux/Unix Servers
Following the public disclosure of a critical zero-day vulnerability in Webmin last week, the project’s maintainers today revealed that the flaw was...
-
 200Malware
200MalwareHackers use Backdoor and Trojan to Attack Financial Departments of Organizations
Hackers use backdoor and remote access trojan that let attackers gain complete remote control over the compromised computer. The campaign particularly targets...
-
 524Malware
524MalwareMultistage Attack Delivers BillGates/Setag Backdoor to Turn Elasticsearch Servers into DDoS Botnet
A new multistage attack exploiting Elasticsearch servers using the old unpatched vulnerability to invoke a shell with a crafted query and encoded...
-
 249Malware
249MalwareAPT15 Hackers Using Steganography Technique to Drop Okrum Backdoor Via PNG File to Evade Detection
Researchers discovered a previously unseen malware called Okrum that distributed from APT15 threat group via a hidden PNG file with steganography technique to...
-

 276News
276NewsTech Companies “Must” Put Backdoors In Encryption, Demands US Attorney General
Encryption has always irked law enforcement agencies and now William Barr, the US General Attorney, has launched a fresh attack against consumer...






