Search results for "Detection"
-

 5.0KMalware
5.0KMalwareNew Malware Targets Windows Subsystem for Linux to Evade Detection
A number of malicious samples have been created for the Windows Subsystem for Linux (WSL) with the goal of compromising Windows machines,...
-

 4.3KCyber Crime
4.3KCyber CrimeThreat actors using CAPTCHA to evade phishing, malware detection
According to researchers, cybercriminals are abusing legitimate challenge and response services like Google’s reCAPTCHA or deploying customized fake CAPTCHA-like validation. Palo Alto...
-
 2.3KMalware
2.3KMalwareNew Malware Family Using CLFS Log Files To Evade Detection
Cybersecurity researchers of FireEye’s Mandiant Advanced Practices team have revealed all the details regarding a new malware family that they have detected...
-
 3.8KCyber Attack
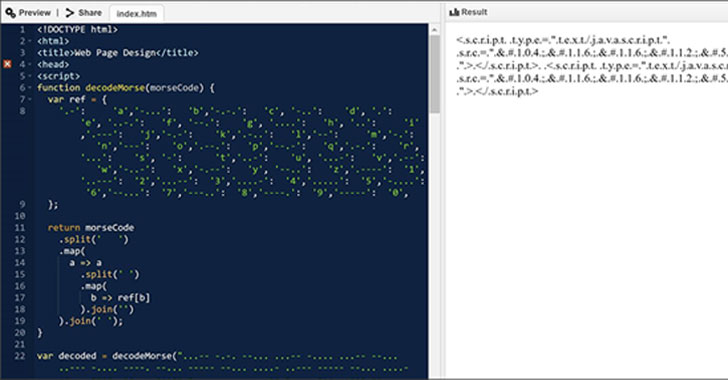
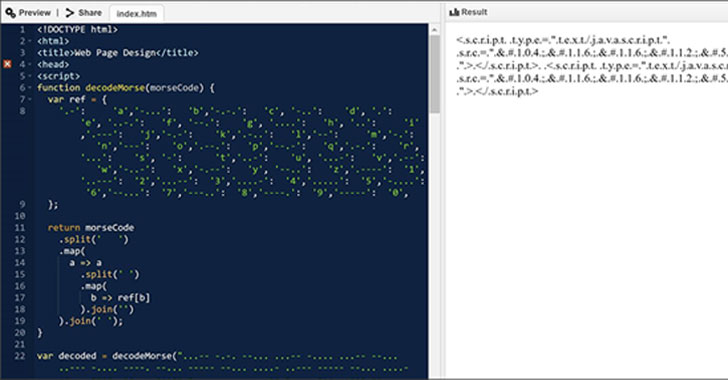
3.8KCyber AttackHackers Spotted Using Morse Code in Phishing Attacks to Evade Detection
Microsoft has disclosed details of an evasive year-long social engineering campaign wherein the operators kept changing their obfuscation and encryption mechanisms every...
-

 1.3KMalware
1.3KMalwareThis New Malware Hides Itself Among Windows Defender Exclusions to Evade Detection
Cybersecurity researchers on Tuesday lifted the lid on a previously undocumented malware strain dubbed “MosaicLoader” that singles out individuals searching for cracked...
-

 3.0KMalware
3.0KMalware[eBook] 7 Signs You Might Need a New Detection and Response Tool
It’s natural to get complacent with the status quo when things seem to be working. The familiar is comfortable, and even if...
-
 2.7KData Breach
2.7KData BreachUsing Breached Password Detection Services to Prevent Cyberattack
Bolstering password policies in your organization is an important part of a robust cybersecurity strategy. Cybercriminals are using compromised accounts as one...
-

 4.9KMalware
4.9KMalwareNew Pingback Malware Using ICMP Tunneling to Evade C&C Detection
Researchers on Tuesday disclosed a novel malware that uses a variety of tricks to stay under the radar and evade detection, while...
-
 792Security Tools
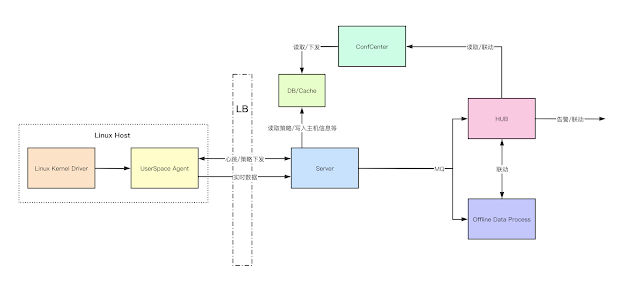
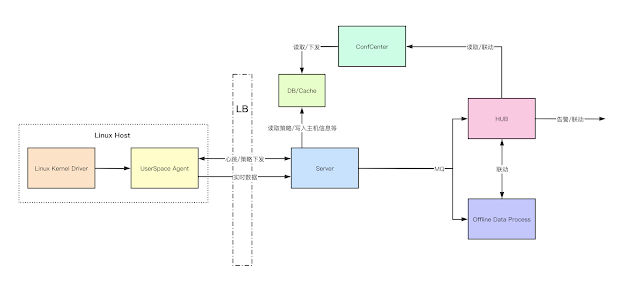
792Security ToolsByteDance-HIDS – Next-Generation Intrusion Detection Solution Project
ByteDance-HIDS is a Cloud-Native Host-Based Intrusion Detection solution project to provide next-generation Threat Detection and Behavior Audition with modern architecture. ByteDance-HIDS...
-

 4.0KData Security
4.0KData SecurityNew phishing technique uses advanced obfuscation and Telegram channels to evade detection. Hackers can easily bypass your firewall
The specialized team FireEye Email Security has published a report on the detection of multiple phishing campaigns in which operators use source...
-

 1.7KRansomware
1.7KRansomwareHackers Abuse Windows Feature To Launch WastedLocker Ransomware to Evade Detection
Recently one of the most dangerous ransomware, WastedLocker, owes its success to a unique bypass mechanism for security solutions and tools that...
-
 5.5KPhishing
5.5KPhishing16Shop – Malware-as-a-service Phishing Toolkit Attack PayPal Users With Anti-Detection Techniques
A prolific phishing kit distribution network dubbed “16Shop” believed to be active since 2018 and developed by a hacking group called the...
-
 5.4KHack Tools
5.4KHack ToolsAttack Monitor – Endpoint Detection And Malware Analysis Software
Attack Monitor is Python application written to enhance security monitoring capabilites of Windows 7/2008 (and all later versions) workstations/servers and to automate...
-
 1.5KHack Tools
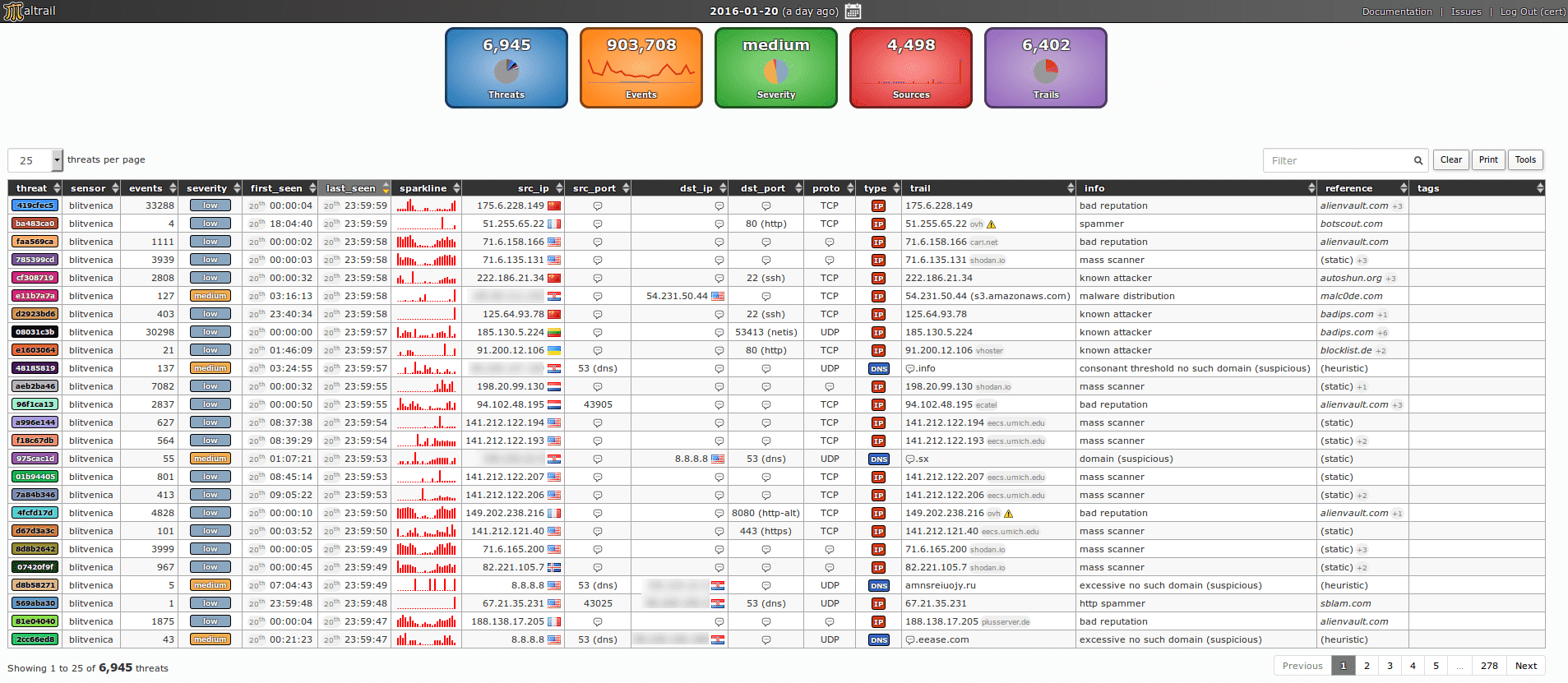
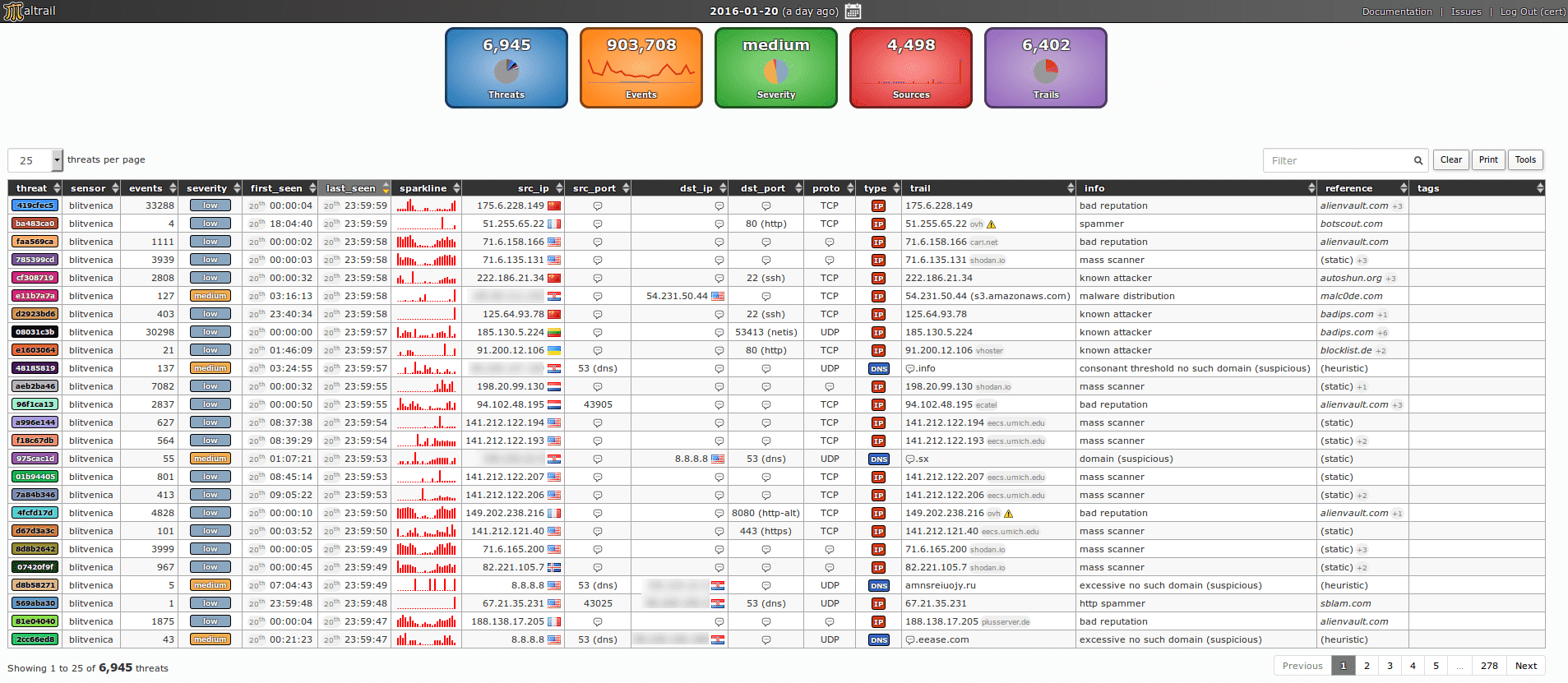
1.5KHack Toolsmaltrail v0.16.69 releases: Malicious traffic detection system
Maltrail is a malicious traffic detection system, utilizing publicly available (black)lists containing malicious and/or generally suspicious trails, along with static trails compiled from...
-

 1.4KHack Tools
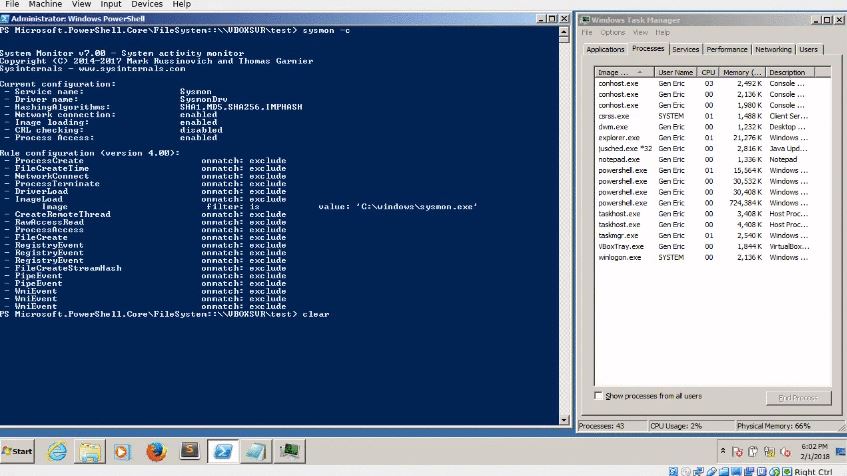
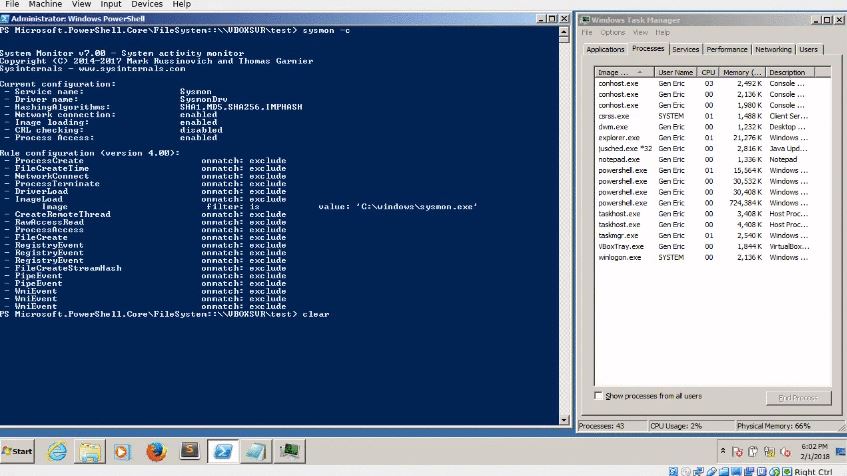
1.4KHack ToolsDetectionLab – Vagrant And Packer Scripts To Build A Lab Environment Complete With Security Tooling And Logging Best Practices
DetectionLab is tested weekly on Saturdays via a scheduled CircleCI workflow to ensure that builds are passing. PurposeThis lab has been designed...
-

 3.6KHack Tools
3.6KHack ToolsSigma Hunting App: containing Sigma detection rules
Sigma Hunting App A Splunk App containing Sigma detection rules, which can be updated dynamically from a Git repository. Motivation Most of...
-
 535Firewall
535FirewallWhids – Open Source Endpoint Detection System for Windows
This is an hybrid solution combining a flexible Host IDS with detection based Incident Response capabilities. The detection engine is built on...
-
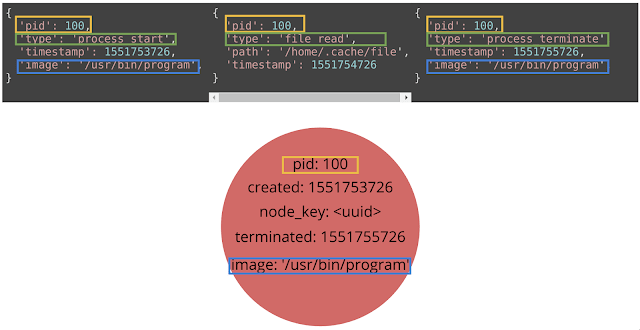
Security Tools
Tylium – Data for Intrusion Detection, Security Analytics and Threat Hunting
These files contain configuration for producing EDR (endpoint detection and response) data in addition to standard system logs. These configurations enable...
-
 609Malware
609MalwareFIN7 APT Hackers Added New Hacking Tools in Their Malware Arsenal to Evade AV Detection
Researchers discovered 2 new hacking tools called BOOSTWRITE and RDFSNIFFER that were added in FIN7 groups malware arsenal with sophisticated capabilities and...
-
 357Data Security
357Data SecurityMasterMana botnet hits users by evading detection with URL shorteners
MasterMana botnet is part of an ongoing malware campaign. The IT security researchers at Prevailion have discovered an active botnet that has...
-
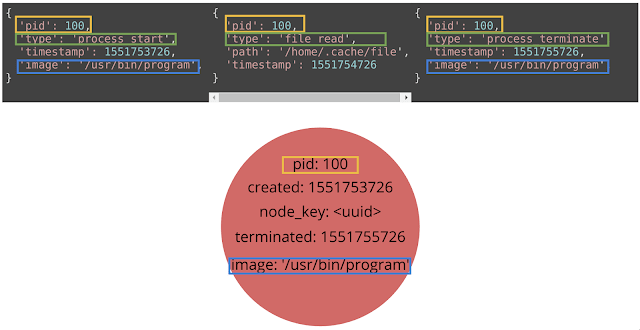 357System Administration
357System AdministrationGrapl – Graph Platform For Detection And Response
Grapl is an open source platform for Detection and Response (D&R). The position that Grapl takes is that Graphs provide a...






