Search results for "Detection"
-

 101Vulnerabilities
101VulnerabilitiesMicrosoft seeks testers for ‘Project Springfield’ bug-detection service
Microsoft is planning to make its internally-used ‘white-box fuzzing’ bug-detection service available to external customers and partners. Microsoft is looking for testers...
-

 101Malware
101MalwareMALWARE EVADES DETECTION WITH NOVEL TECHNIQUE
Researchers have found a new strain of document-based macro malware that evades discovery by lying dormant when it detects a security researcher’s...
-

 326Incidents
326IncidentsMatchlight Dark Web data leak detection software available worldwide
Terbium Labs’ software can now be used to detect when data belonging to companies is being flogged in the underground. Terbium Labs...
-

 229Geek
229GeekMedical Detection Goes High Tech
Interscatter Communication May Re-Define how Chronic Diseases are Managed — Benign everyday medical devices to communicate with smart tech to aid in ailment...
-
 190Firewall
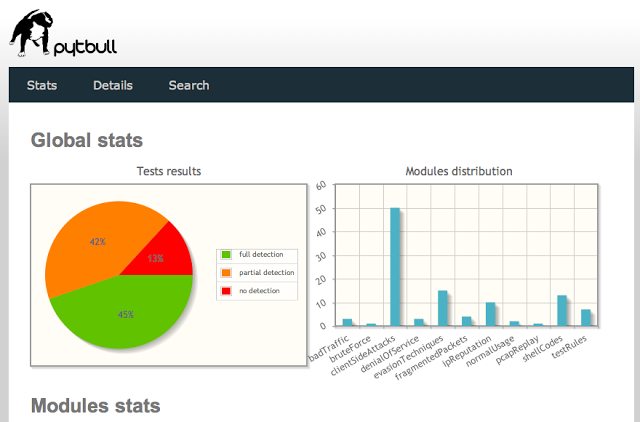
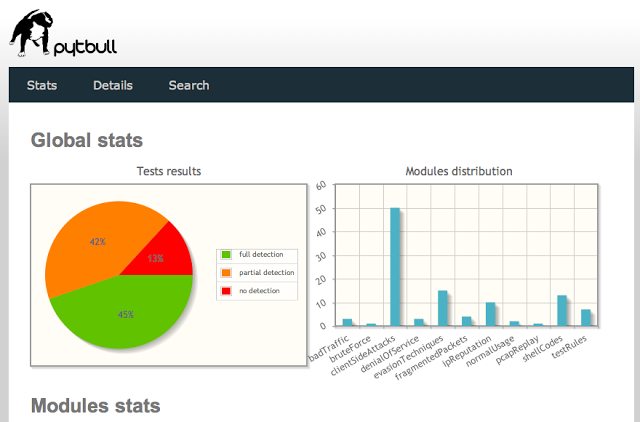
190Firewallpytbull – Intrusion Detection/Prevention System (IDS/IPS) Testing Framework
pytbull is an Intrusion Detection/Prevention System (IDS/IPS) Testing Framework for Snort, Suricata and any IDS/IPS that generates an alert file. It can...
-

 113Data Security
113Data SecurityIrongate malware targets industrial systems, avoids detection
The unusual malware has been specifically designed to target the core systems cities rely on. A new family of malware has been developed...
-
 93Malware
93MalwareDorkbot: 5 years since detection
In the half-decade that has lapsed since Dorkbot was first identified, millions of innocent victims, going about their everyday business, have been...
-

 173Data Security
173Data SecurityNew self-protecting USB trojan able to avoid detection
A unique data-stealing trojan has been spotted on USB devices in the wild – and it is different from typical data-stealing malware. Each...
-

 363Malware
363MalwareNew self‑protecting USB trojan able to avoid detection
A unique data-stealing trojan has been spotted on USB devices in the wild – and it is different from typical data-stealing malware,...
-

 190Vulnerabilities
190VulnerabilitiesVXE Flaw allowed threats to bypass FireEye detection engine
Researchers at Blue Frost Security firm discovered a flaw in the FireEye Virtual Execution Engine (VXE) that allows an attacker to completely...
-

 92Data Security
92Data SecurityTrochilus RAT Evades Antivirus Detection, Used for Cyber-Espionage in South-East Asia
A new type of RAT (Remote Access Trojan) has been discovered in use against governments and civil society organizations in South-East Asia,...
-

 78Data Security
78Data SecurityAuthors digitally signed Spymel Trojan to evade detection
Zscaler ThreatLabZ detected a new infostealer malware family dubbed Spymel that uses stolen certificates to evade detection. In late December, security experts...
-

 92Malware
92MalwareGlassRAT Zero-Detection Trojan Targets Chinese Nationals
A previously undetectable remote administration tool has been uncovered, dubbed “GlassRAT” The zero-detection Trojan appears to have operated stealthily for three years,...
-

 109Data Security
109Data SecurityNew Moker RAT Bypasses Detection
Researchers warned Tuesday the latest APT to make the rounds features a remote access Trojan that can effectively mitigate security measures on machines and grant...
-

 282Hacked
282HackedLaika BOSS: Lockheed Open Sources Secret Cyber Threat Detection Weapon
Short Bytes: Lockheed Martin has decided to open source its secret cyber threat detection tool Laika BOSS at the Black Hat Conference...
-

 439Malware
439MalwareAdvanced Persistent Threats: Using multi‑layered detection to defend against APTs
Advanced persistent threats (APTs) are a growing concern to the world's companies and networks. This recorded webinar looks at real-world data breaches...
-
 230Geek
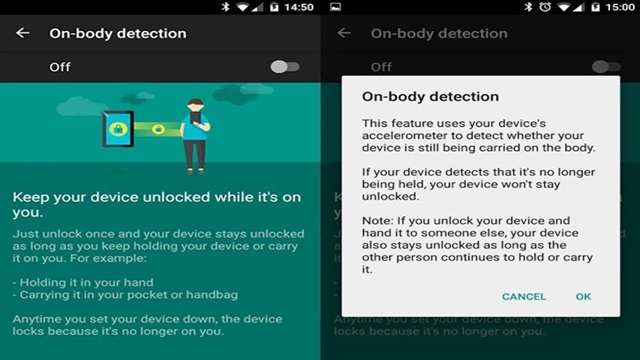
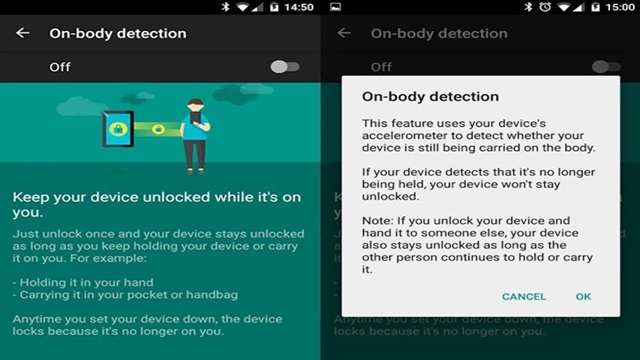
230GeekAndroid On-Body Detection Feature Will Keep Your Phone Safe From Thieves
The new on-body detection feature will lock your phone when you set it down, so thieves who swipe it can’t access your...
-

 99Malware
99MalwareFuture malware might offer real functions to avoid detection
Malware may begin to offer genuinely helpful functionality in the future, in order to "fly under the radar" and fake legitimacy before...
-
 109Malware
109MalwareESET response to Bits of Freedom open letter on detection of government malware
A coalition of digital rights organizations and academics recently published an ‘open letter’ to the Anti-Malware/Anti-Virus industry asking for clarification on vendor...
-
Android
Carrier IQ detection: check your source before you install
Android-specific software that checks for Carrier IQ could create an unanticipated problem.






