Search results for "Hidden"
-

 609Cyber Attack
609Cyber AttackTwo New Malware Linked To Hidden Cobra Hackers- FBI Issues Alert
The US-CERT issued a joint technical alert from DHS and the FBI, warning that two new identified malware has been used by...
-

 293Malware
293MalwareHIDDEN COBRA – A North Korean Hacking Group Attack in Wide using Powerful RAT & SMB Worm -Warned DHS & FBI
HIDDEN COBRA is one of the well known hacking group who is behind the North Korean government spreading Powerful Joanap Backdoor and Brambul...
-
 229Cryptocurrency
229CryptocurrencyUbuntu Snap Store Apps Contains Hidden Cryptocurrency Miner Malware
An Ubuntu user identified a malicious code that mines Bytecoin (BCN) hidden in the source code of the Ubuntu snap package (2048buntu...
-

 156Malware
156MalwareBackdoor hidden in the npm JavaScript package
According to researchers, the node’s Packet Manager (npm) team just avoided a disaster when it discovered and blocked the distribution of a...
-

 356Cryptocurrency
356CryptocurrencyHiddenminer – Android Monero Mining Malware Can Overheat and Cause Device Failure
A new Monero Mining Android malware dubbed ANDROIDOS_HIDDENMINER that uses the device CPU power to mine Monero malware and could cause the...
-

 336Geek
336GeekHiddenMiner Android Monero Mining Malware Cause Device Failure
Another day, another Android malware – This time, the malware not only comes with Monero mining capabilities but its continuous mining process...
-
 198Privacy
198PrivacyHey Siri! Read me this locked iPhone’s hidden messages…
Messages sent to your iPhone may not be as private as you think.
-

 202Hacked
202HackedHidden For 6 Years, ‘Slingshot’ Malware Hacks Your PC Through Your Router
The researchers at Kaspersky Labs have uncovered a malware, dubbed Slingshot, that has been able to hide for around six years. While...
-

 410Malware
410MalwareWith New Bankshot Malware Cybercrime Group Hidden Cobra Targets Financial Sectors
Hidden Cobra cybercrime group continues to target multiple industries and financial sectors. With this new aggressive campaign, the group implanted Bankshot malware...
-
Lists
12 Android Oreo Hidden Features You Can Try
Although I have a special place in my heart for this mobile operating system, I won’t say I am aware of every hidden...
-
 411Lists
411Lists5 Hidden Tips and Tricks for Google Chrome On Android
Google Chrome comes as a default browser installed on most Android phones. It is fast, responsive and comes with all the basic...
-

 207Cryptocurrency
207CryptocurrencyHidden Cryptocurrency Miner Coinhive’s Rapid Growth and it’s Prevention Techniques
It is very usual these days to find many applications having a hidden crypto-mining module. But the recent trend is more mainstream...
-
 302Hacked
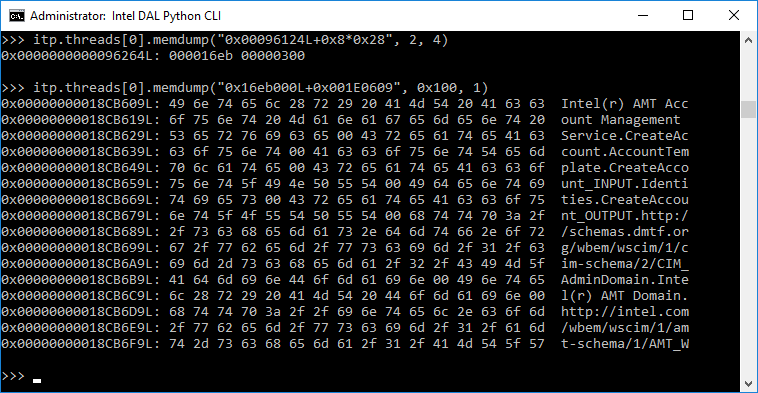
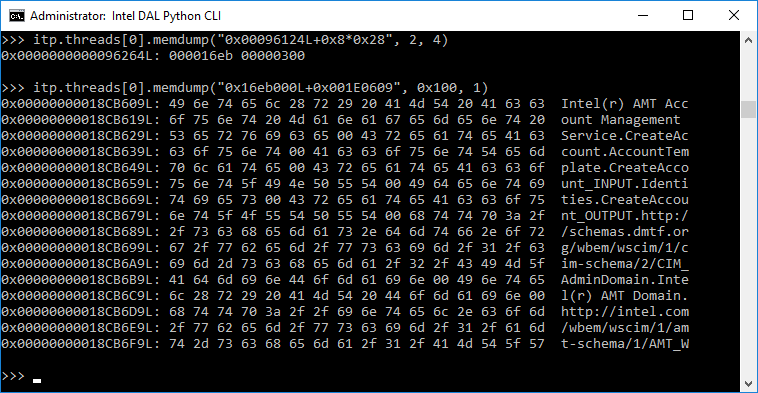
302Hacked“Game Over!” — Intel’s Hidden, MINIX-powered ME Chip Can Be Hacked Over USB
Even the creator of MINIX operating system didn’t know that his for-education operating system is on almost every Intel-powered computer. He is okay...
-

 108Incidents
108IncidentsSomeone Created a Tor Hidden Service to Phish my Tor Hidden Service
SMS Privacy is available as a Tor hidden service, and it turns out ~10% of users actually use it that way. This post...
-

 286How To
286How ToHow To Enable Hidden iOS 11 “Dark Mode” On iPhone And iPad?
On September 17, 2017, iOS 11 mobile operating system was released by Apple. The biggest features of iOS 11 included ARKit, improved camera,...
-
 333Geek
333GeekHidden Kill Switch Identified in Controversial Intel ME controller chip
Europe’s leading cyber-security firm Positive Technologies’ security researchers have a bad news for Intel users. They have detected a secret configuration setting...
-
 160Geek
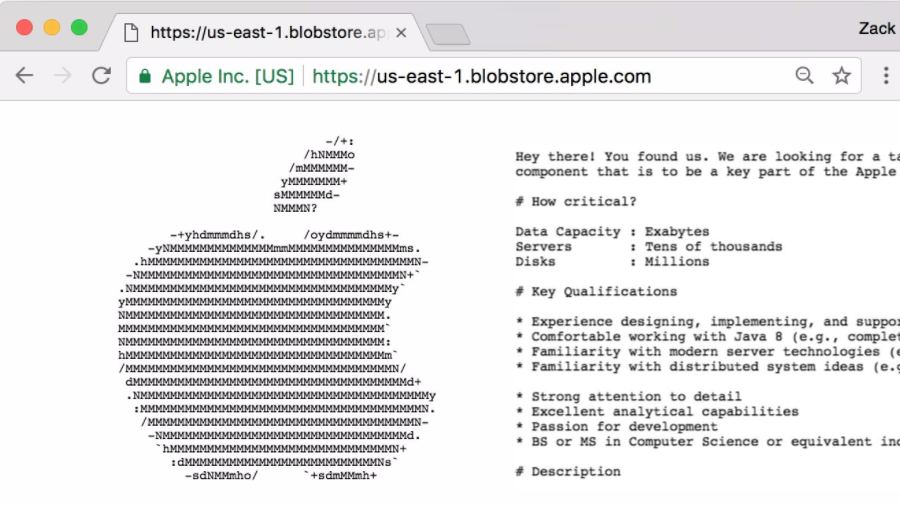
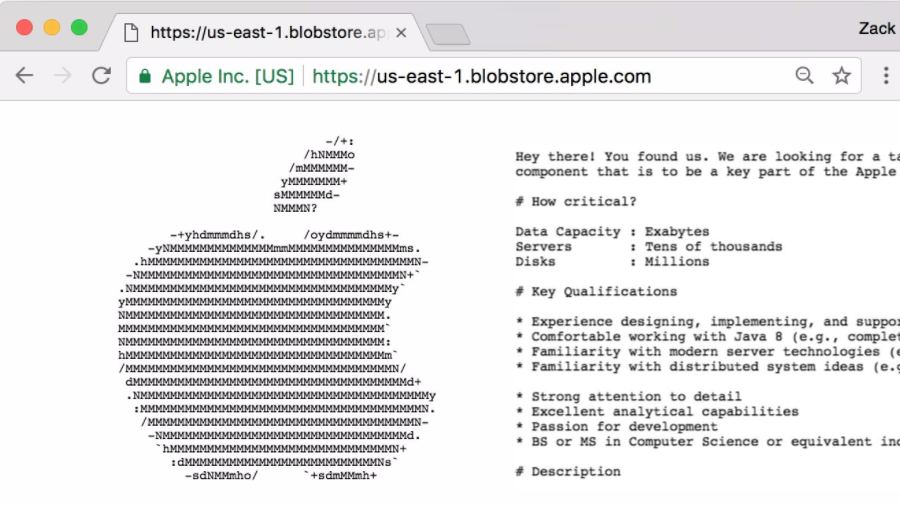
160GeekHey Geeks: Get A Job At Apple By Finding Hidden Postings On Their Website
The biggest tech companies have their rigorous recruitment process to assess the candidates and find if they are suitable for their companies....
-

 328Lists
328Lists11 VLC Tricks & Hidden Features You Must Know
Short Bytes: The name VLC needs no introduction. Although most people perceive it only as a simple media player but hidden beneath...
-

 369Lists
369Lists17 Best Instagram Tricks And Hidden Features You Must Know
Short Bytes: If you love clicking pictures and sharing them with your friends and family, by using some handy Instagram tricks you...
-
 249How To
249How To“Explore Feed”: How To Access Your “Second” And Hidden Facebook News Feed
Short Bytes: Apart from your main News Feed, Facebook offers an option to access a second and hidden feed in its Android...
-

 98How To
98How ToCreating a Hidden Service via Tor for Beginners
Creating a website is pretty simple. Creating a hidden service via Tor isn’t much different. In fact, if you have any semblance...






