Search results for "Hidden"
-
 104Data Security
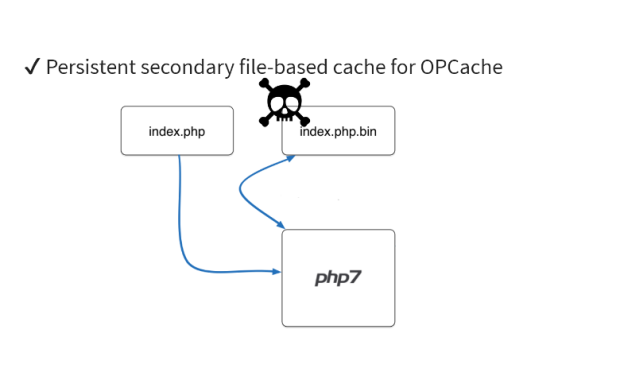
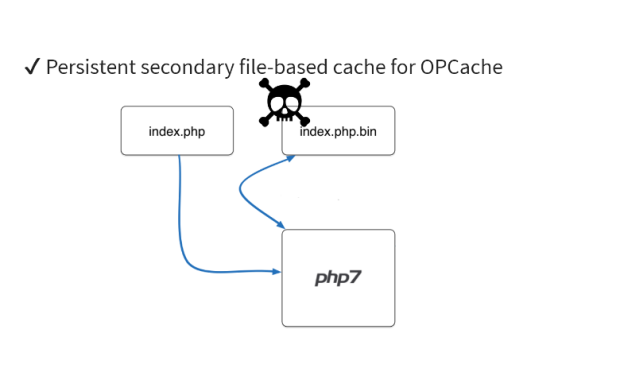
104Data SecurityDetecting Hidden Backdoors in PHP OPcache
In this article, we will be looking at the strategies to detect and analyze malware hidden inside an OPcache file. If you...
-

 264How To
264How ToHow To Create A Hidden User Administrator Account On Windows 10
Short Bytes: Using a hidden user administrator account on Windows 10, you can ensure the privacy of your personal data very easily....
-

 210Data Security
210Data SecurityViber adds end-to-end encryption and hidden chats as messaging app privacy wave grows
Following WhatsApp’s move to add end-to-end encryption to its platform, another big messaging company is joining the wave of apps turning on expanded privacy features.Viber...
-
 153Malware
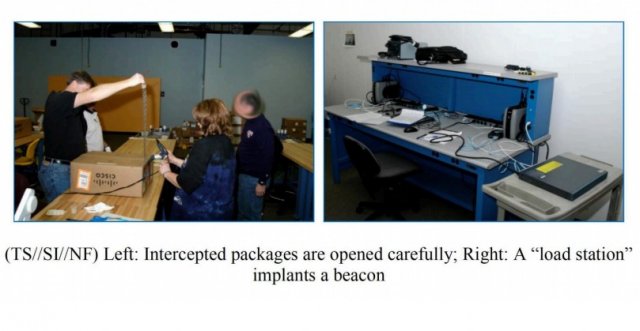
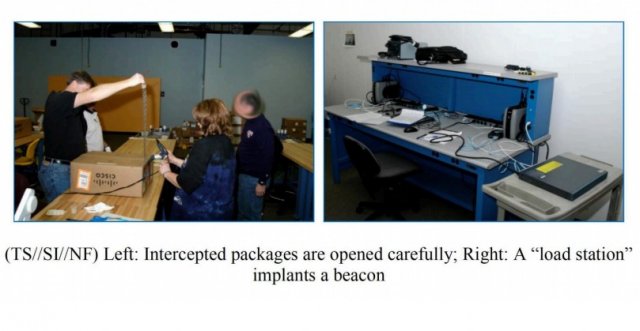
153MalwarePhotos Show How NSA Implants Trojan In Routers For Hidden Access And Spying
ShortBytes: In a recent find out, it has been revealed how NSA implants trojan firmware in the networking devices being delivered to...
-
 213Data Security
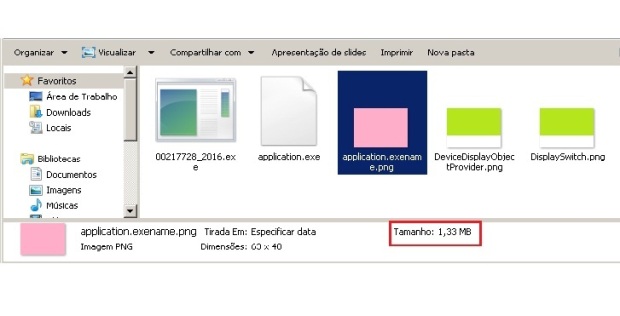
213Data SecurityPNG Embedded – Malicious payload hidden in a PNG file
One of the most complex tasks for the cybercriminals is to ensure their malicious code goes undetected by antivirus and achieves its...
-
 107Data Security
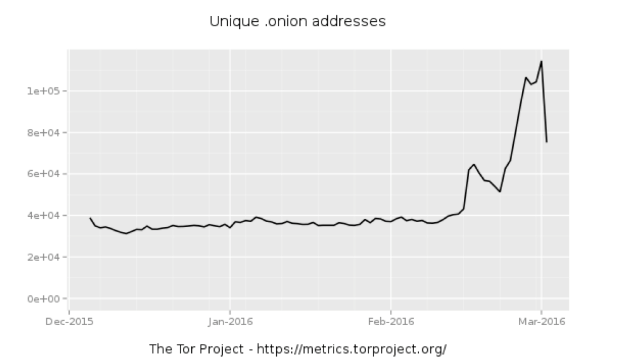
107Data SecurityWhole lotta onions: Number of Tor hidden sites spikes—along with paranoia
What’s driving the surge in hidden services—is it government tampering? In recent weeks, the number of “hidden services”—usually Web servers and other Internet...
-

 173Data Security
173Data SecurityAre Hackers Keeping a Hidden Stash on Your HP Printer’s Hard Drive?
Unprotected HP printer HDDs can be abused if not protected. Security researcher Chris Vickery has discovered that HP LaserJet printers may be abused...
-
 163Incidents
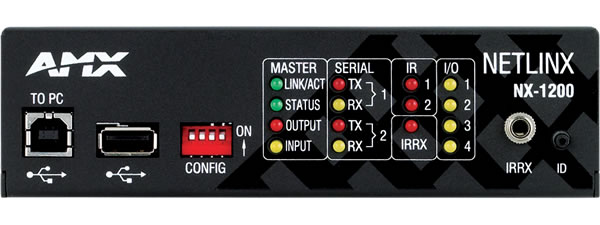
163IncidentsMedia devices sold to feds have hidden backdoor with sniffing functions
Highly privileged account could be used to hack customers’ networks, researchers warn. A company that supplies audio-visual and building control equipment to...
-

 296How To
296How ToHow To Unlock Google Maps’ New Hidden Driving Mode
Short Bytes: Call it a bug or an updated feature of the Google maps, now with the updated version of Google maps,...
-

 201Tricks & How To's
201Tricks & How To'sUnlock Netflix’s hidden categories with these secret codes
Here’s a trick that’s been around for a while but may have passed you by: secret category codes added by Netflix engineers...
-

 128Data Security
128Data SecurityHow to Hack TOR Hidden Services
A lot of people think that TOR services are unhackable because they are on a “secure environment”, but the truth is that...
-
 314Vulnerabilities
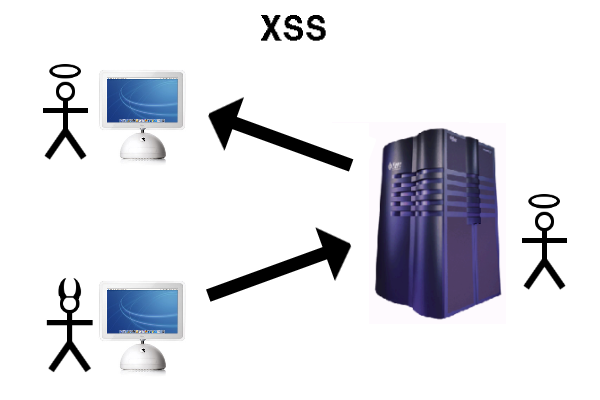
314VulnerabilitiesXSS in Hidden Input Fields
At PortSwigger, we regularly run pre-release builds of Burp Suite against an internal testbed of popular web applications to make sure it’s...
-
 145Vulnerabilities
145VulnerabilitiesChrome for Android Has a Hidden Vulnerability, Quite Simple to Exploit
Google’s Chrome staff got in contact with the security researcher and has already started working on a fix A Chinese security researcher...
-

 76Data Security
76Data SecurityHIDDEN IN PLAIN SIGHT: BRUTE FORCING SLACK PRIVATE FILES
Last year we switched to using Slack for all our internal communication and it’s working out nicely. It’s very developer centric in...
-

 178Malware
178MalwareMalware Is Using the Dark Web to Stay Hidden
The dark web is well known as a space where anything can be bought or sold: guns, drugs, stolen data, and extreme...
-
 122Malware
122MalwareIntelligent system to check malware hidden in shortened Twitter URLs
Tool to check malware in Twitter URLs to be tested during European Football Championships next summer. An intelligent system has been created...
-

 125Incidents
125IncidentsPorn sites hit by malware hidden in adverts
Security firm Malwarebytes says a campaign of malware hidden inside online ads which hit search engine Yahoo earlier this year has now...
-

 207Geek
207GeekAndroid Ransomware Hidden Behind Fake Pornography App
Android is one of the most vulnerable OS in the world — If you are an Android user you need to be...
-
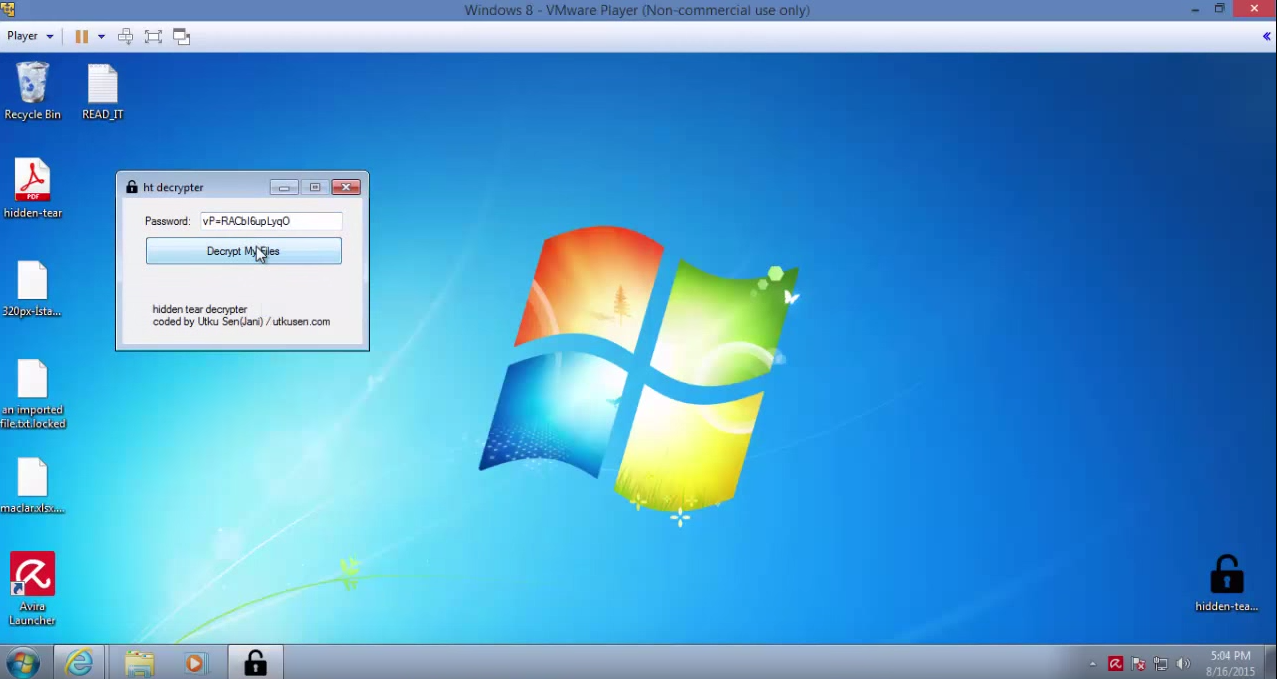
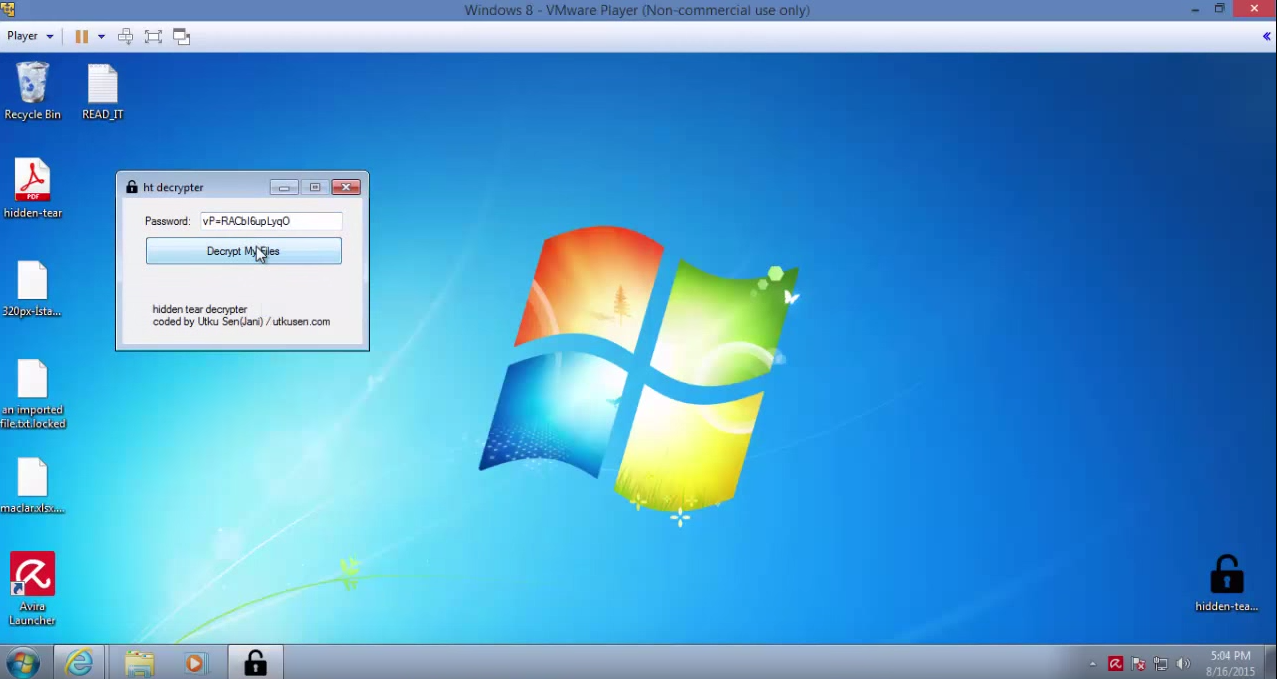 163How To
163How ToHidden Tear – Ransomware-like file crypter
Uses AES algorithm to encrypt files. Sends encryption key to a server. Encrypted files can be decrypted in decryption program with encryption...
-

 105Malware
105MalwareHidden password-stealing malware lurking in your GPU card? Intel Security thinks not
Fears that malware is hiding in people’s graphics chipsets may be overclocked, according to Intel Security. Earlier this year, researchers from the...
-

 166Vulnerabilities
166VulnerabilitiesPatched Ins0mnia Vulnerability Keeps Malicious iOS Apps Hidden
Apple’s monster security update of Aug. 13 included a patch for an iOS vulnerability that could beacon out location data and other...






