Search results for "Hidden"
-
 204Hackers Repository
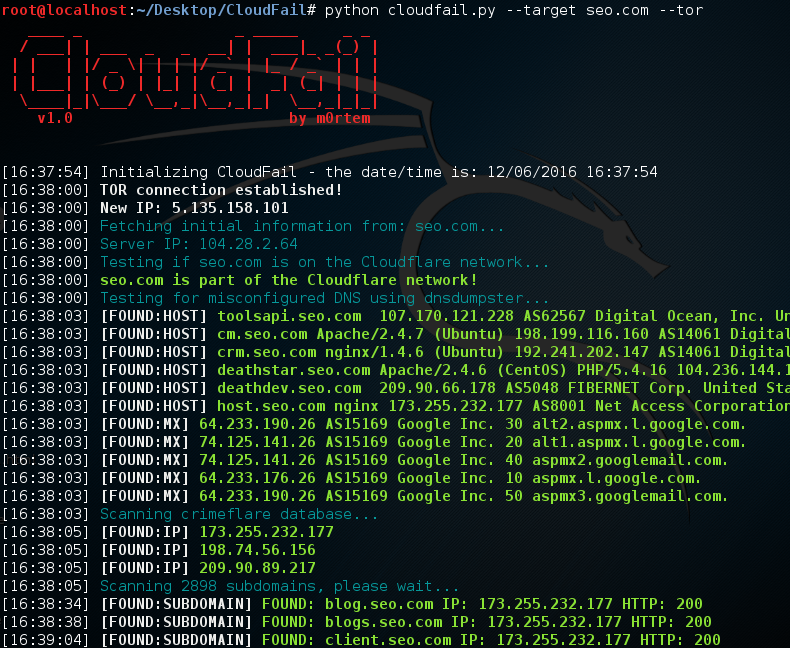
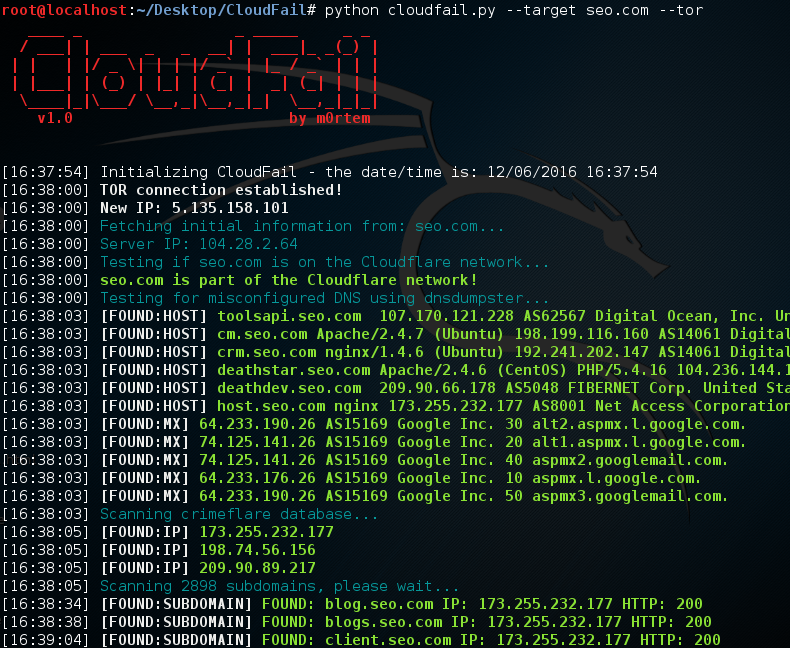
204Hackers RepositoryCloudFail – Utilize misconfigured DNS Find hidden IP’s behind the CloudFlare network
CloudFail Credits: m0rtem CloudFail is a tactical reconnaissance tool which aims to gather enough information about a target protected by CloudFlare in...
-
 257Hackers Repository
257Hackers RepositoryHacking TOR Hidden Services
Hacking TOR Hidden Services What is Tor ? Tor stands for The Onion Route it aims to conceal its users identities and...
-

 116Geek
116Geek10 Android Developer Options Hidden Features For Advanced Users
Short Bytes: At some point, you would have owned an Android device, but have you ever managed to scratch the surface of its...
-

 159Incidents
159IncidentsRansomware hidden inside a Word document that’s hidden inside a PDF
SophosLabs has discovered a new spam campaign where ransomware is downloaded and run by a macro hidden inside a Word document that is...
-

 205Hacked
205HackedCreate TOR’s Hidden .Onion URL Of Any Site With Free EOTK Tool
Short Bytes: Want to create Tor’s hidden .onion URL of a website? A free tool named Enterprise Onion Toolkit (EOTK) can help you...
-

 264Lists
264ListsAndroid Smart Lock: 8 Hidden Ways To Unlock Your Android Smartphone
Short Bytes: Google’s Smart Lock includes various methods to unlock an Android device. You can use voice recognition, facial recognition or a...
-
 100Malware
100MalwareHidden backdoor discovered in Chinese IoT devices
Researchers at Trustwave have uncovered a backdoor in IoT devices from a Chinese manufacturer that could leave them open to exploitation. The...
-

 169How To
169How ToAccess Hidden TV Shows And Movies On Netflix
-

 287How To
287How ToSteghide – Tool To Find Hidden Information And Password In A File
Steghide, is a tool that executes a brute force attack to file with hide information and password established. Linux operating system Steghide Python...
-
 224Backdoors
224BackdoorsBackdoorMan – Toolkit That Helps You Find Malicious, Hidden And Suspicious PHP Scripts And Shells
A Python open source toolkit that helps you find malicious, hidden and suspicious PHP scripts and shells in a chosen destination, it...
-

 154Data Security
154Data SecurityFBI operated 23 Tor-hidden child porn sites, deployed malware from them
Researcher: FBI was likely enabled to run half of all child porn sites on the servers. As Ars has reported, federal investigators temporarily...
-

 392Lists
392Lists15 Hidden Features in Facebook Messenger You Might Not Know
Short Bytes: Messenger is a popular instant messaging platform. It supports text messaging, voice, and video calls. People can also send photos,...
-
 208How To
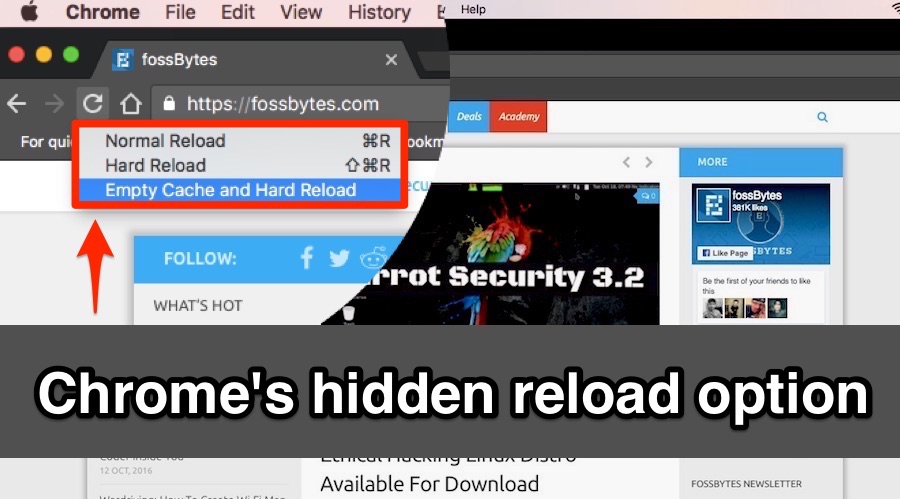
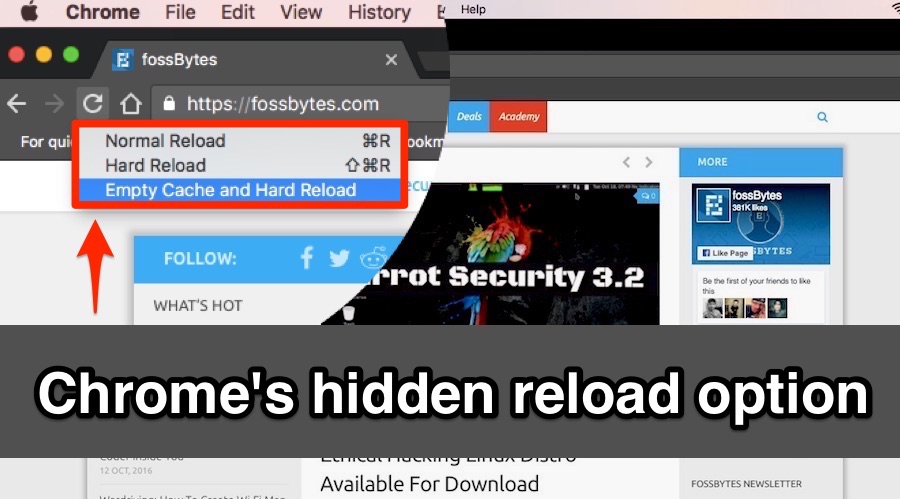
208How ToChrome’s Hidden Reload Menu: “Normal Reload”, “Hard Reload”, and “Empty Cache”
Short Bytes: Do you know about the “Normal Reload”, “Hard Reload”, and “Empty Cache with Hard Reload” option in your web browser? These...
-
 246Geek
246Geek10 Signs That Show There’s A Hidden Coder Inside You
Short Bytes: What are the signs that you should look for before joining a coding class? Apart from the love for programming,...
-
 252Incidents
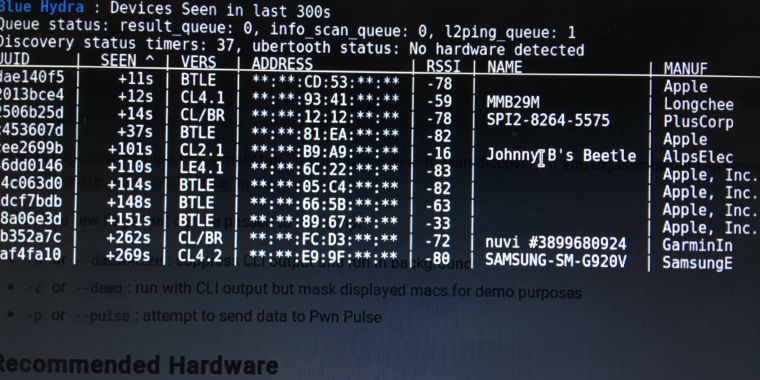
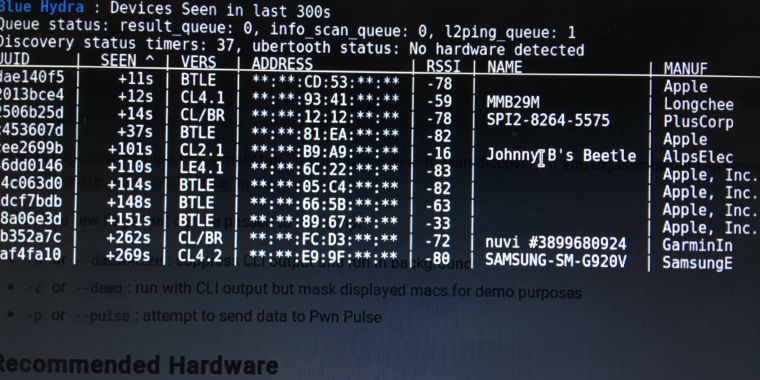
252IncidentsHands-on: Blue Hydra can expose the all-too-unhidden world of Bluetooth
Bluetooth Low Energy devices like smart watches, “wearables,” give you up all day. My new neighbor was using AirDrop to move some files...
-
 188Data Security
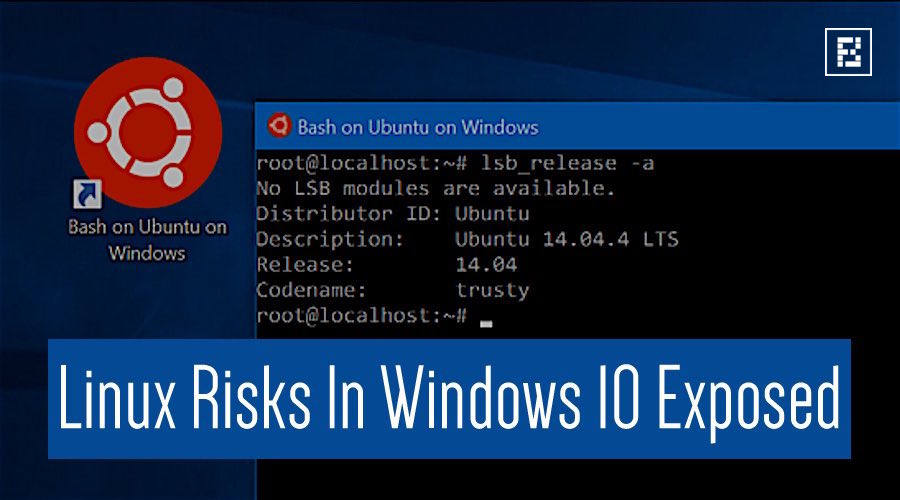
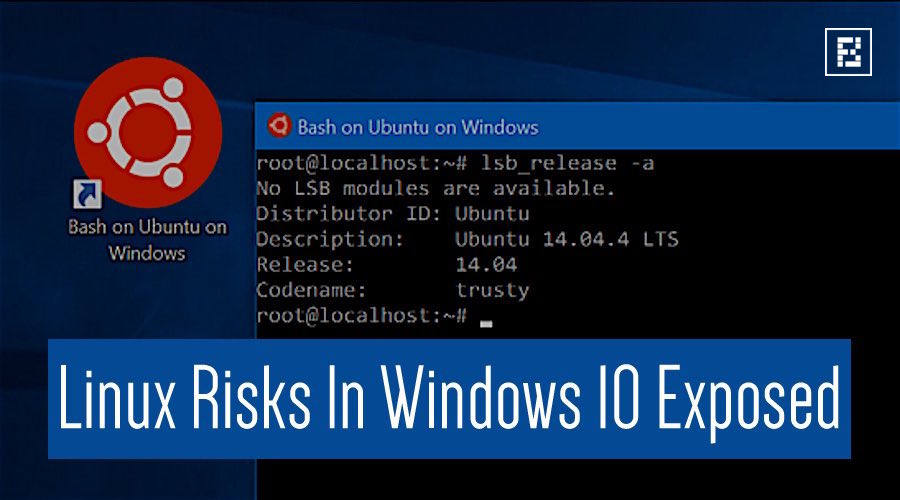
188Data SecurityRisk From Linux Kernel Hidden in Windows 10 Exposed at Black Hat
LAS VEGAS–Microsoft’s Windows 10 includes many innovative security features that are intended to help minimize risk and improve user experience. One such...
-
 195Hacked
195HackedIs Hidden Linux Subsystem In Windows 10 Making Your PC Unsafe?
Short Bytes: A security researcher has claimed that the newly-introduced Linux subsystem in Windows 10 could prove to be a risky affair by...
-

 314Hacked
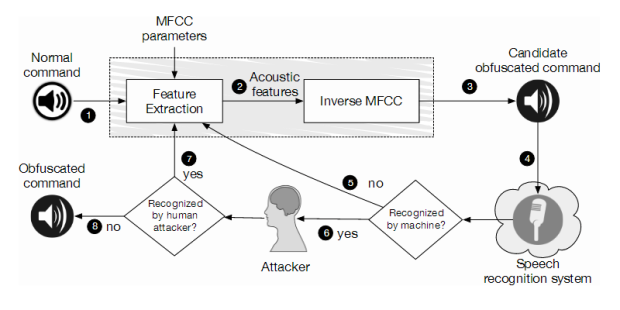
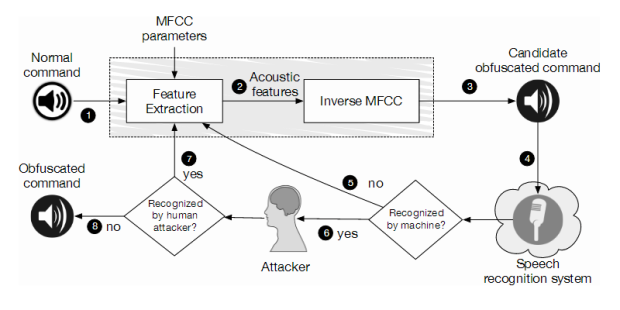
314HackedVoice Commands Hidden In YouTube Videos Can Hack Your Smartphone
Short Bytes: A combined research has been conducted by UC Berkeley and Georgetown University to demonstrate how distorted voice commands hidden in YouTube...
-
 218Incidents
218IncidentsHidden Voice Commands Embedded in YouTube Videos Can Hijack Your Smartphone
Some attacks are hard to spot even by human subjects. A series of distorted voice commands surreptitiously hidden in YouTube videos can force...
-

 247How To
247How ToHow To Play Facebook Messenger’s New And Hidden Football Game
Short Bytes: Thanks to Euro 2016 season, Facebook has rolled out a new easter egg in the form of Messenger Football. All...
-
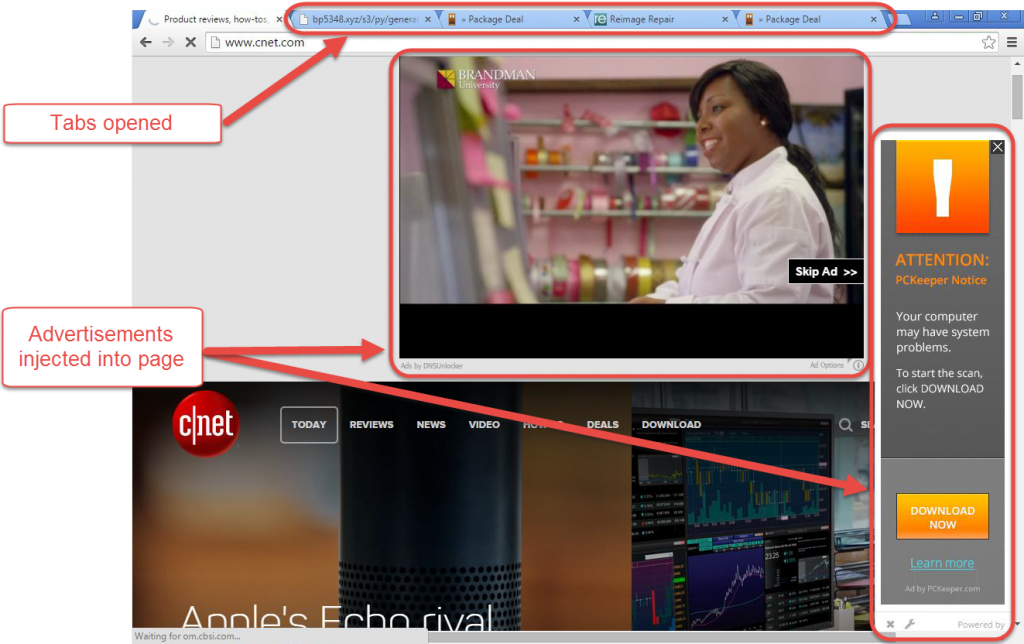
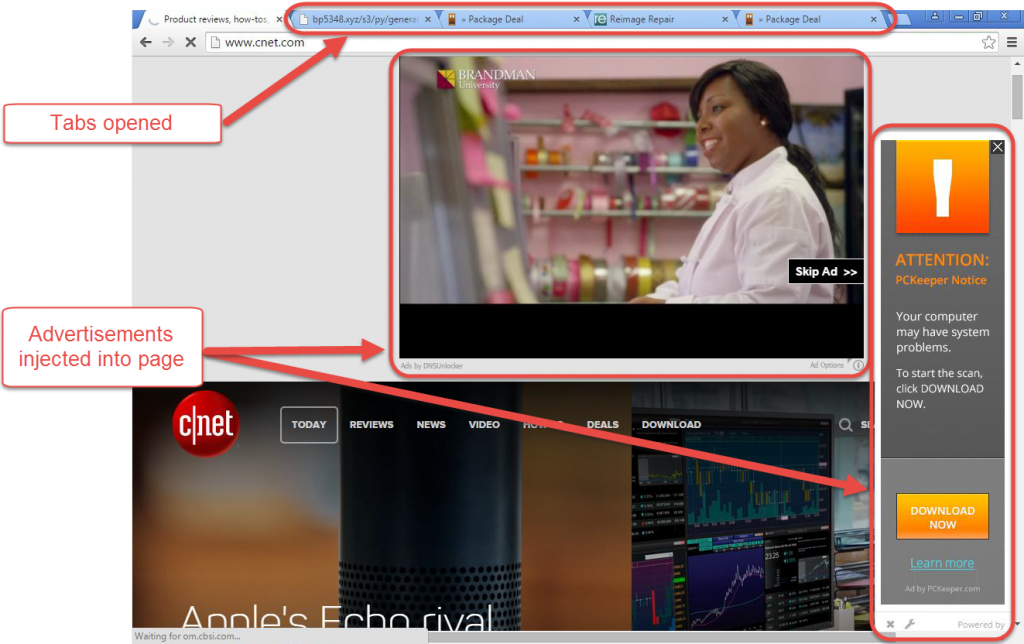 2.3KMalware
2.3KMalwareCrouching Tiger, Hidden DNS
An interesting DNS hijack that sets the victim's computer to use specific DNS servers has emerged. Here are the key details of...






