Search results for "Hidden"
-
 4.9KHack Tools
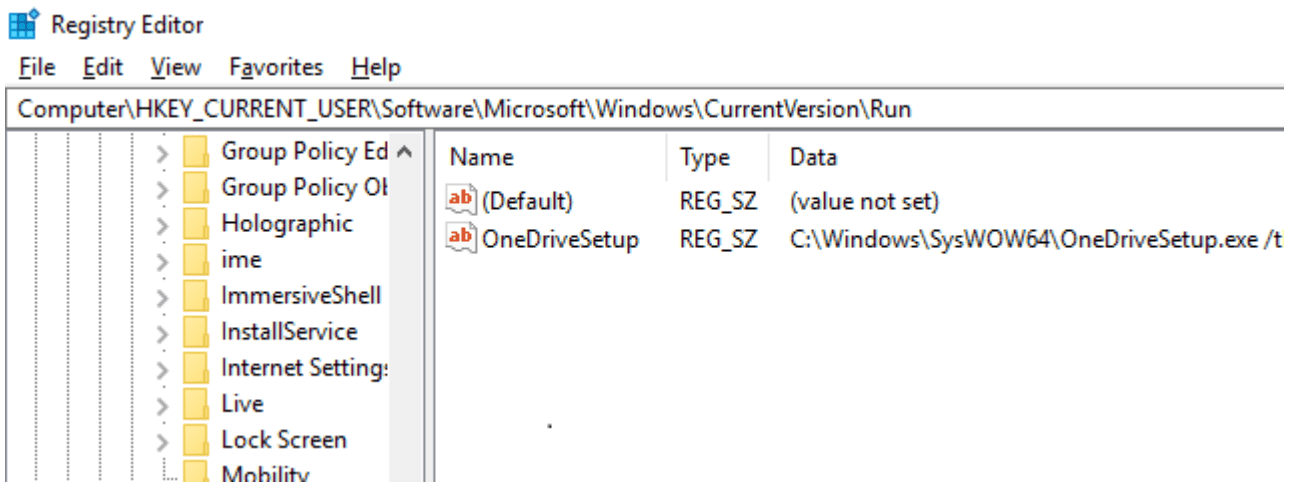
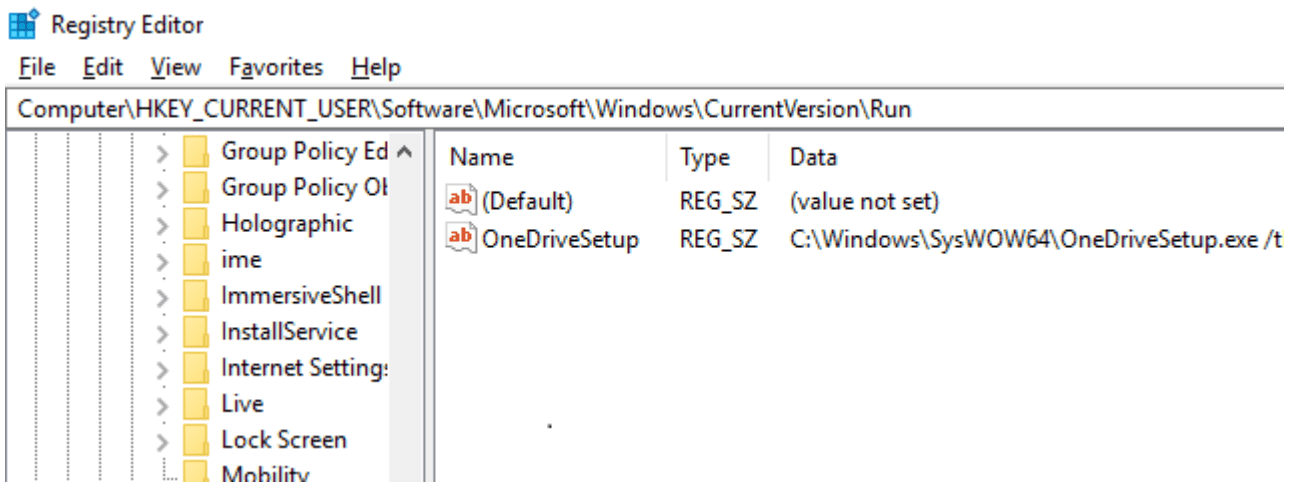
4.9KHack ToolsSharpHide: Tool to create hidden registry keys
SharpHide Just a nice persistence trick to confuse DFIR investigation. Uses NtSetValueKey native API to create a hidden (null-terminated) registry key. This...
-
 854Malware
854MalwareTitanium APT Hackers Inject New Hidden Backdoor on Windows Using Fileless Technique
A new wave of malware attack strikes again from the Titanium APT group that infects windows with hidden backdoor by mimicking common...
-
Cryptography and Encryption
FOCA – Find Metadata And Hidden Information In The Documents
FOCA (Fingerprinting Organizations with Collected Archives)FOCA is a tool used mainly to find metadata and hidden information in the documents it...
-

 526Lists
526Lists11 ‘Hidden’ Android 10 Features We Have Found So Far
The latest Android version has been out for more than a week now, and many of us are working hard to find...
-

 414Infosec
414InfosecShodan and Censys: Finding Hidden Parts On the Internet With Special Search Engines
Our digital lives connect massive things with the Internet. Starting with Smartphones, Wi-Fi routers, Surveillance Camera, Smart TV, SCADA networks and leading...
-

 285Hacked
285HackedThis Innocent USB Charger Is A Hidden Surveillance Camera No One Can See
To tackle uninvited burglars and other intrusions, many people resort to installing closed-circuit TV cameras in their homes. But the problem with...
-

 377Tutorials
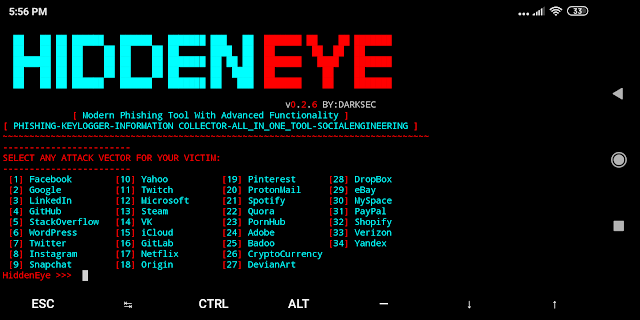
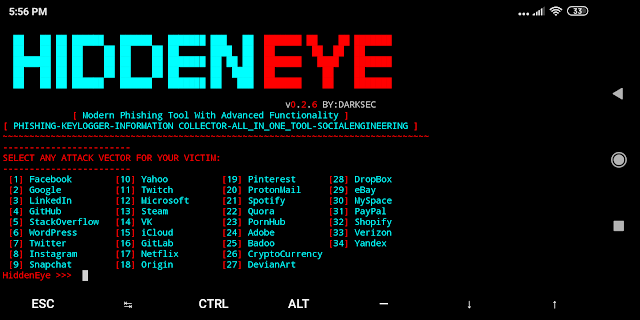
377TutorialsHack your friends Facebook account using HiddenEye
Phishing is what mostly victims fall into trap of fake pages. There are many of methods for creating fake pages. Phishing is...
-
 342Phishing
342PhishingHidden Eye – Modern Phishing Tool With Advanced Functionality
Ultimate Phishing tool with android support available comes with 34 attack vectors of the most popular used services. Hidden Eye Modern Phishing...
-
 277News
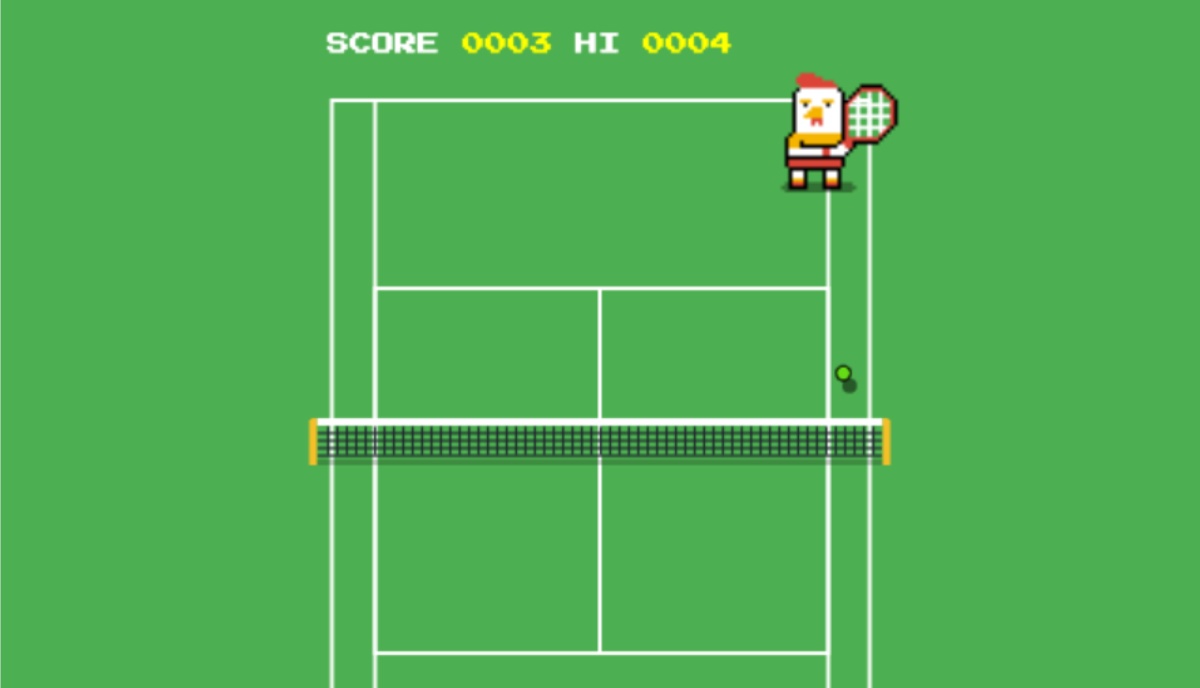
277NewsHow To Play The Hidden ‘Tennis Game’ On Google Search?
Wimbledon is coming to an end this weekend. To mark the occasion, Google is offering a new Easter Egg in the form...
-

 433Malware
433MalwareMore than 25 million smartphones infected with new malware hidden in WhatsApp
An investigation conducted by system audit specialists from the security firm Check Point has revealed the existence of new smartphone malware; dubbed...
-

 308Incidents
308IncidentsLast Facebook outage exposed users’ images hidden information
Facebook suffered a massive outage in its suite of apps yesterday morning; According to website security audit specialists, this flaw provided social...
-

 543TOR
543TORFreshOnions TorScraper – TOR Hidden Service Crawler
This is a copy of the source for the http://zlal32teyptf4tvi.onion hidden service, which implements a tor hidden service crawler / spider and...
-
 333Malware
333MalwareHackers Use Linux Malware HiddenWasp to Attack Linux Systems for Gaining Remote Access
A new sophisticated, unique Linux malware dubbed HiddenWasp used in targeted attacks against victim’s who are already under attack or gone through...
-
 246Malware
246MalwareHiddenWasp, a dangerous malware that affects Linux systems
Although they are not uncommon, network security specialists mention that the security risks present in Linux systems are not known broadly enough....
-

 229News
229NewsHiddenWasp: New Malware Targets Linux Machines To Control Them Remotely
Unlike the Windows cybersecurity ecosystem, the threats concerning the Linux systems aren’t often discussed in much detail. The attacks either go undetected...
-
 363Malware
363MalwareNew way to detect the malware hidden in hardware
While detecting malicious software hidden in hardware parts is an incredibly complex task, cyber forensics course specialists believe that important steps are...
-

 272News
272NewsThis Open Source Extension Displays Hidden Google Search Results
Google receives tonnes of requests from copyright holders daily for removing infringing content. The company then analyzes the received requests and removes the content that violates copyright claims....
-

 324News
324NewsAndroid Q’s Hidden Settings In Pixel Launcher Reveal iPhone-Like Gestures
Google has released the first beta of the upcoming Android Q, and people are frantically searching for new features in the OS....
-
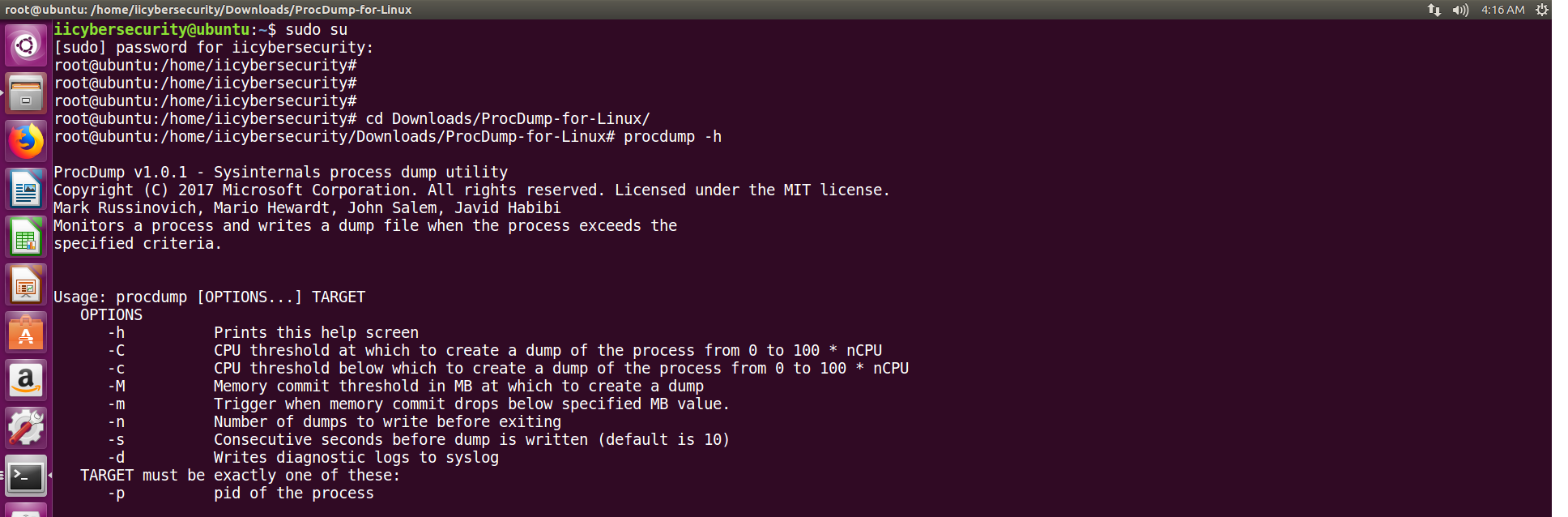
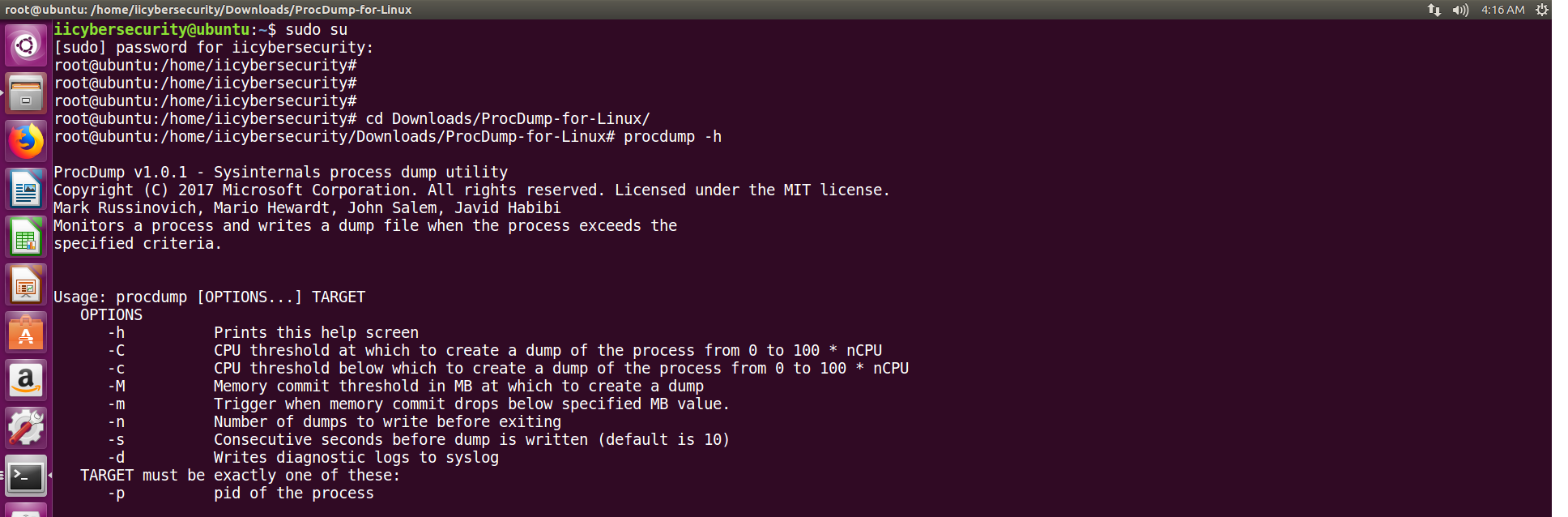 276Tutorials
276TutorialsGet hidden details of Any Linux Processes Using Procdump
Core dumps or memory dumps are created when program is executed. A dump consists of modules or work flow that how program...
-

 174News
174NewsNew Android Malware Uses Motion Sensors To Stay Hidden
Security measures are not the only ones seeing improvements! Malicious apps are also figuring out new ways to enhance its working, and one...
-
 360Tutorials
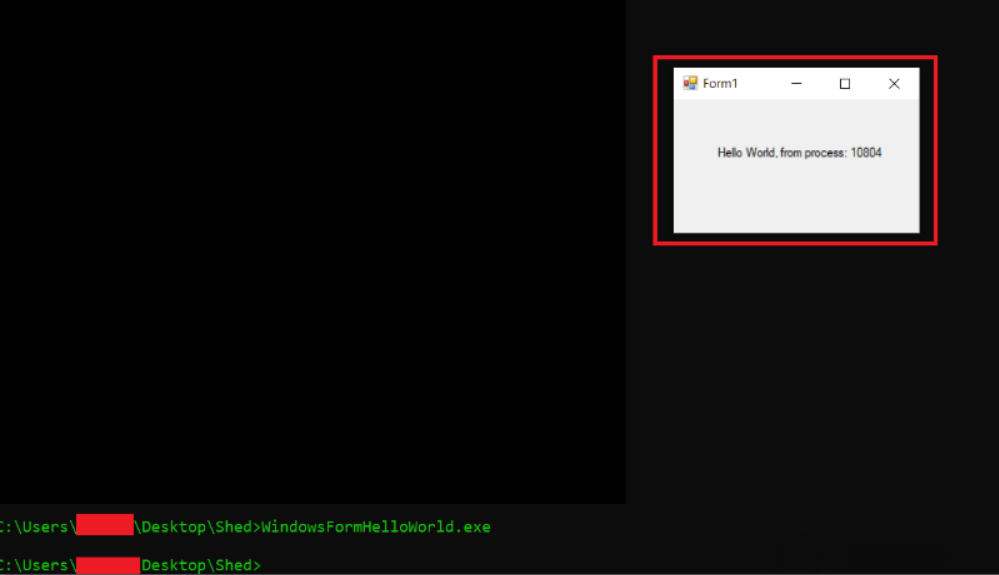
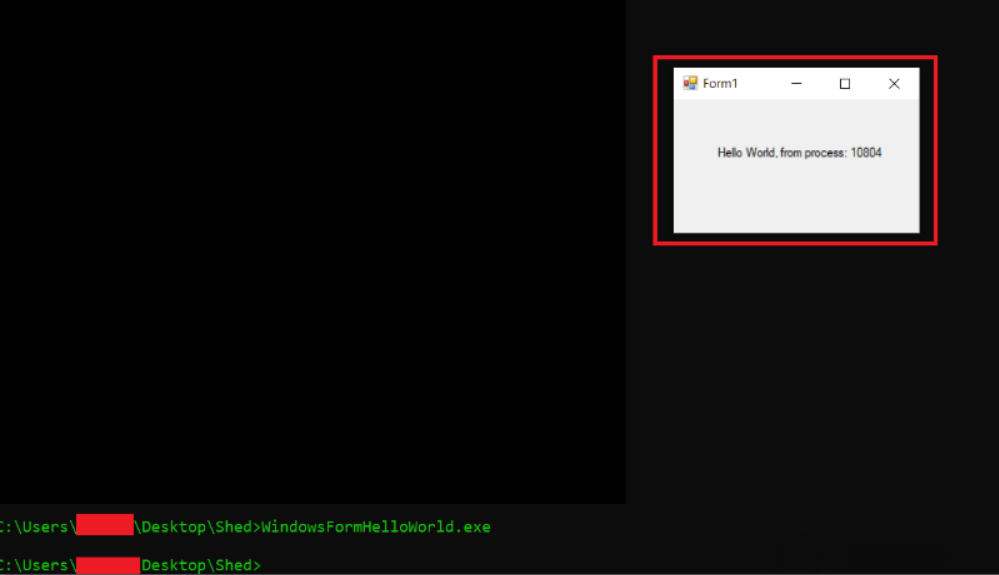
360TutorialsFind hidden malware in .Net program
Information gathering is not an easy task. In many phases, pentester has to go through many tools to gather many information, ethical...






