Search results for "Traffic"
-

 314News
314NewsHacker Group Has Been Hacking DNS Traffic on D-Link Routers
Earlier, we had service provider playing tricks with your DNS traffic. Then, it was difficult for us to fathom unless you are...
-

 379News
379NewsTesla autopilot feature hacked to risk oncoming traffic
Tesla’s High-End Vehicle’s Lane Recognition System not Free from Technical Glitches- Keen Labs Claims in New Research. Cybersecurity firm Keen Labs published...
-

 366Malware
366MalwareHackers using steganography to Drop the Powload Malware & Hide Their Malvertising Traffic
Cyber criminals now approaching a unique way to spread Powload malware with the help of steganography to infect the targeted system. Powload...
-

 669Incidents
669IncidentsDrug traffickers operating on dark web were sentenced to 40 years in jail
The gang managed to generate revenues of more than £150k in a year of activity Three drug traffickers working on dark web...
-
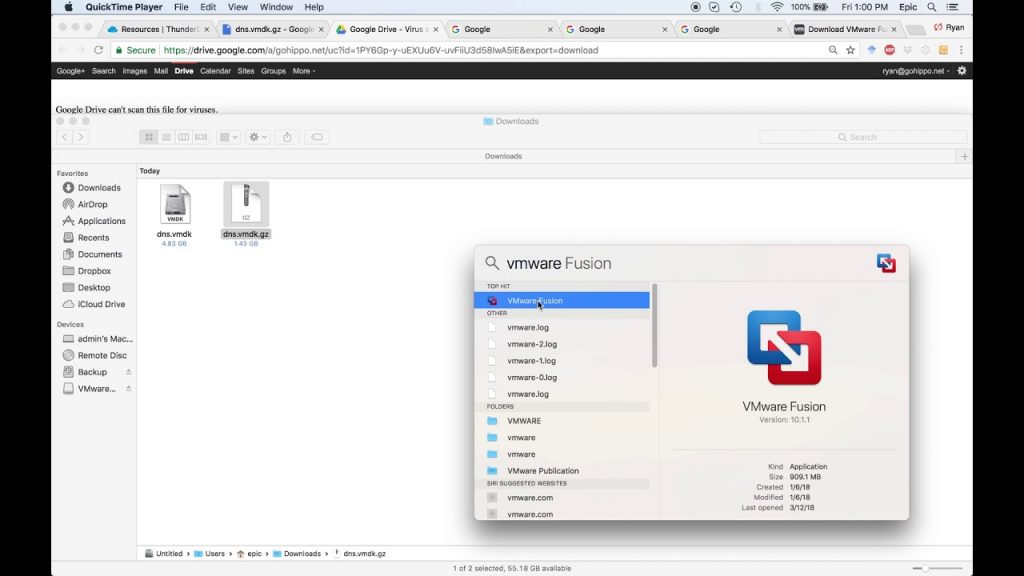
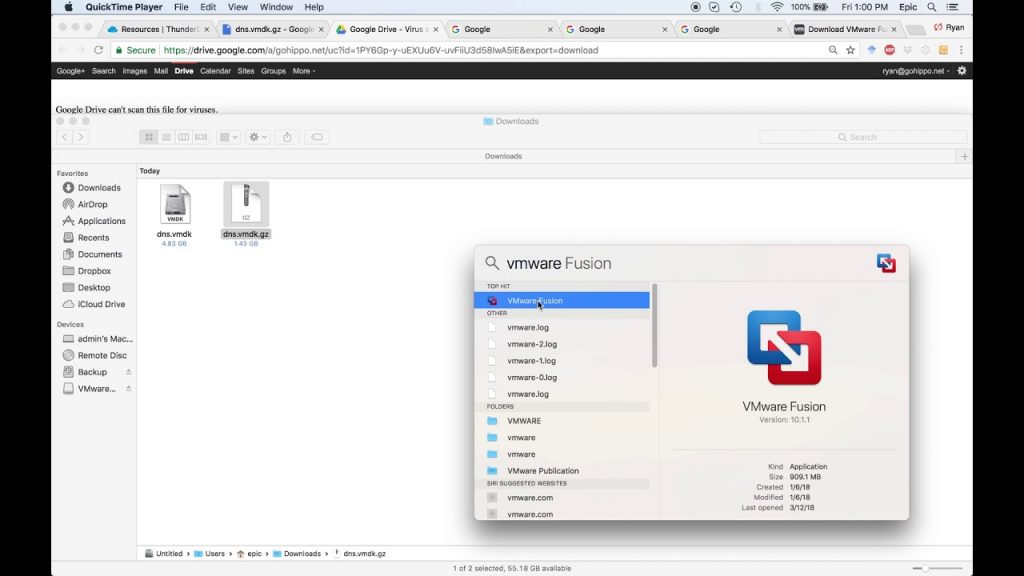 267Hack Tools
267Hack ToolsThunderDNS – Tool To Forward TCP Traffic Over DNS Protocol
This tool can forward TCP traffic over DNS protocol. Non-compile clients + socks5 support. Run Setting up NS records on our domain:...
-
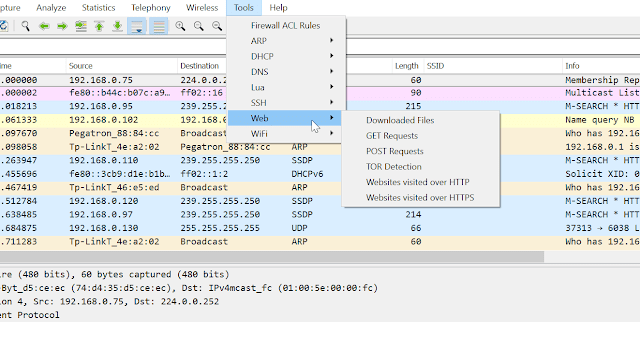
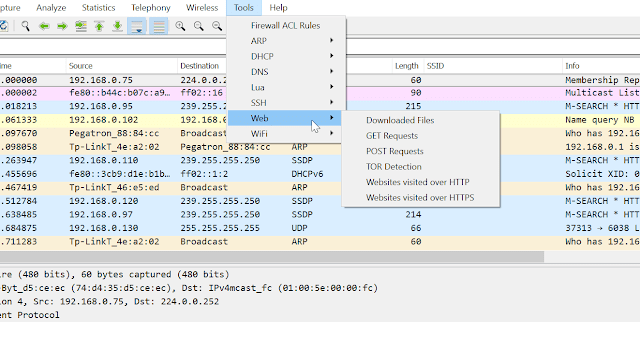 253Network Tools
253Network ToolsPA Toolkit – A Collection Of Traffic Analysis Plugins Focused On Security
PA Toolkit is a collection of traffic analysis plugins to extend the functionality of Wireshark from a micro-analysis tool and protocol dissector...
-
 316Tutorials
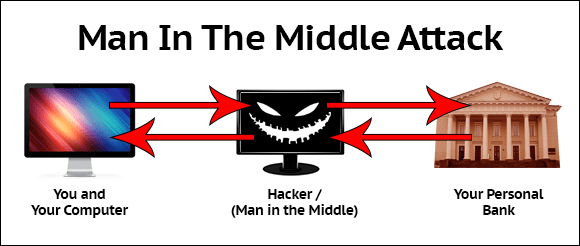
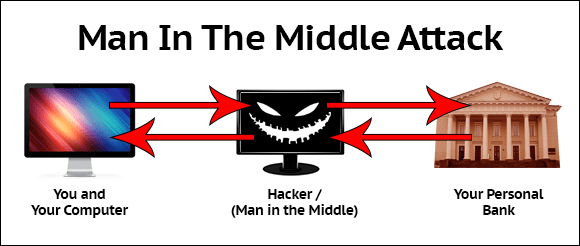
316TutorialsMonitor traffic using MITM (Man in the middle attack)
MITM INRO :- MITM (Man in the middle attack) is a another method where attacker’s sniff the running sessions in a network....
-
 214Hacking Tools
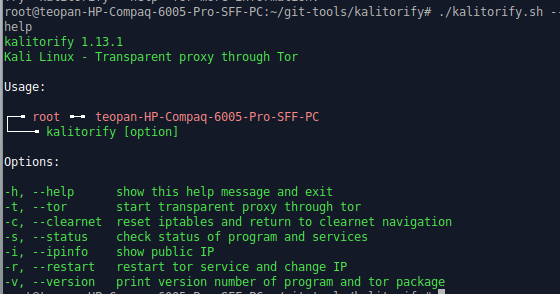
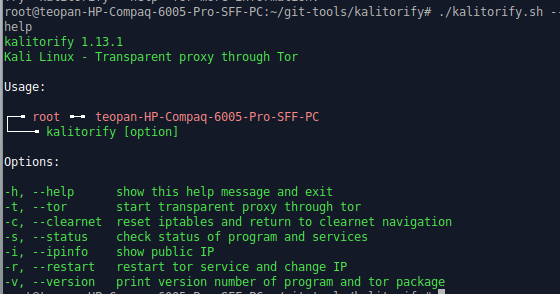
214Hacking ToolsKalitorify – Open Source Tool to Run Kali Linux Traffic Through Tor
Kalitorify is a shell based script for Kali Linux. It uses iptables and TOR to create a transparent proxy. In simple terms,...
-

 286Cryptography and Encryption
286Cryptography and EncryptionAES-Killer v3.0 – Burp Plugin To Decrypt AES Encrypted Traffic Of Mobile Apps On The Fly
Burpsuite Plugin to decrypt AES Encrypted traffic on the fly. Requirements Burpsuite Java Tested on Burpsuite 1.7.36 Windows 10 xubuntu 18.04 Kali...
-

 279Incidents
279IncidentsAnimal traffic via darknet is increasing in India
Species in critical situations are affected by these crimes Specialists in digital forensics and cybersecurity point out that darknet forums are exerting...
-
 257Vulnerability Analysis
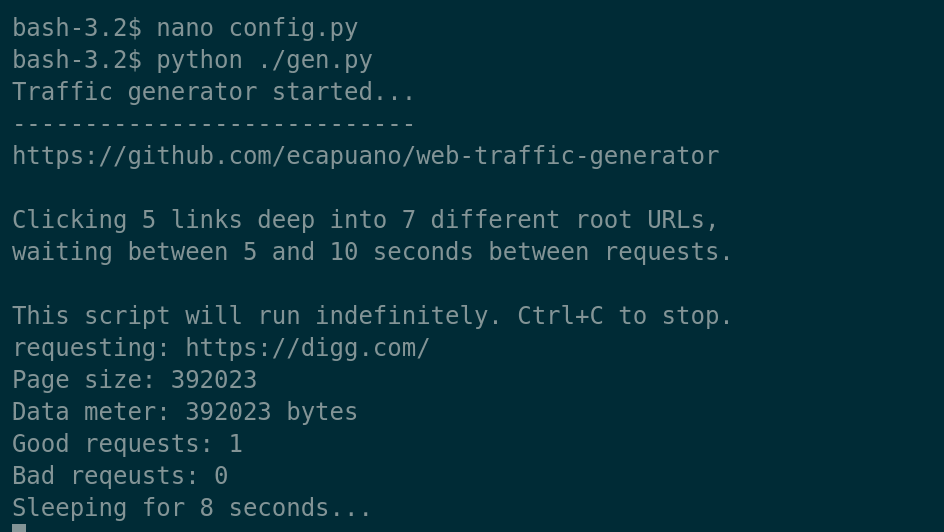
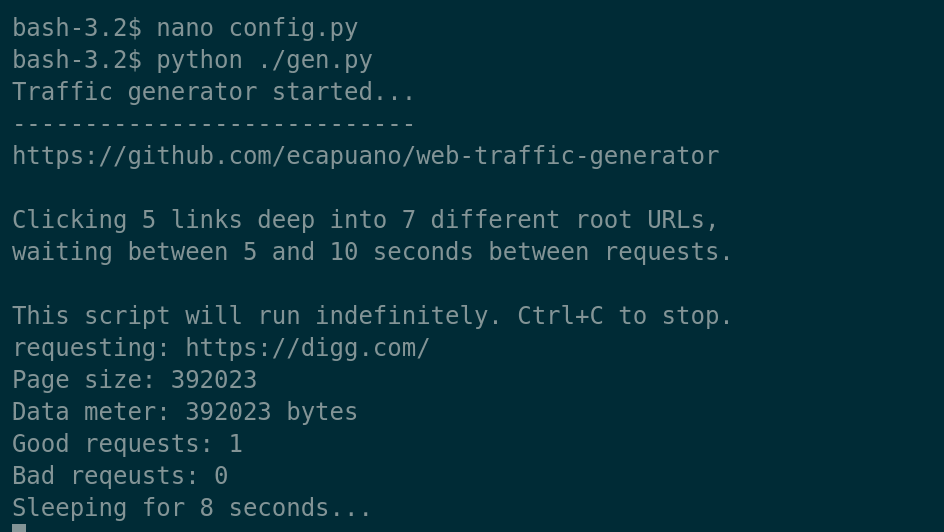
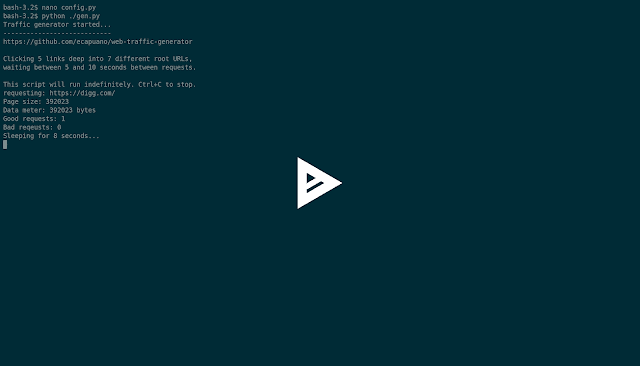
257Vulnerability AnalysisWeb-Traffic-Generator – A Quick And Dirty HTTP/S “Organic” Traffic Generator
Just a simple (poorly written) Python script that aimlessly “browses” the internet by starting at pre-defined rootURLs and randomly “clicking” links on...
-

 262Security Tools
262Security ToolsNameles – Open Source Entropy Based Invalid Traffic Detection And Pre-Bid Filtering
Nameles provides an easy to deploy, scalable IVT detection and filtering solution that is proven to detect at a high level of...
-
 263Security Tools
263Security ToolsEKFiddle v.0.8.2 – A Framework Based On The Fiddler Web Debugger To Study Exploit Kits, Malvertising And Malicious Traffic In General
A framework based on the Fiddler web debugger to study Exploit Kits, malvertising and malicious traffic in general. Installation Download and install...
-

 195Incidents
195IncidentsEnormous botnet used to hijack traffic destined for Brazilian banks
This botnet redirects hijacked traffic to more than 50 active phishing sites More than 100k routers have suffered the modification of their DNS configuration to redirect users to phishing pages. Redirection occurs only...
-
 216Hack Tools
216Hack ToolsWeb Traffic Generator – A quick and dirty HTTP/S “organic” traffic generator.
Just a simple (poorly written) Python script that aimlessly “browses” the internet by starting at pre-defined rootURLs and randomly “clicking” links on...
-

 323Data Security
323Data SecurityUpdate your devices: New Bluetooth flaw lets attackers monitor traffic
The Bluetooth flaw also opens door to a man-in-the-middle attack. The IT security researchers at Israel Institute of Technology have discovered a critical security vulnerability in...
-

 228Tricks & How To's
228Tricks & How To'sJingling Traffic Software – Free Download
Jingling traffic software/bot is a freeware to promote website mainly for Webmasters,Web Store,Twitter,Facebook and Blog to rapidly improve traffic. (IP,PV,UV) Jingling Traffic...
-
 321News
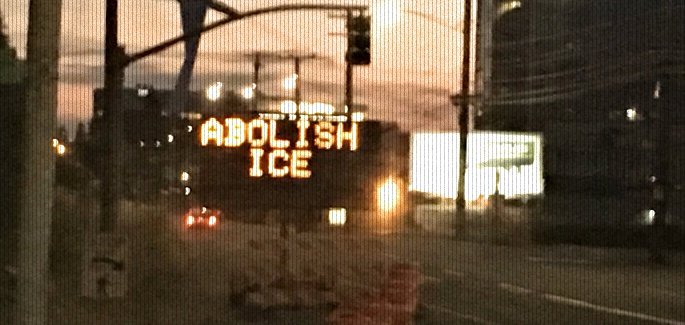
321NewsTraffic sign near ICE headquarters hacked with “Abolish ICE” message
For the last few years, hacking a traffic sign or an electronic billboard has become a trend. Some hack it for fun...
-
 306Malware Analysis
306Malware AnalysisMaltrail – Malicious Traffic Detection System
Maltrail is a malicious traffic detection system, utilizing publicly available (black)lists containing malicious and/or generally suspicious trails, along with static trails compiled...
-

 254Hacked
254HackedAndroid P Will Block Apps From Sending Internet Traffic That Anyone Can See
Android P will prevent apps from using unencrypted connections by default while establishing connections over the internet, according to a blog post...
-
 296Infosec
296InfosecDomain Fronting – A New Technique For Hiding Malware Command and Control (C2) Traffic within a Content Delivery Network
A New Technique called ” Domain Fronting “ allow cybercriminals to hide the command & control Networks Traffic within a CDN. It acts...






