Search results for "vulnerabilities"
-

 333Vulnerabilities
333VulnerabilitiesThree critical vulnerabilities can be chained to take full control of D-Link routers
Researchers from the Silesian University of Technology in Poland discovered several flaws that could be exploited to take control over some models...
-
 267Vulnerability Analysis
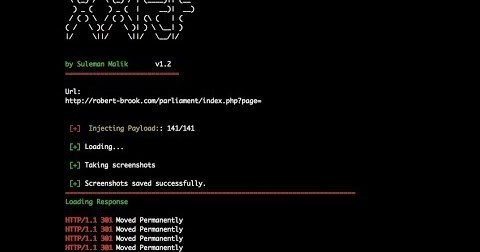
267Vulnerability AnalysisXXRF Shots – Tool to Test SSRF Vulnerabilities
What is SSRF vulnerability? Server Side Request Forgery (SSRF) is a type of vulnerability class where attacker sends crafted request from a...
-
 260Vulnerabilities
260VulnerabilitiesJuniper Networks launches multiple solutions for Junos OS vulnerabilities
The company has released security updates to address the serious vulnerabilities that affect its operating system This week, Juniper Networks has launched...
-

 347Vulnerabilities
347VulnerabilitiesVulnerabilities affect Shopify, Tinder and many other sites
The flaw was found while experts analyzed the user-side security of dating apps A team of forensic experts set out to conduct...
-

 341Vulnerabilities
341VulnerabilitiesMicrosoft Released Security Updates & Fixed 49 Vulnerabilities that Affected Microsoft Products
Microsoft released security update under patch Tuesday that affected many of its products along with certain critical Windows zero-day flaw. There are...
-
 342Vulnerabilities
342VulnerabilitiesMozilla Firefox Releases 62.0.3 & Security Updates for 2 High Critical Vulnerabilities
Mozilla Firefox Released security updates that cover 2 critical vulnerabilities in Firefox 62.0.3 and Firefox ESR 60.2.2. One of the remote code execution...
-

 255Vulnerabilities
255VulnerabilitiesVulnerabilities expose Iomega and LenovoEMC NAS devices to attacks
Lenovo has launched an alert for nine “high-risk” rated vulnerabilities that impact 20 network attached storage devices (NAS) sold by the company,...
-

 325News
325NewsNo Takers for Zero-Day Vulnerabilities on the Dark Web
According to experts vulnerability sales have been all but driven off the dark web, which now operates in the open. For years...
-

 251Vulnerabilities
251VulnerabilitiesMultiple vulnerabilities in Fuji Electric V-Server
This tool connects PCs within organizations to industrial control systems Experts in ethical hacking discovered various vulnerabilities in Fuji Electric V-Server, a...
-

 202Vulnerabilities
202VulnerabilitiesOpsview publishes new vulnerabilities report
The flaws could allow code execution Ethical hacking specialists have recently published a vulnerability report jointly with the enterprise systems monitoring software provider Opsview. The...
-

 311News
311NewsUK Based Firm EE Hit by Two Security Vulnerabilities
As revealed by Tech Crunch, the UK-based telecommunication firm EE, endured recurrent flaws in its online system. In one week, EE fixed...
-

 392Hacking Tools
392Hacking ToolsTplmap – Open Source Tool to Scan For Server Side Template Injection Vulnerabilities
Tplmap is a python tool that can find code injection and Server Side Templates Injection (SSTI) vulnerabilities by using sandbox escape techniques....
-

 346News
346NewsAdobe Released Security Patches For Photoshop Vulnerabilities
Adobe has released its latest security patches that would help fix the multiple critical vulnerabilities that have been detected in Adobe Photoshop...
-

 302Vulnerabilities
302VulnerabilitiesSerious vulnerabilities in Philips medical devices
Advanced hacking skills are not necessary to exploit the flaw Several remote code execution vulnerabilities have been found on Philips devices designed...
-

 282News
282NewsTrend Micros Launches Virtual Patching Vs. Unpatched Vulnerabilities
Trend Micro is introducing a new update on how its software implements automatic updates, they dubbed it “Virtual Patching”. It is designed...
-
 261Hacking Tools
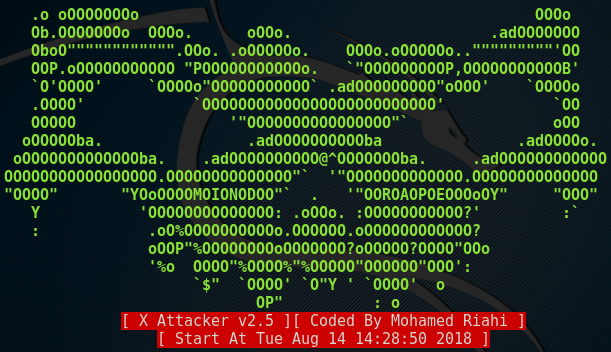
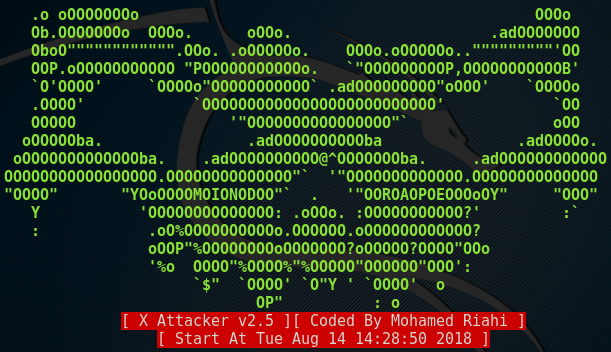
261Hacking ToolsXAttacker Tool – Scan and Auto Exploit Web Vulnerabilities
XAttacker is a perl tool capable of scanning and auto-exploiting vulnerabilities in web applications. By providing a target website to the tool,...
-

 188Vulnerabilities
188VulnerabilitiesMore than 10K vulnerabilities have been revealed so far this year
A considerable amount of the vulnerabilities revealed are considered as critical flaws A cyber security organization report shows that 16.6% of the vulnerabilities reported in the...
-

 245Vulnerabilities
245VulnerabilitiesVulnerabilities in pre-installed apps expose millions of Android devices
Your new phone could be remotely hacked Almost all phones that operate with Android include apps pre-installed by manufacturers or operators, known...
-

 349Hacked
349HackedDefcon 2018: Hacker Exploits Vulnerabilities In macOS With “Invisible Clicks”
At Defcon 2018, ex-NSA staffer and a popular Mac hacker Patrick Wardle presented his research work which involved bypassing the layers of...
-

 359Vulnerabilities
359VulnerabilitiesVulnerabilities in Square and PayPal affect mobile points of sale
There are bugs in lots of points of sale that compromise mobile payment systems Several vulnerabilities in the mobile point of sale devices (mPOS)...
-

 260Vulnerabilities
260VulnerabilitiesCritical vulnerabilities present in smart city systems
Researchers have discovered countless zero-day vulnerabilities that can be used to disrupt critical systems Experts in enterprise network security from the International...






