Search results for "vulnerabilities"
-

 215Vulnerabilities
215VulnerabilitiesKaspersky Lab Now Offers $100,000 for Vulnerabilities
Just days before its annual information security training summit starts in Cancun, Mexico, Kaspersky Lab announced an extension to its bug bounty...
-
 278Mobile Hacking
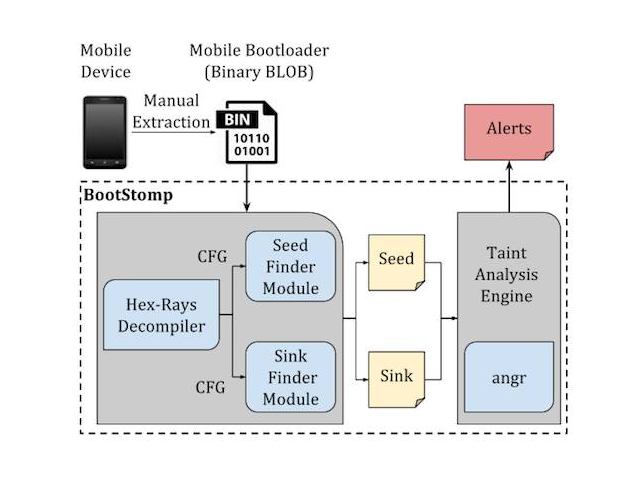
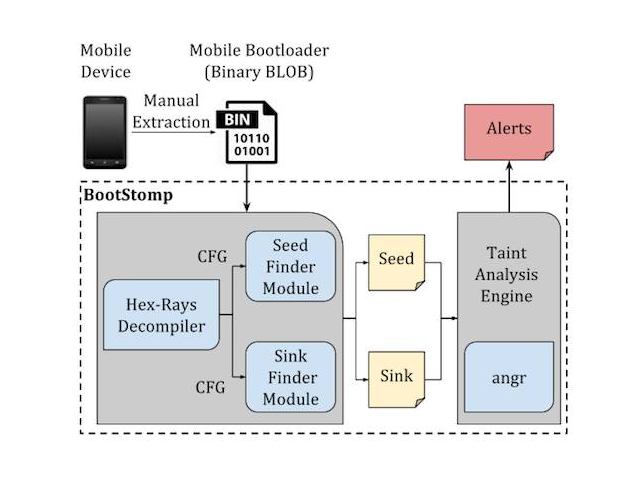
278Mobile HackingBootStomp – Find Android Bootloader Vulnerabilities
BootStomp is a Python-based tool, with Docker support that helps you find two different classes of Android bootloader vulnerabilities and bugs. It...
-

 175Data Security
175Data SecurityOpen Bug Bounty announce 100K fixed vulnerabilities
Open Bug Bounty consists of a team of no more than 10 researchers from several countries with backgrounds in IT, cyber security and law,...
-

 263News
263News2017 Saw Software Vulnerabilities Increase by 31 Percent
Reports say that there has been a 31 percent increase in the number of software vulnerabilities in 2017 compared to 2016 and...
-
 225Information Gathering
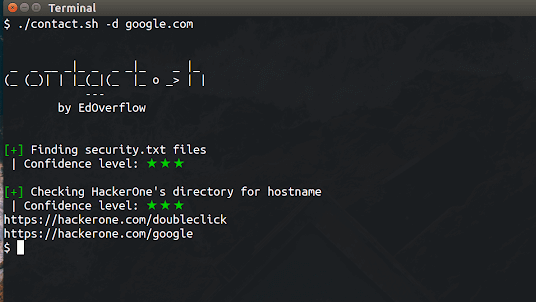
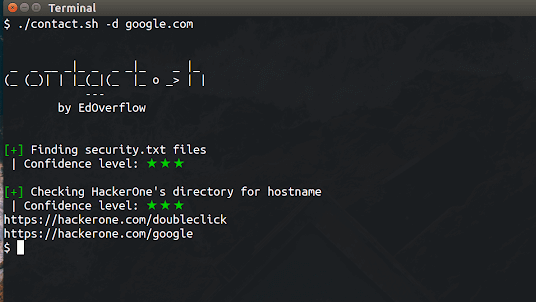
225Information Gatheringcontact.sh – An OSINT tool to find contacts in order to report security vulnerabilities
An OSINT tool to find contacts in order to report security vulnerabilities. Installation Linux Make sure you have installed the whois and...
-
 229Cryptocurrency
229CryptocurrencyHackers Abusing Apache CouchDB Vulnerabilities to Deploy Malware & Mining Monero Cryptocurrency
Cryptocurrency Mining Malware performing a crypto mining attack by exploiting the vulnerabilities in the popular database system. According to their global Sensor reports...
-
 210Hacked
210HackedMicrosoft Fixes 50 Vulnerabilities In February’s Patch Tuesday Update
Microsoft has released February’s cumulative updates for Windows 10, better known as Patch Tuesday. The reason why the update is worth getting...
-
 211Vulnerabilities
211VulnerabilitiesZerodium offers $45,000 for Linux zero-day vulnerabilities
The private exploit seller is expanding its reach to acquire bugs in popular Linux builds. Zerodium is offering $45,000 to hackers willing...
-
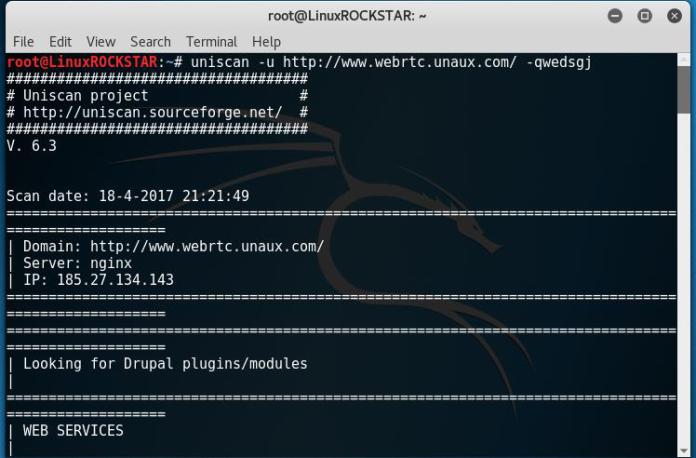
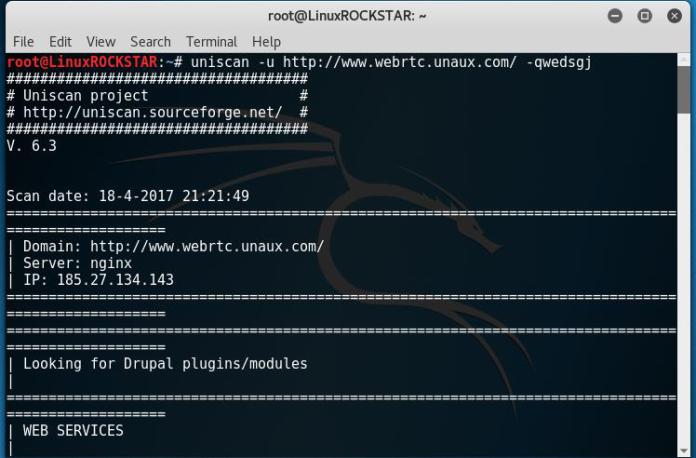 302Website Hacking
302Website HackingScan website for vulnerabilities with Uniscan
Uniscan is a simple Remote File Include, Local File Include and Remote Command Execution vulnerability scanner. Requirements: Kali Linux Uniscan (Comes Pre-Installed...
-

 228Malware
228MalwareNew Microsoft Office Vulnerabilities Used to Distribute Zyklon Malware that Creating Backdoor
Recently patched critical Microsoft office vulnerabilities are used for distributing powerful Zyklon Malware that has some sophisticated functionalities such as creating a backdoor...
-
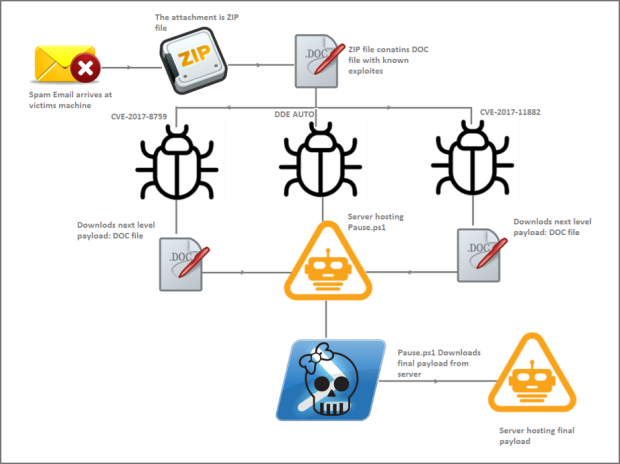
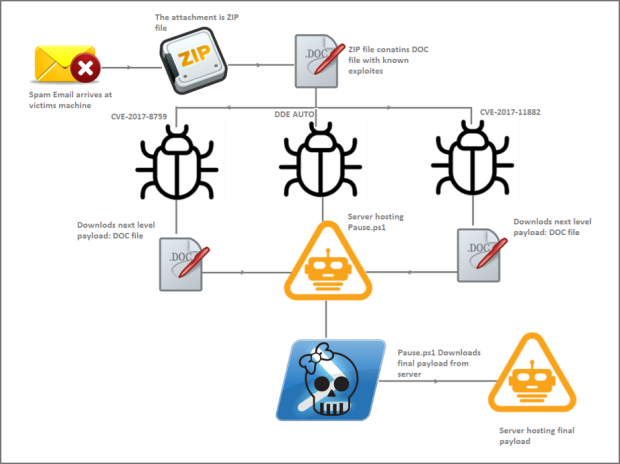 271Incidents
271IncidentsMicrosoft Office Vulnerabilities Used to Distribute Zyklon Malware in Recent Campaign
Zyklon is a publicly available, full-featured backdoor capable of keylogging, password harvesting, downloading and executing additional plugins, conducting distributed denial-of-service (DDoS) attacks,...
-
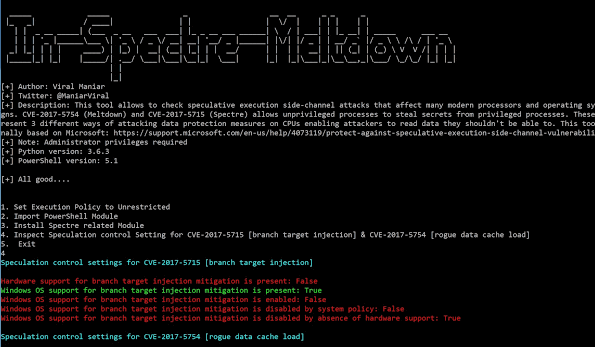
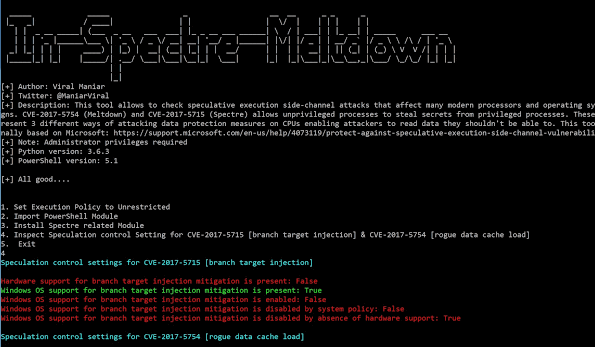 255Vulnerability Analysis
255Vulnerability AnalysisIn-Spectre-Meltdown – Tool to identify Meltdown & Spectre Vulnerabilities in processors
This tool allows to check speculative execution side-channel attacks that affect many modern processors and operating systems designs. CVE-2017-5754 (Meltdown) and CVE-2017-5715...
-

 215Vulnerabilities
215VulnerabilitiesZero-day vulnerabilities hijack full Dell EMC Data Protection Suite
Researchers have discovered severe vulnerabilities in the suite which can lead to full system takeover. Security researchers have discovered a set of...
-

 185Vulnerabilities
185VulnerabilitiesApple confirms iPhone, Mac affected by Meltdown-Spectre vulnerabilities
The iPhone maker has confirmed all Mac systems and devices running iOS are affected by the vulnerabilities, but also said there are...
-

 209Vulnerabilities
209VulnerabilitiesMeltdown and Spectre vulnerabilities bring the computing apocalypse, and yes, you are screwed
Earlier today, we reported on some shocking news — there is a serious vulnerability that affects Intel processors. To make matters worse, patching...
-

 384Vulnerabilities
384VulnerabilitiesTrackmageddon – Location Tracking Services (GPS) Vulnerabilities Allow to Access Unauthorized GPS Location Data
Security researchers discovered multiple vulnerabilities dubbed “Trackmageddon” which affects GPS services and online location tracking devices. The vulnerabilities with GPS location tracking...
-

 170Hack Tools
170Hack ToolsAutorize – A Burp Suite Extension For Detecting Authorization Vulnerabilities
Autorize is an automatic authorization enforcement detection extension for Burp Suite. It helps you detect authorization vulnerabilities. It is sufficient to give to...
-

 425Infosec
425InfosecTOP 10 Cyber Attacks and Critical Vulnerabilities of 2017
The year 2017 experienced many sophisticated cyber attacks which have been made a huge impact on the organization as well as individuals....
-
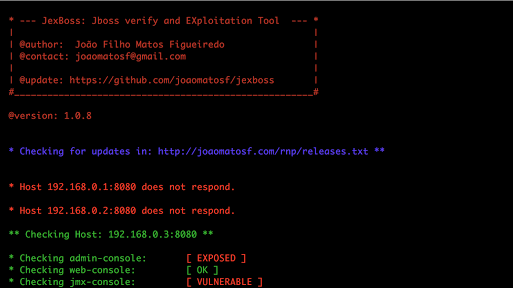
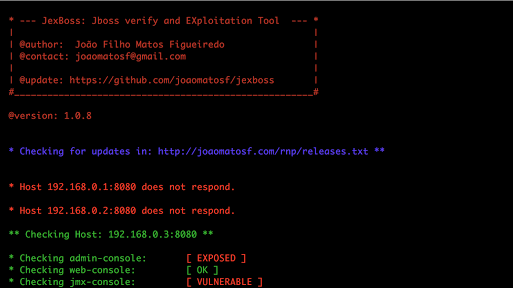 280Exploitation Tools
280Exploitation ToolsJexBoss – JBoss (and others Java Deserialization Vulnerabilities) verify and Exploitation Tool
JexBoss is a tool for testing and exploiting vulnerabilities in JBoss Application Server and others Java Platforms, Frameworks, Applications, etc. Requirements Python...
-

 315Cyber Crime
315Cyber CrimeCyber Criminals to Exploit Vulnerabilities.
Cyber attacks continue to be the major nightmare for most of the business, and most of that is because of the vulnerabilities...
-

 270News
270NewsApple released patches to address vulnerabilities in the High Sierra.
Apple had to rush in to make a quick update on serious vulnerabilities in macOS. The vulnerability hole was so serious that...






