Search results for "vulnerabilities"
-

 308Vulnerabilities
308VulnerabilitiesUsers could spread fake news because of WhatsApp vulnerabilities
Flaws allows malicious users to modify content Enterprise network security specialists report that the popular instant messaging app WhatsApp has been affected by multiple...
-
 196Vulnerabilities
196VulnerabilitiesMultiple vulnerabilities found in OpenEMR system
The OpenEMR system is used around the world Enterprise network security specialists from the International Institute of Cyber Security stated that health...
-

 174Vulnerabilities
174Vulnerabilities160 HP printer models contain two critical vulnerabilities
The company has launched patches for two serious bugs that affect over 160 models of multifunctional printers A few days after publishing...
-

 285News
285NewsHow Businesses Can Prevent Software Vulnerabilities
In a new study made by cybersecurity firm Rapid 7, it was revealed that their company’s penetration testers had successfully exploited at...
-
 327Malware
327MalwareHackers Distributing FELIXROOT Backdoor Malware using Microsoft Office Vulnerabilities
Newly discovered malware campaign distributing powerful FELIXROOT Backdoor using Microsoft Office Vulnerabilities to compromise the victim’s windows computers. FELIXROOT backdoor campaign initially...
-

 179News
179NewsApache Tomcat Patched Important Security Vulnerabilities
The Apache Software Foundation (ASF) has released security updates to address multiple vulnerabilities on its Apache Tomcat application server, one of which allows...
-

 210News
210NewsThese Vacuum Cleaner Vulnerabilities Are The New IoT Nightmare
Cybersecurity researchers have detected a couple of vulnerabilities in an IoT vacuum cleaner lineup that could let hackers spy on the victims,...
-
 265Hacked
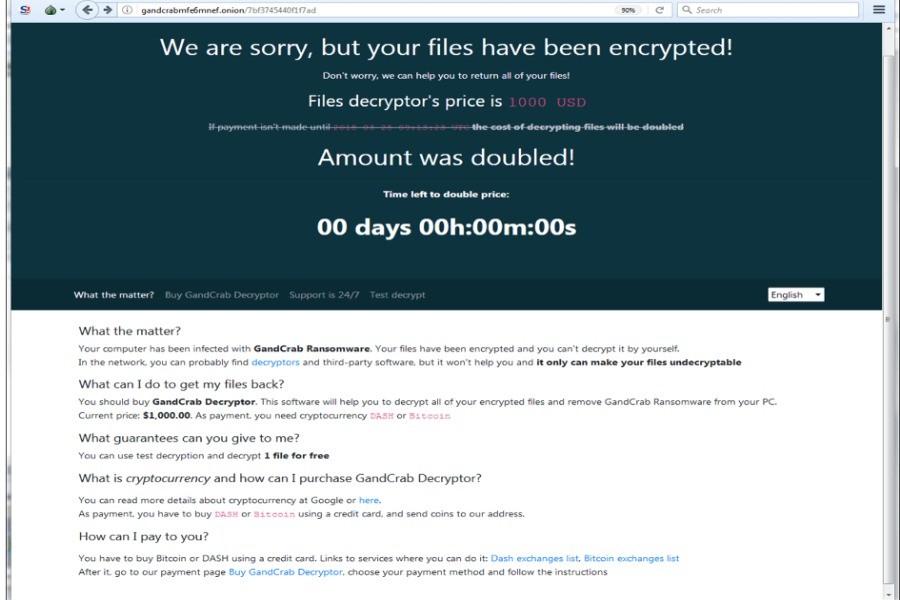
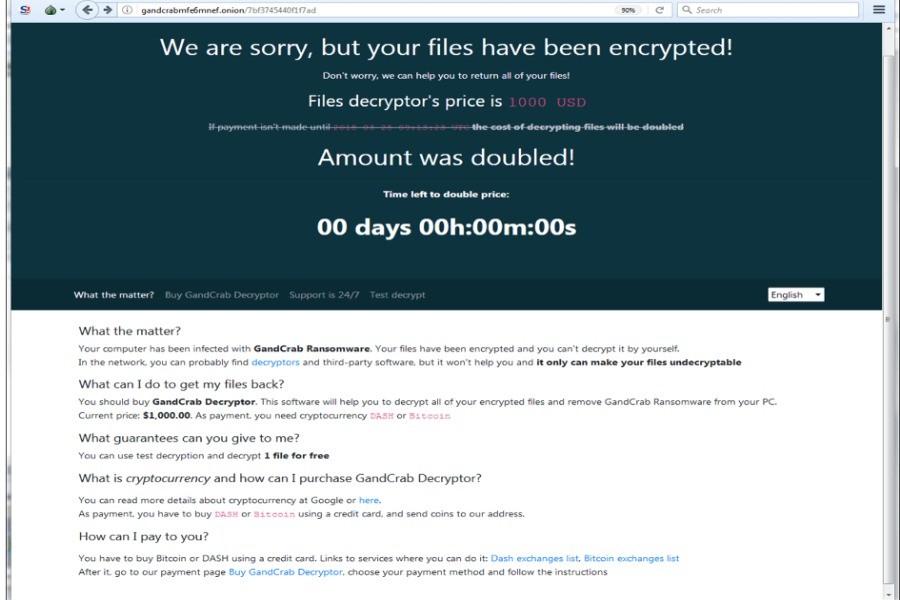
265HackedRewritten GandCrab Ransomware Targets SMB Vulnerabilities To Attack Faster
GandCrab ransomware, which has created a hullabaloo in the cybersecurity industry by constantly evolving, has yet again caused a commotion. The latest...
-
Hack Tools
Sherlock – Tool to find missing Windows patches for Local Privilege Escalation Vulnerabilities
PowerShell script to quickly find missing Microsoft patches for native privilege escalation vulnerabilities. Currently looks for: MS10-Zero15 : User Mode to Ring...
-

 283Vulnerabilities
283VulnerabilitiesSiemens revealed vulnerabilities in some of their SICLOCK central clocks, some of them are critical
Siemens warns of the presence of six vulnerabilities in some of its SICLOCK central clocks, which synchronize the time in industrial environments,...
-

 219News
219NewsUK IT professionals are better at handling security vulnerabilities
A survey was conducted by Outpost24 to identify the managing of cyber-security exposure. This survey was conducted at Infosecurity and around 250...
-
 369Hacking Tools
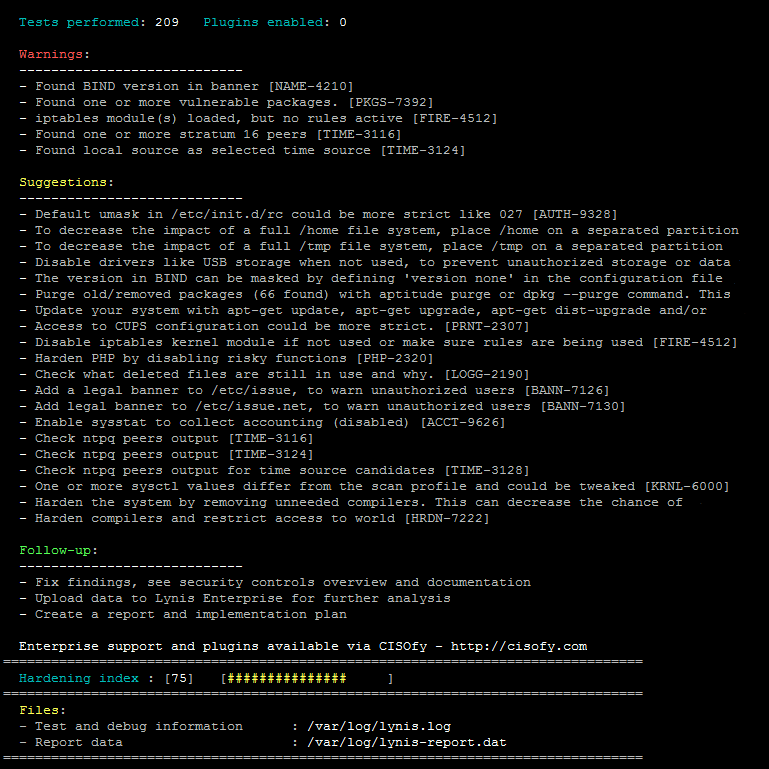
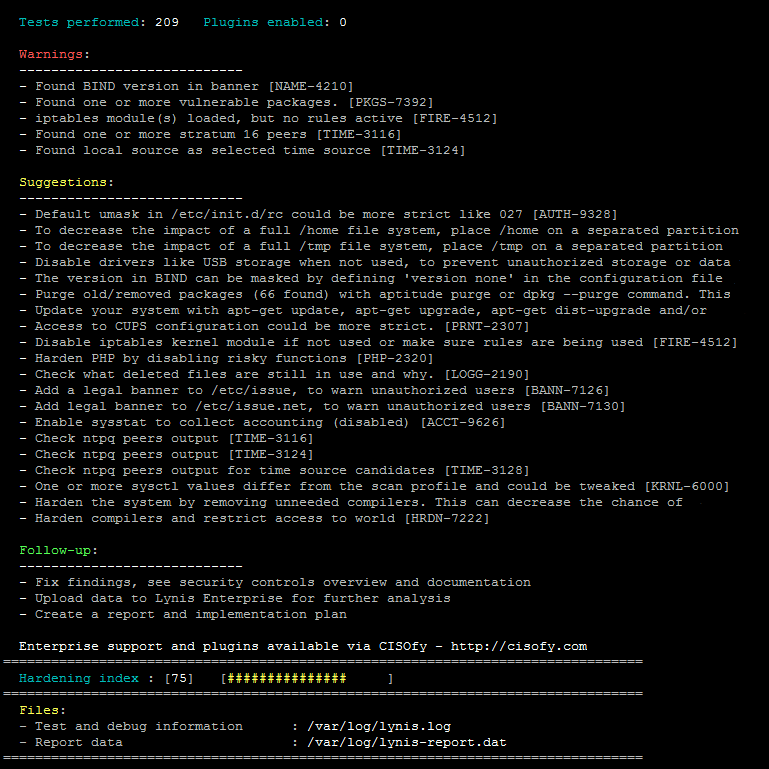
369Hacking ToolsLynis – The Security Tool for Finding Linux and Mac OS Vulnerabilities
So what is this Lynis tool all about? Lynis is a security tool used for auditing Unix based systems it’s main aims...
-

 319Vulnerabilities
319VulnerabilitiesLTE and 5G networks could be affected by new vulnerabilities
A group of pentest researchers has demonstrated ability to passively identify session details and perform hijacking, allowing phishing attacks. According to the International Institute...
-

 310Vulnerabilities
310VulnerabilitiesCisco launches 34 update patches for different vulnerabilities, 5 of them critical
Cisco, a company dedicated to manufacturing telecommunications devices, launched patches for 34 failures in its software, including solutions for five critical vulnerabilities...
-

 424Vulnerabilities
424VulnerabilitiesCisco Released Patches for More than 30 Vulnerabilities Including the 5 Critical One’s in FXOS and NX-OS
Cisco released patches for 34 vulnerabilities affecting multiple products that include 5 critical vulnerabilities, 20 High severity vulnerabilities and 9 medium level...
-
 176Vulnerabilities
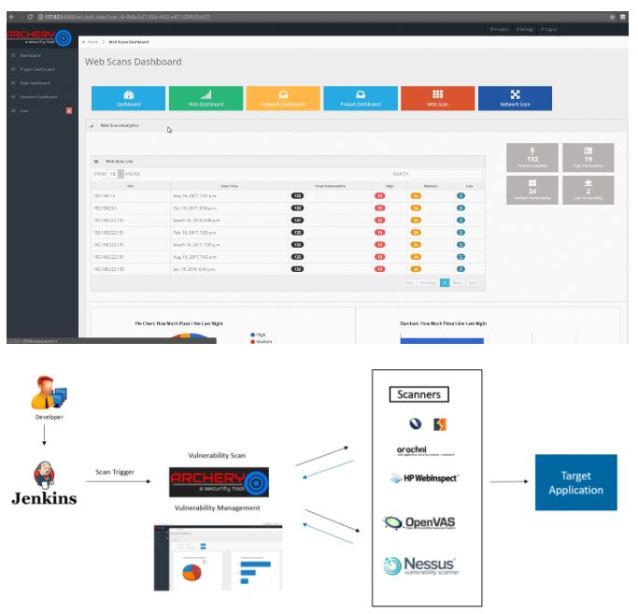
176VulnerabilitiesArchery, perform scans and manage vulnerabilities with this tool
An information security expert explains that, Archery is an open source vulnerability management and evaluation tool that helps developers and evaluators perform scans and...
-

 343Vulnerabilities
343VulnerabilitiesMultiple Vulnerabilities in IBM QRadar SIEM Allows Attackers to Escalate Privileges and to Execute Arbitrary Commands
Multiple Vulnerabilities found in IBM QRadar chained together allows a remote attacker to bypass authentication and to execute arbitrary commands with root...
-

 263Vulnerabilities
263VulnerabilitiesD-Link DIR-620 Routers with Critical Vulnerabilities
After an investigation, security professionals have found a backdoor account in the firmware of the D-Link DIR-620 routers; this allows malicious actors...
-

 194Vulnerabilities
194VulnerabilitiesVulnerabilities let BMW models to be hackable
A research team from the Tencent firm discovered several security vulnerabilities in BMW models. Tencent Keen Security Lab’s information security experts found 14 vulnerabilities...
-

 332Vulnerabilities
332VulnerabilitiesCritical vulnerabilities discovered in Dell devices
A recent investigation revealed six vulnerabilities in Dell EMC RecoverPoint devices. One of the flaws found allows attackers to execute remote unauthenticated...
-

 289Vulnerabilities
289VulnerabilitiesHow to exploit two zero-days vulnerabilities simultaneously in a single attack: unicorn attack
In an unusual case someone managed to develop a malware attack that, with one click, exploits separate zero-day vulnerabilities in two different...






