Search results for "vulnerabilities"
-
 206Vulnerabilities
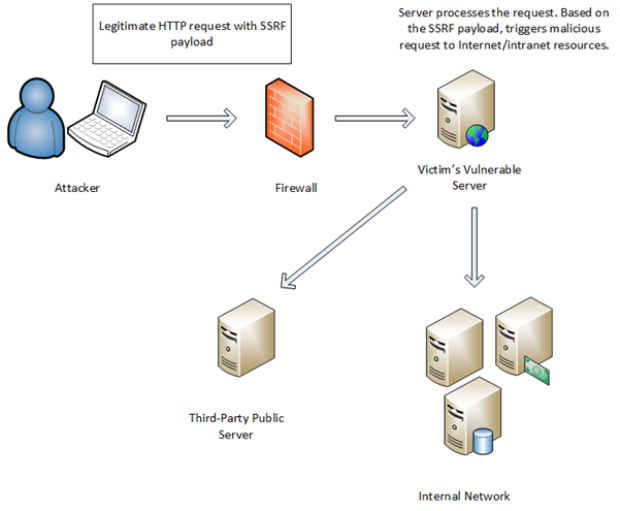
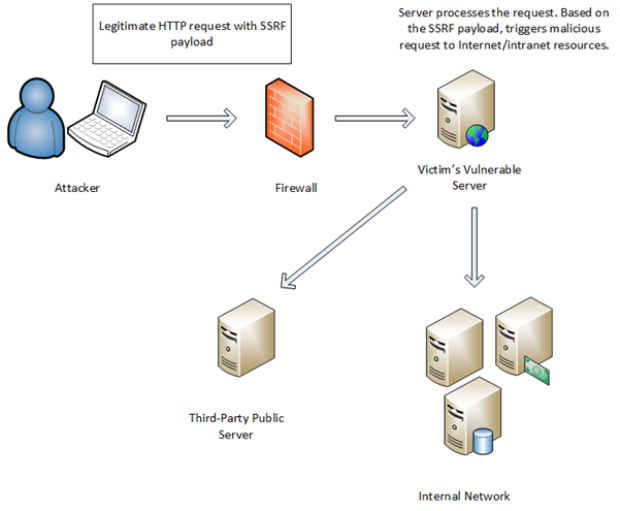
206VulnerabilitiesAbusing the AWS metadata service using SSRF vulnerabilities
I recently worked on a small toy project to execute untrusted Python code in Docker containers. This lead me to test several...
-
 93Data Security
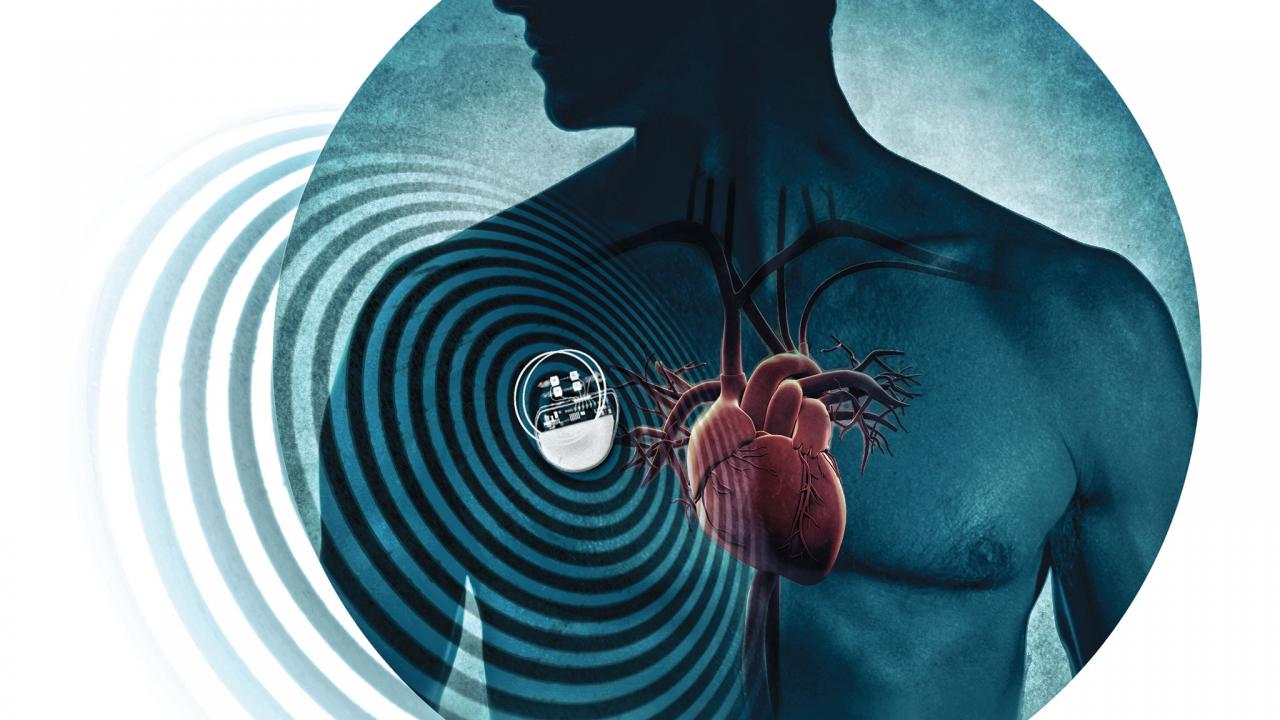
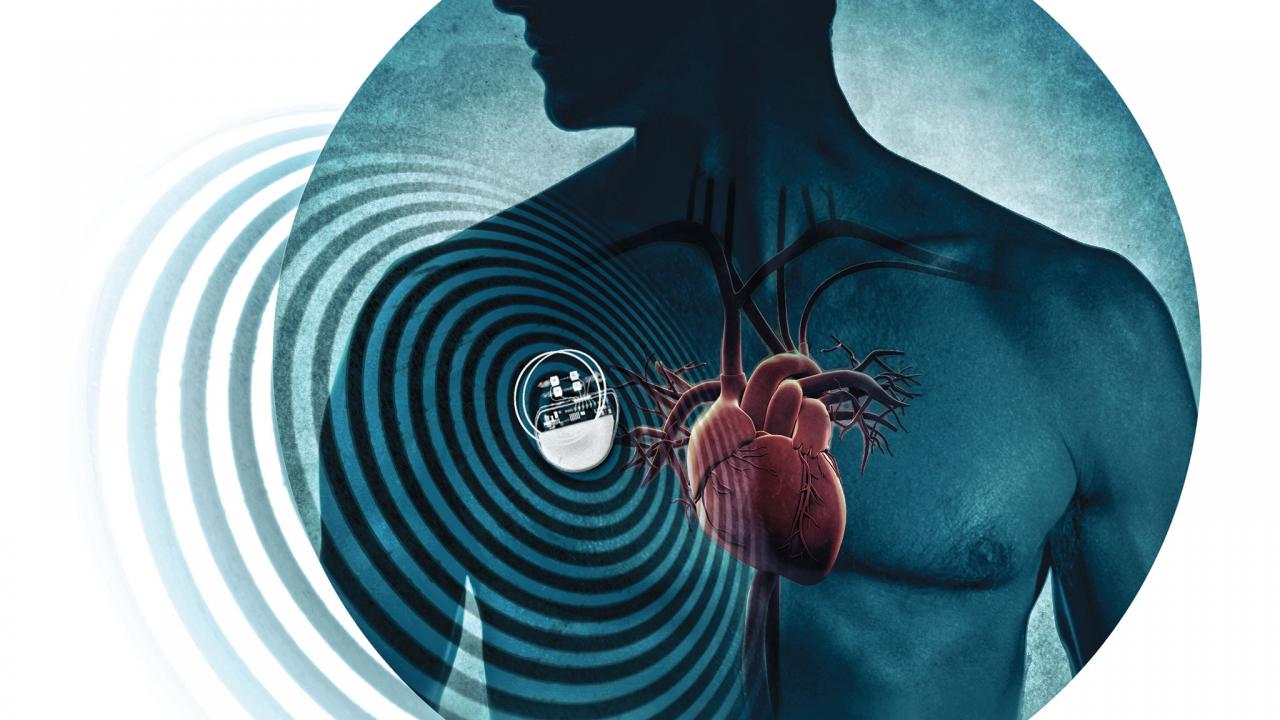
93Data Security8,000 Vulnerabilities Found in Pacemakers
A staggering 8,000 vulnerabilities have been discovered in one of the most widespread medical advancements keeping people alive today: The pacemaker. White...
-
 294Vulnerabilities
294VulnerabilitiesSources to Trace New Vulnerabilities
Vulnerability defined as the weakness that allows attacker to enter in and harm, it may be a flaw in design or misconfiguration....
-
 464Vulnerabilities
464Vulnerabilities6 Critical RCE and Buffer Overflow Vulnerabilities in IBM Informix Dynamic Server and Informix Open Admin Tool
IBM Informix Dynamic Server and Informix Open Admin Tool contains 6 Critical Vulnerabilities including RCE and a Buffer overflow in HEAP. IBM Informix...
-

 340Pentest
340PentestNew Burp Suite Version 1.7.23 adds support for 5 new Vulnerabilities
Burp Suite is a graphical tool for testing Web application security. The tool is composed in Java and created by PortSwigger Security....
-

 170Vulnerabilities
170VulnerabilitiesSecurity vulnerabilities in Hyundai Blue Link mobile app allowed hackers to steal vehicles
Security vulnerabilities in the Hyundai Blue Link mobile apps allowed hackers to steal vehicles, the car maker fixed them. Security vulnerabilities in...
-

 214Vulnerabilities
214VulnerabilitiesVulnerabilities in Linksys routers allow attackers to hijack dozens of models
Cyber security experts disclosed the existence of 10 unpatched security flaws in dozens of Linksys routers widely used today. The IOActive senior...
-
 162Hackers Repository
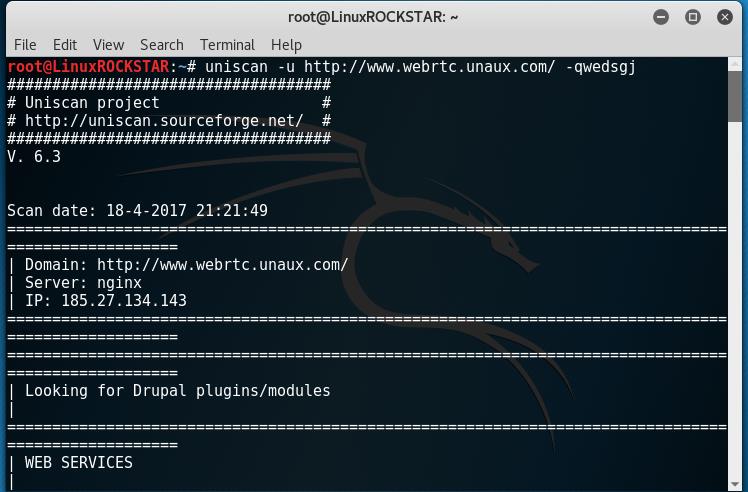
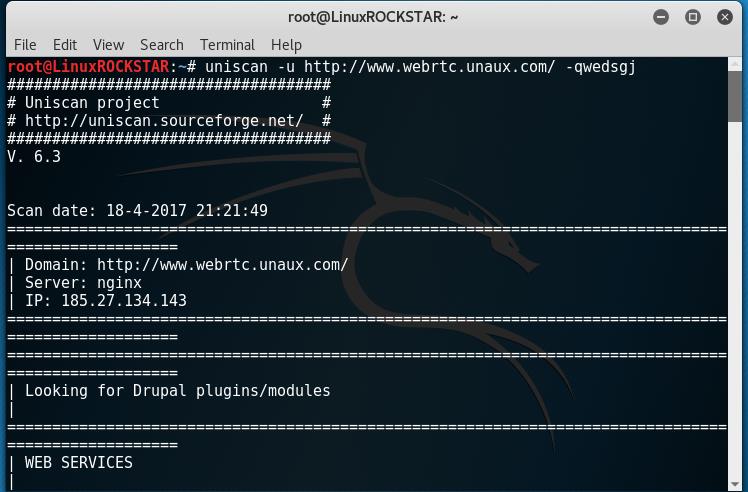
162Hackers RepositoryScan website for vulnerabilities with Uniscan Kali Linux Tutorial
Welcome back, in this tutorial you will learn how to scan and fingerprint a web server or device to find vulnerabilities. To...
-
 186Vulnerabilities
186VulnerabilitiesMICROSOFT PATCHES THREE VULNERABILITIES UNDER ATTACK
Microsoft today patched a zero-day Word vulnerability that has been publicly attacked along with deploying fixes for Internet Explorer, Microsoft Edge and...
-
 100Vulnerabilities
100VulnerabilitiesRIVERBED PATCHES VULNERABILITIES IN APPLICATION MONITORING PORTAL
Riverbed Technology has patched four serious vulnerabilities in its SteelCentral portal, a centralized application performance monitoring platform. The flaws could allow an...
-

 133Vulnerabilities
133VulnerabilitiesGoogle and Apple Issue Security Updates for Critical Broadcom WiFi Vulnerabilities
Owners of Android and iOS devices should pay special attention to security updates released by Google and Apple on Monday, as they...
-
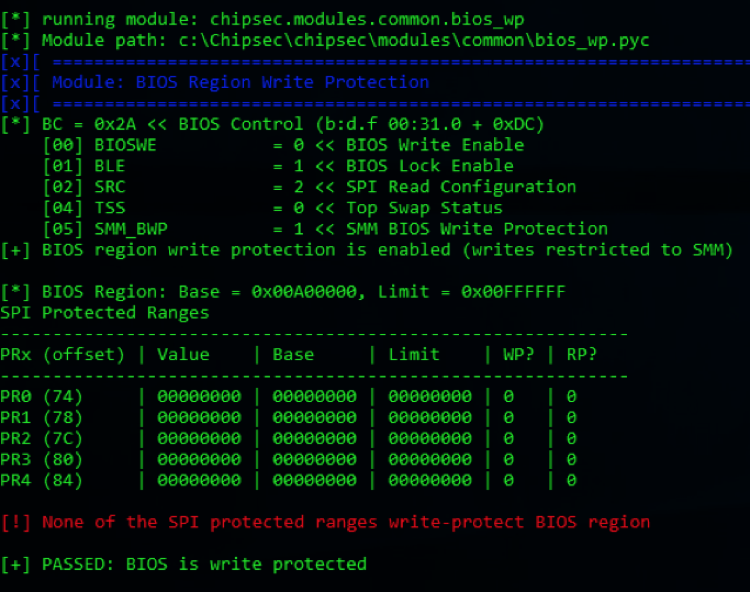
 204Vulnerabilities
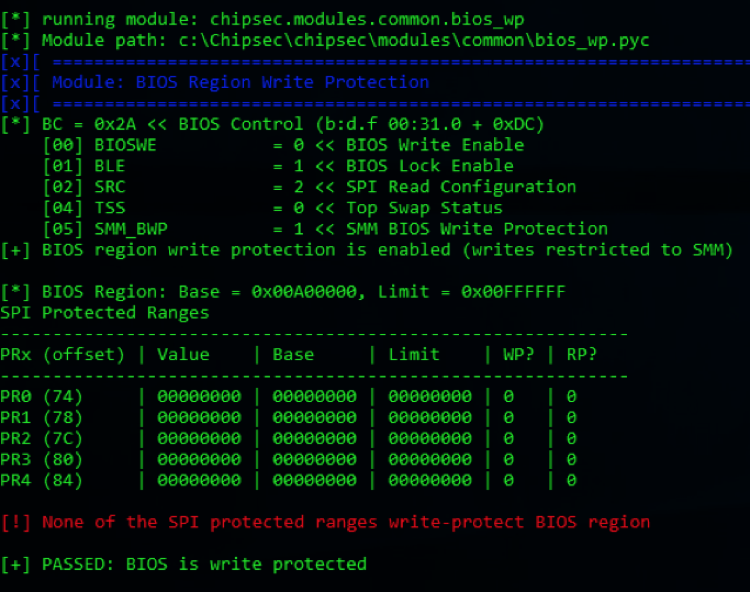
204VulnerabilitiesUEFI Vulnerabilities allow to fully compromise Gigabyte Mini PCs
Experts at Cylance disclosed two UEFI flaws that can be exploited by attackers to install a backdoor on some Gigabyte BRIX mini...
-
 143Vulnerabilities
143VulnerabilitiesResearchers Disclose Vulnerabilities in GIGABYTE BRIX Systems
Earlier this month, we teased a proof of concept for UEFI ransomware, which was presented at RSA Conference 2017. The HackingTeam, Snowden,...
-
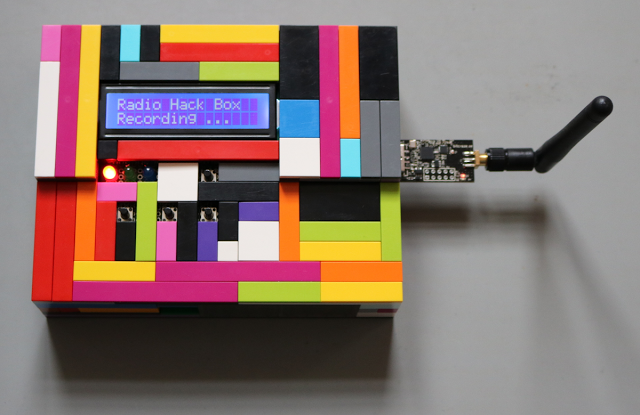 274Hacking Tutorials
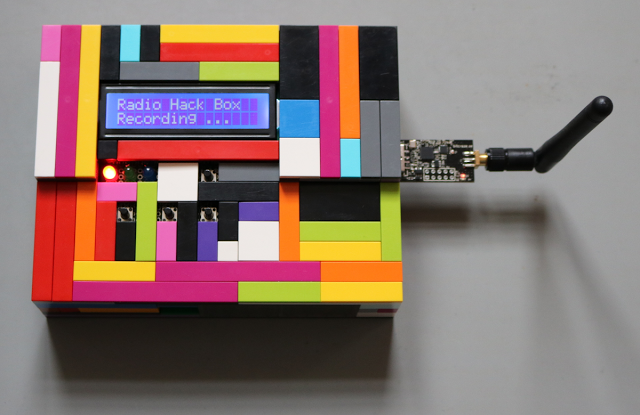
274Hacking TutorialsRadio Hack Box – Tool to Demonstrate Vulnerabilities in Wireless Input Devices
The SySS Radio Hack Box is a proof-of-concept software tool to demonstrate the replay and keystroke injection vulnerabilities of the wireless keyboard...
-
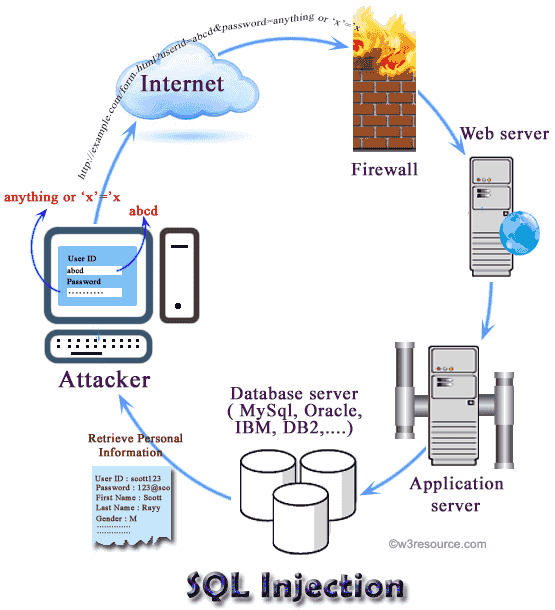
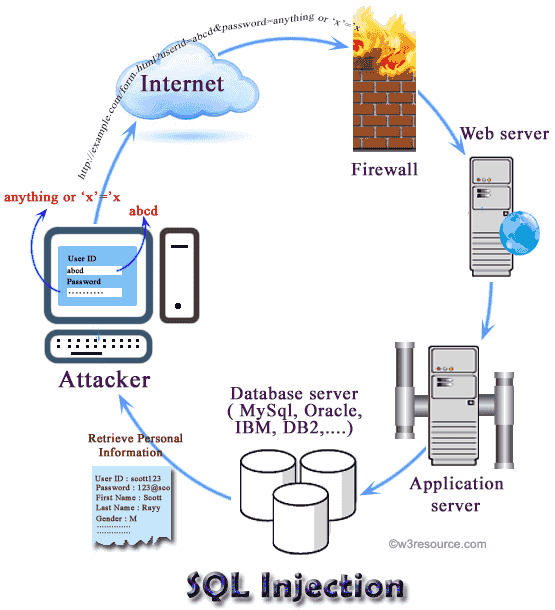 195Hackers Repository
195Hackers RepositorySQL Inject Me -Firefox Extension used to test for SQL Injection vulnerabilities
SQL Inject Me is a Firefox addon created by Security Compass it is used for finding SQL vulnerabilities in Web applications. SQL...
-

 189Vulnerabilities
189VulnerabilitiesDrupal releases Security update for Multiple Vulnerabilities
Drupal is a content management software. It’s utilized to make a considerable amount of the websites and applications you utilize each day....
-
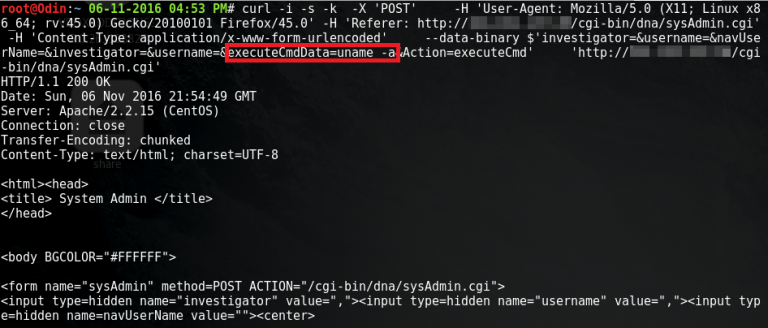
 188Data Security
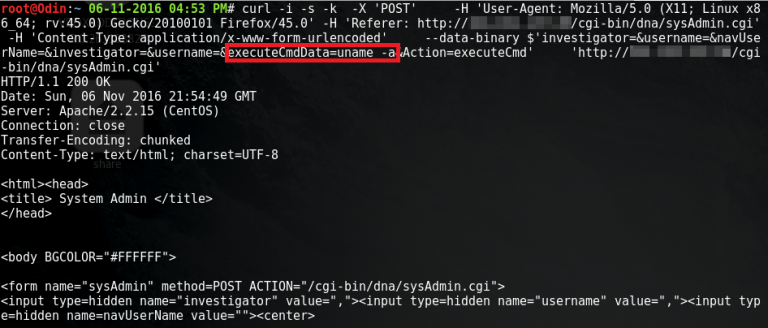
188Data SecurityMultiple vulnerabilities discovered in DNA sequencing web-application
Shorebreak Security penetration testers discovered seven serious vulnerabilities in the dnaLIMS web application during the course of a blackbox penetration test for...
-

 112Geek
112GeekMicrosoft Bug Bounty Program: Report Vulnerabilities, Get up to $30,000
For the last couple of year, Google has been releasing details about unpatched vulnerabilities discovered by its researchers in Microsoft’s products. Now,...
-

 127Vulnerabilities
127VulnerabilitiesUnexpected Journey #2 – Taking Down Entire Domain Using Vulnerabilities of a SIEM Product
As I said on my previous article, being a penetration tester makes us feel like a group of traveler. Today, I would...
-

 154Vulnerabilities
154VulnerabilitiesUPDATED FIRMWARE DUE FOR SERIOUS TP-LINK ROUTER VULNERABILITIES
Chinese router maker TP-Link is wrestling with the disclosure of a handful of vulnerabilities in its C2 and C20i routers. The most...
-
 156Vulnerabilities
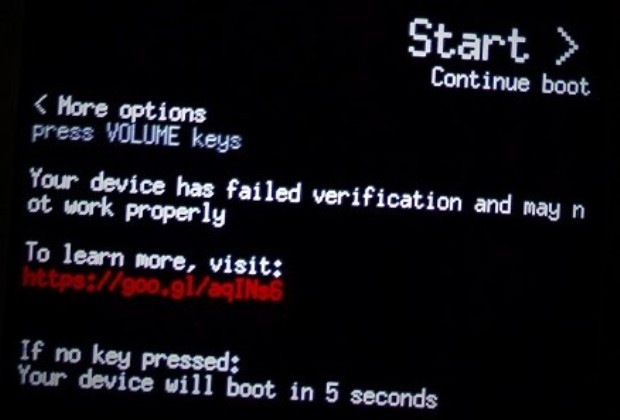
156VulnerabilitiesOwning a Locked OnePlus 3/3T: Bootloader Vulnerabilities
In this blog post I disclose two vulnerabilities in the OnePlus 3/3T bootloader. The first one, CVE-2017-5626, is a critical severity vulnerability...