Search results for "vulnerabilities"
-

 169Vulnerabilities
169VulnerabilitiesImportant Kernel Updates Patch 7 Vulnerabilities in All Supported Ubuntu OSes
Canonical announced a few hours ago the availability of new kernel updates for all supported Ubuntu Linux operating systems, patching a total...
-
 276Vulnerabilities
276VulnerabilitiesSerious Linux vulnerabilities “Dirty COW” is a privilege escalation vulnerability in the Linux Kernel – Linux users urged to protect
Recently ,there have been some serious vulnerabilities found in various Linux systems. Whilst OS vulnerabilities are a common occurrence. The ‘Dirty Cow’...
-

 350Vulnerabilities
350VulnerabilitiesWordPress Publishes Critical Security Update XSS, SQL Injection vulnerabilities
WordPress 4.7.1 and earlier forms are influenced by various vulnerabilities. A remote attacker could exploit some of these vulnerabilities to take control...
-

 208Vulnerabilities
208VulnerabilitiesPHP Melody 2.7 – Multiple Vulnerabilities
What’s interesting when I come across a new piece of software is how the initial impressions change after reading the code. If...
-

 202Data Security
202Data SecurityGeneral Electrics plays down industrial control plant vulnerabilities
Only a local hacker in a facility would be able to run an attack. General Electric (GE) has pushed out an update...
-

 210Vulnerabilities
210VulnerabilitiesWordPress 4.7.1 released, patches eight vulnerabilities and 62 bugs
According to the release notes the latest version of WordPress 4.7.1 addresses eight security vulnerabilities and other 62 bugs. Wednesday the latest...
-

 89Vulnerabilities
89VulnerabilitiesCritical RCE vulnerabilities affect SwiftMailer, PhpMailer and ZendMail
The security expert Dawid Golunski from Legal Hackers has reported critical RCE flaws in the popular PHP libraries SwiftMailer, PhpMailer and ZendMail....
-

 113Vulnerabilities
113VulnerabilitiesMICROSOFT PATCHES PUBLICLY DISCLOSED IE, EDGE VULNERABILITIES
Microsoft today patched a half-dozen critical browser vulnerabilities that have been publicly disclosed, but apparently not used in attacks as of yet....
-
 124Vulnerabilities
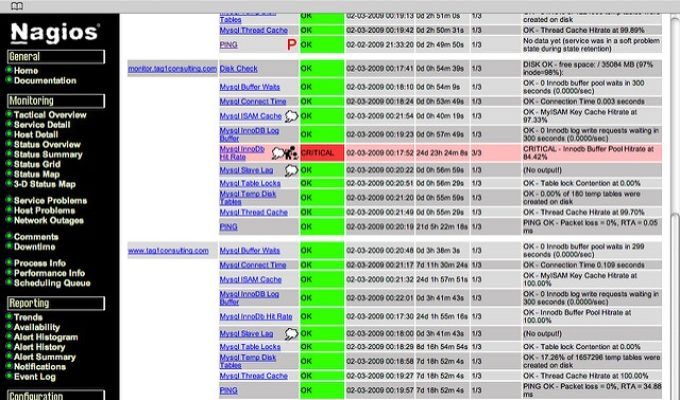
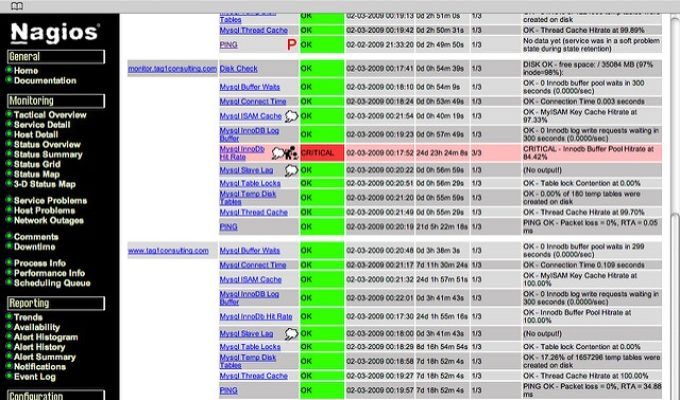
124VulnerabilitiesNAGIOS CORE PATCHES ROOT, RCE VULNERABILITIES
Nagios Core has been updated to take care of two critical vulnerabilities that can be pinned together to attack servers hosting the...
-
 85Data Security
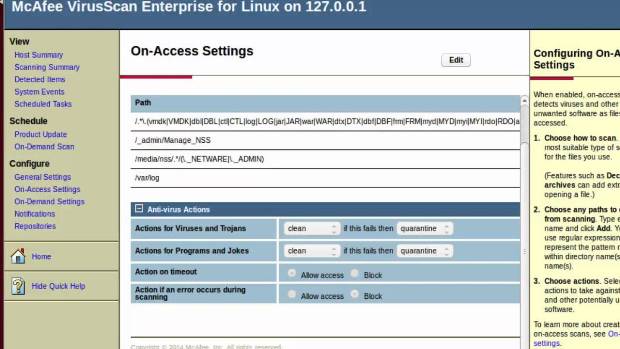
85Data SecurityVulnerabilities Found in Linux Security Software Can Give Hackers Root Access
McAfee patches flaws in its Linux security solution. Remote code execution flaws found in McAfee VirusScan Enterprise for Linux could allow an...
-
 139Vulnerabilities
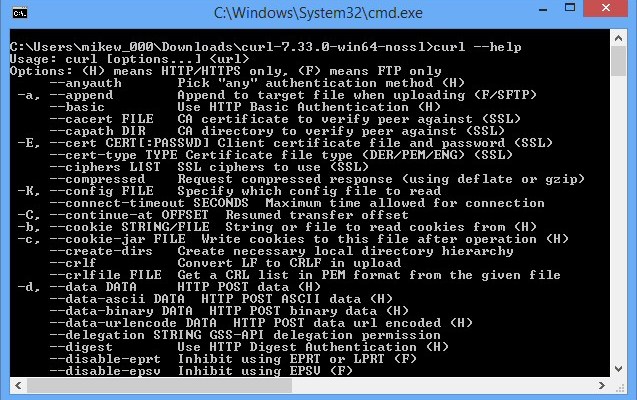
139VulnerabilitiesAn audit revealed dozen vulnerabilities in the cURL
Security experts who conducted an audit on cURL discovered nearly a dozen vulnerabilities that were patched in the last release. The cURL...
-

 165Data Security
165Data SecurityCRITICAL MYSQL VULNERABILITIES CAN LEAD TO SERVER COMPROMISE
Critical vulnerabilities in MySQL and vendor deployments by database servers MariaDB and PerconaDB have been identified that can lead to arbitrary code...
-

 209How To
209How ToUse This Tool and Scan Your IoT Devices For Vulnerabilities
The security of IoT devices is the problem the world is sure to face in the coming years. To make it easy...
-
How To
How to Scan for SMB vulnerabilities using Nmap
Hi there my fellow hackers, we are back with another tutorial. Today we will see how we can use a Nmap script...
-

 94Vulnerabilities
94VulnerabilitiesBT Wi-Fi extender, extends to XSS and password changing vulnerabilities
Following an investigation by Pen Test Partners, British Telecom (BT) has released a firmware upgrade for their popular range of Wi-Fi extenders....
-

 169Vulnerabilities
169VulnerabilitiesNiche software vulnerabilities leave enterprises open to attack
News of software vulnerabilities often centers on products from well-known companies that potentially put large numbers of end users at risk. But...
-
How To
How to Scan for Vulnerabilities Using Nessus
Welcome back guys. Today we will see how you can check for vulnerabilities using Nessus. Usually vulnerability scans are done before doing the penetration...
-
 317Geek
317Geek8 Linux Kernel Vulnerabilities Patched In Ubuntu 16.04 LTS, Update Now
Short Bytes: Canonical has released a new update for Ubuntu 16.04 LTS operating system, its official flavors, and derivates. This update covers...
-

 93Vulnerabilities
93VulnerabilitiesOBIHAI PATCHES MEMORY CORRUPTION, DOS, CSRF VULNERABILITIES IN IP PHONES
Obihai Technology recently patched vulnerabilities in its ObiPhone IP phones that could have led to memory corruption, buffer overflow, and denial of service...
-

 172Vulnerabilities
172VulnerabilitiesMultiple Vulnerabilities in BHU WiFi “uRouter”
The BHU WiFi uRouter, manufactured and sold in China, looks great – and it contains multiple critical vulnerabilities. An unauthenticated attacker could...
-
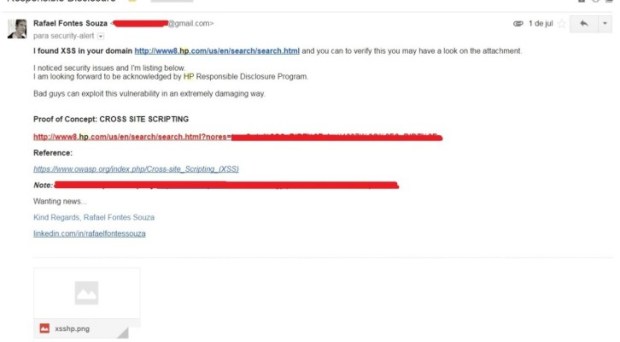
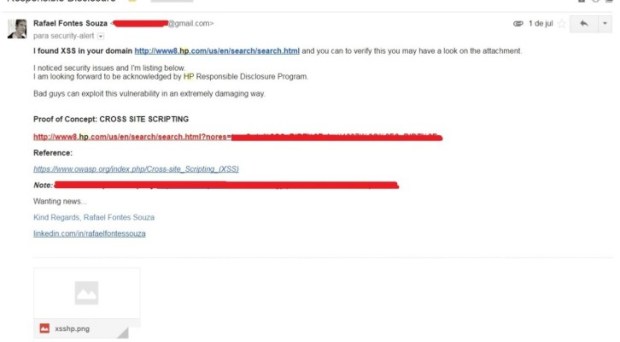 181Vulnerabilities
181VulnerabilitiesSecurity Researcher found vulnerabilities on the HP Website
The security expert Rafael Fontes Souza has discovered vulnerabilities in the website of HP (Hewlett Packard) and decided to explain concepts of...






