Search results for "vulnerabilities"
-

 2.4KVulnerabilities
2.4KVulnerabilities4 important vulnerabilities patched in VMware vRealize Log Insight
VRealize Log Insight is a log collecting and analytics virtual appliance that gives administrators the ability to collect, display, manage, and analyze...
-

 5.0KVulnerabilities
5.0KVulnerabilitiesSecurity Navigator Research: Some Vulnerabilities Date Back to the Last Millennium
Vulnerability analysis results in Orange Cyberdefenses’ Security Navigator show that some vulnerabilities first discovered in 1999 are still found in networks today....
-
 5.1KVulnerabilities
5.1KVulnerabilities4 critical BIOS vulnerabilities affect DELL Laptops like Alienware, Inspiron, Vostro models
Technology business Dell has its headquarters in the United States. It is in the business of creating and selling computers as well...
-

 1.2KVulnerabilities
1.2KVulnerabilitiesFour server-side request forgery (SSRF) vulnerabilities impacting different Azure services
Orca, a business that specializes in cloud security, has disclosed information on four server-side request forgery (SSRF) vulnerabilities that affect several Azure...
-

 5.0KVulnerabilities
5.0KVulnerabilitiesCisco Issues Warning for Unpatched Vulnerabilities in EoL Business Routers
Cisco has warned of two security vulnerabilities affecting end-of-life (EoL) Small Business RV016, RV042, RV042G, and RV082 routers that it said will...
-
 264Vulnerabilities
264VulnerabilitiesExploit code to hack Lexmark printers and photocopiers published, uses zero day vulnerabilities
The American corporation Lexmark International, Inc. is a privately owned business that specializes in the production of laser printers and other image...
-

 616Malware
616MalwareRansomware gangs are exploiting Fortinet Devices vulnerabilities. Patch these high-severity command injection flaws
Fortinet, a company that develops next-generation firewalls, VPNs, antivirus, and endpoint solutions, among other products, issued a public security advisory on October...
-

 417Vulnerabilities
417VulnerabilitiesFortinet and Zoho Urge Customers to Patch Enterprise Software Vulnerabilities
Fortinet has warned of a high-severity flaw affecting multiple versions of FortiADC application delivery controller that could lead to the execution of...
-

 1.6KVulnerabilities
1.6KVulnerabilitiesAPI Vulnerabilities leaked client’s data of BMW, Roll Royce, Mercedes-Benz, Ferrari, Porsche, Jaguar, Land Rover, Ford, KIA, Honda, Infiniti, Nissan, Acura, Hyundai, Toyota, and Genesis
Hackers may have been able to perform malicious activity, such as unlocking, starting, and tracking cars, as well as exposing customers’ personal...
-
 3.9KMalware
3.9KMalwareLinux Malware Exploit Over 30 Vulnerabilities in WordPress Themes & Plugins
In an attempt to inject malicious JavaScript into WordPress plugins and themes that are outdated, a previously detected Linux malware that is...
-

 1.4KVulnerabilities
1.4KVulnerabilities4 critical vulnerabilities in Samba: Patch immediately
Samba is a free software re-implementation of the SMB networking protocol that offers file and print services for a variety of Microsoft...
-

 4.2KVulnerabilities
4.2KVulnerabilitiesSamba Issues Security Updates to Patch Multiple High-Severity Vulnerabilities
Samba has released software updates to remediate multiple vulnerabilities that, if successfully exploited, could allow an attacker to take control of affected...
-
 4.1KVulnerabilities
4.1KVulnerabilitiesTop 5 Web App Vulnerabilities and How to Find Them
Web applications, often in the form of Software as a Service (SaaS), are now the cornerstone for businesses all over the world....
-

 5.1KVulnerabilities
5.1KVulnerabilitiesCritical vulnerabilities affecting VMware Workspace ONE Access and Identity Manager
VMware has patched two security flaws in VMware Workspace ONE Access and Identity Manager as of today: Authenticated Remote Code Execution Vulnerability...
-
 1.8KMalware
1.8KMalwareNew Go-based Botnet Exploiting Exploiting Dozens of IoT Vulnerabilities to Expand its Network
A novel Go-based botnet called Zerobot has been observed in the wild proliferating by taking advantage of nearly two dozen security vulnerabilities...
-

 4.8KVulnerabilities
4.8KVulnerabilities7 security vulnerabilities in Sophos Firewall version
Customers have been alerted by Sophos that many vulnerabilities, including ones that may lead to arbitrary code execution, have been patched in...
-

 2.8KData Security
2.8KData SecurityMost exploited API Vulnerabilities in 2022
It is common knowledge that maintaining a high level of cyber security has rapidly become one of the top priorities for businesses...
-

 2.3KVulnerabilities
2.3KVulnerabilitiesVulnerabilities in Mastodon, allow to download or delete all the files on the server, including those exchanged via Direct Messages and change everyone’s profile image
Mastodon has been under the limelight as a result of the exodus of former Twitter users who left the platform in response...
-

 247Vulnerabilities
247Vulnerabilities3 vulnerabilities in Zoom Client and Zoom Rooms allows threat actor to become admin of the machine
According to the most recent research, three recently found security flaws in Zoom can grant an attacker access to root or SYSTEM...
-
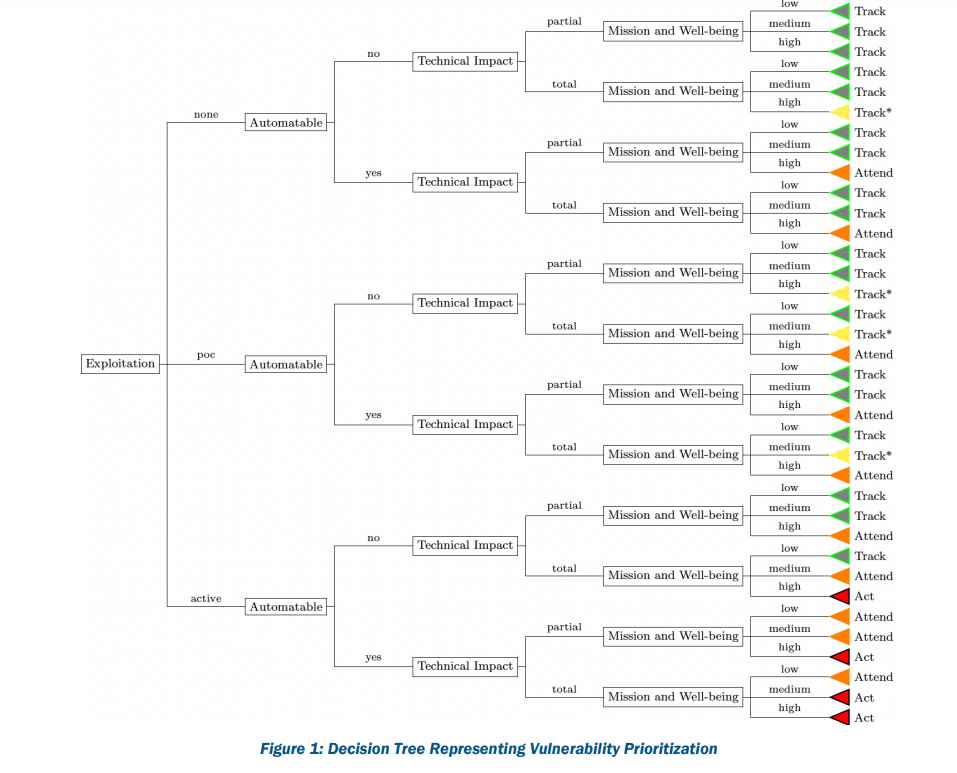
 3.7KData Security
3.7KData Security6 factors to consider for prioritizing remediation of vulnerabilities in a network using SSVC strategy
Given that 2021 set a record for the number of vulnerabilities disclosed and that threat actors improved their capacity to weaponize vulnerabilities,...
-

 2.8KData Security
2.8KData SecurityUpdate firmware of these Lenovo ThinkBook, IdeaPad, and Yoga laptops models as 3 critical vulnerabilities allow them to be hacked forever, even after removing the hard drive
Critical flaws that affect many ThinkBook, IdeaPad, and Yoga laptop models have been resolved by Lenovo and may have allowed an attacker...






