Search results for "vulnerabilities"
-
 1.5KVulnerabilities
1.5KVulnerabilitiesMicrosoft Warns of Uptick in Hackers Leveraging Publicly-Disclosed 0-Day Vulnerabilities
Microsoft is warning of an uptick among nation-state and criminal actors increasingly leveraging publicly-disclosed zero-day vulnerabilities for breaching target environments. The tech...
-

 300Vulnerabilities
300VulnerabilitiesCISA Warns of Critical Vulnerabilities in 3 Industrial Control System Software
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has published three Industrial Control Systems (ICS) advisories about multiple vulnerabilities in software from...
-
 1.4KVulnerabilities
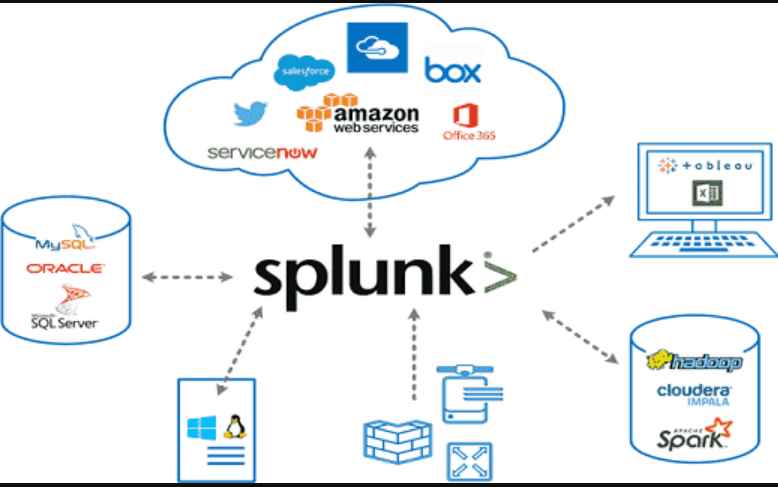
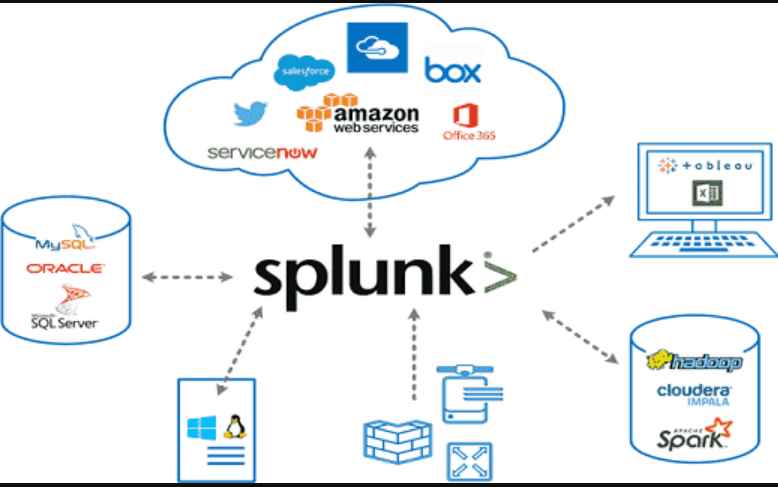
1.4KVulnerabilitiesEight high-severity vulnerabilities in Splunk Enterprise Software allow threat actors to take control of a network
With the use of the Splunk software, real-time data can be collected, indexed, and corroborated in a searchable repository from which graphs,...
-
 2.0KVulnerabilities
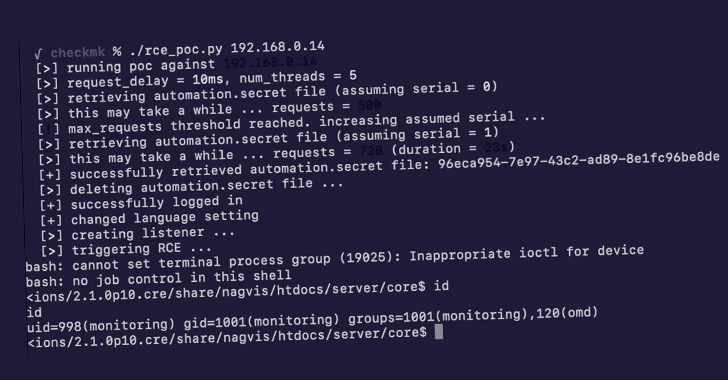
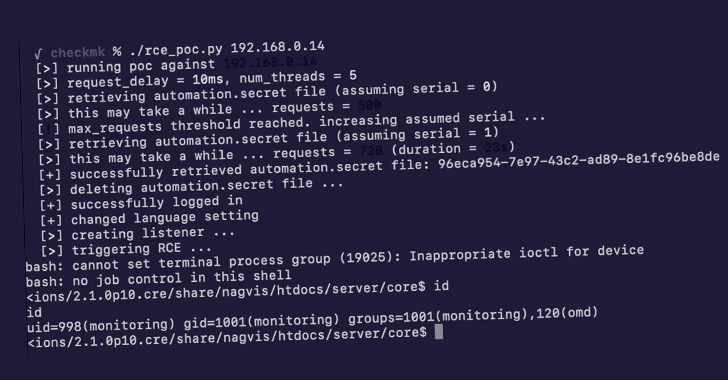
2.0KVulnerabilitiesMultiple Vulnerabilities Reported in Checkmk IT Infrastructure Monitoring Software
Multiple vulnerabilities have been disclosed in Checkmk IT Infrastructure monitoring software that could be chained together by an unauthenticated, remote attacker to...
-
 2.3KVulnerabilities
2.3KVulnerabilitiesOpenSSL Releases Patch for 2 New High-Severity Vulnerabilities
The OpenSSL project has rolled out fixes to contain two high-severity flaws in its widely used cryptography library that could result in...
-
 3.7KVulnerabilities
3.7KVulnerabilitiesLast Years Open Source – Tomorrow’s Vulnerabilities
Linus Torvalds, the creator of Linux and Git, has his own law in software development, and it goes like this: “given enough...
-

 2.7KVulnerabilities
2.7KVulnerabilities2 important vulnerabilities (XXE & RCE) in VMware Cloud Foundation. Patch immediately
The serious XML External Entity (XXE) and remote code execution (RCE) vulnerabilities in Cloud Foundation have been patched, according to VMware. CVE-2021-39144...
-

 3.2KVulnerabilities
3.2KVulnerabilitiesHackers Actively Exploiting Cisco AnyConnect and GIGABYTE Drivers Vulnerabilities
Cisco has warned of active exploitation attempts targeting a pair of two-year-old security flaws in the Cisco AnyConnect Secure Mobility Client for...
-

 2.8KVulnerabilities
2.8KVulnerabilities3 critical vulnerabilities in Veeam Backup & Replication solution allow ransomware to steal credentials & encrypt your backups
For virtual environments built on VMware vSphere, Nutanix AHV, and Microsoft Hyper-V hypervisors, Veeam Backup & Replication is a proprietary backup application....
-

 1.4KVulnerabilities
1.4KVulnerabilitiesVulnerabilities in Nginx allows DoS attack; Patch now
Out-of-bounds read causing DoS Attack – CVE-ID: CVE-2022-41741, CVE-2022-41742 A remote attacker might exploit this nginx vulnerability to access potentially sensitive data or launch...
-

 2.4KLeaks
2.4KLeaksWordPress Security Update 6.0.3 Patches 16 Vulnerabilities
This week, WordPress 6.0.3 began to be distributed. The most recent security update fixes 16 flaws. In addition to addressing open redirect,...
-
 2.5KVulnerabilities
2.5KVulnerabilities5 critical remote code execution vulnerabilities in Linux kernel. !Patch immediately!
The Linux kernel WiFi stack has five serious flaws, according to research, which a hacker might use to execute arbitrary code or...
-

 2.7KVulnerabilities
2.7KVulnerabilitiesTwo important vulnerabilities ( CVSSv3 score > 7) in VMware ESXi, vCenter Server & Cloud Foundation
The leader in virtualization and cloud computing technologies, VMware, has released a security fix for two vulnerabilities in its vCenter Server software...
-
 4.0KVulnerabilities
4.0KVulnerabilities3 critical malicious code execution vulnerabilities in Linux kernel
A security investigator has discovered three new code execution flaws in the Linux kernel that might be exploited by a local or...
-

 1.2KVulnerabilities
1.2KVulnerabilitiesTwo zero day vulnerabilities in Exchange Server. No patch available
Microsoft has acknowledged that it is aware of two zero-day vulnerabilities in Exchange Server that have been used in deliberate attacks. The...
-

 571Vulnerabilities
571VulnerabilitiesTwo critical WhatsApp vulnerabilities allow hacking WhatsApp (Android & iOS) via call or video file. Update immediately
Two security flaws in WhatsApp’s chat app for iOS and Android that might have been used to remotely execute malware on the device...
-

 3.8KLeaks
3.8KLeaksVulnerabilities in the iBoot Power Distribution Unit Let Hackers Remotely Shut Down Devices
Researchers found serious flaws in Dataprobe’s iBoot power distribution unit (PDU), which may be used by hostile parties to remotely hijack the...
-

 1.9KVulnerabilities
1.9KVulnerabilitiesHackers Exploit WebLogic Vulnerabilities to Deliver Cryptocurrency-Mining Malware
In order to deliver cryptocurrency mining malware, the threat actors are actively exploiting both old and newly discovered vulnerabilities in Oracle WebLogic...
-
 1.8KVulnerabilities
1.8KVulnerabilitiesLenovo Several High-Severity BIOS Vulnerabilities Impacts Hundreds of Devices
Recently, Lenovo’s new BIOS updates fixes the high-severity vulnerabilities impacting hundreds of devices in several models (Desktop, All in One, IdeaCentre, Legion,...
-

 1.4KVulnerabilities
1.4KVulnerabilitiesCritical BIOS vulnerabilities affect Lenovo Desktop, Desktop AIO, Smart Edge, Smart Office, ThinkStation, and ThinkSystem models
Four BIOS-related vulnerabilities have recently been discovered, according to a new security alert from Lenovo. Threat actors can use these flaws to...
-

 2.7KMalware
2.7KMalwareMirai Variant MooBot Botnet Exploiting D-Link Router Vulnerabilities
A variant of the Mirai botnet known as MooBot is co-opting vulnerable D-Link devices into an army of denial-of-service bots by taking...






