Search results for "vulnerabilities"
-

 2.6KVulnerabilities
2.6KVulnerabilities3 critical vulnerabilities in XEN project allows to take control of host OS via VMs in x86 PV
Xen is a hypervisor that allows multiple computer operating systems to run on the same computer hardware simultaneously. The Xen Project community...
-

 4.0KTutorials
4.0KTutorialsHow to find zero-day vulnerabilities with Fuzz Faster U Fool (ffuf): Detailed free fuzzing tool tutorial
Today, the specialists of the Cyber Security 360 course of the International Institute of Cyber Security (IICS) will show us in detail...
-

 1.6KVulnerabilities
1.6KVulnerabilitiesTwo critical command injection vulnerabilities in Fujitsu cloud storage system allow remote encryption or deletion of files
Two bugs in the web interface of a Fujitsu cloud storage system would allow authenticated threat actors to read, write, and even...
-

 3.0KVulnerabilities
3.0KVulnerabilities8 critical vulnerabilities in GitLab would allow hackers to install backdoors in your code
In its most recent security release, GitLab announced the launching of GitLab Community Edition (CE) and GitLab Enterprise Edition (EE) versions 15.01,...
-

 4.0KVulnerabilities
4.0KVulnerabilitiesCISA Warned About Critical Vulnerabilities in Illumina’s DNA Sequencing Devices
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) and Food and Drug Administration (FDA) have issued an advisory about critical security vulnerabilities...
-

 4.9KVulnerabilities
4.9KVulnerabilities9 critical vulnerabilities in Mozilla Thunderbird allow easy takeover of your machine via email
Cybersecurity specialists reported the detection of multiple flaws in the Mozilla Thunderbird multiplatform email client, which successful exploitation would allow malicious hackers...
-

 3.3KVulnerabilities
3.3KVulnerabilities2 critical vulnerabilities in Apache Traffic Server: Patch immediately
Information security specialists reported the detection of two severe flaws in Apache Traffic Server (ATS), a modular, high-performance reverse proxy and forward...
-

 4.3KMalware
4.3KMalwareEnemyBot: New IoT malware exploits one-day vulnerabilities to hack thousands of devices
Cybersecurity specialists from AT&T Alien Labs report the detection of an Internet of Things (IoT) malware variant targeting content management systems (CMS),...
-
 3.1KMalware
3.1KMalwareA New Linux-based Botnet Targeting Vulnerabilities in Web Servers & Android Servers
Currently, a new botnet extends its reach with the help of code originating from various pieces of malware. The company is doing...
-
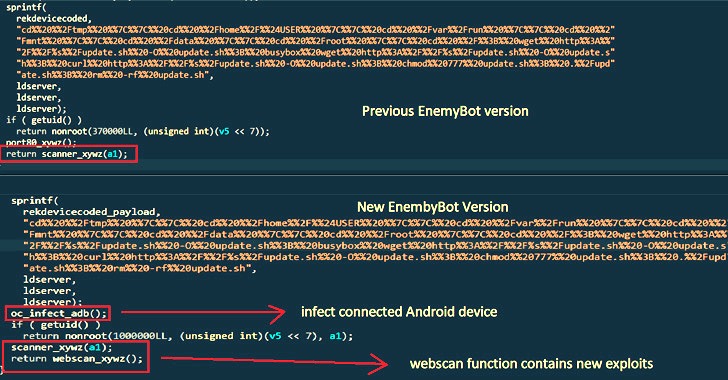
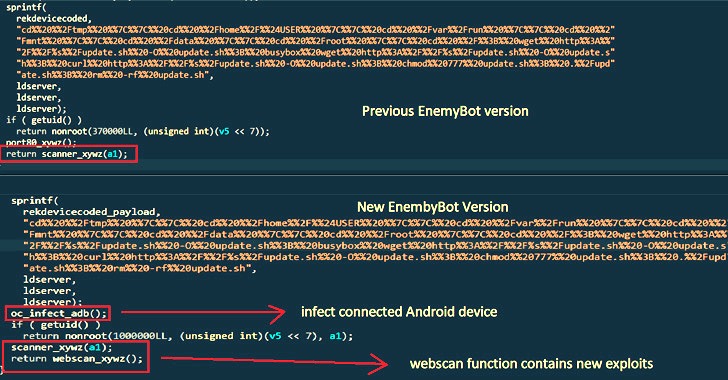 2.6KMalware
2.6KMalwareEnemyBot Linux Botnet Now Exploits Web Server, Android and CMS Vulnerabilities
A nascent Linux-based botnet named Enemybot has expanded its capabilities to include recently disclosed security vulnerabilities in its arsenal to target web...
-

 455Leaks
455LeaksChrome 102 Patches 32 Vulnerabilities
Google is preparing to promote Chrome 102 to take its place after releasing Chrome 101 just over a month ago. The new...
-

 2.9KVulnerabilities
2.9KVulnerabilities7 high-severity vulnerabilities in Open Automation Software Platform, used for connectivity between PLCs and IoT devices
Cisco Talos researchers detected multiple critical vulnerabilities in Open Automation Software Platform, a solution powered by a universal data connector that allows...
-

 2.9KVulnerabilities
2.9KVulnerabilitiesCritical security vulnerabilities in NETGEAR BR200 and BR500 routers: Impossible to patch these issues
Tech firm NETGEAR released a security alert related to multiple vulnerabilities in the BR200 and BR500 routers. As per the report, a...
-

 3.2KVulnerabilities
3.2KVulnerabilities3 critical vulnerabilities in SonicWall SMA 1000 SSLVPN affect over 500k companies
In a security alert, SonicWall has strongly urged its customers to address some security flaws in its Secure Mobile Access (SMA) Series...
-

 1.1KVulnerabilities
1.1KVulnerabilitiesCRITICAL VULNERABILITIES ALLOW HACKING MULTIPLE KONICA MINOLTA DEVICES
Researchers from SEC Consult Vulnerability Lab reported the detection of a sandbox breakout vulnerability present in some Konica Minolta bizhub multifunctional models....
-

 535Vulnerabilities
535VulnerabilitiesNew tool to find vulnerabilities in the way applications like Microsoft Word and Adobe Acrobat process JavaScript: Cooperative mutation attack
A group of researchers developed a tool capable of detecting errors in the way applications such as Adobe Acrobat or Microsoft Word...
-

 841Leaks
841LeaksVulnerabilities That Allow Hijacking of Most Ransomware to Prevent File Encryption
A cyber-attack is a malicious attack undertaken by cybercriminals against single or numerous computers, computer systems, networks, or infrastructures utilizing one or...
-

 4.8KVulnerabilities
4.8KVulnerabilities17 critical vulnerabilities affect 16,000 F5 BIG-IP security products
A report by F5 Networks points to the detection of a critical vulnerability that would allow threat actors with access to an...
-
 3.9KVulnerabilities
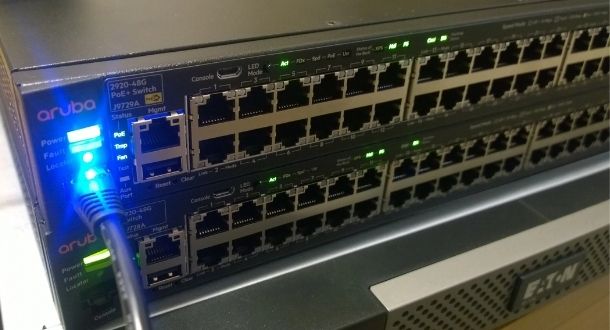
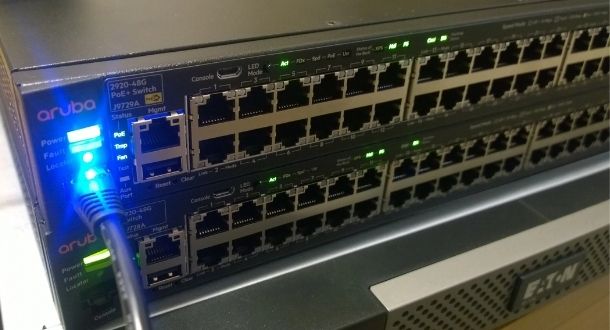
3.9KVulnerabilitiesThousands of airports, hospitals and hotels affected by critical vulnerabilities in Aruba and Avaya switches
Five critical remote code execution (RCE) vulnerabilities have been confirmed to be found in millions of Aruba and Avaya devices whose exploitation...
-

 966Incidents
966IncidentsYou can earn 1.5 million dollar by finding vulnerabilities in Android 13 Beta
Google has decided to temporarily increase payments in its vulnerability bounty program for those researchers who submit reports of flaws in Android...
-

 4.7KVulnerabilities
4.7KVulnerabilitiesZero-day vulnerabilities in Netatalk affect NAS products from Synology, QNAP and Western Digital. Protect your storage solutions before they’re encrypted with ransomware
Several manufacturers of network-attached storage (NAS) solutions have alerted their customers to the detection of critical vulnerabilities in Netatalk. The exploitation of...






