Search results for "vulnerabilities"
-

 1.4KVulnerabilities
1.4KVulnerabilitiesCritical BIOS vulnerabilities affect Lenovo Desktop, Desktop AIO, Smart Edge, Smart Office, ThinkStation, and ThinkSystem models
Four BIOS-related vulnerabilities have recently been discovered, according to a new security alert from Lenovo. Threat actors can use these flaws to...
-

 2.7KMalware
2.7KMalwareMirai Variant MooBot Botnet Exploiting D-Link Router Vulnerabilities
A variant of the Mirai botnet known as MooBot is co-opting vulnerable D-Link devices into an army of denial-of-service bots by taking...
-

 5.2KVulnerabilities
5.2KVulnerabilitiesGoogle will pay up to $31,000 to those who find vulnerabilities in its open source software
Google has launched its new Vulnerability Bounty Program for its open source software. The company will pay up to more than US$31,000...
-

 4.6KVulnerabilities
4.6KVulnerabilitiesCISA Adds 10 New Known Actively Exploited Vulnerabilities to its Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday added 10 new actively exploited vulnerabilities to its Known Exploited Vulnerabilities (KEV)...
-

 1.8KVulnerabilities
1.8KVulnerabilitiesCISA Adds 7 New Actively Exploited Vulnerabilities to Catalog
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday moved to add a critical SAP security flaw to its Known Exploited...
-

 3.2KVulnerabilities
3.2KVulnerabilitiesApple Releases Security Updates to Patch Two New Zero-Day Vulnerabilities
Apple on Wednesday released security updates for iOS, iPadOS, and macOS platforms to remediate two zero-day vulnerabilities previously exploited by threat actors...
-

 3.3KVulnerabilities
3.3KVulnerabilitiesÆPIC and SQUIP Vulnerabilities Found in Intel and AMD Processors
A group of researchers has revealed details of a new vulnerability affecting Intel CPUs that enables attackers to obtain encryption keys and...
-
 3.5KVulnerabilities
3.5KVulnerabilitiesFix these Windows vulnerabilities before someone exploits them
On many occasions, security flaws appear that can compromise our devices. They can affect operating systems like Windows, applications, drivers. It is...
-

 3.5KVulnerabilities
3.5KVulnerabilitiesHackers Use Open Redirect Vulnerabilities in Online Services to Deliver Phishing Content
Researchers at Resecurity noticed threat actors leveraging Open Redirect Vulnerabilities which is popular in online services and apps to evade spam filters...
-

 2.2KVulnerabilities
2.2KVulnerabilities3 critical vulnerabilities in Argo CD allow complete take over of your applications and servers
Argo CD is a declarative GitOps continuous delivery tool for Kubernetes. It is required because Application definitions, configurations, and environments should be...
-

 1.1KVulnerabilities
1.1KVulnerabilities3 critical vulnerabilities in 9 Cisco Router models allows complete takeover of any network
3 vulnerabilities in Cisco Small Business RV160, RV260, RV340, and RV345 Series Routers could allow an unauthenticated threat actor to remotely execute...
-
 4.1KVulnerabilities
4.1KVulnerabilitiesCritical Security Vulnerabilities In Netgear Business Routers Which The Netgear Team Can’t Fix. Stop Using These Routers As Soon As Possible
The manufacturer NETGEAR has issued an urgent notice for all owners of professional VPN and firewall routers, the affected models are the...
-

 2.0KVulnerabilities
2.0KVulnerabilities3 vulnerabilities affecting IBM QRadar SIEM. Patch immediately
IBM has published details of vulnerabilities affecting IBM QRadar SIEM. Below are the details. 1) Improper input validation CVE-ID: CVE-2017-9801 Description The...
-

 2.7KVulnerabilities
2.7KVulnerabilities3 Critical Vulnerabilities In Lenovo Laptops’ UEFI (70 Models Including Thinkbook) Allow Them To Be Hacked Forever, Even After Removing The Hard Drive
Lenovo released security fixes to address three vulnerabilities that reside in the UEFI firmware shipped with over 70 product models, including several...
-

 1.8KMalware
1.8KMalwareNew UEFI Firmware Vulnerabilities Impact Several Lenovo Notebook Models
Consumer electronics maker Lenovo on Tuesday rolled out fixes to contain three security flaws in its UEFI firmware affecting over 70 product...
-

 3.2KVulnerabilities
3.2KVulnerabilities11 important vulnerabilities in Fortinet products FortiOS, FortiAnalyzer, FortiADC, FortiManager, FortiProxy, FortiClient, FortiDeceptor, FortiSwitch, FortiRecoder & FortiVoiceEnterprise
Fortinet, an American multinational corporation headquartered in Sunnyvale, California. The company develops and sells cybersecurity solutions, such as physical firewalls, antivirus software,...
-

 2.0KVulnerabilities
2.0KVulnerabilitiesSolving the indirect vulnerability enigma – fixing indirect vulnerabilities without breaking your dependency tree
Fixing indirect vulnerabilities is one of those complex, tedious and, quite frankly, boring tasks that no one really wants to touch. No...
-

 910Vulnerabilities
910VulnerabilitiesSAN storage products of Dell, Fujitsu, HP, Huawei, IBM, Brocade and Lenovo affected by 9 critical vulnerabilities
Broadcom published that software used by its storage networking company Brocade is affected by 9 important vulnerabilities, and the same vulnerabilities impact...
-
 2.1KVulnerabilities
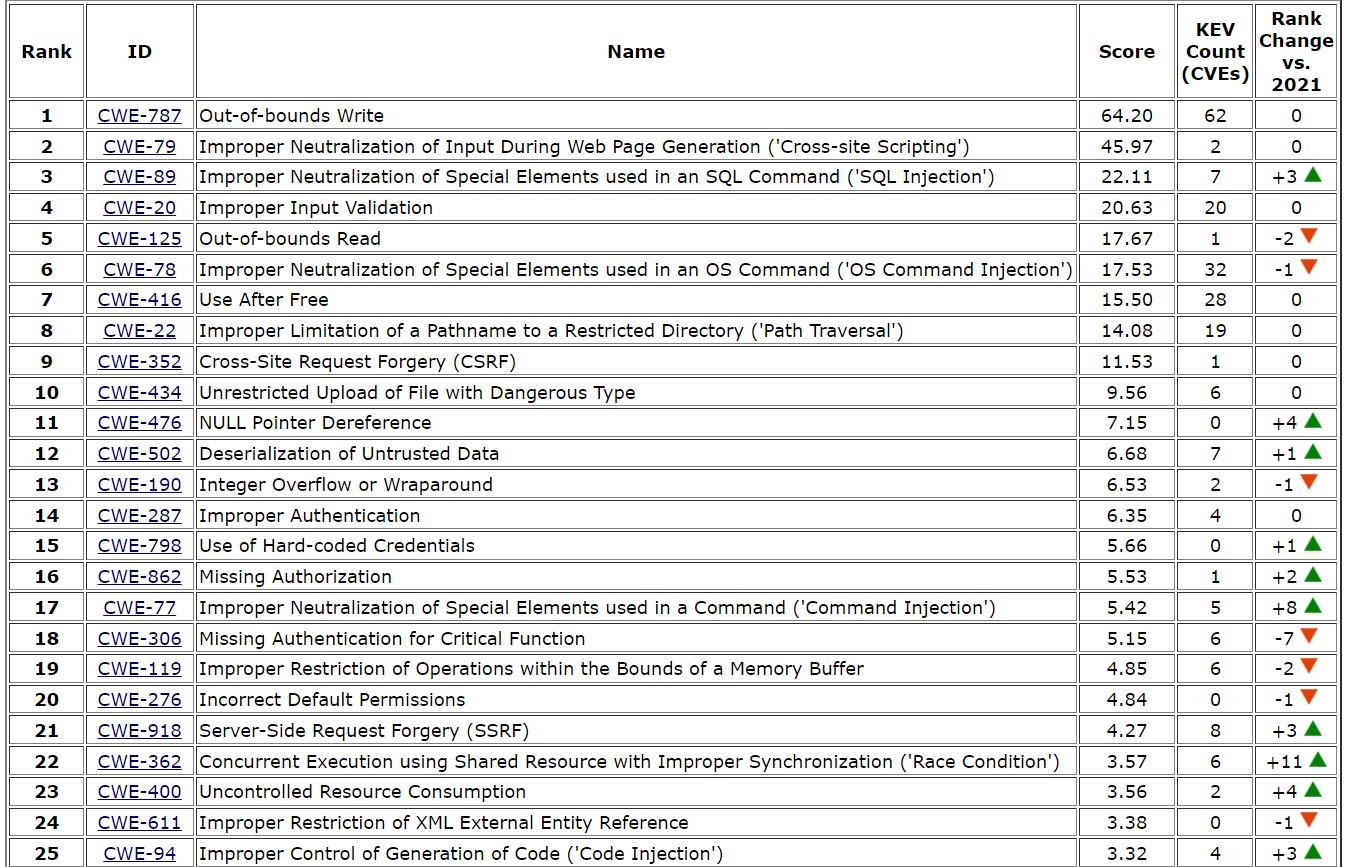
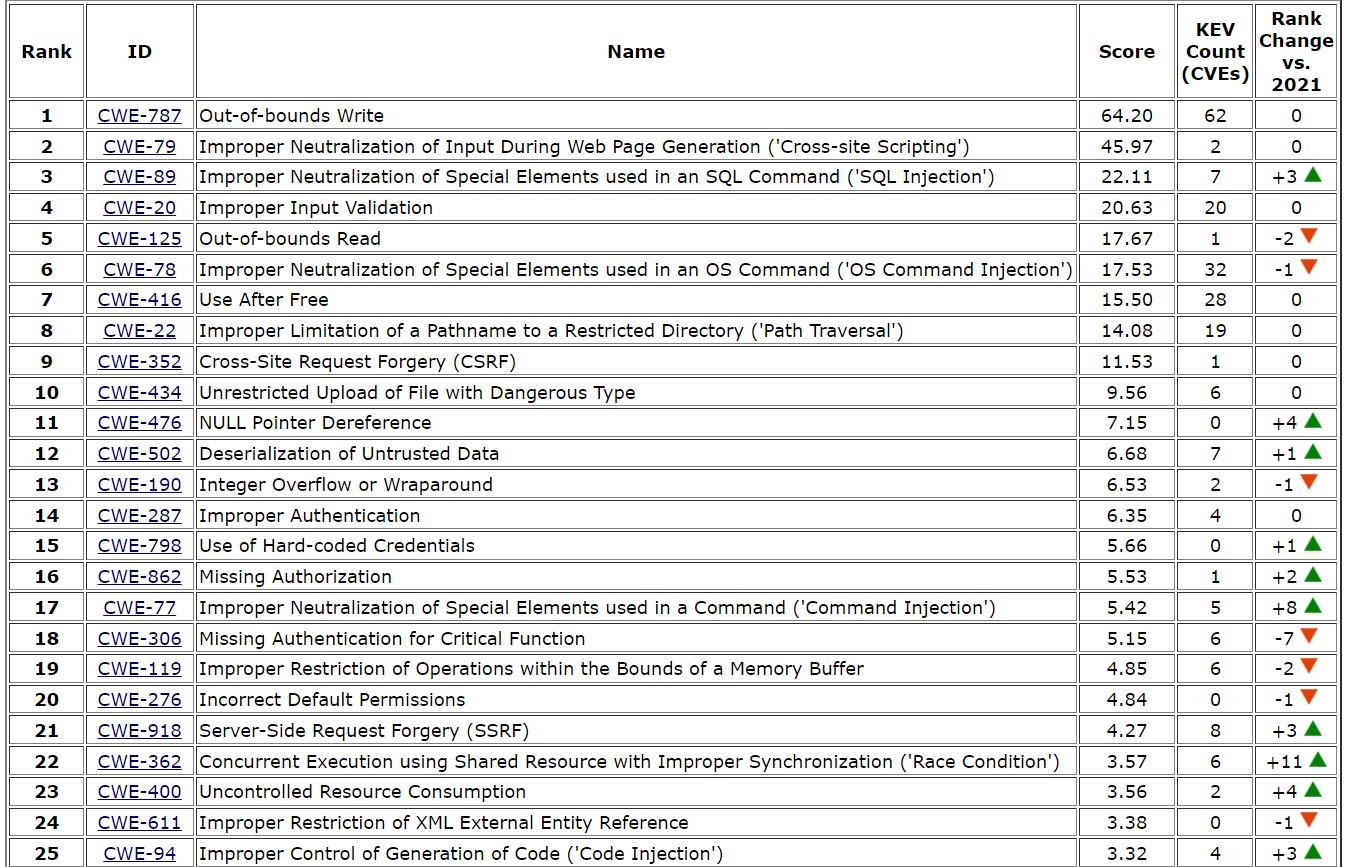
2.1KVulnerabilitiesTop 25 Most Dangerous vulnerabilities of 2022. Easily exploitable CWE (Common Weakness Enumeration)
Common Weakness Enumeration (CWE) is Managed by MITRE and it a released top 25 Most Dangerous Software vulnerabilities list. This list shows...
-

 2.1KVulnerabilities
2.1KVulnerabilitiesCritical Information disclosure, Incomplete cleanup and Race condition vulnerabilities in Citrix Hypervisor. Download hotfixes.
Citrix Hypervisor is an industry leading platform for cost-effective desktop, server, and cloud virtualization infrastructures. Citrix Hypervisor enables organizations of any size...
-

 1.5KVulnerabilities
1.5KVulnerabilitiesAmazon Linux server can be hacked easily. Critical Privilege Escalation vulnerability in Log4j Hotpatch released to fix Log4j vulnerabilities
Amazon Linux team is advising its clients about a critical vulnerability affecting Linux servers. Amazon Linux 2 is a Linux operating system...






