All posts tagged "privacy"
-

 4.2KSurveillance
4.2KSurveillanceWhat is a data breach & how to prevent one?
What is a data breach? A data breach is a security lapse where a non-authorized person can assess sensitive information without authorization....
-
 403Data Security
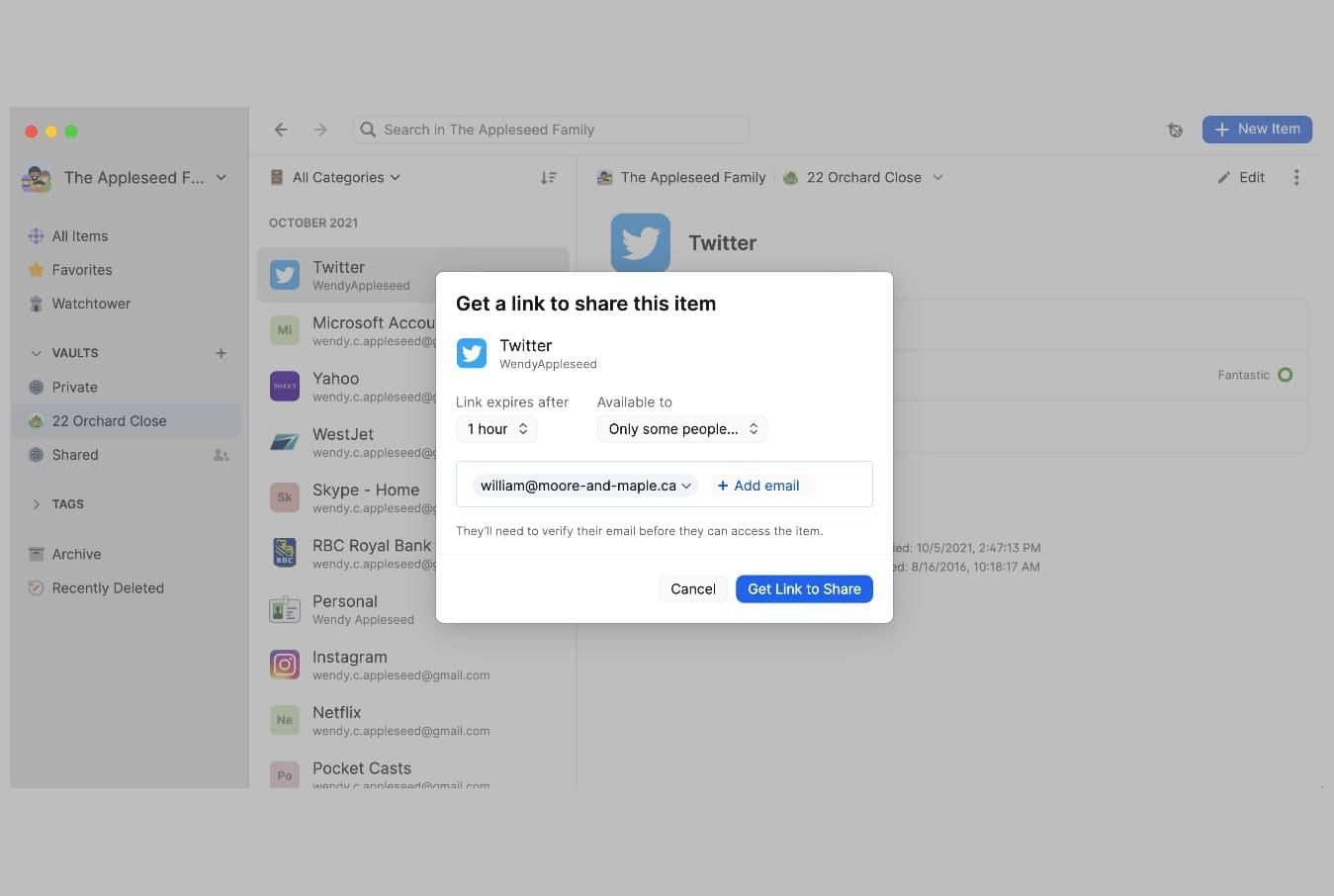
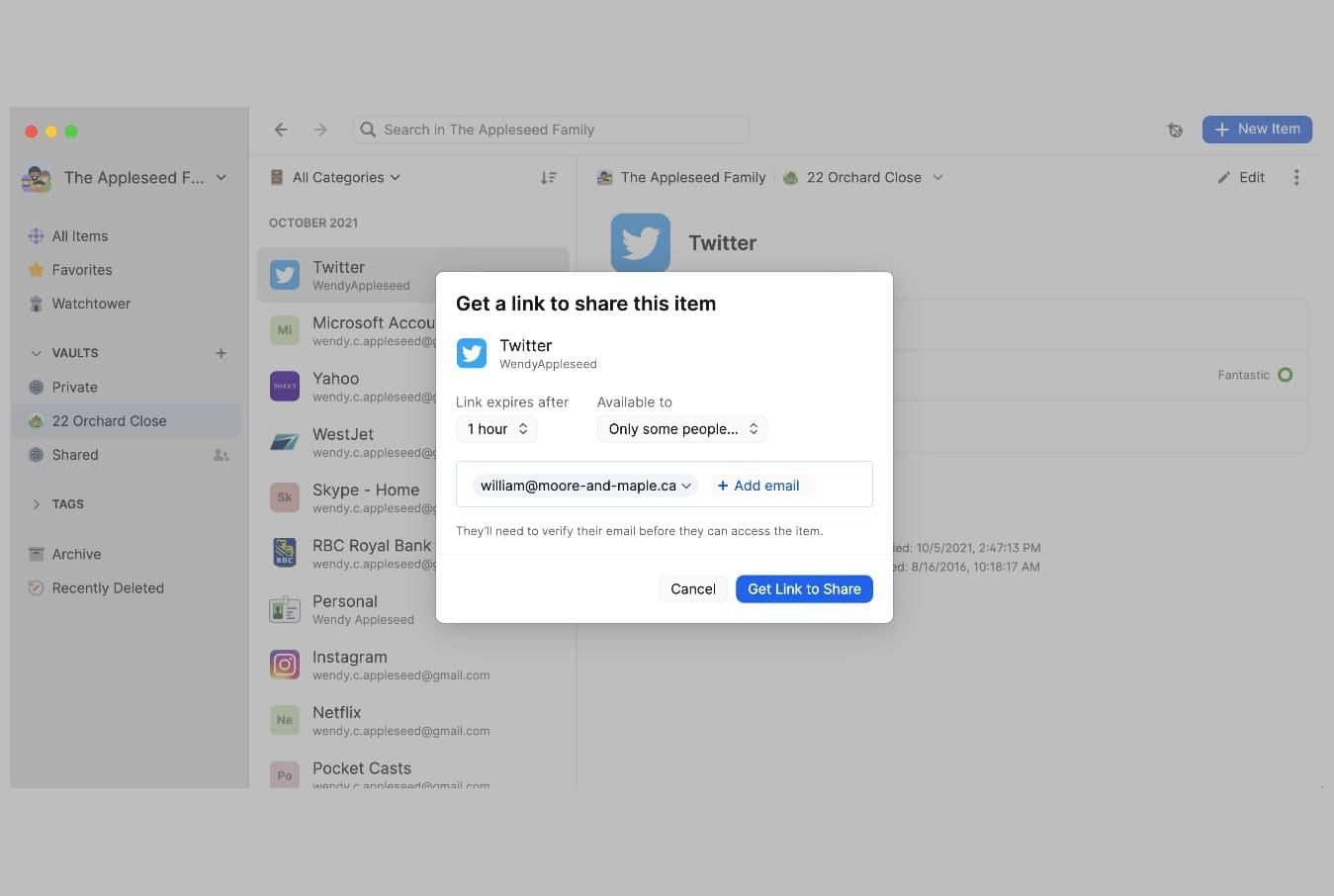
403Data SecurityPsst! tool by 1Password lets users share passwords using a link
1Password password manager has introduced a new tool called Password Secure Sharing Tool or Psst! that lets users share their passwords or...
-
 4.9KNews
4.9KNewsStorybooks for children app FarFaria exposed data of 3M users
According to FarFaria, its apps are “created for children ages 2-9” meaning that the incident exposed children to cybercriminals. Another day, another...
-
 5.2KNews
5.2KNewsThe Telegraph newspaper exposed 10TB of subscriber data
The data was exposed due to an unprotected Elasticsearch cluster and remained open to public access without any security authentication. Well-known security...
-

 3.2KSurveillance
3.2KSurveillanceLithuania wants users to dump Chinese phones citing data collection
Lithuania’s Defense Ministry has released a warning, urging consumers to get rid of their Chinese phones and not to buy new ones....
-
 3.4KHow To
3.4KHow ToHow to use VPN to access blocked websites?
Governments and regimes across the globe use censorship as a tool to control the flow of information. This article highlights how one...
-

 4.8KSurveillance
4.8KSurveillanceProtonMail logged, shared activist’s IP address with Swiss police
ProtonMail is being criticized for sharing French activist’s IP address with Swiss authorities while claiming it does not save logs. End-to-end encrypted...
-

 2.1KSurveillance
2.1KSurveillanceWhitehat hacker shows how to detect hidden cameras in Airbnb, hotels
The Whitehat hacker and IT security researcher Marcus Hutchins, who saved the world from the WannaCry ransomware attack, has shared simple yet...
-
 3.4KData Security
3.4KData Security$120 charging cable O.MG remotely steals data from Apple devices
Originally, O.MG Cable was introduced in 2019. In 2019, at DEFCON, an IT security researcher going by the online handle of MG...
-

 3.7KData Security
3.7KData Security38 million records exposed in Microsoft Power apps misconfiguration
According to researchers, the incident involved 47 government and private entities across the United States. The IT security researchers at UpGuard published...
-
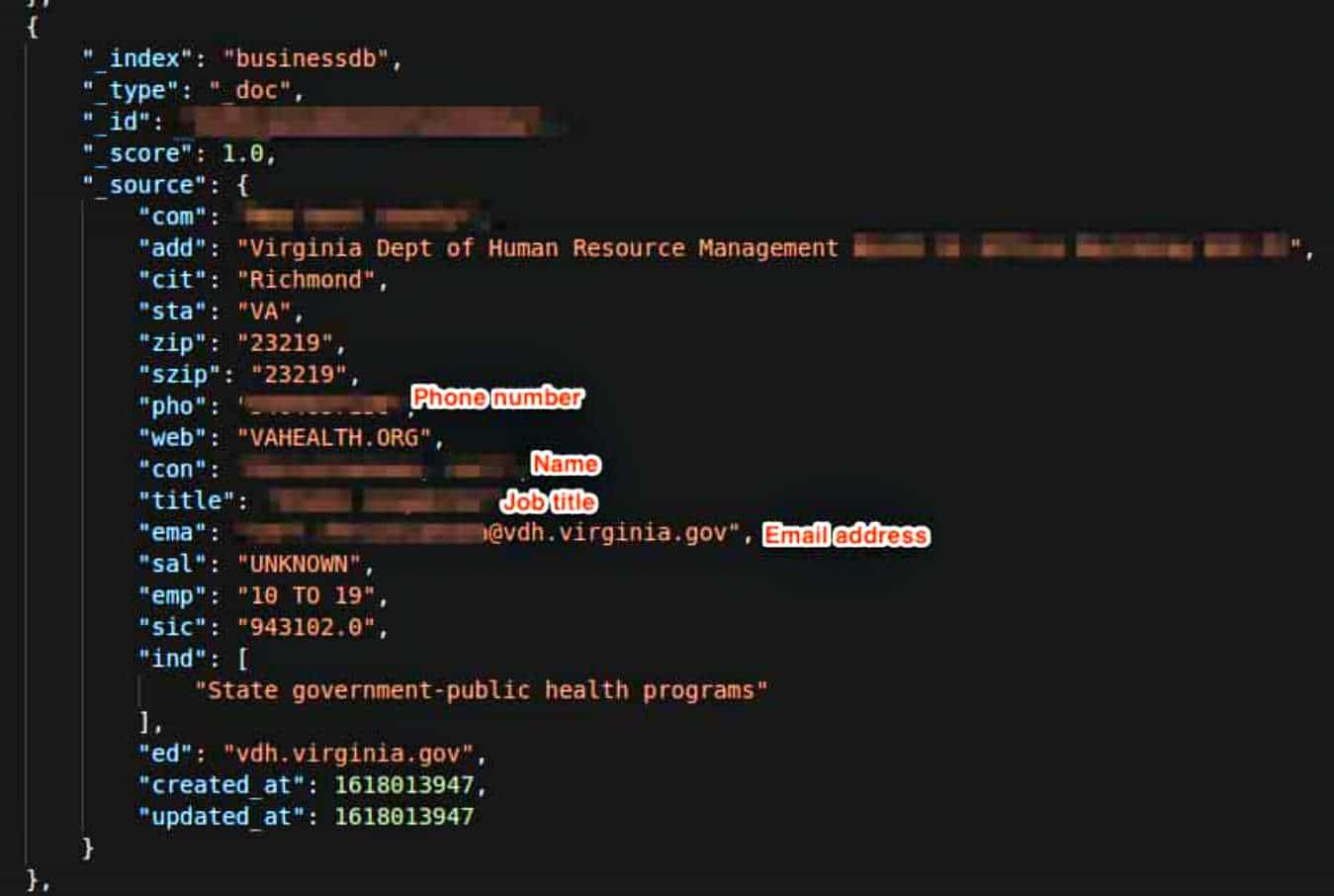
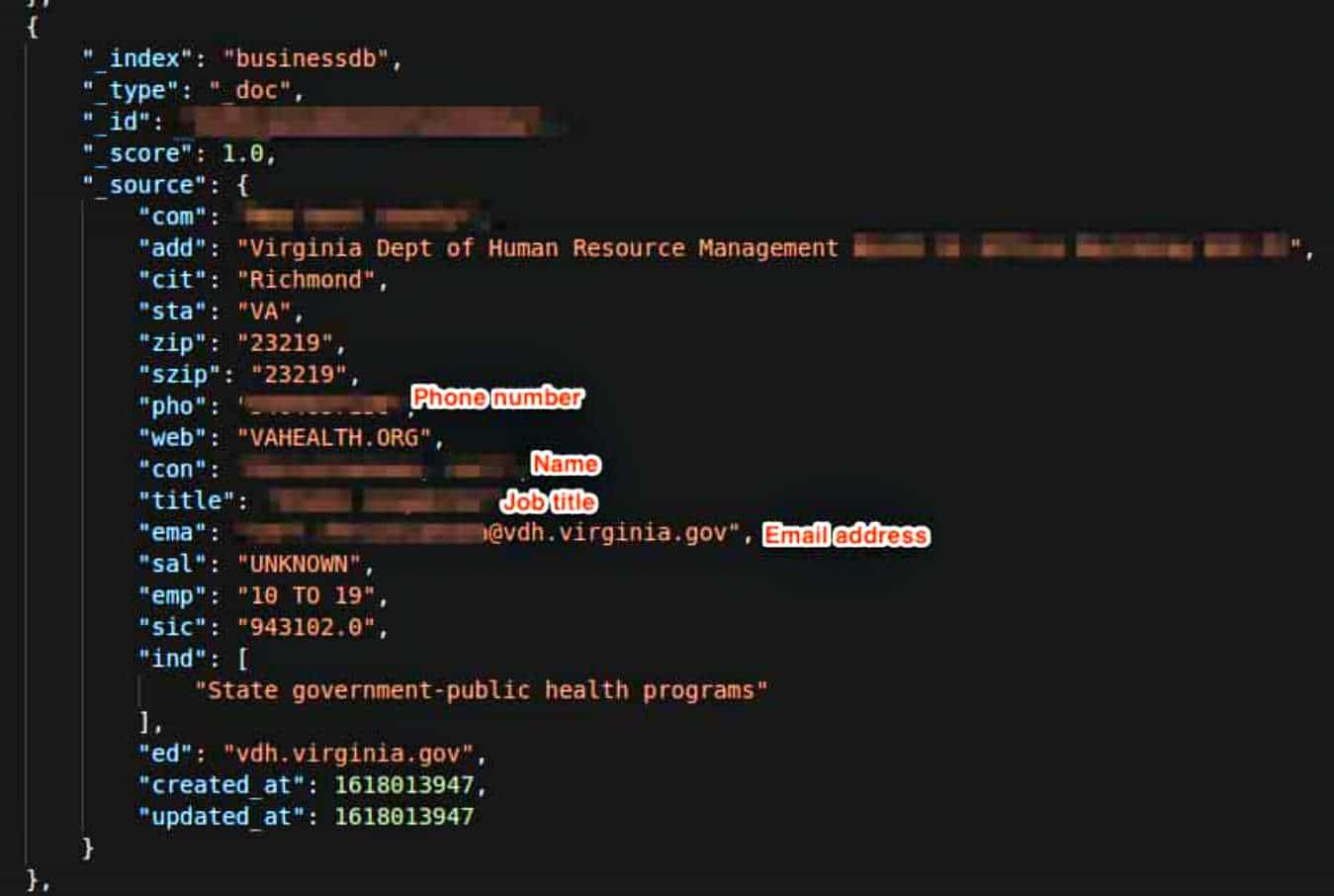 2.9KData Security
2.9KData SecurityLead generation firm exposed household data of 63 million Americans
Most of the email addresses checked by researchers contained .gov suffixes or indicated that the user worked for New York Police Department....
-

 2.5KData Security
2.5KData SecurityCalgary Parking Authority exposed sensitive data of residents
In total, CPA exposed 502 GB worth of data without any security authentication. Anurag Sen, a security researcher identified a data leak...
-
 1.2KData Security
1.2KData SecurityHousehold data of 35 million US residents exposed in database mess up
The Elasticsearch database was left exposed without any security authentication which means it could have been accessed by anyone with access to...
-
 720Data Security
720Data SecurityMisconfigured AWS bucket exposed 421GB of Artwork Archive data
The trove of data was left exposed unencrypted and without any password or security authentication. The team of IT security researchers at...
-
 5.0KData Security
5.0KData SecurityIsraeli spyware used in hacking phones of activists, journalists globally
In groundbreaking research, it has been revealed that governments and regimes around the world used NSO Group’s Pegasus spyware, a company based...
-
 3.4KData Security
3.4KData SecurityHow data collected in gaming can be used to breach user privacy
“Surveilling the Gamers: Privacy Impacts of the Video Game Industry,” a new research reveals how personal and financial data collected by gaming...
-
 2.5KGeek
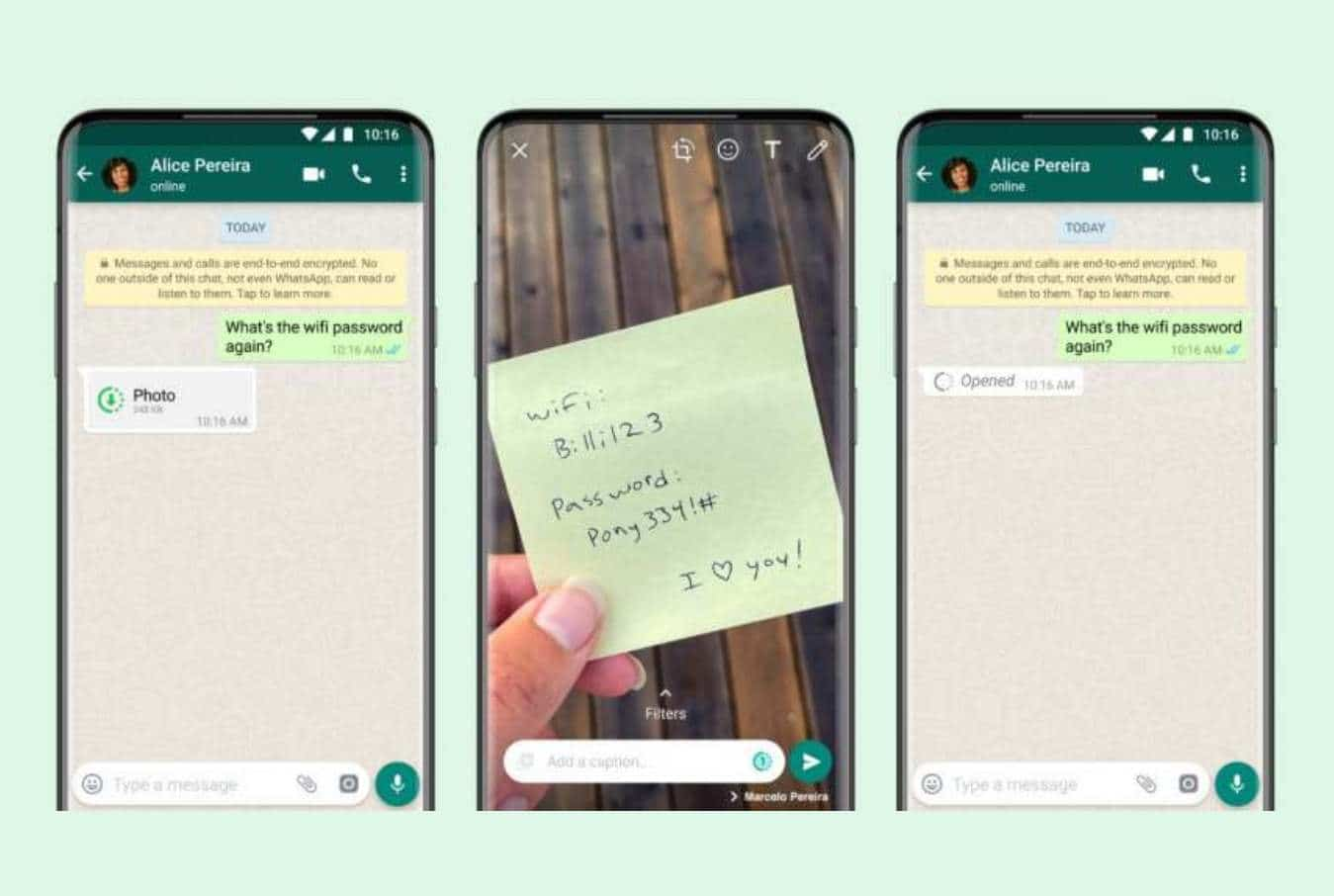
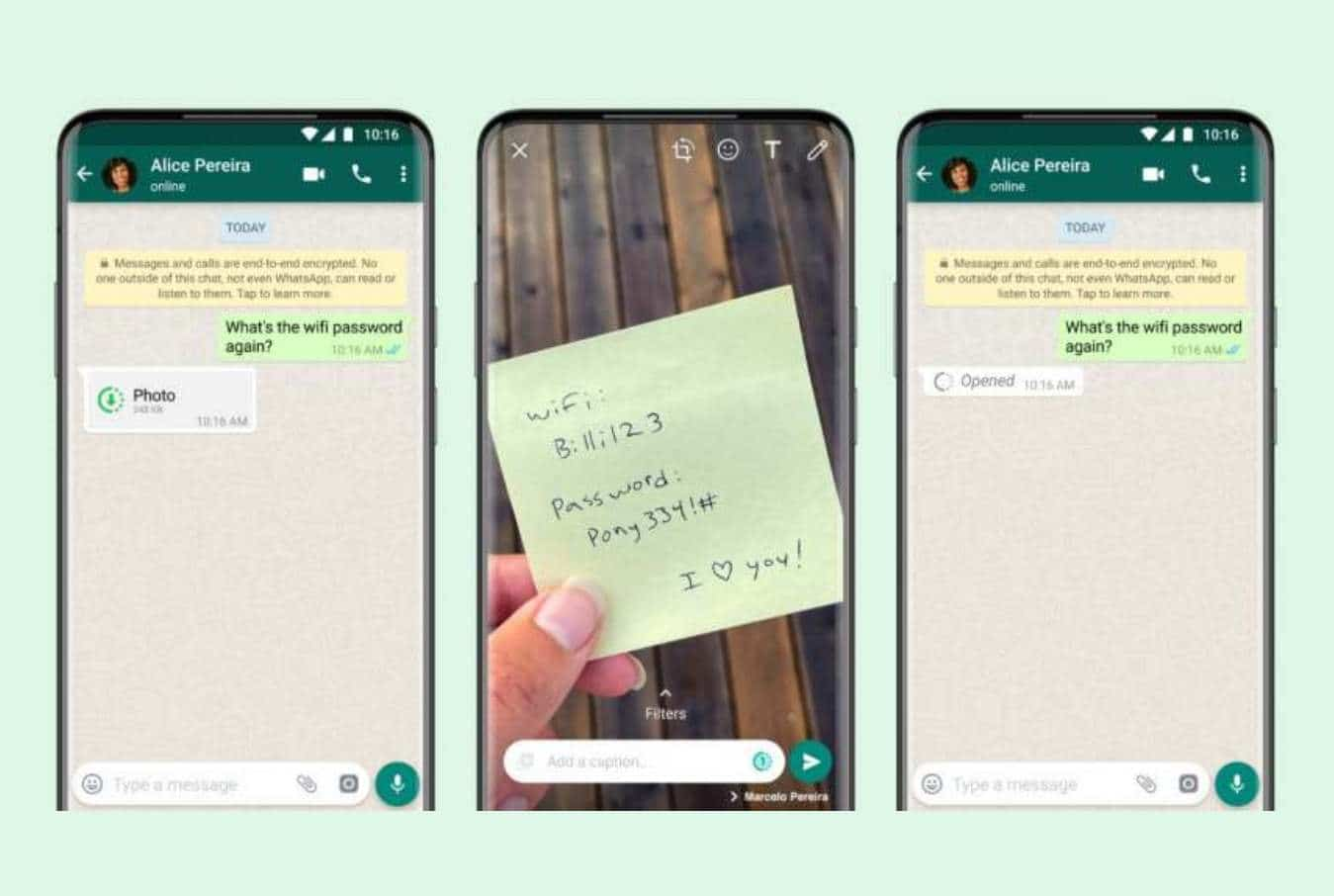
2.5KGeekWhatsApp Introduces View Once Feature for Videos and Photos
View Once feature will keep the images accessible for a maximum of 14 days and expire afterward. It’s quite amusing that Facebook...
-
 3.2KData Security
3.2KData SecurityIdentity Theft – 5 Ways to Secure Your Identity Online
More and more people are falling victim to identity theft today. This concept covers any kind of crime, scam, or form of...
-

 4.4KData Security
4.4KData SecurityBaby clothing giant Carter’s exposed trove of shoppers data
Reportedly, Carter’s failure to implement proper authentication protocols on the store’s parcel tracking pages exposed data and shoppers to scams. VpnMentor analysts...
-

 592How To
592How ToHow to automatically accept or disable browser cookies notice on any site
Tired of accepting or rejecting cookie notices on websites you visit? You can now use any of these 3 browser extensions to...
-
 3.6KData Security
3.6KData SecurityThroughTek Flaw Exposed Millions of IoT Cameras to Spying
The vulnerability exisits in the company’s P2P SDK, a function that allows a client on a desktop or mobile app to access...






