All posts tagged "cybersecurity"
-

 4.9KMalware
4.9KMalwareResearchers Link ShadowPad Malware Attacks to Chinese Ministry and PLA
Cybersecurity researchers have detailed the inner workings of ShadowPad, a sophisticated and modular backdoor that has been adopted by a growing number...
-

 1.4KMalware
1.4KMalwareExperts Warn of Hacking Group Targeting Aviation and Defense Sectors
Entities in the aviation, aerospace, transportation, manufacturing, and defense industries have been targeted by a persistent threat group since at least 2017...
-

 2.7KData Breach
2.7KData BreachHow Attack Surface Management Preempts Cyberattacks
The wide-ranging adoption of cloud facilities and the subsequent mushrooming of organizations’ networks, combined with the recent migration to remote work, had...
-

 2.6KCyber Attack
2.6KCyber AttackHackers Exploited 0-Day Vulnerability in Zimbra Email Platform to Spy on Users
A threat actor, likely Chinese in origin, is actively attempting to exploit a zero-day vulnerability in the Zimbra open-source email platform as...
-

 2.6KVulnerabilities
2.6KVulnerabilitiesCritical Flaws Discovered in Cisco Small Business RV Series Routers
Cisco has patched multiple critical security vulnerabilities impacting its RV Series routers that could be weaponized to elevate privileges and execute arbitrary...
-
 4.9KMalware
4.9KMalwareNew SEO Poisoning Campaign Distributing Trojanized Versions of Popular Software
An ongoing search engine optimization (SEO) poisoning attack campaign has been observed abusing trust in legitimate software utilities to trick users into...
-
 3.5KData Breach
3.5KData BreachCynet’s Keys to Extend Threat Visibility
We hear about the need for better visibility in the cybersecurity space – detecting threats earlier and more accurately. We often hear...
-
 606Cyber Attack
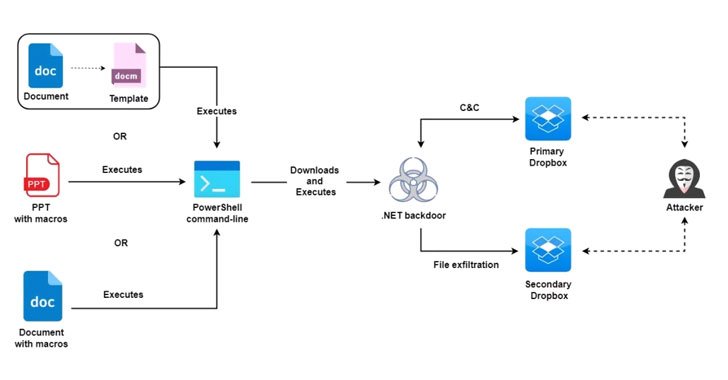
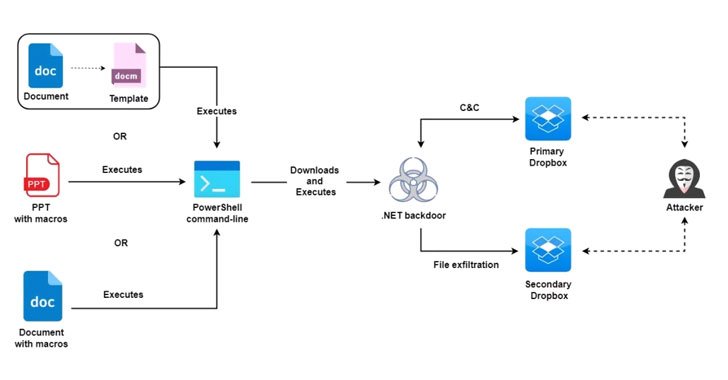
606Cyber AttackMolerats Hackers Hiding New Espionage Attacks Behind Public Cloud Infrastructure
An active espionage campaign has been attributed to the threat actor known as Molerats that abuses legitimate cloud services like Google Drive...
-

 4.6KMalware
4.6KMalwareGoogle Details Two Zero-Day Bugs Reported in Zoom Clients and MMR Servers
An exploration of zero-click attack surface for the popular video conferencing solution Zoom has yielded two previously undisclosed security vulnerabilities that could...
-
 3.1KCyber Attack
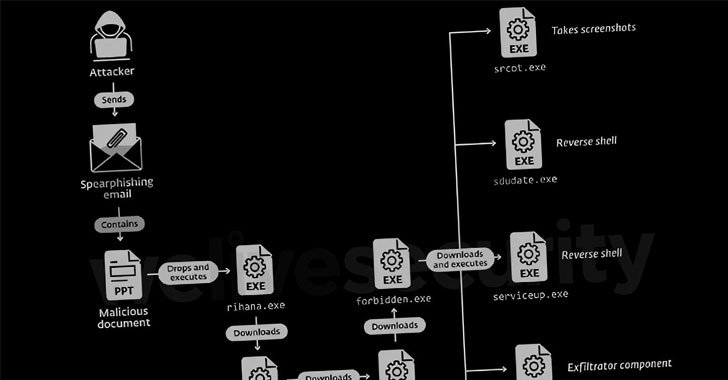
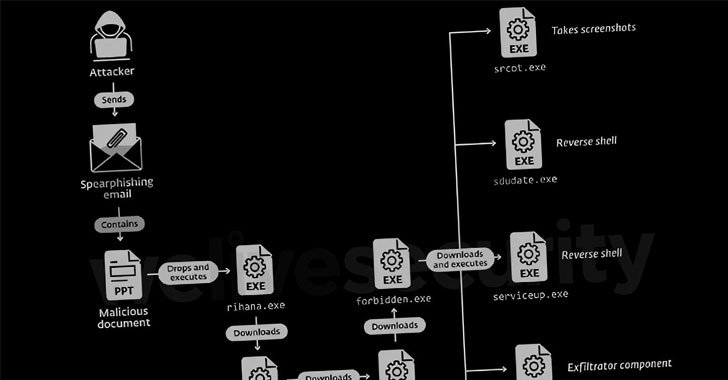
3.1KCyber AttackDoNot Hacking Team Targeting Government and Military Entities in South Asia
A threat actor with potential links to an Indian cybersecurity company has been nothing if remarkably persistent in its attacks against military...
-

 786Malware
786MalwareDDoS IRC Bot Malware Spreading Through Korean WebHard Platforms
An IRC (Internet Relay Chat) bot strain programmed in GoLang is being used to launch distributed denial-of-service (DDoS) attacks targeting users in...
-
 600Malware
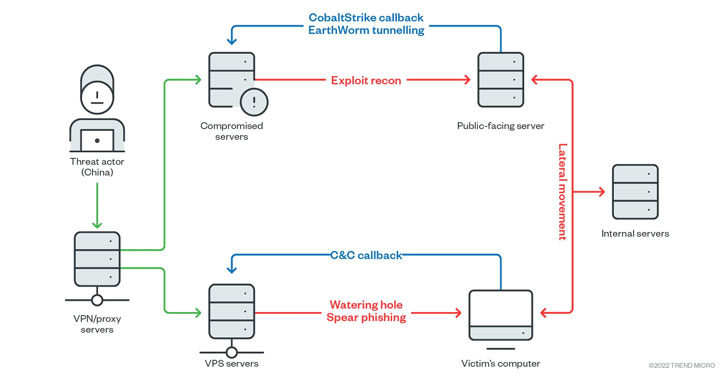
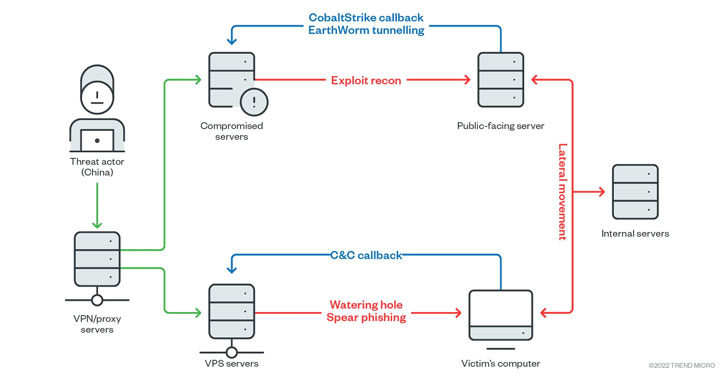
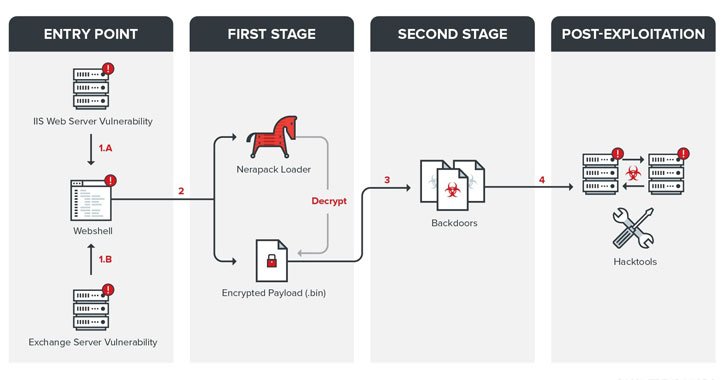
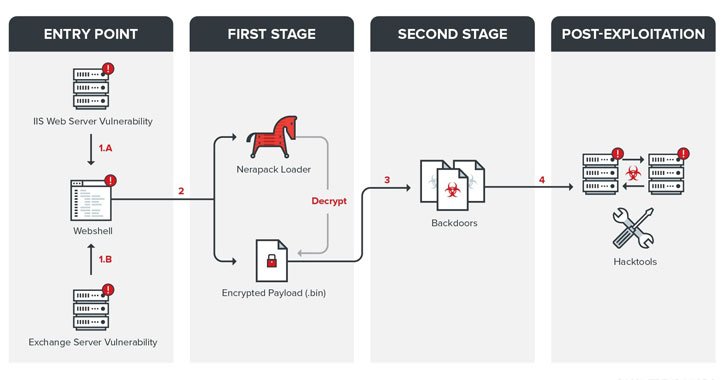
600MalwareEarth Lusca Hackers Aimed at High-Value Targets in Government and Private Sectors
An elusive threat actor called Earth Lusca has been observed striking organizations across the world as part of what appears to be...
-

 3.2KVulnerabilities
3.2KVulnerabilitiesApple Releases iPhone and iPad Updates to Patch HomeKit DoS Vulnerability
Apple on Wednesday rolled out software updates for iOS and iPadOS to remediate a persistent denial-of-service (DoS) issue affecting the HomeKit smart...
-

 5.2KMalware
5.2KMalwareNew Trick Could Let Malware Fake iPhone Shutdown to Spy on Users Secretly
Researchers have disclosed a novel technique by which malware on iOS can achieve persistence on an infected device by faking its shutdown...
-
 3.5KMalware
3.5KMalwareNew Zloader Banking Malware Campaign Exploiting Microsoft Signature Verification
An ongoing ZLoader malware campaign has been uncovered exploiting remote monitoring tools and a nine-year-old flaw concerning Microsoft’s digital signature verification to...
-
 1.3KMalware
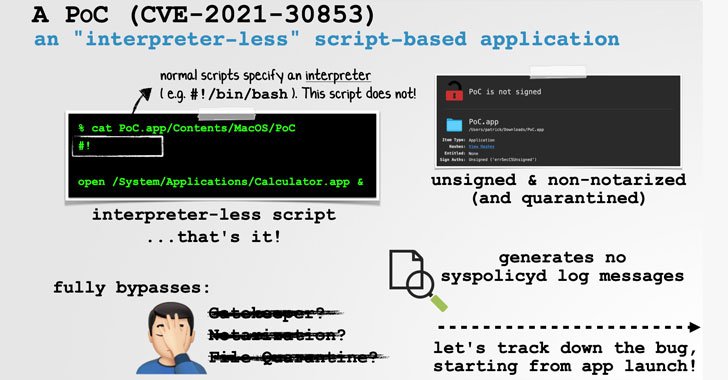
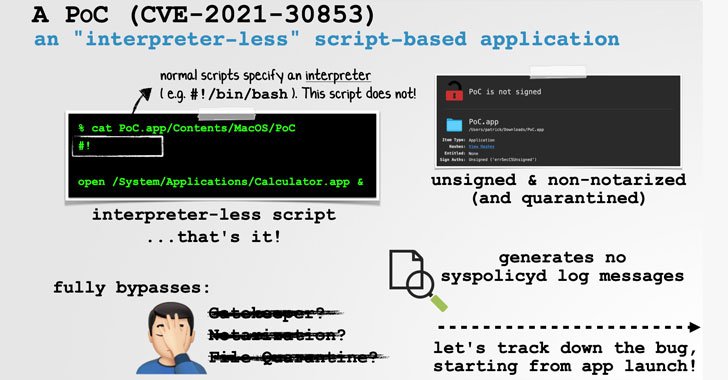
1.3KMalwareExpert Details macOS Bug That Could Let Malware Bypass Gatekeeper Security
Apple recently fixed a security vulnerability in the macOS operating system that could be potentially exploited by a threat actor to “trivially...
-

 4.5KVulnerabilities
4.5KVulnerabilitiesResearchers Disclose Unpatched Vulnerabilities in Microsoft Teams Software
Microsoft said it won’t be fixing or is pushing patches to a later date for three of the four security flaws uncovered...
-
 3.7KMalware
3.7KMalwareTropic Trooper Cyber Espionage Hackers Targeting Transportation Sector
Transportation industry and government agencies related to the sector are the victims of an ongoing campaign since July 2020 by a sophisticated...
-

 4.0KCyber Attack
4.0KCyber AttackCISA Compliance for 2022
The last several years have seen an ever-increasing number of cyber-attacks, and while the frequency of such attacks has increased, so too...
-

 4.2KCyber Attack
4.2KCyber AttackHow Extended Security Posture Management Optimizes Your Security Stack
As a CISO, one of the most challenging questions to answer is “How well are we protected right now?” Between the acceleration...
-

 1.8KMalware
1.8KMalwareOver 300,000 MikroTik Devices Found Vulnerable to Remote Hacking Bugs
At least 300,000 IP addresses associated with MikroTik devices have been found vulnerable to multiple remotely exploitable security vulnerabilities that have since...






