All posts tagged "cybersecurity"
-

 3.6KMalware
3.6KMalwareChinese Hackers Target Major Southeast Asian Telecom Companies
Three distinct clusters of malicious activities operating on behalf of Chinese state interests have staged a series of attacks to target networks...
-

 5.4KMalware
5.4KMalwarePhony Call Centers Tricking Users Into Installing Ransomware and Data-Stealers
An ongoing malicious campaign that employs phony call centers has been found to trick victims into downloading malware capable of data exfiltration...
-

 3.9KVulnerabilities
3.9KVulnerabilitiesTop 30 Critical Security Vulnerabilities Most Exploited by Hackers
Intelligence agencies in Australia, the U.K., and the U.S. issued a joint advisory on Wednesday detailing the most exploited vulnerabilities in 2020...
-

 1.3KMalware
1.3KMalwareThis New Malware Hides Itself Among Windows Defender Exclusions to Evade Detection
Cybersecurity researchers on Tuesday lifted the lid on a previously undocumented malware strain dubbed “MosaicLoader” that singles out individuals searching for cracked...
-
 2.8KMalware
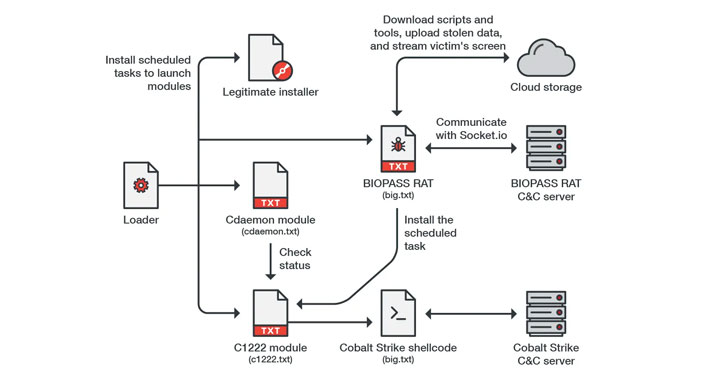
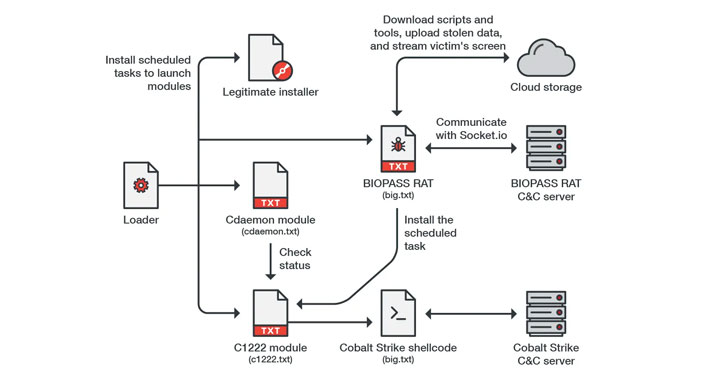
2.8KMalwareHackers Spread BIOPASS Malware via Chinese Online Gambling Sites
Cybersecurity researchers are warning about a new malware that’s striking online gambling companies in China via a watering hole attack to deploy...
-

 4.7KMalware
4.7KMalwareKaseya Rules Out Supply-Chain Attack; Says VSA 0-Day Hit Its Customers Directly
U.S. technology firm Kaseya, which is firefighting the largest ever supply-chain ransomware strike on its VSA on-premises product, ruled out the possibility...
-

 3.3KMalware
3.3KMalwareFIN7 Supervisor Gets 7-Year Jail Term for Stealing Millions of Credit Cards
A Ukrainian national and a mid-level supervisor of the hacking group known as FIN7 has been sentenced to seven years in prison...
-

 4.3KVulnerabilities
4.3KVulnerabilitiesCritical Auth Bypass Bug Affects VMware Carbon Black App Control
VMware has rolled out security updates to resolve a critical flaw affecting Carbon Black App Control that could be exploited to bypass...
-

 893Cyber Attack
893Cyber AttackNorth Korea Exploited VPN Flaw to Hack South’s Nuclear Research Institute
South Korea’s state-run Korea Atomic Energy Research Institute (KAERI) on Friday disclosed that its internal network was infiltrated by suspected attackers operating...
-

 3.0KMalware
3.0KMalware[eBook] 7 Signs You Might Need a New Detection and Response Tool
It’s natural to get complacent with the status quo when things seem to be working. The familiar is comfortable, and even if...
-

 2.1KMalware
2.1KMalwareMolerats Hackers Return With New Attacks Targeting Middle Eastern Governments
A Middle Eastern advanced persistent threat (APT) group has resurfaced after a two-month hiatus to target government institutions in the Middle East...
-
 4.5KMalware
4.5KMalwareLive Cybersecurity Webinar — Deconstructing Cobalt Strike
Organizations’ cybersecurity capabilities have improved over the past decade, mostly out of necessity. As their defenses get better, so do the methods,...
-

 3.5KMalware
3.5KMalwareNew Cyber Espionage Group Targeting Ministries of Foreign Affairs
Cybersecurity researchers on Thursday took the wraps off a new cyberespionage group that has been behind a series of targeted attacks against...
-
 2.7KData Breach
2.7KData BreachUsing Breached Password Detection Services to Prevent Cyberattack
Bolstering password policies in your organization is an important part of a robust cybersecurity strategy. Cybercriminals are using compromised accounts as one...
-

 3.3KMalware
3.3KMalwareCrypto-Mining Attacks Targeting Kubernetes Clusters via Kubeflow Instances
Cybersecurity researchers on Tuesday disclosed a new large-scale campaign targeting Kubeflow deployments to run malicious cryptocurrency mining containers. The campaign involved deploying...
-

 2.0KMalware
2.0KMalwareEBook – Creating a Large Company Security Stack on a Lean Company Budget
The speed at which malicious actors have improved their attack tactics and continue to penetrate security systems has made going bigger the...
-
 4.5KMalware
4.5KMalwareFeds Secretly Ran a Fake Encrypted Chat App and Busted Over 800 Criminals
In an unprecedented sting operation, the U.S. Federal Bureau of Investigation (FBI) and Australian Federal Police (AFP) ran an encrypted chat service...
-

 2.3KMalware
2.3KMalwareLatvian Woman Charged for Her Role in Creating Trickbot Banking Malware
The U.S. Department of Justice (DoJ) on Friday charged a Latvian woman for her alleged role as a programmer in a cybercrime...
-

 1.2KMalware
1.2KMalwareGitHub Updates Policy to Remove Exploit Code When Used in Active Attacks
Code-hosting platform GitHub Friday officially announced a series of updates to the site’s policies that delve into how the company deals with...
-

 4.4KMalware
4.4KMalwareALERT: Critical RCE Bug in VMware vCenter Server Under Active Attack
Malicious actors are actively mass scanning the internet for vulnerable VMware vCenter servers that are unpatched against a critical remote code execution...
-

 4.0KMalware
4.0KMalwareGoogle Chrome to Help Users Identify Untrusted Extensions Before Installation
Google on Thursday said it’s rolling out new security features to Chrome browser aimed at detecting suspicious downloads and extensions via its...






