All posts tagged "cybersecurity"
-

 504Cyber Crime
504Cyber CrimeHow to Ensure Data-Centric Cybersecurity?
In the current cybersecurity landscape, the threats facing enterprises have evolved; and now highlight a growing level of sophistication in the methods...
-
 1.4KHack Tools
1.4KHack ToolsExploitivator – Automate Metasploit Scanning And Exploitation
This has only been tested on Kali.It depends on the msfrpc module for Python, described in detail here: https://www.trustwave.com/Resources/SpiderLabs-Blog/Scripting-Metasploit-using-MSGRPC/Install the necessary Kali...
-

 3.6KHack Tools
3.6KHack ToolsRTTM – Real Time Threat Monitoring Tool
Monitoring possible threats of your company on Internet is an impossible task to be achieved manually. Hence many threats of the company...
-

 1.4KHack Tools
1.4KHack ToolsHashCobra – Hash Cracking Tool
hashcobra Hash Cracking tool. Usage $ ./hashcobra -H--==[ hashcobra by sepehrdad ]==--usage: hashcobra -o <opr> [options] | [misc]options: -a <alg> - hashing...
-
 2.5KHack Tools
2.5KHack ToolsSplunk Attack Range – A Tool That Allows You To Create Vulnerable Instrumented Local Or Cloud Environments To Simulate Attacks Against And Collect The Data Into Splunk
The Attack Range solves two main challenges in development of detections. First, it allows the user to quickly build a small lab...
-
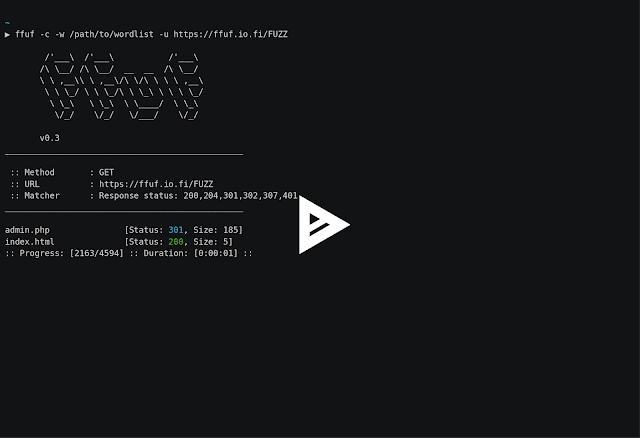
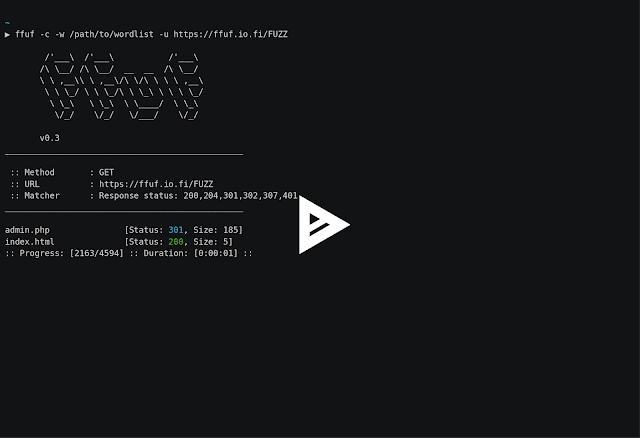 4.9KHack Tools
4.9KHack ToolsFfuf – Fast Web Fuzzer Written In Go
A fast web fuzzer written in Go.Heavily inspired by the great projects gobuster and wfuzz. Features Fast! Allows fuzzing of HTTP header...
-

 1.9KIncidents
1.9KIncidents20 years in prison for sending malware emails and infecting computers
According to ethical hacking specialists, two Romanian citizens have been sentenced to 20 years in prison for infecting more than 400,000 computer...
-

 799Hack Tools
799Hack ToolsFileintel – A Modular Python Application To Pull Intelligence About Malicious Files
This is a tool used to collect various intelligence sources for a given file. Fileintel is written in a modular fashion so...
-

 4.1KMalware
4.1KMalwareA bug in the Ryuk ransomware makes data recovery impossible even if the ransom is paid. Who will fix this flaw?
Hundreds of things could go wrong after a ransomware victim pays the money demanded by criminals. Digital forensics specialists from security firm...
-
 3.3KHack Tools
3.3KHack ToolsGenact – A Nonsense Activity Generator
Pretend to be busy or waiting for your computer when you should actually be doing real work! Impress people with your insane...
-

 2.1KIncidents
2.1KIncidentsBMW was hacked; potential trading secrets leaking
Currently any company can become a victim of a cyberattack. According to cybersecurity specialists, automobile company BMW detected and monitored a hacker...
-
 3.9KHack Tools
3.9KHack ToolsReconPi – Set Up Your Raspberry Pi To Perform Basic Recon Scans
ReconPi – A lightweight recon tool that performs extensive reconnaissance with the latest tools using a Raspberry Pi.Start using that Raspberry Pi...
-
 756Hack Tools
756Hack ToolsCAINE 11 – GNU/Linux Live Distribution For Digital Forensics Project, Windows Side Forensics And Incident Response
CAINE (Computer Aided INvestigative Environment) is an Italian GNU/Linux live distribution created as a Digital Forensics project. Currently, the project manager is Nanni Bassetti...
-
 4.3KHack Tools
4.3KHack ToolsNgrev – Tool For Reverse Engineering Of Angular Applications
Graphical tool for reverse engineering of Angular projects. It allows you to navigate in the structure of your application and observe the...
-
 4.8KHack Tools
4.8KHack ToolsFunctrace – A Function Tracer
functrace is a tool that helps to analyze a binary file with dynamic instrumentation using DynamoRIO (http://dynamorio.org/).These are some implemented features (based...
-

 3.7KHack Tools
3.7KHack ToolsApk-Mitm – A CLI Application That Prepares Android APK Files For HTTPS Inspection
A CLI application that automatically prepares Android APK files for HTTPS inspection Inspecting a mobile app’s HTTPS traffic using a proxy is...
-
 4.5KHack Tools
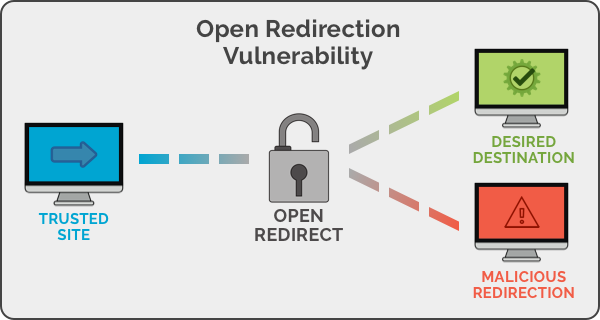
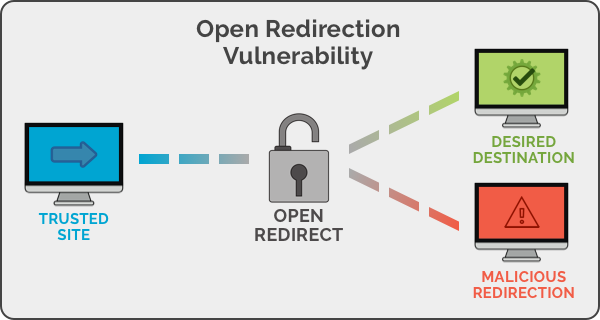
4.5KHack ToolsOpen Redirect Payload List
Unvalidated redirects and forwards are possible when a web application accepts untrusted input that could cause the web application to redirect the...
-

 1.7KHack Tools
1.7KHack ToolsAntiDisposmail – Detecting Disposable Email Addresses
Antbot.pw provides a free, open API endpoint for checking a domain or email address against a frequently-updated list of disposable domains. CORS...
-

 4.2KMalware
4.2KMalwareNew fileless malware for MAC is undetectable
A new report revealed by digital forensics specialists claims that hackers that make up the dangerous Lazarus group are trying to inject...
-

 2.4KVulnerabilities
2.4KVulnerabilitiesHow to hijack VPN tunnel session on Linux, FreeBSD, OpenBSD, MacOS, iOS and Android
A group of vulnerability testing specialists from the University of New Mexico, made up of William J. Tolley, Beau Kujath and Jedidiah...
-
 2.4KHack Tools
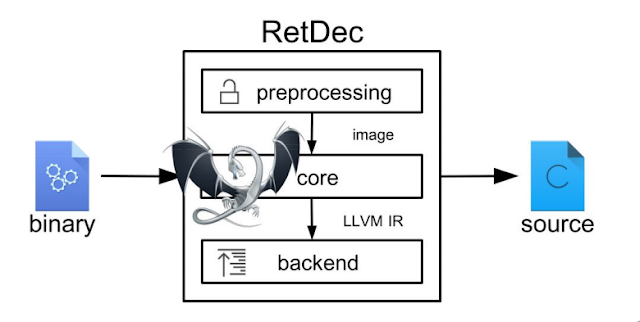
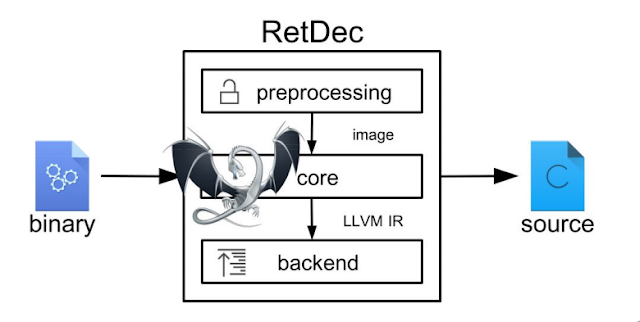
2.4KHack ToolsRetDec – A Retargetable Machine-Code Decompiler Based On LLVM
RetDec is a retargetable machine-code decompiler based on LLVM.The decompiler is not limited to any particular target architecture, operating system, or executable...






