All posts tagged "cybersecurity"
-
 2.3KHack Tools
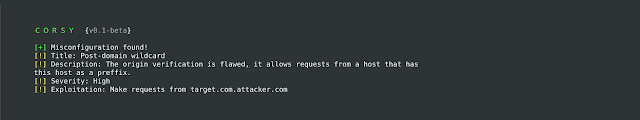
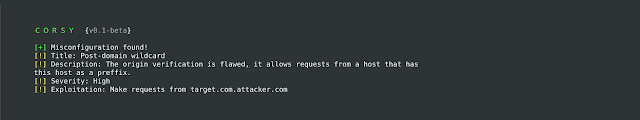
2.3KHack ToolsCorsy – CORS Misconfiguration Scanner
Corsy is a lightweight program that scans for all known misconfigurations in CORS implementations. UsageUsing Corsy is pretty simplepython corsy.py -u https://example.comA...
-
 4.6KHack Tools
4.6KHack ToolsFlan – A Pretty Sweet Vulnerability Scanner By CloudFlare
Flan Scan is a lightweight network vulnerability scanner. With Flan Scan you can easily find open ports on your network, identify services...
-

 2.5KIncidents
2.5KIncidentsNYPD loses fingerprint database due to malware infection
According to digital forensics specialists, a company that provides IT services to the New York Police Department (NYPD) accidentally disconnected the database...
-

 3.2KVulnerabilities
3.2KVulnerabilities37 critical vulnerabilities found in VNC solutions. Patches now available
These are bad news for software programmers worldwide. Vulnerability testing researchers report the finding of 37 security flaws affecting four major implementations...
-

 2.8KIncidents
2.8KIncidentsHackers leak personal information from OnePlus customers
Currently any company is exposed to computer security incidents. This time, web application security experts report that OnePlus, a smartphone manufacturer based...
-

 1.0KIncidents
1.0KIncidentsMore than a billion personal records leaked. The biggest data breach in history
Data breaches have become routine, although each new reported incident seems to more seriously affect a larger number of users. Data protection...
-
 1.2KHack Tools
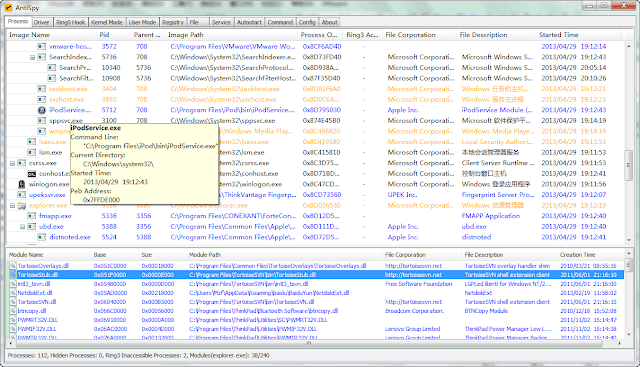
1.2KHack ToolsAntispy – A Free But Powerful Anti Virus And Rootkits Toolkit
AntiSpy is a free but powerful anti virus and rootkits toolkit.It offers you the ability with the highest privileges that can detect,analyze...
-

 2.2KHack Tools
2.2KHack ToolsRE:TERNAL – Repo Containing Docker-Compose Files And Setup Scripts Without Having To Clone The Individual Reternal Components
RE:TERNAL is a centralised purple team simulation platform. Reternal uses agents installed on a simulation network to execute various known red-teaming techniques...
-
 1.8KHack Tools
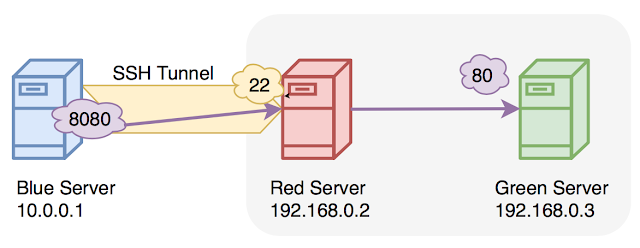
1.8KHack ToolsSshtunnel – SSH Tunnels To Remote Server
Inspired by https://github.com/jmagnusson/bgtunnel, which doesn’t work on Windows.See also: https://github.com/paramiko/paramiko/blob/master/demos/forward.py Requirements paramiko Installationsshtunnel is on PyPI, so simply run: pip install sshtunnel...
-
 1.0KHack Tools
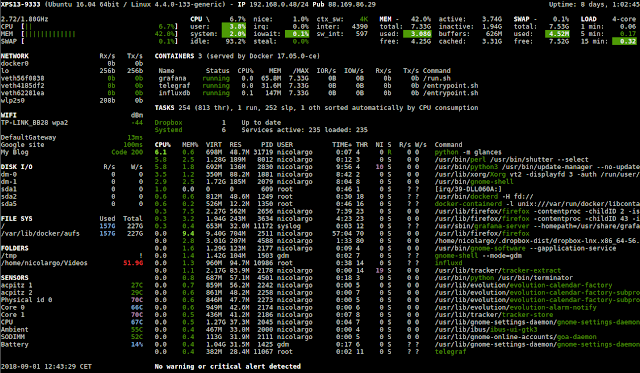
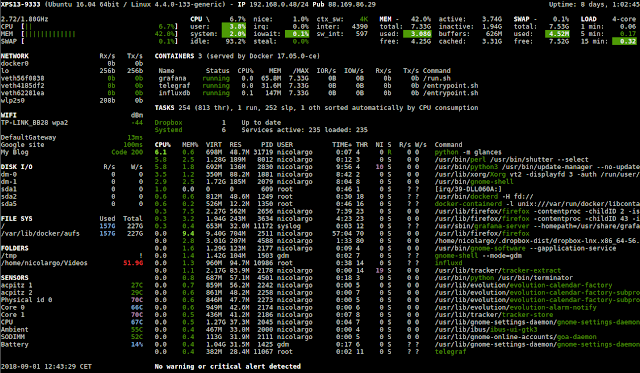
1.0KHack ToolsGlances – An Eye On Your System. A Top/Htop Alternative For GNU/Linux, BSD, Mac OS And Windows Operating Systems
Glances is a cross-platform monitoring tool which aims to present a large amount of monitoring information through a curses or Web based...
-
 1.8KHack Tools
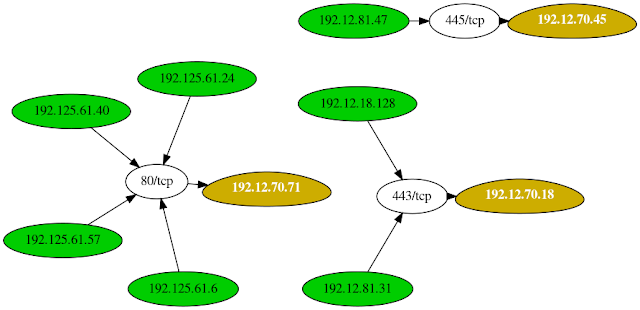
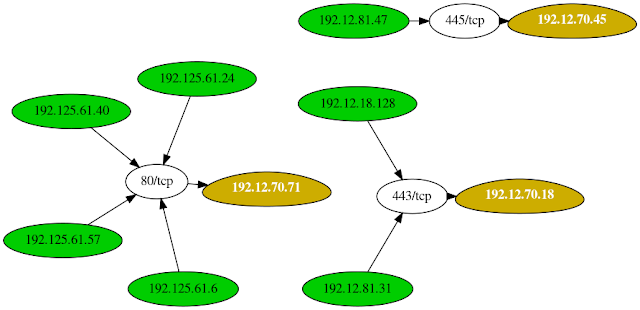
1.8KHack ToolsLeprechaun – Tool Used To Map Out The Network Data Flow To Help Penetration Testers Identify Potentially Valuable Targets
The purpose of this tool is to help penetration testers identify potentially valuable targets on the internal network environment. By aggregating netstat...
-
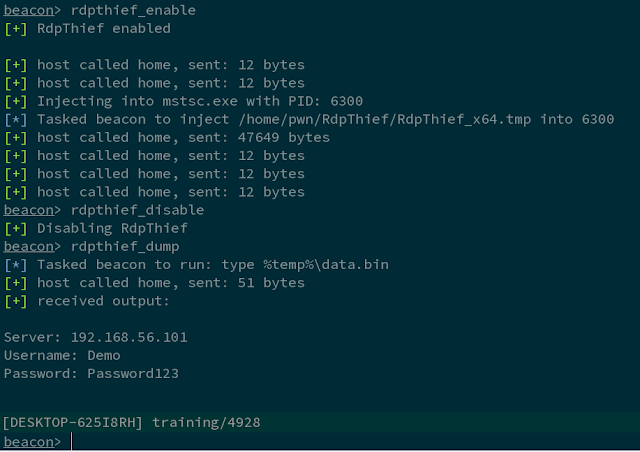
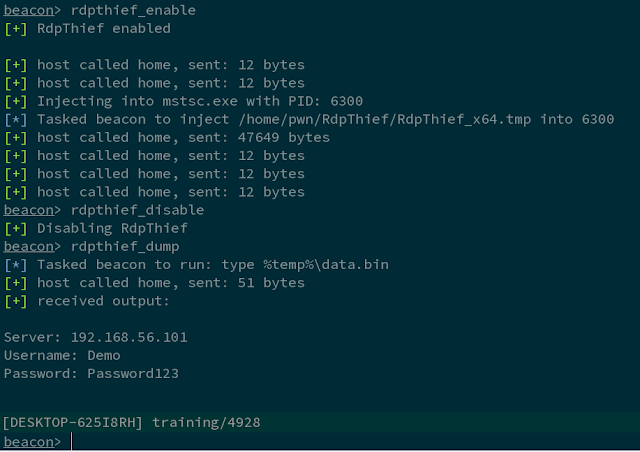 453Hack Tools
453Hack ToolsRdpThief – Extracting Clear Text Passwords From Mstsc.Exe Using API Hooking
RdpThief by itself is a standalone DLL that when injected in the mstsc.exe process, will perform API hooking, extract the clear-text credentials...
-

 3.3KVulnerabilities
3.3KVulnerabilitiesCritical vulnerability in Jetpack plugin affects millions of WordPress websites
Again, new reports of security flaws that could affect the millions of WordPress users, the most popular content management system (CMS), have...
-
 3.8KHack Tools
3.8KHack ToolsDNCI – Dot Net Code Injector
DNCI allows the injection of .Net code (.exe or .dll) remotely in unmanaged processes in windows. 1. Project StructureThe project is structured...
-
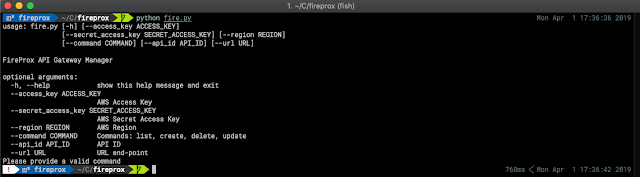
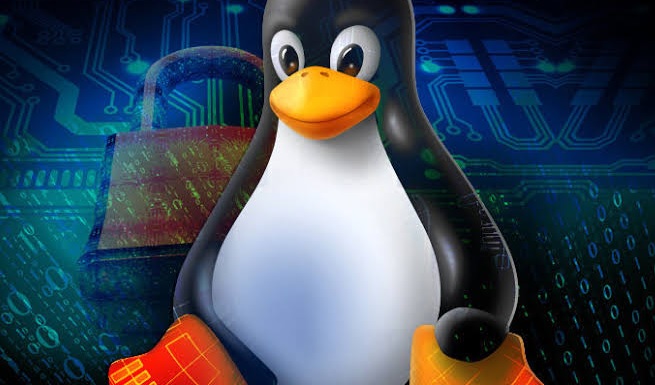
 5.0KHack Tools
5.0KHack ToolsFireProx – AWS API Gateway Management Tool For Creating On The Fly HTTP Pass-Through Proxies For Unique IP Rotation
Being able to hide or continually rotate the source IP address when making web calls can be difficult or expensive. A number...
-

 5.2KIncidents
5.2KIncidentsAccor Hotels suffers from data breach; users’ personal information gets leaked
Information security specialists from firm vpnMentor, led by expert Noam Rotem, discovered a data breach that affected Gekko Group, a subsidiary brand...
-

 4.6KData Security
4.6KData SecurityRobin Hood-like hacker breaks into Cayman Islands banks and shows how to hack a bank easily
A report recently published by Unicorn Riot, an independent digital media collective, has revealed a hacking operation against a major money laundering...
-
 4.8KVulnerabilities
4.8KVulnerabilitiesUpdate your Linux servers with Webmin, critical vulnerability detected
Network security researchers from Netlab firm have just released a report that mentions that Linux servers running no patched Webmin installations are...
-
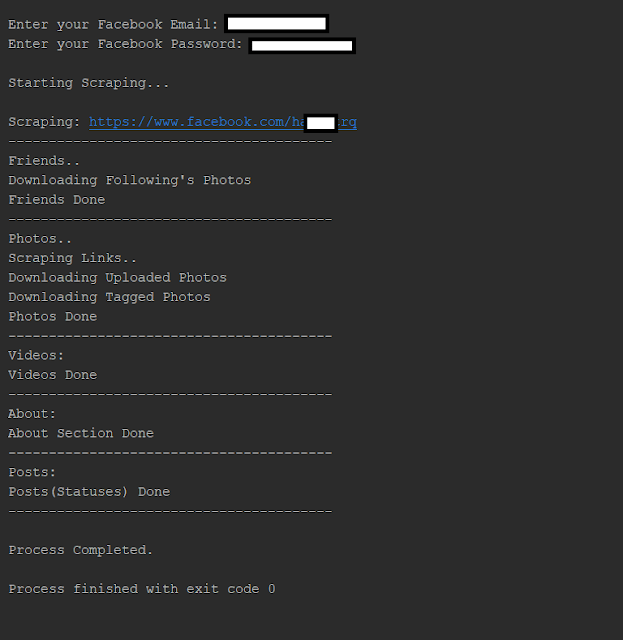
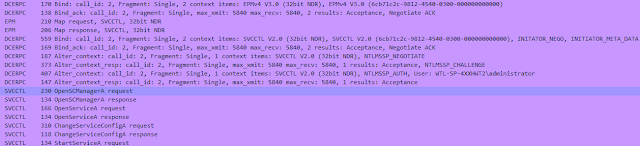
 3.0KHack Tools
3.0KHack ToolsUltimate Facebook Scraper – A Bot Which Scrapes Almost Everything About A Facebook User’S Profile Including All Public Posts/Statuses Available On The User’S Timeline, Uploaded Photos, Tagged Photos, Videos, Friends List And Their Profile Photos
Tooling that automates your social media interactions to collect posts, photos, videos, friends, followers and much more on Facebook. FeaturesA bot which...
-
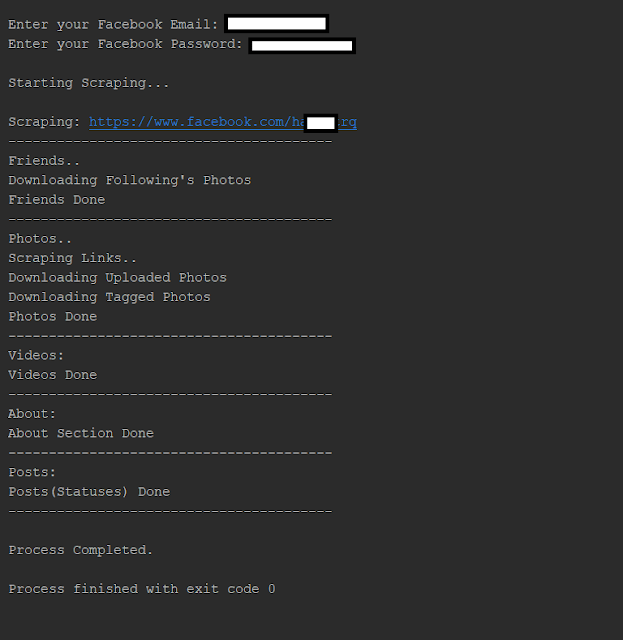
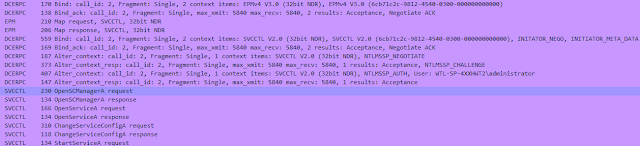 2.9KHack Tools
2.9KHack ToolsSCShell – Fileless Lateral Movement Tool That Relies On ChangeServiceConfigA To Run Command
Fileless lateral movement tool that relies on ChangeServiceConfigA to run command. The beauty of this tool is that it doesn’t perform authentication...
-

 3.2KVulnerabilities
3.2KVulnerabilitiesCritical vulnerability in Oracle grants provides full access to hackers. Update as soon as possible
A research published by vulnerability testing experts at security firm Onapsis claims that multiple vulnerabilities have been discovered in Oracle’s E-Business Suite....






