All posts tagged "cybersecurity"
-

 4.4KVulnerabilities
4.4KVulnerabilitiesCisco VoIP Telephony has 19 vulnerabilities. Update as soon as possible
Information security specialists at IT secure firm Tenable Research report the discovery of 19 vulnerabilities in Cisco SPA100 Series Voice over Internet...
-

 2.1KIncidents
2.1KIncidentsIs it secure to use Monero? Cryptocurrency website and wallet are hacked
Digital forensics specialists report that the official website of Monero, one of the most popular cryptocurrencies, was compromised due to the presence...
-

 938Data Security
938Data SecurityDownload free Jigsaw ransomware decryption tool
These are excellent news for ransomware victims. Specialists in ethical hacking of security firm Emsisoft have just announced the launch of a...
-

 1.2KIncidents
1.2KIncidentsMacy’s customers credit card data gets leaked. Why do companies keep making the same mistakes?
According to web application security specialists, Macy’s department store has been affected by a data breach that has compromised financial details of...
-
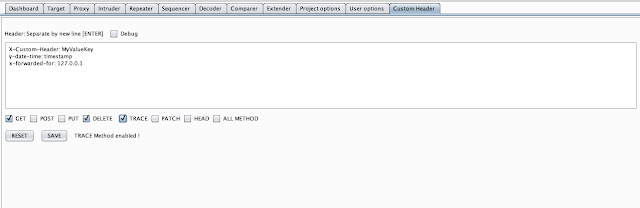
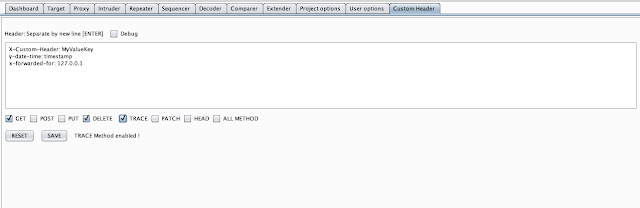 4.2KHack Tools
4.2KHack ToolsCustom Header – Automatic Add New Header To Entire BurpSuite HTTP Requests
This Burp Suite extension allows you to customize header with put a new header into HTTP REQUEST BurpSuite (Scanner, Intruder, Repeater, Proxy...
-

 4.5KHack Tools
4.5KHack ToolsDdoor – Cross Platform Backdoor Using Dns Txt Records
Cross-platform backdoor using dns txt records. What is ddor?ddor is a cross platform light weight backdoor that uses txt records to execute...
-

 631Vulnerabilities
631VulnerabilitiesOver 100 zero-day vulnerabilities discovered in ICS components from Bosch, Siemens, Schneider, BACnet, Nortek and more
According to digital forensics specialists at security firm Applied Risk there are more than 100 vulnerabilities in multiple building management systems (BMS)...
-
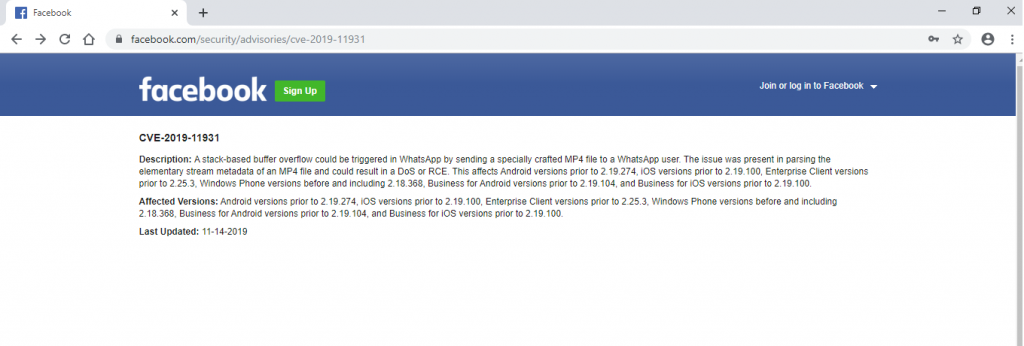
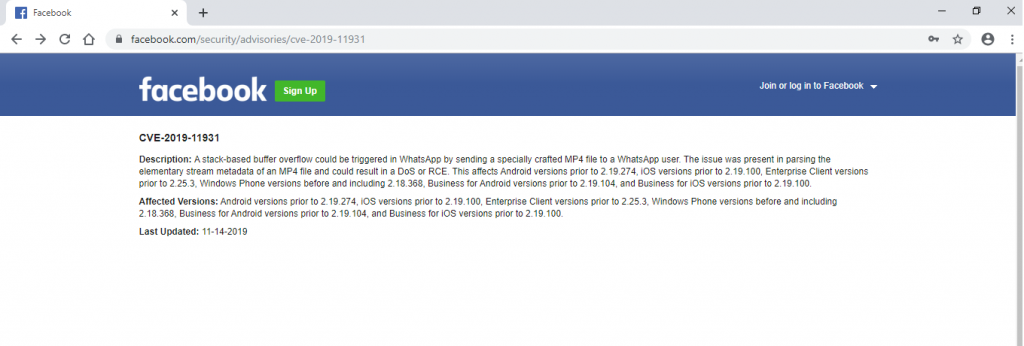 2.8KVulnerabilities
2.8KVulnerabilitiesDownloading a video file though WhatsApp could allow your smartphone to be hacked
Again, WhatsApp has become the target of malicious hacker attacks. According to web application security specialists, a critical vulnerability has been revealed...
-
 1.6KHack Tools
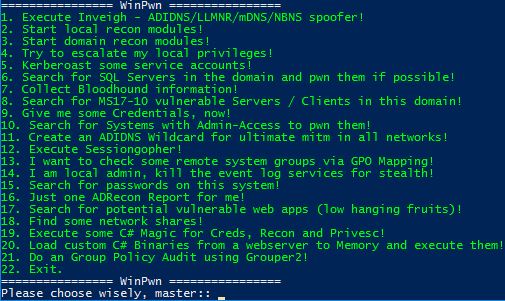
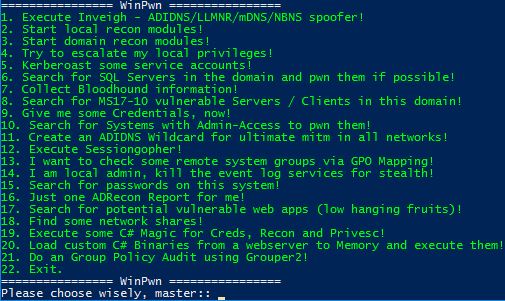
1.6KHack ToolsWinPwn – Automation For Internal Windows Penetrationtest / AD-Security
In many past internal penetration tests I often had problems with the existing Powershell Recon / Exploitation scripts due to missing proxy...
-
 2.2KHack Tools
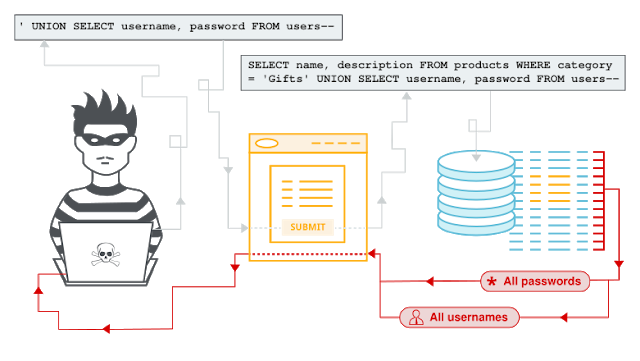
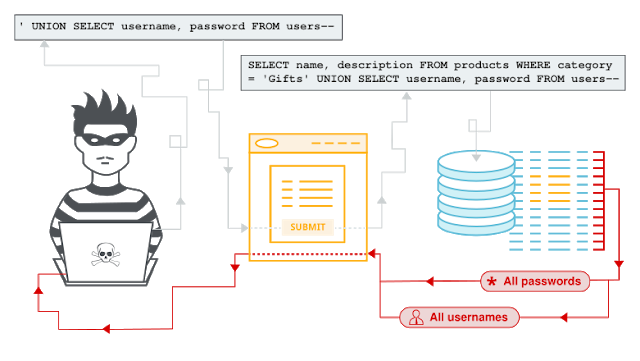
2.2KHack ToolsSQL Injection Payload List
SQL InjectionIn this section, we’ll explain what SQL injection is, describe some common examples, explain how to find and exploit various kinds...
-
 709Hack Tools
709Hack ToolsAndor – Blind SQL Injection Tool With Golang
Blind SQL Injection Tool with Golang.UsageDownload andor.go and go to the folder where the file andor.go located. And type this to command...
-

 1.4KHack Tools
1.4KHack ToolsDetectionLab – Vagrant And Packer Scripts To Build A Lab Environment Complete With Security Tooling And Logging Best Practices
DetectionLab is tested weekly on Saturdays via a scheduled CircleCI workflow to ensure that builds are passing. PurposeThis lab has been designed...
-

 1.4KRansomware
1.4KRansomwareGet Ransomware Protection For The Holidays: Reason Cybersecurity at 70% Off
Ransomware attacks are still something to be wary of these days. 2019 saw a resurgence in ransomware attacks and they’re expected to...
-

 4.5KHack Tools
4.5KHack ToolsRedPeanut – A Small RAT Developed In .Net Core 2 And Its Agent In .Net 3.5/4.0
[*] RedPeanut is a small RAT developed in .Net Core 2 and its agent in .Net 3.5 / 4.0. RedPeanut code execution...
-

 3.9KHack Tools
3.9KHack ToolsSeeker v1.1.9 – Accurately Locate Smartphones Using Social Engineering
Concept behind Seeker is simple, just like we host phishing pages to get credentials why not host a fake page that requests...
-
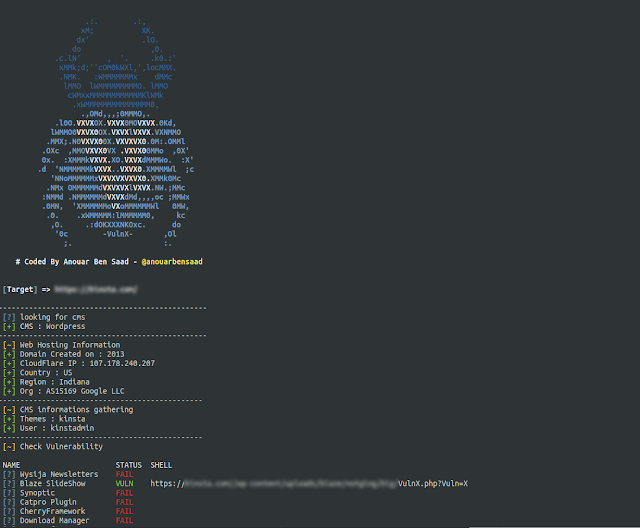
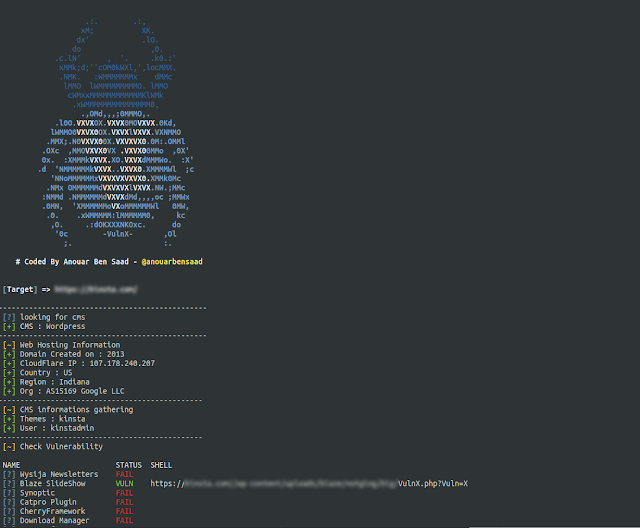 1.9KHack Tools
1.9KHack ToolsVulnx v1.9 – An Intelligent Bot Auto Shell Injector That Detect Vulnerabilities In Multiple Types Of CMS (WordPress, Joomla, Drupal, Prestashop…)
Vulnx is An Intelligent Bot Auto Shell Injector that detect vulnerabilities in multiple types of Cms, fast cms detection,informations gathering and vulnerabilitie...
-
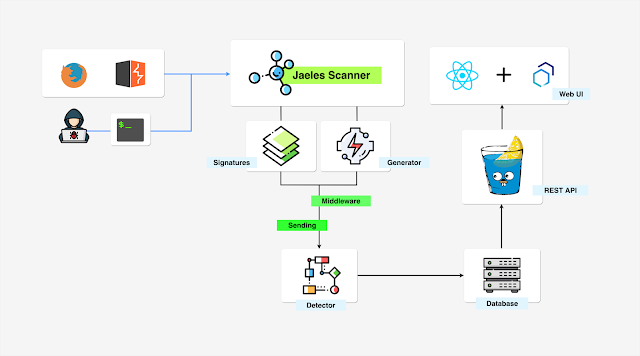
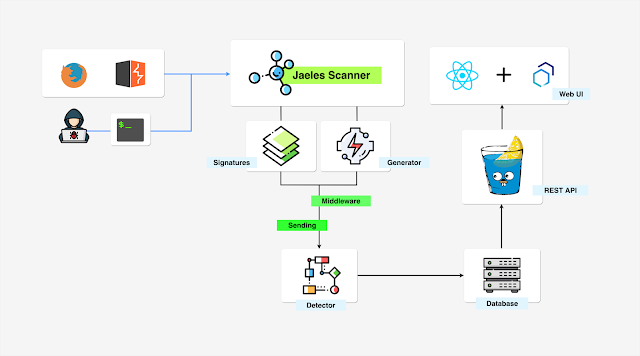 3.6KHack Tools
3.6KHack ToolsJaeles – The Swiss Army Knife For Automated Web Application Testing
Jaeles is a powerful, flexible and easily extensible framework written in Go for building your own Web Application Scanner.Installation go get -u...
-

 3.0KData Security
3.0KData SecurityData breaches affect more than 28 million Canadian citizens
According to data protection specialists, for one year now all Canadian companies have been subject to the Personal Information and Electronic Documents...
-

 4.0KIncidents
4.0KIncidentsOver 60,000 cybercriminals and hackers arrested
According to reports from ethical hacking specialists, Chinese authorities managed to resolve more than 45,000 cybercrime cases, as well as arresting more...
-

 4.3KHack Tools
4.3KHack ToolsRFI/LFI Payload List
As with many exploits, remote and local file inclusions are only a problem at the end of the encoding. Of course it...
-

 1.0KMalware
1.0KMalwareNever charge your Android or iOS smartphone in public places; new malware “juice-jacking”
A new threat has caught the attention of the cybersecurity community in Los Angeles, California. According to the district attorney office, some...






