All posts tagged "cybersecurity"
-

 1.9KIncidents
1.9KIncidentsCheck Point firewall ZoneAlarm suffers data breach incident
According to information security specialists, ZoneAlarm, the firewall software produced by security firm Check Point, was the victim of a data breach...
-
 3.9KHack Tools
3.9KHack ToolsEvil-Winrm v1.9 – The Ultimate WinRM Shell For Hacking/Pentesting
This shell is the ultimate WinRM shell for hacking/pentesting. WinRM (Windows Remote Management) is the Microsoft implementation of WS-Management Protocol. A standard...
-
 2.9KVulnerabilities
2.9KVulnerabilitiesHow to use headphones or Bluetooth to hack and take control of any Android device
A recent research published by vulnerability testing specialists from Purdue University details a new exploit that abuses some Android operating system smartphones...
-
 3.5KHack Tools
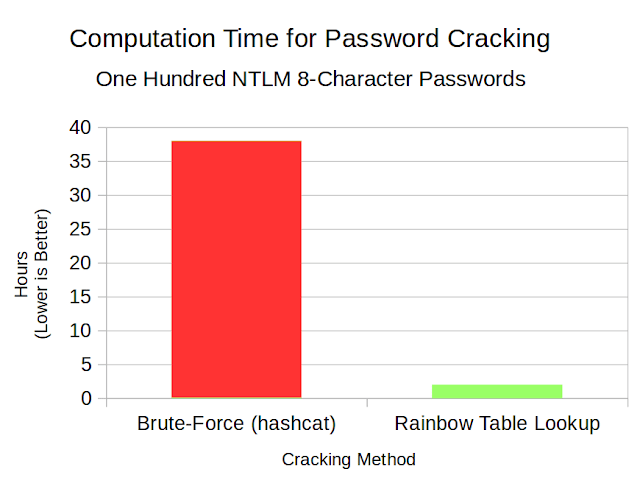
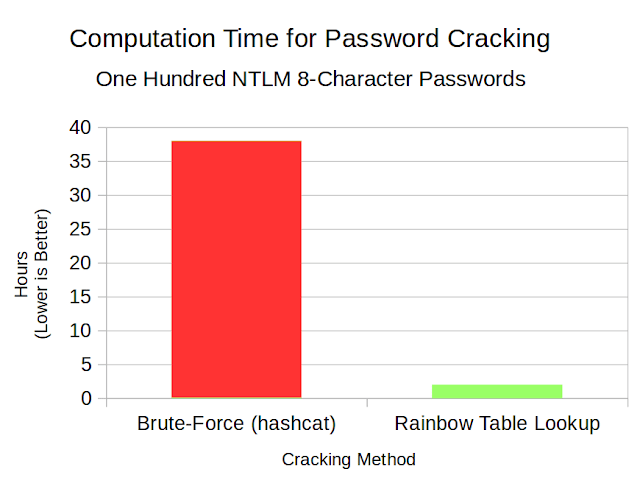
3.5KHack ToolsRainbow Crackalack – Rainbow Table Generation And Lookup Tools
This project produces open-source code to generate rainbow tables as well as use them to look up password hashes. While the current...
-

 5.4KHack Tools
5.4KHack ToolsBrave Browser – Next Generation Secure, Fast And Private Web Browser with Adblocker
The Brave Privacy Browser is your fast, safe private web browser with ad blocker, private tabs and pop-up blocker. Browse without being...
-
 2.8KHack Tools
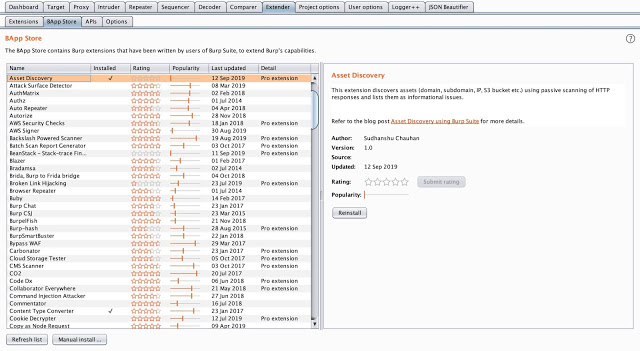
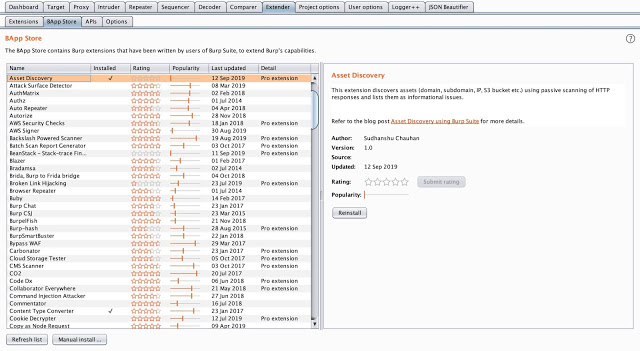
2.8KHack ToolsAsset Discover – Burp Suite Extension To Discover Assets From HTTP Response
Burp Suite extension to discover assets from HTTP response using passive scanning. Refer our blog Asset Discovery using Burp Suite for more...
-

 3.4KData Security
3.4KData SecurityISO 27701, the new cybersecurity and data privacy standard
According to data protection specialists, the International Organization for Standardization (ISO) and the International Electrotechnical Commission (IEC) launched a new set of...
-

 5.5KData Security
5.5KData Security2019 will be known as the year with the most cyberattacks in history
Information security experts anticipate that the balance in cybersecurity by the end of 2019 will be disastrous. According to figures collected up...
-

 3.0KIncidents
3.0KIncidentsWill PEMEX pay the $5M USD to hackers for the ransomware attack?
A couple of days ago web application security specialists reported a ransomware attack on Petroleos Mexicanos (PEMEX), a state-controlled Mexican oil company....
-

 4.8KMalware
4.8KMalwareRansomware as-a-service available 24X7; new Black Friday deal
Digital forensics specialists report the emergence of Buran, a new scheme for any user to acquire everything necessary to deploy a ransomware...
-
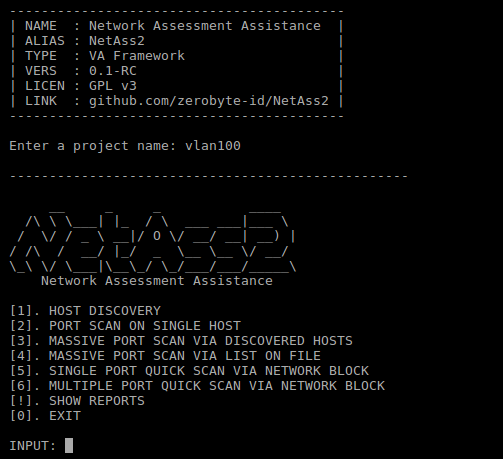
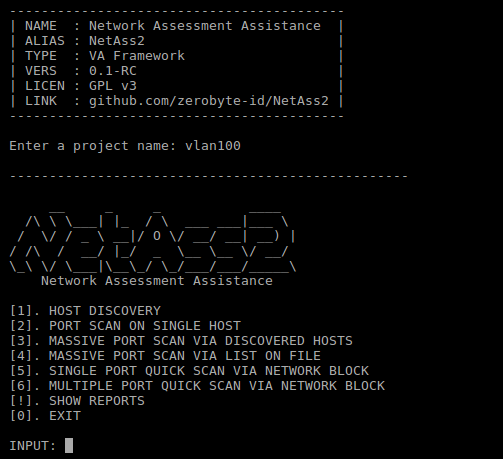 4.6KHack Tools
4.6KHack ToolsNetAss2 – Network Assessment Assistance Framework
Easier network scanning with NetAss2 (Network Assessment Assistance Framework). Make it easy for Pentester to do penetration testing on network. Dependencies nmap...
-

 3.2KHack Tools
3.2KHack ToolsRsdl – Subdomain Scan With Ping Method
Subdomain Scan With Ping Method. Flags Value Description –hostname example.com Domain for scan. –output Records the output with the domain name. –list...
-

 2.2KData Security
2.2KData SecurityCyber insurance shopper checklist: Things to consider before hiring these services
Information security related incidents have become so common that any organization, whether it is a major multinational company or a small business,...
-

 2.3KVulnerabilities
2.3KVulnerabilitiesTwo critical zero-day vulnerabilities found at thousands of ATMs
A team of digital forensics specialists has reported the finding of two major zero-day vulnerabilities in some ATM machines widely used in...
-
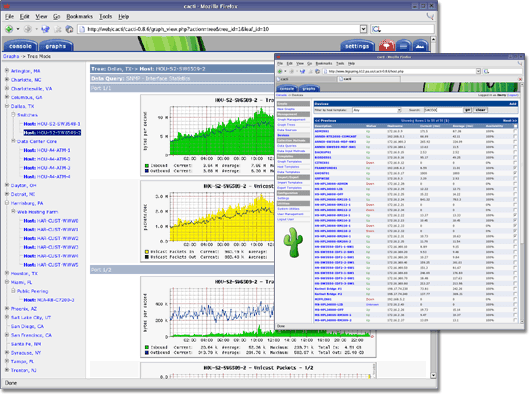
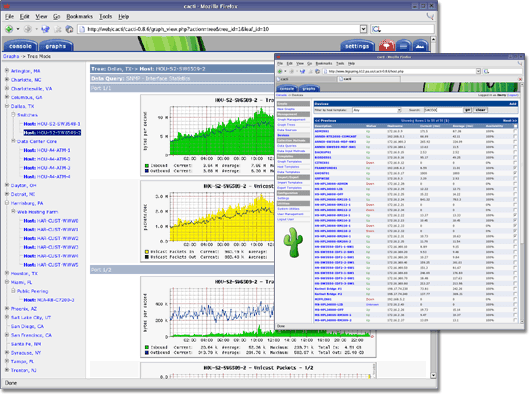 1.5KHack Tools
1.5KHack ToolsCacti – Complete Network Graphing Solution
IMPORTANTWhen using source or by downloading the code directly from the repository, it is important to run the database upgrade script if...
-
 2.0KMalware
2.0KMalwareA new and dangerous backdoor available on deep web
According to reports from digital forensics experts, the dangerous hacker group known as Platinum has announced the release of Titanium, a new...
-

 4.9KVulnerabilities
4.9KVulnerabilitiesCritical vulnerability affects Linux Ubuntu and FreeBSD systems
According to vulnerability testing specialists, a compression library included by default in multiple Linux distributions (Ubuntu, Debian, Gentoo, Arch Linux and FreeBSD...
-

 2.3KIncidents
2.3KIncidentsFortnite online servers worldwide under DDoS attack
Increasingly, cybersecurity incidents are affecting thousands, or even millions, of members of the gamer community. According to experts in ethical hacking, this...
-

 4.9KIncidents
4.9KIncidentsA major cloud services company suffers massive ransomware infection
The week is just beginning and new security incidents affecting major technology companies have already being reported. According to web application security...
-

 933Hack Tools
933Hack ToolsGCPBucketBrute – A Script To Enumerate Google Storage Buckets, Determine What Access You Have To Them, And Determine If They Can Be Privilege Escalated
A script to enumerate Google Storage buckets, determine what access you have to them, and determine if they can be privilege escalated....
-
 3.0KHack Tools
3.0KHack Toolsthreat_note – DPS’ Lightweight Investigation Notebook
threat_note is a web application built by Defense Point Security to allow security researchers the ability to add and retrieve indicators related...






