All posts tagged "cybersecurity"
-

 2.9KHack Tools
2.9KHack ToolsGoblin – An Impish, Cross-Platform Binary Parsing Crate, Written In Rust
Documentationhttps://docs.rs/goblin/changelog UsageGoblin requires rustc 1.31.1.Add to your Cargo.toml [dependencies]goblin = "0.1" Features awesome crate name zero-copy, cross-platform, endian-aware, ELF64/32 implementation – wow!...
-

 2.3KHack Tools
2.3KHack ToolsCCAT – Cloud Container Attack Tool For Testing Security Of Container Environments
Cloud Container Attack Tool (CCAT) is a tool for testing security of container environments. Quick reference Where to get help: the Pacu/CloudGoat/CCAT...
-
 1.3KHack Tools
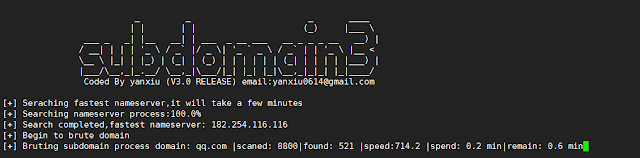
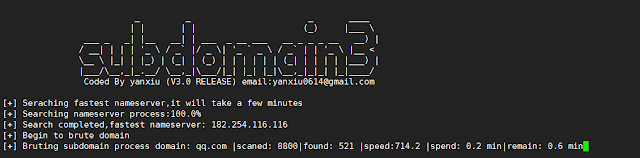
1.3KHack ToolsSubdomain3 – A New Generation Of Tool For Discovering Subdomains
Subdomain3 is a new generation of tool , It helps penetration testers to discover more information in a shorter time than other...
-

 4.1KHack Tools
4.1KHack ToolsMordor – Re-play Adversarial Techniques
The Mordor project provides pre-recorded security events generated by simulated adversarial techniques in the form of JavaScript Object Notation (JSON) files for...
-
 5.4KHack Tools
5.4KHack ToolsAttack Monitor – Endpoint Detection And Malware Analysis Software
Attack Monitor is Python application written to enhance security monitoring capabilites of Windows 7/2008 (and all later versions) workstations/servers and to automate...
-

 4.1KIncidents
4.1KIncidents4 million credit cards used in restaurants for sale in hacking forums
A hacker group has released a new database of stolen payment cards on Joker’s Stash, a popular hacking forum. According to web...
-

 1.5KMalware
1.5KMalwareNew malware transfers money from your mobile banking app to a hackers’ account
There are currently multiple variants of malware for mobile devices used for different purposes. Digital forensics experts mention that, during the most...
-

 4.3KHack Tools
4.3KHack ToolsBaseQuery – A Way To Organize Public Combo-Lists And Leaks In A Way That You Can Easily Search Through Everything
Your private data is being traded and sold all over the internet as we speak. Tons of leaks come out on a...
-

 4.6KIncidents
4.6KIncidentsMagento Marketplace was hacked; the most insecure platform
Data protection experts reported an intrusion that has impacted Adobe Magento Marketplace users, employed to purchase, sell, and download themes and plugins...
-

 2.1KIncidents
2.1KIncidentsPalo Alto suffers data breach. Are its customers’ networks secured?
Information security specialists reported that Palo Alto Networks, a major security firm based in California, US, has become victim to a data...
-

 3.2KIncidents
3.2KIncidentsSecurity firm Prosegur shuts down operations after ransomware attack
According to ethical hacking specialists, multinational private security firm Prosegur was the victim of a massive ransomware attack that forced the shutdown...
-

 3.6KHack Tools
3.6KHack ToolsNetstat2Neo4J – Create Cypher Create Statements For Neo4J Out Of Netstat Files From Multiple Machines
Graphs help to spot anomalies and patterns in large datasets.This script takes netstat information from multiple hosts and formats them in a...
-

 2.1KData Security
2.1KData SecurityHow hotels are being hacked? A method used by cybercriminals
Multiple hotel chain employees constantly receive emails that they should probably ignore, as they could fall victim to a massive phishing campaign...
-
 3.2KHack Tools
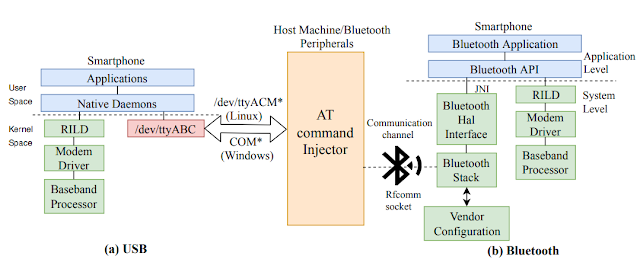
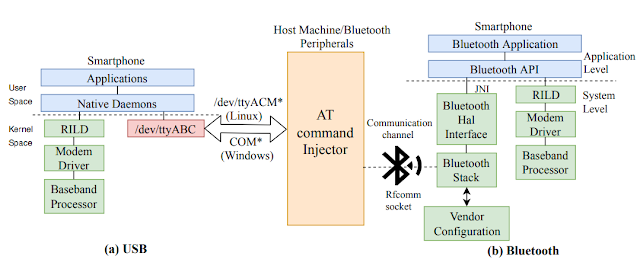
3.2KHack ToolsATFuzzer – Dynamic Analysis Of AT Interface For Android Smartphones
“Opening Pandora’s Box through ATFuzzer: Dynamic Analysis of AT Interface for Android Smartphones” is accepted to the 35th Annual Computer Security Applications...
-
 497Hack Tools
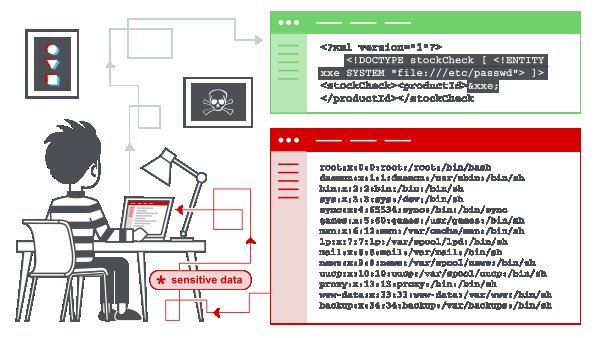
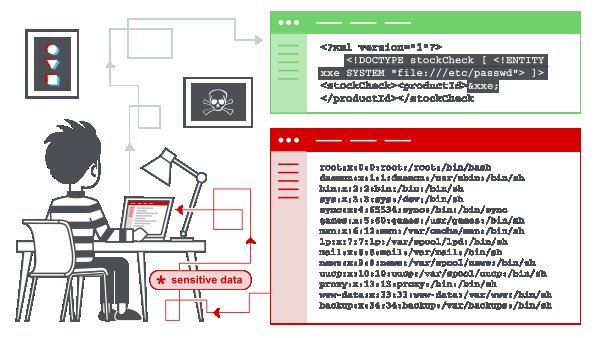
497Hack ToolsXML External Entity (XXE) Injection Payload List
In this section, we’ll explain what XML external entity injection is, describe some common examples, explain how to find and exploit various...
-

 483Incidents
483IncidentsCryptocurrency exchange platform Upbit was hacked; $50M USD robbed
Despite some of them have advanced security measures, cryptocurrency exchange platforms remain one of the hackers’ favorite targets. As reported by digital...
-
 3.3KMalware
3.3KMalwareThis malware infects your device when you watch a Facebook ad
Ethical hacking specialists from security firm ESET report the emergence of a new banking Trojan tracked in multiple locations in Latin America....
-
 1.1KHack Tools
1.1KHack ToolsKali Linux 2019.4 Release – Penetration Testing and Ethical Hacking Linux Distribution
We are incredibly excited to announce our fourth and final release of 2019, Kali Linux 2019.4. 2019.4 includes some exciting new updates:...
-

 3.4KVulnerabilities
3.4KVulnerabilitiesCritical SQL injection vulnerability affecting phpMyAdmin
Vulnerability testing specialists reported the finding of a security flaw in phpMyAdmin, one of the world’s most widely used MySQL database management...
-

 4.7KIncidents
4.7KIncidentsNursing homes affected by ransomware infection. Hackers demand 14M USD payment
Over a hundred nursing homes in the US have had their operations crippled because the company providing them with technology services has...
-

 2.9KVulnerabilities
2.9KVulnerabilitiesCritical server-side vulnerability in Jira affects cloud deployments; update now
Multiple reports have recently emerged about serious security flaws affecting cloud deployments. This time, digital forensics experts at security firm Palo Alto...






