All posts tagged "cybersecurity"
-

 3.3KVulnerabilities
3.3KVulnerabilitiesThe Vulnerabilities of the Past Are the Vulnerabilities of the Future
Major software vulnerabilities are a fact of life, as illustrated by the fact that Microsoft has patched between 55 and 110 vulnerabilities...
-

 2.4KMalware
2.4KMalwareExperts Uncover Yet Another Chinese Spying Campaign Aimed at Southeast Asia
An ongoing cyber-espionage operation with suspected ties to China has been found targeting a Southeast Asian government to deploy spyware on Windows...
-
 1.8KCyber Attack
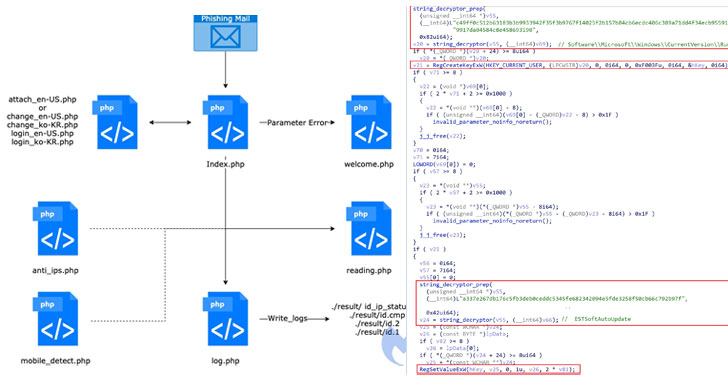
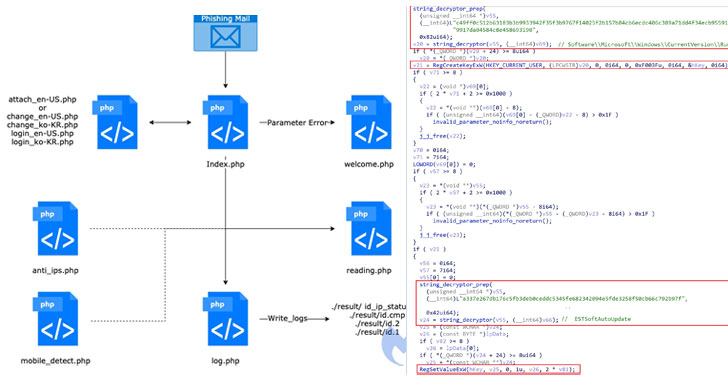
1.8KCyber AttackResearchers Uncover Hacking Operations Targeting Government Entities in South Korea
A North Korean threat actor active since 2012 has been behind a new espionage campaign targeting high-profile government officials associated with its...
-
 2.0KMalware
2.0KMalwareUS Seizes Domains Used by SolarWinds Hackers in Cyber Espionage Attacks
Days after Microsoft, Secureworks, and Volexity shed light on a new spear-phishing activity unleashed by the Russian hackers who breached SolarWinds IT...
-

 3.9KMalware
3.9KMalwareResearchers Warn of Facefish Backdoor Spreading Linux Rootkits
Cybersecurity researchers have disclosed a new backdoor program capable of stealing user login credentials, device information and executing arbitrary commands on Linux...
-

 1.4KMalware
1.4KMalwareSolarWinds Hackers Target Think Tanks With New ‘NativeZone’ Backdoor
Microsoft on Thursday disclosed that the threat actor behind the SolarWinds supply chain hack returned to the threat landscape to target government...
-

 592Malware
592MalwareChinese Cyber Espionage Hackers Continue to Target Pulse Secure VPN Devices
Cybersecurity researchers from FireEye unmasked additional tactics, techniques, and procedures (TTPs) adopted by Chinese threat actors who were recently found abusing Pulse...
-

 1.4KMalware
1.4KMalwareMalvertising Campaign On Google Distributed Trojanized AnyDesk Installer
Cybersecurity researchers on Wednesday publicized the disruption of a “clever” malvertising network targeting AnyDesk that delivered a weaponized installer of the remote...
-
 3.8KVulnerabilities
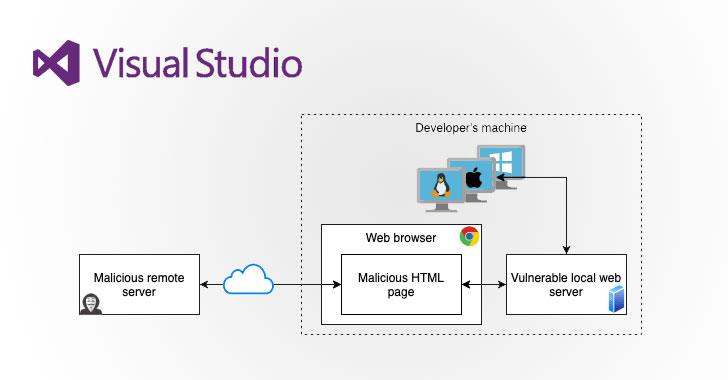
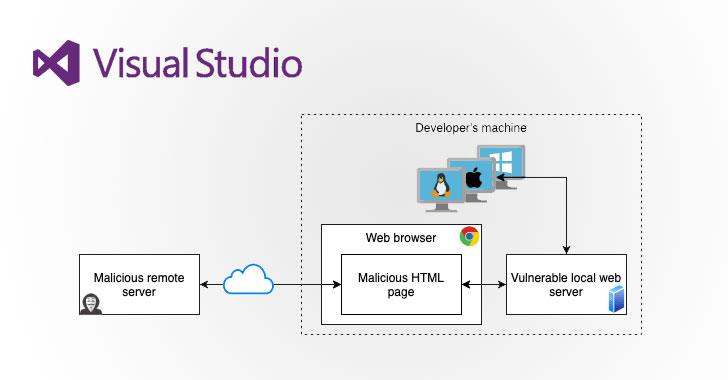
3.8KVulnerabilitiesNewly Discovered Bugs in VSCode Extensions Could Lead to Supply Chain Attacks
Severe security flaws uncovered in popular Visual Studio Code extensions could enable attackers to compromise local machines as well as build and...
-

 3.8KMalware
3.8KMalwareData Wiper Malware Disguised As Ransomware Targets Israeli Entities
Researchers on Tuesday disclosed a new espionage campaign that resorts to destructive data-wiping attacks targeting Israeli entities at least since December 2020...
-

 3.7KVulnerabilities
3.7KVulnerabilitiesNew High-Severity Vulnerability Reported in Pulse Connect Secure VPN
Ivanti, the company behind Pulse Secure VPN appliances, has published a security advisory for a high severity vulnerability that may allow an...
-

 4.3KVulnerabilities
4.3KVulnerabilitiesNew High-Severity Vulnerability Reported in Pulse Connect Secure VPN
Ivanti, the company behind Pulse Secure VPN appliances, has published a security advisory for a high severity vulnerability that may allow an...
-

 2.7KMalware
2.7KMalwareNew Bluetooth Flaws Let Attackers Impersonate Legitimate Devices
Adversaries could exploit newly discovered security weaknesses in Bluetooth Core and Mesh Profile Specifications to masquerade as legitimate devices and carry out...
-

 5.1KMalware
5.1KMalwareNew Bluetooth Flaws Let Attackers Impersonate Legitimate Devices
Adversaries could exploit newly discovered security weaknesses in Bluetooth Core and Mesh Profile Specifications to masquerade as legitimate devices and carry out...
-

 3.4KMalware
3.4KMalwareResearchers Link CryptoCore Attacks On Cryptocurrency Exchanges to North Korea
State-sponsored hackers affiliated with North Korea have been behind a slew of attacks on cryptocurrency exchanges over the past three years, new...
-

 4.1KMalware
4.1KMalwareResearchers Link CryptoCore Attacks On Cryptocurrency Exchanges to North Korea
State-sponsored hackers affiliated with North Korea have been behind a slew of attacks on cryptocurrency exchanges over the past three years, new...
-

 2.4KMalware
2.4KMalwareAir India Hack Exposes Credit Card and Passport Info of 4.5 Million Passengers
India’s flag carrier airline, Air India, has disclosed a data breach affecting 4.5 million of its customers over a period stretching nearly...
-
 1.1KMalware
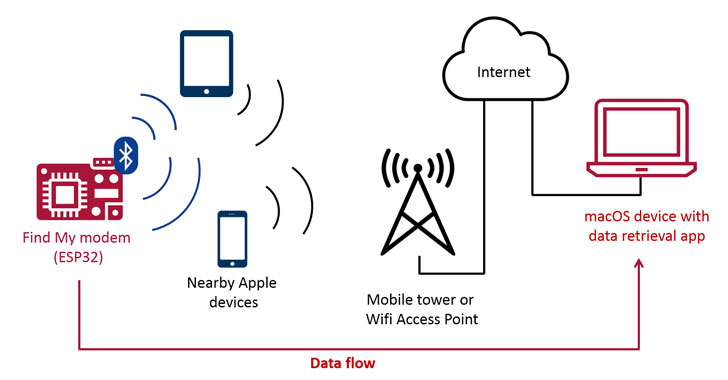
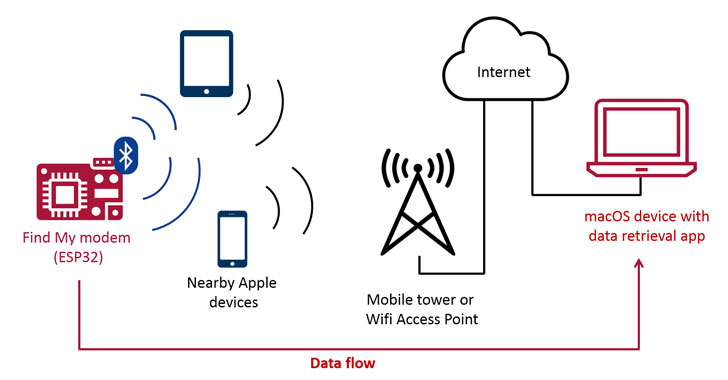
1.1KMalwareApple’s Find My Network Can be Abused to Exfiltrate Data From Nearby Devices
Latest research has demonstrated a new exploit that enables arbitrary data to be uploaded from devices that are not connected to the...
-

 1.5KMalware
1.5KMalwareExperts Warn About Ongoing AutoHotkey-Based Malware Attacks
Cybersecurity researchers have uncovered an ongoing malware campaign that heavily relies on AutoHotkey (AHK) scripting language to deliver multiple remote access trojans...
-

 1.0KMalware
1.0KMalwareHackers Using Microsoft Build Engine to Deliver Malware Filelessly
Threat actors are abusing Microsoft Build Engine (MSBuild) to filelessly deliver remote access trojans and password-stealing malware on targeted Windows systems. The...
-

 1.2KMalware
1.2KMalwareColonial Pipeline Paid Nearly $5 Million in Ransom to Cybercriminals
Colonial Pipeline on Thursday restored operations to its entire pipeline system nearly a week following a ransomware infection targeting its IT systems,...






