All posts tagged "malware"
-

 222Incidents
222IncidentsHome routers under attack in ongoing malvertisement blitz
DNSChanger causes network computers to visit fraudulent domains. As you read these words, malicious ads on legitimate websites are targeting visitors with...
-

 344Data Security
344Data SecurityThis Malware converts your Computer into a Cryptocurrency Miner
Zcash, a cryptocurrency that debuted on 28th October 2016, is believed to be more anonymous than the overhyped Bitcoin. This new virtual currency...
-
 305Geek
305GeekLow-cost Android Smartphones Shipped with Malicious Firmware
Security researchers at Dr.Web, a Russia-based antivirus developer firm, have identified various cheap Android brands are being shipped with a malware in their firmware...
-

 331Geek
331GeekScammers spreading celebrity nude PDFs on Facebook, pushing malware installation
Google Chrome is one of the most used Internet browsers but lately, it is being used by cybercriminals and scammers to infect...
-

 180Cyber Crime
180Cyber CrimeRansomware with a deal: Infect other computers, get your decryption key
We know that through ransomware, cyber criminals get an excellent opportunity to make some easy money by encrypting data on the victim’s...
-

 157Malware
157MalwareMicrosoft PowerShell Becomes a More Popular Malware-Spreading Tool
Symantec warns of growing number of malicious scripts. Microsoft PowerShell is a really powerful tool for IT professionals running Windows, and the...
-
 360Data Security
360Data SecurityNew Exo Android Trojan Sold on Hacking Forums, Dark Web
Malware coders are advertising a new Android trojan that can be used for phishing banking credentials, intercepting SMS messages, locking devices with...
-
 109Malware
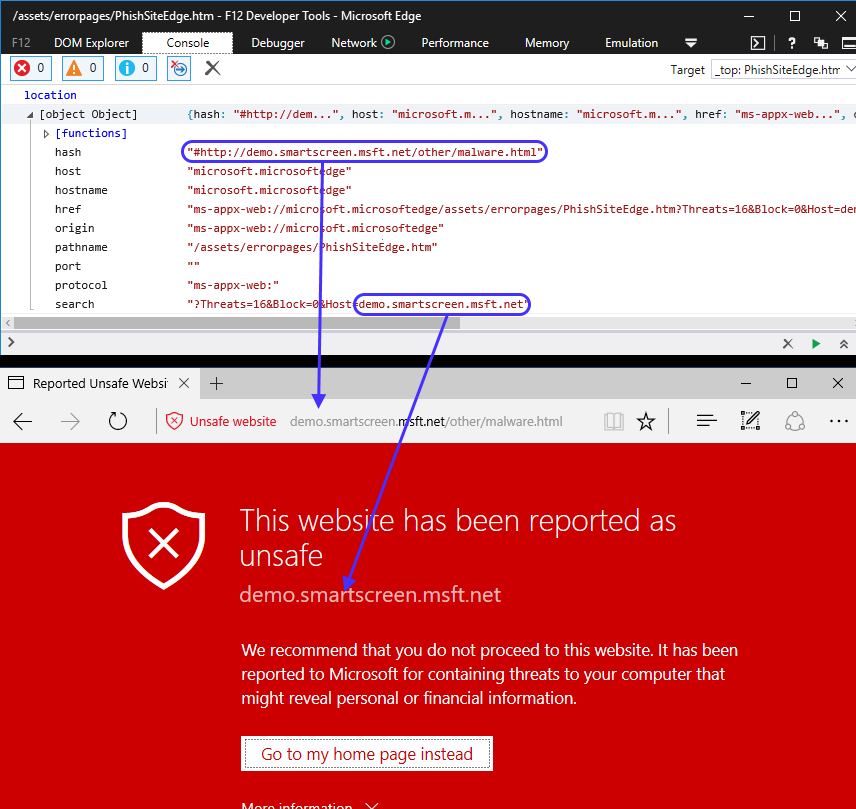
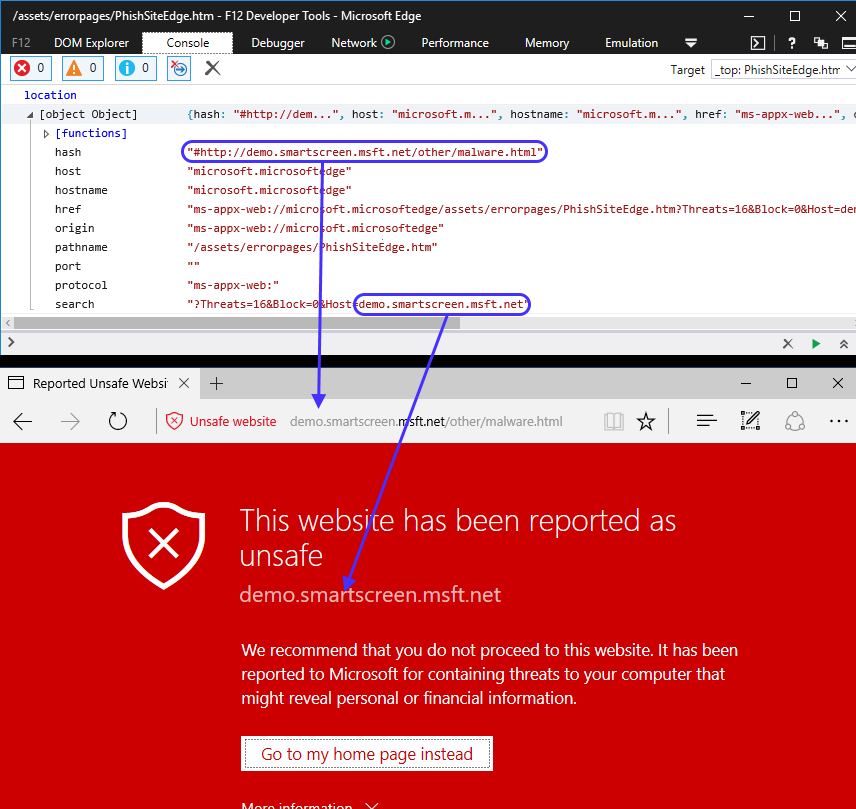
109MalwareSpoofing the Address Bar with the Malware Warning
Over the last few months, we’ve seen a proliferation of these tech-support scams where users end up “locked” in their browsers with...
-

 196Malware
196MalwareAndroid Malware Uses TeamViewer Mobile App to Take Control of Remote Devices
Crooks are spreading Android malware disguised as a one-time password (OTP) generator app for banking apps that steals the user’s banking credentials...
-
 319Data Security
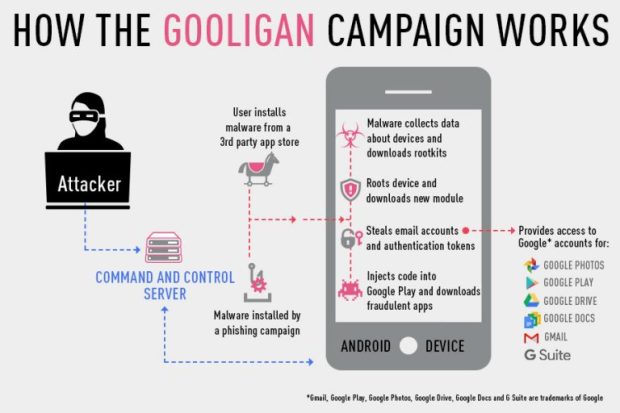
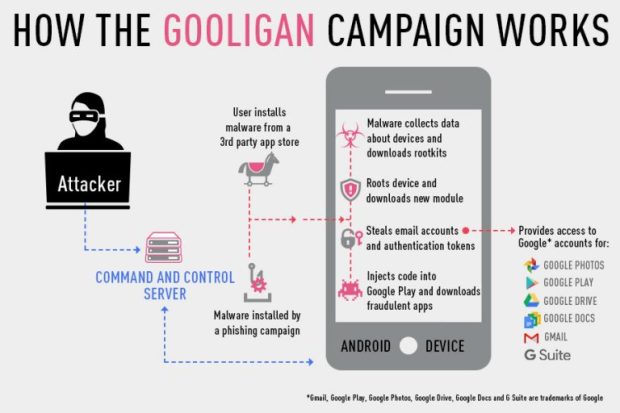
319Data SecurityMore Than 1 Million Google Accounts Breached by Gooligan
As a result of a lot of hard work done by our security research teams, we revealed today a new and alarming...
-

 290News
290NewsComputer Systems at Carleton University Shut Down due to Ransomware
Carleton University (Canada, Ottawa, Ontario) students must keep their computers and Wi-Fi routers off because some of the computers at the university...
-

 92Malware
92MalwareNew Proteus Malware Can Mine for Crypto-Currency, Log Keystrokes, and More
A new multi-functional malware family detected as Proteus can transform the computers of infected users in proxy servers, can mine for various...
-

 320News
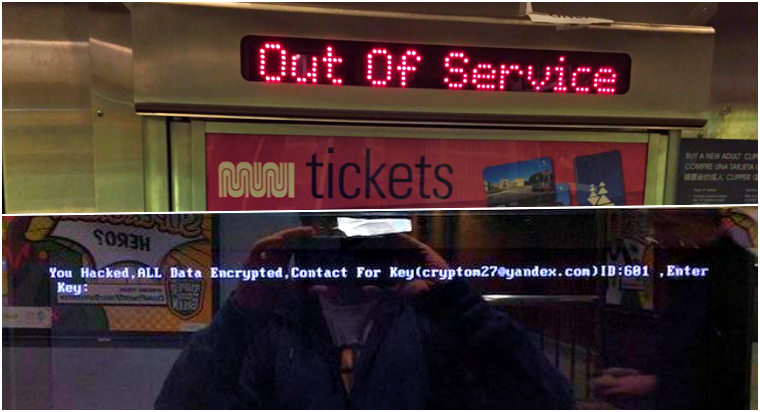
320NewsHacker Who Hacked SF Rail System for Ransom Hacked by Another Hacker
On Friday 25th, the San Francisco Municipal Railway (MUNI) had their computer systems hacked and locked by a hacker who ended up...
-
 294News
294NewsSan Francisco Railway’ Fare System Hacked for 100 Bitcoin Ransom
On Friday 25th, a report emerged that the San Francisco Municipal Railway (MUNI) couldn’t operate because its fare system, which is entirely...
-

 364Data Security
364Data SecurityMalware can Convert your Headphones into Microphone for Hackers
We know that our computer or laptop’s webcam is quite vulnerable to hacking and usually hiding their webcam’s lens with a piece...
-

 273Cyber Crime
273Cyber CrimeThe First Ransomware to Exploit Telegram Cracked and Decryptor Published
A security researcher whose name is Nathan Scott managed to break the encryption model employed by the Telecrypt ransomware. The unusual characteristic that made this virus to stand out was the server-client connection method. This...
-

 214Hacked
214HackedFeel “Safe”, Your Headphones Can Be Used As A Microphone To Spy On You
Short Bytes: Researchers at the Ben Gurion University, Israel, have created a malware, called Speake(a)r, to exploit a feature on Realtek codec chips....
-

 67Data Security
67Data Security[ TECHNICAL TEARDOWN: EXPLOIT & MALWARE IN .HWP FILES ]
This article will focus on teaching analysts on analysing malicious JavaScript code within the HWP files and a walkthrough of how we...
-
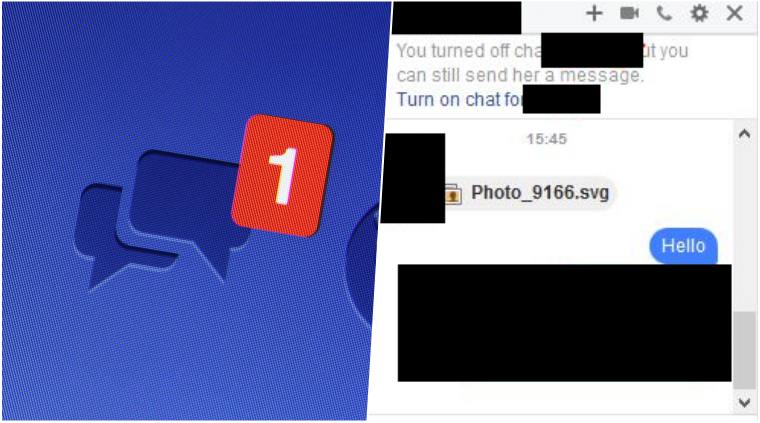
 344Cyber Crime
344Cyber CrimeScammers Using Images on Facebook Messenger to Drop Locky Ransomware
Facebook Messenger has become a favorite target of cyber-criminals lately since the social network’s messenger service is continuously being targeted with malware...
-
 88Data Security
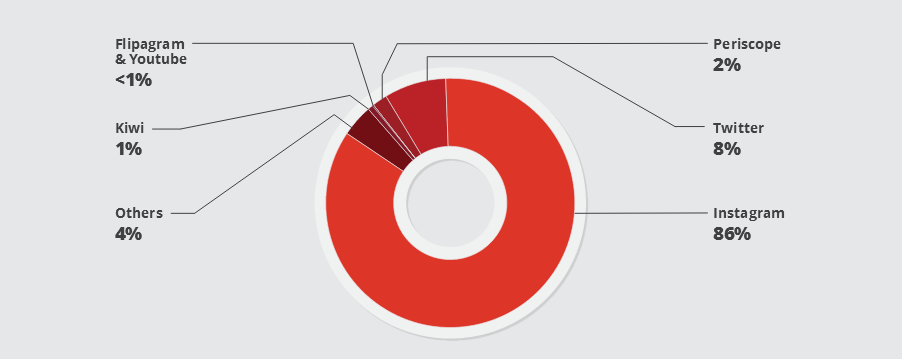
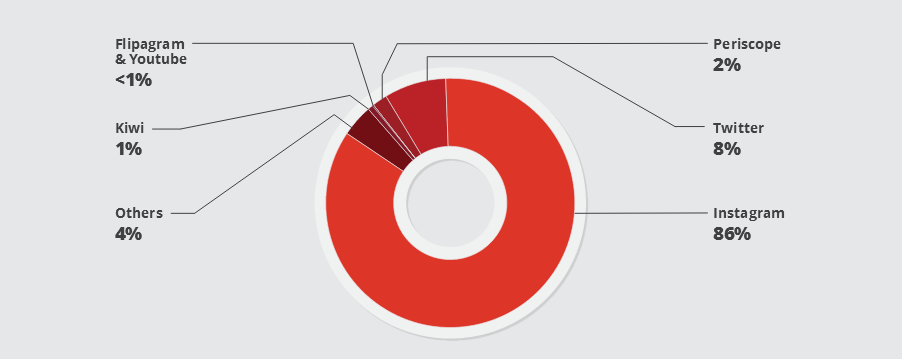
88Data SecurityA Botnet of IoT Devices Is Behind Many Instagram Fake Profiles
A botnet of IoT (Internet of Things) devices created with the Linux/Moose malware is behind many bots that are plaguing social networks...
-

 159Incidents
159IncidentsOffice Depot caught claiming out-of-box PCs showed “symptoms of malware”
News investigations show office supply chain sold unneeded fixes for $180. Office Depot and its sister retailer OfficeMax have stopped using a...






